upload-labs通关(Pass-06~Pass-10)
目录
Pass-06
Pass-07
Pass-08
Pass-09
Pass-10
Pass-06
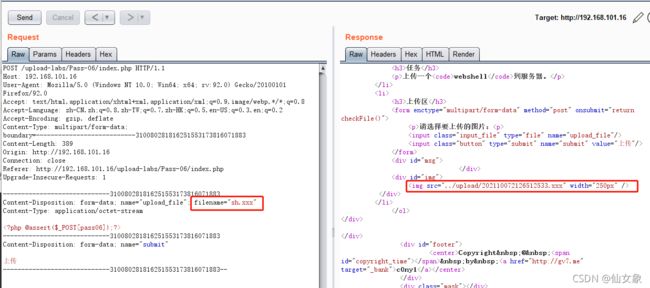
上传sh.php失败,burp中将抓到的包send to repeater
修改filename为sh.xxx发现可以上传成功,说明是黑名单过滤
将报文send to intruder,按照Pass-03的套路爆破后缀名(upload-labs通关(Pass-01~Pass-05)_箭雨镜屋-CSDN博客)
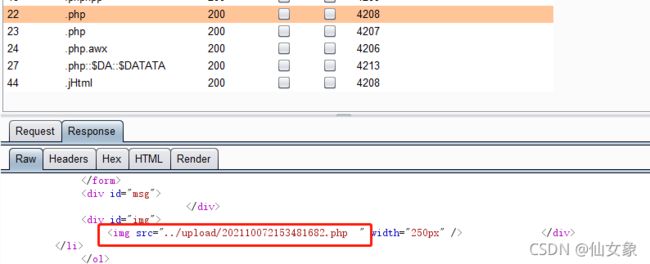
爆破结果用../upload过滤,发现只有如下后缀的文件上传成功
仔细查看Response报文后发现,有如下两个文件可以作为webshell(服务器是windows系统),也就是说本关可以双写::$DATA绕过,也可以用大写绕过
用蚁剑尝试一下连接这两个shell。先试双写::$DATA的,如下图所示,可以连接成功
再试试大写绕过的。特别注意,我在我的环境上,用apache 2.4.39的时候连接失败,Response报文状态码500,用nginx 1.15.11是可以成功的,并且用蚁剑连接的时候,蚁剑中url地址的文件名后缀大小写无所谓。
代码分析:
比起之前的关卡,本关在用上传文件的文件名后缀和黑名单比较之前没有把文件后缀转换成小写,所以大写绕过黑名单过滤可以成功。
if (isset($_POST['submit'])) {
if (file_exists(UPLOAD_PATH)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess",".ini");
$file_name = trim($_FILES['upload_file']['name']);
$file_name = deldot($file_name);//删除文件名末尾的点
$file_ext = strrchr($file_name, '.');
$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA
$file_ext = trim($file_ext); //首尾去空
if (!in_array($file_ext, $deny_ext)) {
$temp_file = $_FILES['upload_file']['tmp_name'];
$img_path = UPLOAD_PATH.'/'.date("YmdHis").rand(1000,9999).$file_ext;
if (move_uploaded_file($temp_file, $img_path)) {
$is_upload = true;
} else {
$msg = '上传出错!';
}
} else {
$msg = '此文件类型不允许上传!';
}
} else {
$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';
}
}Pass-07
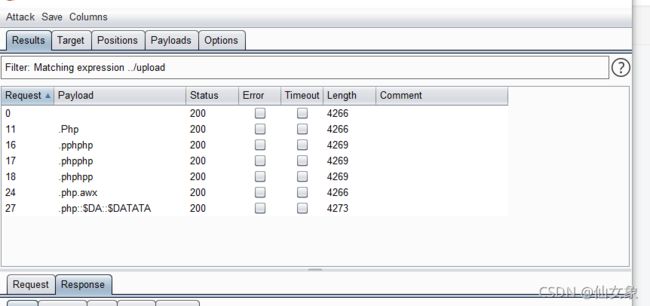
上传sh.php失败,burp中将抓到的包send to repeater
修改filename为sh.xxx发现可以上传成功,说明是黑名单过滤
将报文send to intruder,按照Pass-03的套路爆破后缀名,爆破结果用../upload过滤,发现只有如下后缀的文件上传成功
仔细观察Response报文后发现,本关可以双写::$DATA或者在文件名末尾加空格绕过(windows系统)
双写::$DATA的webshell之前演示过,就不演示了,演示一下以空格结尾的webshell,第22个payload是两个空格,第23个payload是一个空格,这里仅以22演示,其实也和之前关卡提到的文件名以0x88结尾差不多。
代码分析:
本关代码其实也没啥可分析的,本来黑名单就不安全,还分析个啥。。不过相比Pass-05,本关在用上传的文件的后缀和黑名单比较之前,没有把结尾的空格去掉,所以可以用空格绕过。
if (isset($_POST['submit'])) {
if (file_exists(UPLOAD_PATH)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess",".ini");
$file_name = $_FILES['upload_file']['name'];
$file_name = deldot($file_name);//删除文件名末尾的点
$file_ext = strrchr($file_name, '.');
$file_ext = strtolower($file_ext); //转换为小写
$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA
if (!in_array($file_ext, $deny_ext)) {
$temp_file = $_FILES['upload_file']['tmp_name'];
$img_path = UPLOAD_PATH.'/'.date("YmdHis").rand(1000,9999).$file_ext;
if (move_uploaded_file($temp_file,$img_path)) {
$is_upload = true;
} else {
$msg = '上传出错!';
}
} else {
$msg = '此文件不允许上传';
}
} else {
$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';
}
}Pass-08
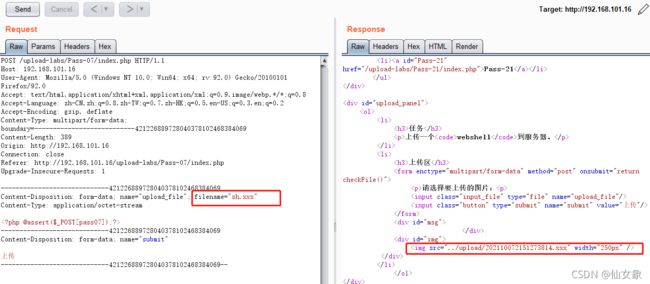
上传sh.php失败,burp中将抓到的包send to repeater
修改filename为sh.xxx发现可以上传成功,说明是黑名单过滤
将报文send to intruder,按照Pass-03的套路爆破后缀名,爆破结果用../upload过滤,发现只有如下后缀的文件上传成功
仔细观察Response报文后发现,本关可以通过在文件名末尾加.绕过(第20,第21个payload,windows系统)
虽然爆破结果中显示上传成功的文件名有../upload/sh.php.和../upload/sh.php..,但实际上服务器上的文件名是sh.php,所以用蚁剑连接的时候文件名末尾不需要加点(不过加点也不碍事)
代码分析:
不看代码都能猜到这关是把去掉文件名末尾的点的步骤删掉了。。。
if (isset($_POST['submit'])) {
if (file_exists(UPLOAD_PATH)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess",".ini");
$file_name = trim($_FILES['upload_file']['name']);
$file_ext = strrchr($file_name, '.');
$file_ext = strtolower($file_ext); //转换为小写
$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA
$file_ext = trim($file_ext); //首尾去空
if (!in_array($file_ext, $deny_ext)) {
$temp_file = $_FILES['upload_file']['tmp_name'];
$img_path = UPLOAD_PATH.'/'.$file_name;
if (move_uploaded_file($temp_file, $img_path)) {
$is_upload = true;
} else {
$msg = '上传出错!';
}
} else {
$msg = '此文件类型不允许上传!';
}
} else {
$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';
}
}
Pass-09
上传sh.php失败,burp中将抓到的包send to repeater
修改filename为sh.xxx发现可以上传成功,说明是黑名单过滤
将报文send to intruder,按照Pass-03的套路爆破后缀名,爆破结果用../upload过滤,发现只有如下后缀的文件上传成功
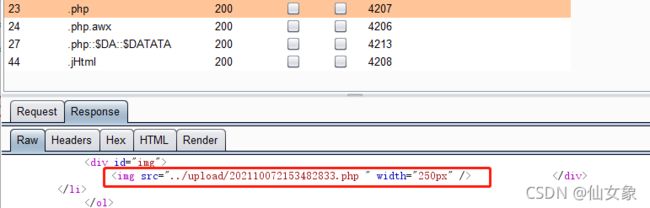
仔细观察Response报文后发现,本关可以通过在文件名末尾加::$DATA来绕过(windows系统)
![]()
蚁剑连接的时候,文件后缀直接写.php就行,不要加::$DATA
代码分析:
不看代码都能猜到这关是把去掉字符串::$DATA的步骤删掉了。。。
if (isset($_POST['submit'])) {
if (file_exists(UPLOAD_PATH)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess",".ini");
$file_name = trim($_FILES['upload_file']['name']);
$file_name = deldot($file_name);//删除文件名末尾的点
$file_ext = strrchr($file_name, '.');
$file_ext = strtolower($file_ext); //转换为小写
$file_ext = trim($file_ext); //首尾去空
if (!in_array($file_ext, $deny_ext)) {
$temp_file = $_FILES['upload_file']['tmp_name'];
$img_path = UPLOAD_PATH.'/'.date("YmdHis").rand(1000,9999).$file_ext;
if (move_uploaded_file($temp_file, $img_path)) {
$is_upload = true;
} else {
$msg = '上传出错!';
}
} else {
$msg = '此文件类型不允许上传!';
}
} else {
$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';
}
}Pass-10
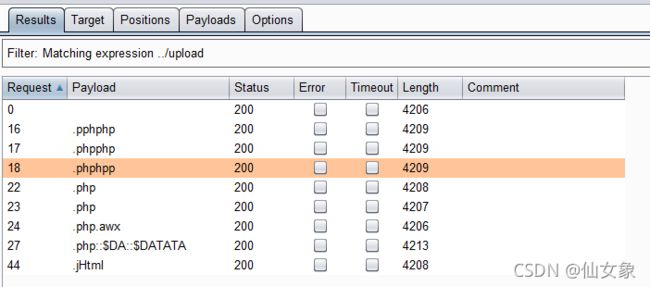
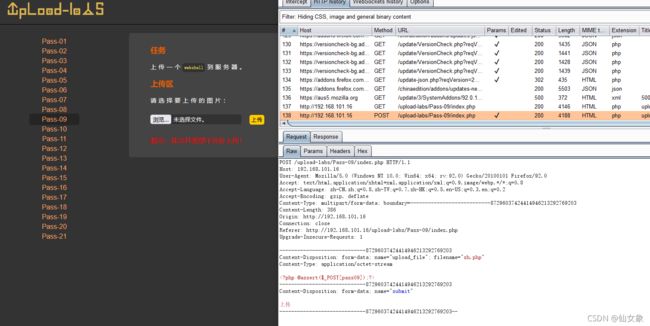
上传sh.php失败,burp中将抓到的包send to repeater
修改filename为sh.xxx发现可以上传成功,说明是黑名单过滤
将报文send to intruder,按照Pass-03的套路爆破后缀名,爆破结果用../upload过滤,发现只有如下后缀的文件上传成功(说实话我的文件名后缀字典里面本来没有这关的解的,毕竟它稍微有点奇葩,后来对着代码缕了答案,把答案写到后缀字典里才有了下面的爆破结果……做upload-labs的一大收获可能就是后缀字典更充实了……所以其实emmm前面的好几关也可以用本关的方法)
可以作为webshell的是sh.php. .(windows系统),上传成功后据说文件名是sh.php. ,但实际上服务器上文件名就是sh.php
代码分析:
首先trim()删除文件名末尾的多个空格,然后deldot()删除文件名末尾的多个点,strrchr()以第一个.为界取出后缀,strtolower()将后缀转化为小写,str_ireplace()去掉后缀中的一个::$DATA,最后trim()删除后缀末尾的多个空格。处理完的后缀与黑名单对比,如果后缀不在黑名单中,则上传后的文件名是去掉文件名末尾的空格,再去掉文件名末尾的点之后的文件名。
按照这个顺序倒推,就可以发现后缀.php. .(点空格点)是可以绕过黑名单检查的。
if (isset($_POST['submit'])) {
if (file_exists(UPLOAD_PATH)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess",".ini");
$file_name = trim($_FILES['upload_file']['name']);
$file_name = deldot($file_name);//删除文件名末尾的点
$file_ext = strrchr($file_name, '.');
$file_ext = strtolower($file_ext); //转换为小写
$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA
$file_ext = trim($file_ext); //首尾去空
if (!in_array($file_ext, $deny_ext)) {
$temp_file = $_FILES['upload_file']['tmp_name'];
$img_path = UPLOAD_PATH.'/'.$file_name;
if (move_uploaded_file($temp_file, $img_path)) {
$is_upload = true;
} else {
$msg = '上传出错!';
}
} else {
$msg = '此文件类型不允许上传!';
}
} else {
$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';
}
}