TLS协议
TLS简介
TLS协议基于面向连接的TCP协议,它可被看作由两个主要部分组成:TLS记录协议(TLS Record Protocol)和TLS握手协议(TLS Handshake Protocol)。它可以实现传输应用数据前的通信双方身份的认证,加密套件(对称加密算法,签名算法等)的协商,会话密钥的协商,以及握手完成后的数据加密、压缩传输、以及数据完整性的校验。
TLS握手具体的过程
1.TCP三次握手
TCP的三次握手过程,建立TCP连接。
2.TLS握手过程
(1)TLS的握手是建立在TCP连接之上的。
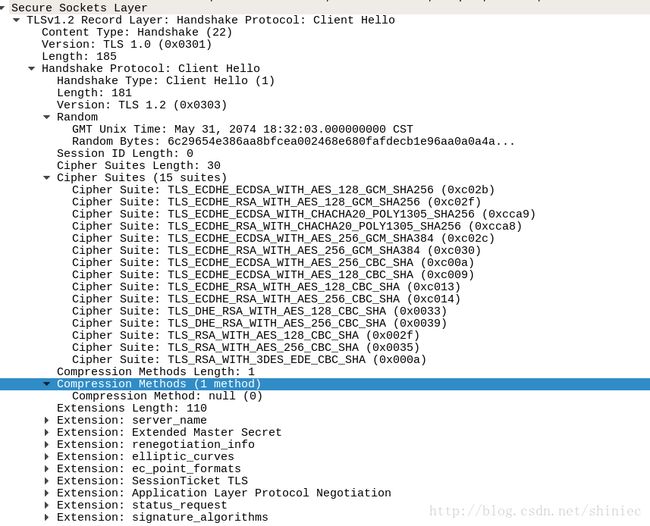
(2)客户端向服务器发送client hello数据包。
在client hello数据包中说明了客户端使用的协议版本号、随机数、加密套件以及其他的扩展。wireshark抓包结果如下图:
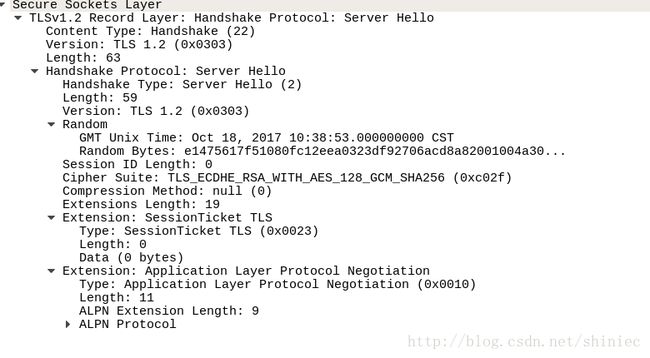
(3)服务器收到client hello后向客户端发送server hello数据包。
在server hello中包含了协议版本号、随机数、服务器选择的加密套件以及其他的扩展。wireshark抓包结果如下图:
(4)服务器向客户端发送证书。wireshark抓包结果如下图:
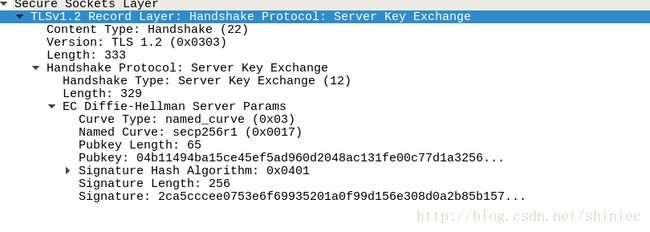
(5)服务器向客户端发送server key exchange,其中包含了pubkey,wireshark抓包结果如下图:
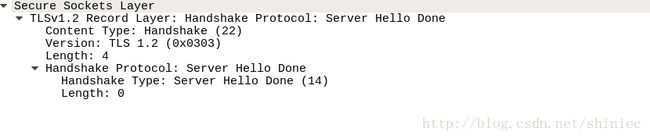
(6)服务器向客户端发送server hello done,wireshark抓包结果如下图:
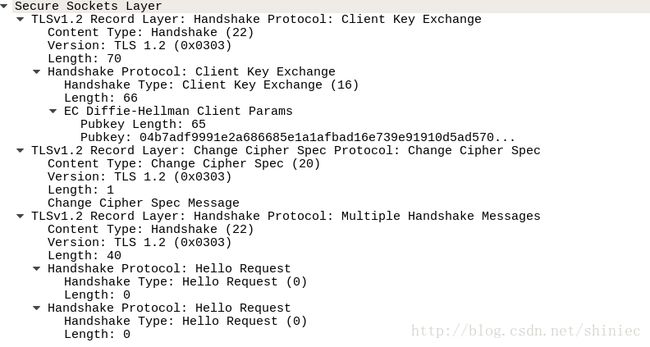
(7)客户端向服务器发送client key exchange、change cipher spec,wireshark抓包结果如下图:
(8)服务器向客户端发送new session ticket,wireshark抓包结果如下图:
(9)服务器向客户端发送change cipher spec, wireshark抓包结果如下图:
(10)服务器向客户端发送hello request, wireshark抓包结果如下图:
服务器向客户端发送change cipher spec, wireshark抓包结果如下图:
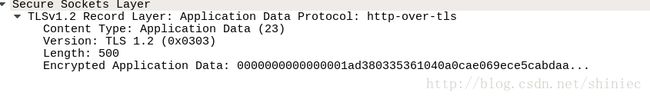
(11)客户端向服务器发送数据,wireshark抓包结果如下图:
openssl实现TLS
1.证书准备
在tls的通信中可以设置,双方认证和单向认证。如果需要双向的认证,需要有通信双方的证书。通过openssl的提供的应用程序功能可以搭建自己的简单的CA,从而颁发证书。
2.基于openssl的TLS实现
客户端程序
#include 服务器端程序
#include 参考
http://blog.csdn.net/liangyihuai/article/details/53098482