CAN201-Computer Network(2)
文章目录
- 4. Network Layer
-
- 4.1 Router
-
- 4.1.1 Input port functions
- 4.1.2 Destination-based forwarding
- 4.1.3 Switching fabrics
- 4.1.4 Input port queueing
- 4.1.5 Output ports
- 4.2 Internet Protocol
-
- 4.2.1 IP fragmentation, reassembly
- 4.3 IPv4 addressing
-
- 4.3.1 Subnets
- 4.3.2 Network Classes
- 4.3.3 CIDR
- 4.3.4 DHCP
- 4.3.5 Hierarchical addressing
- 4.4 NAT
- 4.5 IPv6
-
- 4.5.1 IPv6 datagram format:
- 4.5.22 Transition from IPv4 to IPv6
- 4.6 Generalized Forward and SDN
- 5. Control Plane
-
- 5.1 Routing protocols: Dijkstra
- 5.2 Routing protocols: Distance vector algorithm
- 5.3 Intra-AS routing in the Internet: OSPF
-
- 5.3.1 Internet approach to scalable routing
- 5.4 Routing among the ISPs: BGP
-
- 5.4.1 BGP messages
- 5.4.2 BGP route selection
- 5.4.3 achieving policy via advertisements
- 5.5 The SDN control plane
-
- 5.5.1 Key Characteristics of SDN Architecture
- 5.5.1 OpenFlow protocol
- 5.6 ICMP
- 5.6 SNMP
-
- 5.6.1 SNMP protocol
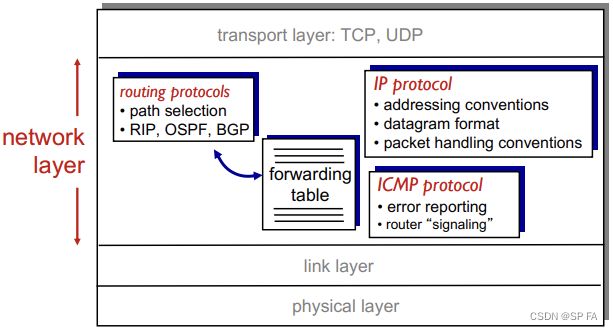
4. Network Layer
- Transport segment from sending to receiving host
- On sending side encapsulates segments into datagrams
- On receiving side, delivers segments to transport layer
- Network layer protocols in every host, router
- Router examines header fields in all IP datagrams passing through it.
Two key network-layer functions
- Forwarding: move packets from router’s input to appropriate router output.
- Routing: determine route taken by packets from source to destination (Routing algorithms)
data plane
- Local, per-router function
- Determines how datagram arriving on router input port is forwarded to router output port.
- Forwarding function
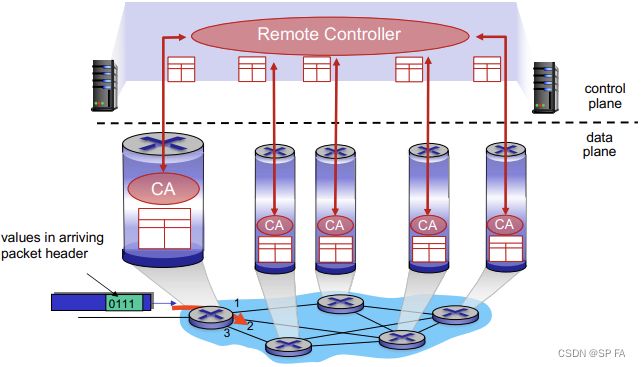
control plane
- Network-wide logic
- Determines how datagram is routed among routers along end-end path from source host to destination host
- Two control-plane approaches:
- traditional routing algorithms: implemented in routers.
- software-defined networking (SDN): implemented in (remote) servers.
Pre-router control plane
A distinct (typically remote) controller interacts with local control agents (CAs)
4.1 Router
High-level view of generic router architecture:

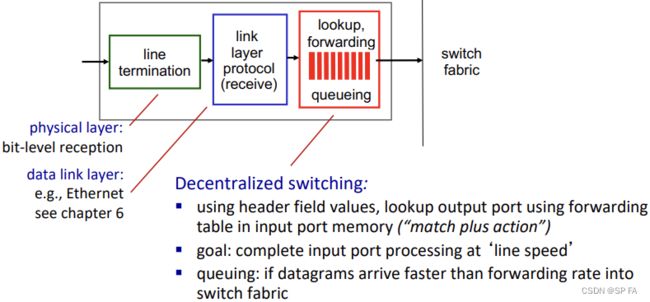
4.1.1 Input port functions
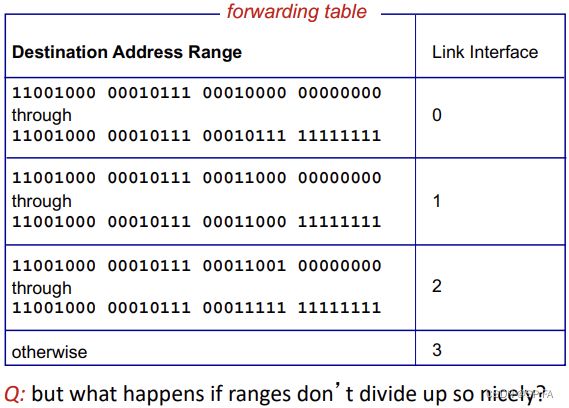
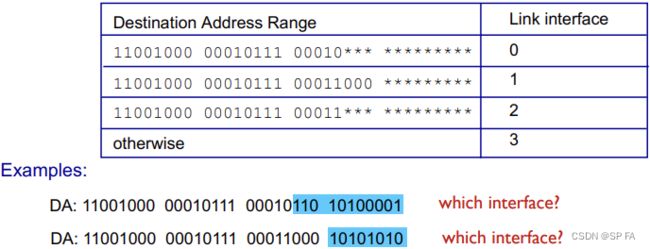
4.1.2 Destination-based forwarding
- When looking forwarding table entry for given destination address, use longest address prefix that matches destination address.
- Longest prefix matching: often performed using ternary content addressable memories (TCAMs)
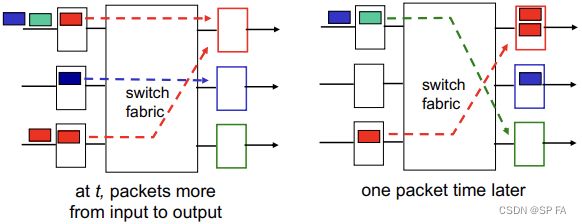
4.1.3 Switching fabrics
- Transfer packet from input buffer to appropriate output buffer
- Switching rate: rate at which packets can be transfer from inputs to outputs
- Often measured as multiple of input/output line rate
- N inputs: switching rate N times line rate desirable
- Three types of switching fabrics
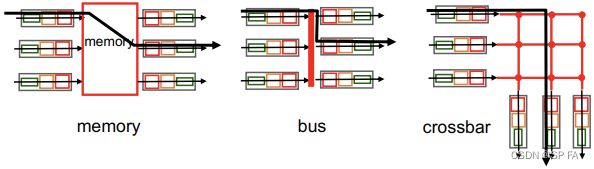
- Switching via memory (first generation routers)
- Traditional computers with switching under direct control of CPU
- Packet copied to system’s memory
- Speed limited by memory bandwidth (2 bus crossings per datagram)
- Switching via a bus
- Datagrams from input port memory to output memory via a shared bus
- Bus contention: switching speed limited by bus bandwidth
- Cisco 5600: 32 bus
- Switching via interconnection network
- Overcome bus bandwidth limitations
- Banyan networks, crossbar, other interconnection nets initially developed to connect processors in multiprocessor
- Advanced design: fragmenting datagram into fixed length cells, switch cells through the fabric
- Cisco 12000: switches 60 Gbps through the interconnection network.
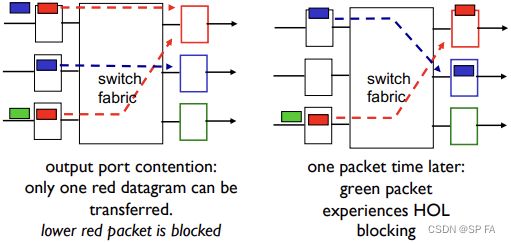
4.1.4 Input port queueing
- Fabric slower than input ports combined, so queueing may occur at input queues (queueing delay and loss due to input buffer overflow)
- Head-of-the-line (HOL) blocking: queued datagram at front of queue prevents others in queue from moving forward
4.1.5 Output ports
- RFC 3439 rule of thumb: average buffering equal to “typical” R T T RTT RTT (say 250 msec) times link capacity C C C
- Recent recommendation: with N N N flows, buffering equal to R T T ⋅ C N \frac{RTT\cdot C}{\sqrt N} NRTT⋅C
Scheduling mechanisms
- Scheduling: choose next packet to send on link
- FIFO scheduling: send in order of arrival to queue
- Discard policy: if packet arrives to full queue
- Tail drop: drop arriving packet
- Priority: drop/remove on priority basis
- Random: drop/remove randomly
- Discard policy: if packet arrives to full queue
- Priority
- send highest priority queued packet
- Multiple classes, with different priorities. Class may depend on marking or other header info (IP source / dest, port numbers)
- Round Robin (RR) scheduling
- Multiple classes
- Cyclically scan class queues, sending one complete packet from each class (if available)
- Weighted Fair Queueing (WFQ)
- Generalized Round Robin
- Each class gets weighted amount of service in each cycle
4.2 Internet Protocol
Host, router network layer functions:
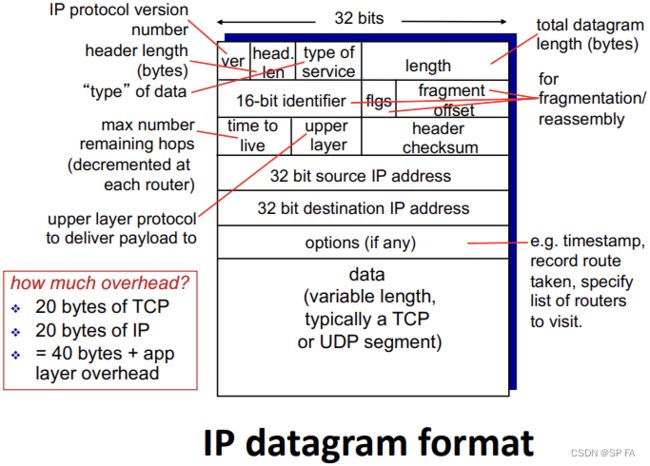
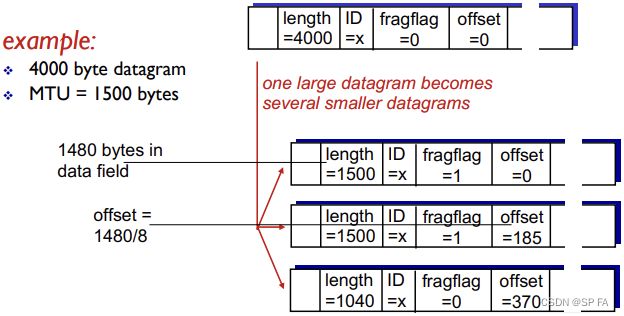
4.2.1 IP fragmentation, reassembly
Network links have MTU (max transfer size), largest possible link-level frame (Different link types, defferent MTUs)
Large IP datagram divided within net
- One datagram becomes several datagrams
- “Reassembled” only at final destination
- IP header bits used to identify, order related fragments.
4.3 IPv4 addressing
IP address: 32-bit identifier for host, router interface
Interface: connection between host/router and physical link
- Router’s typically have multiple interfaces
- Host typically has one or two interfaces
IP addresses associated with each interface
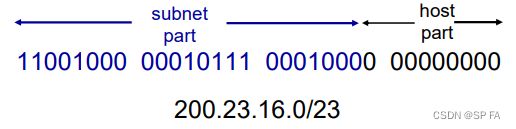
4.3.1 Subnets
IP address, two parts:
- Subnet part: high order bits
- Host part: low order bits
What’s a subnet?
Device interfaces with same subnet part of IP address. Can physically reach each other without intervening router
Recipe
To determine the subnets, detach each interface from its host or router, creating islands of isolated networks. Each isolated network is called a subnet.
4.3.2 Network Classes
Classful addressing
- The network portion of an IP address were constrained to be 8, 16, or 24 bits in length.
- Subnets with 8-, 16-, and 24-bit subnet addresses were known as class A, B and C networks.
- It became problematic
- A class A (/8) subnet could accommodate only up to 2 8 − 2 = 254 2^8 − 2 = 254 28−2=254 hosts
- A class B (/16) subnet supporting 2 16 – 2 = 65534 2^{16} – 2 = 65534 216–2=65534 hosts, which is too large
4.3.3 CIDR
CIDR: Classless Inter Domain Routing
- Subnet portion of address of arbitrary length
- Address format: a.b.c.d/x, where x is # bits in subnet portion of address
4.3.4 DHCP
DHCP: Dynamic Host Configuration Protocol
Goal: allow host to dynamically obtain its IP address from network server when it joins network
- Can renew its lease on address in use
- Allows reuse of addresses (only hold address while connected/“on”)
- Support for mobile users who want to join network (more shortly)
DHCP overview:
- host broadcasts “DHCP discover” msg [optional]
- DHCP server responds with “DHCP offer” msg [optional]
- host requests IP address: “DHCP request” msg
- DHCP server sends address: “DHCP ack” msg
DHCP can return more than just allocated IP address on subnet:
- Address of first-hop router for client
- Name and IP address of DNS sever
- Network mask (indicating network versus host portion of address)
4.3.5 Hierarchical addressing
route aggregation
Hierarchical addressing allows efficient advertisement of routing information
The ability to use a single prefix to advertise multiple networks is often referred to as address aggregation or route aggregation.
4.4 NAT
NAT: network address translation

Motivation: local network uses just one IP address as far as outside world is concerned:
- Range of addresses not needed from ISP: just one IP address for all devices
- Can change addresses of devices in local network without notifying outside world
- Can change ISP without changing addresses of devices in local network
- Devices inside local net not explicitly addressable, visible by outside world (a security plus)
Implementation: NAT router must:
- Remember (in NAT translation table) every (source IP address, port #) to (NAT IP address, new port #) translation pair
- Outgoing datagrams: replace (source IP address, port #) of every outgoing datagram to (NAT IP address, new port #)
- Incoming datagrams: replace (NAT IP address, new port #) in dest fields of every incoming datagram with corresponding (source IP address, port #) stored in NAT table.
16-bit port-number field: 60,000 simultaneous connections with a single LAN-side address.
NAT is controversial:
- Routers should only process up to layer 3
- Address shortage should be solved by IPv6
- Violates end-to-end argument (NAT possibility must be taken into account by app designers, e.g., P2P applications)
- NAT traversal: what if client wants to connect to server behind NAT?
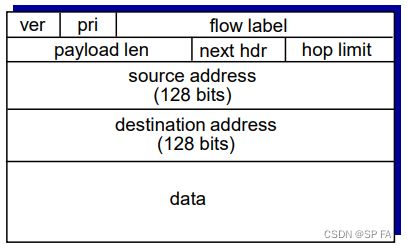
4.5 IPv6
Initial motivation: 32-bit address space soon to be completely allocated.
Additional motivation:
- Header format helps speed processing/forwarding
- Header changes to facilitate Q&S
4.5.1 IPv6 datagram format:
Fixed-length 40 byte header. No fragmentation allowed.
- Priority (Traffic Class): identify priority among datagrams in flow.
- Flow Label: identify datagrams in same “flow”.
- Next header: identify upper layer protocol for data.
Other changes from IPv4
- Checksum: removed entirely to reduce processing time at each hop.
- Options: allowed, but outside of header, indicated by “Next Header” field.
- ICMPv6: new version of ICMP. Additional message types and Multicast group management functions.
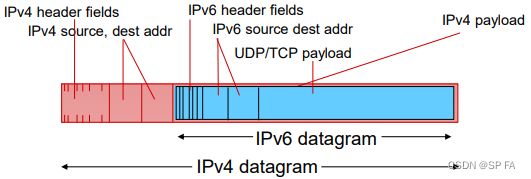
4.5.22 Transition from IPv4 to IPv6
Not all routers can be upgraded simultaneously
- No “flag days”
- How will network operate with mixed IPv4 and IPv6 routers?
Tunneling: IPv6 datagram carried as payload in IPv4 datagram among IPv4 routers
4.6 Generalized Forward and SDN
- Flow: defined by header fields
- Generalized forwarding: simple packet-handling rules
- Pattern: match values in packet header fields
- Actions: for matched packet: drop, forward, modify, matched packet or send matched packet to controller
- Priority: disambiguate overlapping patterns
- Counters: #bytes and #packets
Flow table in a router (computed and distributed by controller) define router’s match + action rules
OpenFlow: Flow Table Entries
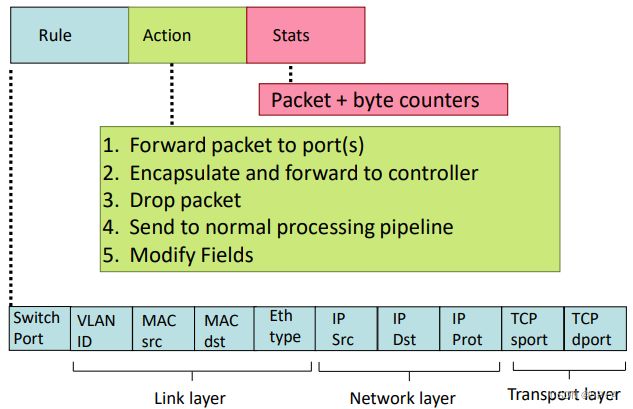
match+action: unifies different kinds of devices
- Router
- match: longest destination IP prefix
- action: forward out a link
- Switch
- match: destination MAC address
- action: forward or flood
- Firewall
- match: IP addresses and TCP/UDP port numbers
- action: permit or deny
- NAT
- match: IP address and port
- action: rewrite address and port
5. Control Plane
two network-layer functions:
- forwarding: move packets from router’s input port to appropriate output port (data plane)
- routing: determine route taken by packets from source to destination (control plane)
Two approaches to structuring network control plane:
- per-router control (traditional): Individual routing algorithm components in each and every router interact with each other in control plane to compute forwarding tables
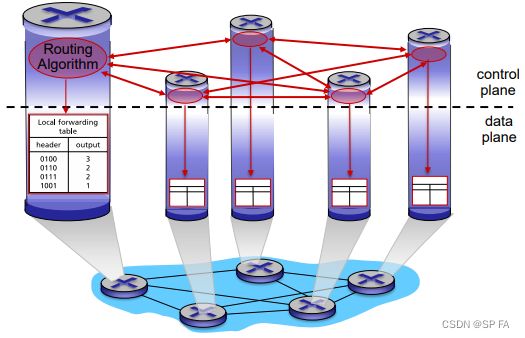
- logically centralized control (software defined networking): A distinct (typically remote) controller interacts with local control agents (CAs) in routers to compute forwarding tables

Why a logically centralized control plane?
- Easier network management: avoid router misconfigurations, greater flexibility of traffic flows
- Table-based forwarding (recall OpenFlow API) allows “programming” routers
- Centralized “programming” easier: compute tables centrally and distribute
- Distributed “programming more difficult: compute tables as result of distributed algorithm (protocol) implemented in each and every router
- Open (non-proprietary) implementation of control plane
5.1 Routing protocols: Dijkstra
Routing protocol goal: determine “good” paths (equivalently, routes), from sending hosts to receiving host, through network of routers
- Path: sequence of routers packets will traverse in going from given initial source host to given final destination host
- “good”: least “cost”, “fastest”, “least congested”
- Routing: a “top-10” networking challenge!
使用 Dijkstra 算法来解决,把网络抽象为一张图,跑最短路。
5.2 Routing protocols: Distance vector algorithm
From time-to-time, each node sends its own distance vector estimate to neighbors When x receives new DV estimate from neighbor, it updates
its own DV using B-F equation (通过松弛更新当前节点的最短路)
Iterative, asynchronous: each local iteration caused by:
- Local link cost change
- DV update message from neighbor
Distributed: Each node notifies neighbors only when its DV changes, neighbors then notify their neighbors if necessary.
link cost changes
- Node detects local link cost change
- Updates routing info, recalculates distance vector
- If DV changes, notify neighbors
- good news travels fast but Bad news travels slow – “count to infinity”
5.3 Intra-AS routing in the Internet: OSPF
Making routing scalable
Our routing study thus far - idealized
- All routers identical
- Network “flat”
Scale: with billions of destinations:
- Can’t store all destinations in routing tables!
- Routing table exchange would swamp links!
Administrative autonomy
- Internet = network of networks
- Each network admin may want to control routing in its own network
5.3.1 Internet approach to scalable routing
Aggregate routers into regions known as “autonomous systems” (AS)
Intra-AS routing
- Routing among hosts, routers in same AS
- All routers in AS must run same intra-domain protocol
- Routers in different AS can run different intra-domain routing protocol
- Gateway router: at “edge” of its own AS, has link(s) to router(s) in other AS’es
Inter-AS routing
- Routing among AS’es
- Gateways perform inter-domain routing (as well as intra-domain routing)
Interconnected ASes
Forwarding table configured by both intra- and inter-AS routing algorithm
- Intra-AS routing determine entries for destinations within AS
- Inter-AS & intra-AS determine entries for external destinations
Inter-AS tasks
Suppose router in AS1 receives datagram destined outside of AS1:
- Router should forward packet to gateway router, but which one?
- AS1 must:
- Learn which dests are reachable through AS2, which through AS3
- Propagate this reachability info to all routers in AS1
Intra-AS Routing
Aka interior gateway protocols (IGP)
Most common intra-AS routing protocols:
- RIP: Routing Information Protocol
- OSPF: Open Shortest Path First (IS-IS* protocol essentially same as OSPF)
- IGRP: Interior Gateway Routing Protocol (Cisco proprietary for decades, until 2016)
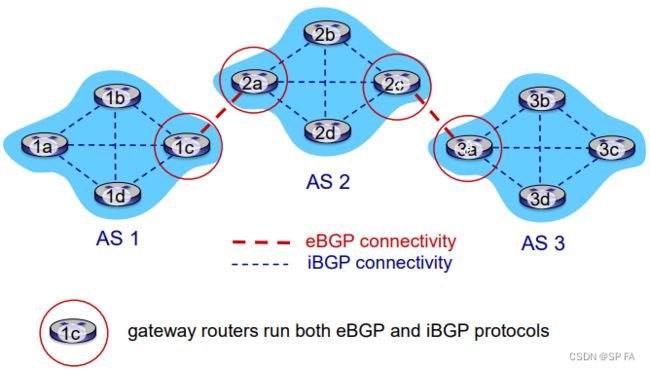
5.4 Routing among the ISPs: BGP
BGP (Border Gateway Protocol): the de facto inter-domain routing protocol
BGP provides each AS router a means to:
- eBGP: obtain subnet prefix reachability information from neighboring ASes. Allows subnet to advertise its existence to rest of Internet: “I am here.”
- iBGP: propagate reachability information to all AS-internal routers, and determine “best” routes to other networks based on reachability information and policy
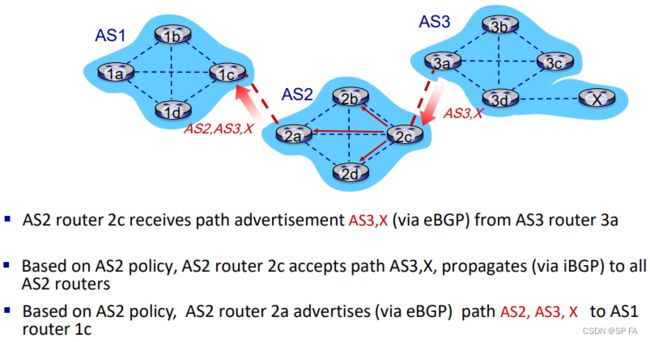
- BGP session: two BGP routers (“peers”) exchange BGP messages over semi-permanent TCP connection (using port 179). Advertising paths to different destination network prefixes (BGP is a “path vector” protocol)
- When AS3 gateway router 3a advertises path AS3,X to AS2 gateway router 2c: AS3 promises to AS2 it will forward datagrams towards X.

Path attributes and BGP routes
Advertised prefix includes BGP attributes: prefix + attributes = “route”
Two important attributes:
- AS-PATH: list of ASes through which prefix advertisement has passed.
- NEXT-HOP: indicates the IP address of the router interface that begins the AS-PATH.
- Policy-based routing:
- Gateway receiving route advertisement uses import policy to accept/decline path (e.g., never route through AS Y).
- AS policy also determines whether to advertise path to other neighboring ASes.
5.4.1 BGP messages
- BGP messages exchanged between peers over TCP connection
- BGP messages:
- OPEN: opens TCP connection to remote BGP peer and authenticates sending BGP peer
- UPDATE: advertises new path (or withdraws old)
- KEEPALIVE: keeps connection alive in absence of UPDATES; also ACKs OPEN request
- NOTIFICATION: reports errors in previous msg; also used to close connection
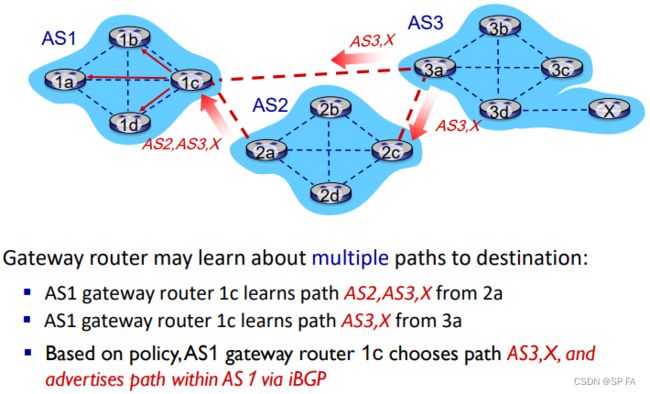
5.4.2 BGP route selection
Router may learn about more than one route to destination AS, selects route based on:
- local preference value attribute: policy decision
- shortest AS-PATH
- closest NEXT-HOP router: hot potato routing
- choose local gateway that has least intra-domain cost, don’t worry about inter-domain cost
- additional criteria
5.4.3 achieving policy via advertisements
Suppose an ISP only wants to route traffic to/from its customer networks (does not want to carry transit traffic between other ISPs)
A,B,C are provider networks, X,W,Y are customer (of provider networks), X is dual-homed: attached to two networks.
policy to enforce: X does not want to route from B to C via X, so X will not advertise to B a route to C

- A advertises path Aw to B and to C
- B chooses not to advertise BAw to C:
- B gets no “revenue” for routing CBAw, since none of C, A, w are B’s customers.
- C does not learn about CBAw path
- C will route through CAw (not using B) to get to w
Why different Intra-, Inter-AS routing?
Policy:
- inter-AS: admin wants control over how its traffic routed, who routes through its net.
- intra-AS: single admin, so no policy decisions needed
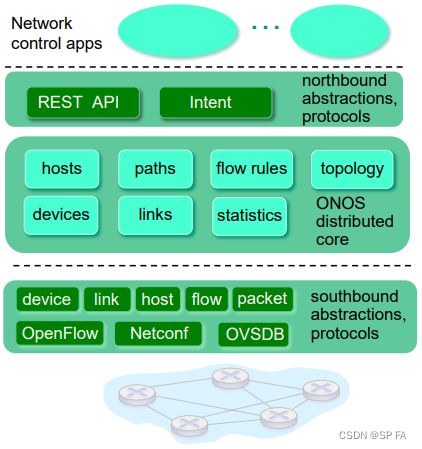
5.5 The SDN control plane
SDN: Software defined networking
- Internet network layer: historically has been implemented via distributed, per-router approach
- Monolithic router contains switching hardware, runs proprietary implementation of Internet standard protocols (IP, RIP, IS-IS, OSPF, BGP) in proprietary router OS (e.g., Cisco IOS)
- Different “middleboxes” for different network layer functions: firewalls, load balancers, NAT boxes,
- Renewed interest in rethinking network control plane
5.5.1 Key Characteristics of SDN Architecture
- Fast, simple, commodity switches implementing generalized data-plane forwarding in hardware
- Switch flow table computed, installed by controller
- API for table-based switch control: defines what is controllable and what is not
- Protocol for communicating with controller
SDN controller (network OS)
- Maintains network state information
- Interacts with network control applications “above” via northbound API
- Interacts with network switches “below” via southbound API
- Implemented as distributed system for performance, scalability, fault-tolerance, robustness
Network-control apps
- “brains” of control: implement control functions using lower-level services, API provided by SND controller
- Open: can be provided by 3rd party: distinct from routing vendor, or SDN controller
5.5.1 OpenFlow protocol
- Operates between controller, switch
- TCP used to exchange messages (optional encryption)
- Three classes of OpenFlow messages:
- controller-to-switch
- asynchronous (switch to controller)
- symmetric (misc)
controller-to-switch messages
- Features: controller queries switch features, switch replies
- Configure: controller queries/sets switch configuration parameters
- Modify-state: add, delete, modify flow entries in the OpenFlow tables
- Packet-out: controller can send this packet out of specific switch port
switch-to-controller messages
- Packet-in: transfer packet (and its control) to controller. See packet-out message from controller
- Flow-removed: flow table entry deleted at switch
- Port status: inform controller of a change on a port.
OpenDaylight (ODL) controller
- ODL Lithium controller
- Network apps may be contained within, or be external to SDN controller
- Service Abstraction Layer: interconnects internal, external applications and services
- Control apps separate from controller
- Intent framework: high-level specification of service: what rather than how
- Considerable emphasis on distributed core: service reliability, replication performance scaling.
5.6 ICMP
ICMP: internet control message protocol
Used by hosts & routers to communicate network-level information
- error reporting: unreachable host, network, port, protocol
- echo request/reply (used by ping)
Network-layer “above” IP:
- ICMP msgs carried in IP datagrams
ICMP message: type, code plus first 8 bytes of IP datagram causing error.
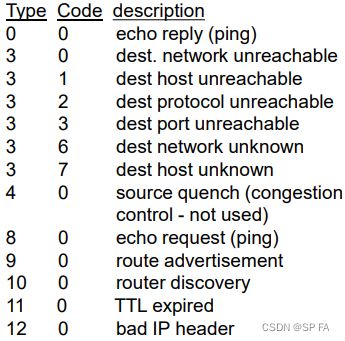
Traceroute and ICMP
Source sends series of UDP segments to destination
- first set has TTL =1
- second set has TTL=2, etc.
- unlikely port number
When datagram in nth set arrives to nth router:
- router discards datagram and sends source ICMP message (type 11, code 0)
- ICMP message include name of router & IP address
When ICMP message arrives, source records RTTs.
Stopping criteria:
- UDP segment eventually arrives at destination host
- destination returns ICMP “port unreachable” message (type 3, code 3)
- source stops
5.6 SNMP
Network management includes the deployment, integration and coordination of the hardware, software, and human elements to monitor, test, poll, configure, analyze, evaluate, and control the network and element resources to meet the real-time, operational performance, and Quality of Service requirements at a reasonable cost. – Saydam 1996
Infrastructure for network management
Managed devices contain managed objects whose data is gathered into a Management Information Base (MIB)
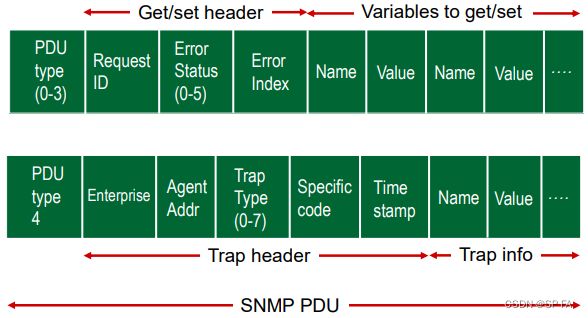
5.6.1 SNMP protocol
Two ways to convey MIB info, commands:

message types
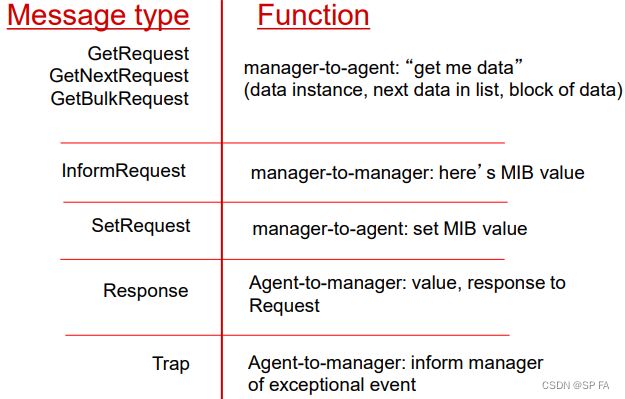
message formats