- 《凤凰架构》C12-容器间网络
Epi_HHH
阅读笔记网络容器
一、Linux网络虚拟化1)干预网络通信——以NetFliter与iptable为例钩子是iptables在内核网络协议栈处理数据包时的“插入点”,也就是规则生效的具体时刻和位置。数据包经过网络栈,会在不同阶段被iptables规则检查。INPUT:处理进入本机的数据包OUTPUT:处理由本机发出的数据包FORWARD:处理经过本机转发的数据包PREROUTING:数据包进入路由决策前(常用来做D
- Node.js 中的 JWT 认证:从生成到验证的完整指南
盛夏绽放
node.js有问必答后端
文章目录Node.js中的JWT认证:从生成到验证的完整指南一、JWT是什么?为什么需要它?传统session与JWT对比二、JWT的结构解析三、Node.js中实现JWT1.安装jsonwebtoken包2.生成JWT3.验证JWT4.错误处理大全四、高级应用场景1.刷新令牌机制2.在不同路由中的验证中间件五、安全最佳实践六、常见问题解答七、完整示例代码结语主要内容包括:使用jsonwebtok
- ROS 避障技术介绍
Xian-HHappy
机器人-Robotros避障
ROS避障技术介绍一、ROS避障系统概述ROS(机器人操作系统)作为移动机器人开发的主流框架,其避障技术依托模块化设计,通过传感器数据融合、环境建模与运动规划实现动态障碍物规避。在物流机器人、服务机器人、自动驾驶等场景中,ROS避障系统需满足实时性、安全性与灵活性要求,核心流程包括环境感知-障碍建模-路径规划-运动控制四个环节。二、避障核心组件与原理1.传感器层:环境信息获取激光雷达(如Velod
- AlpineLinux安装部署MariaDB
山岚的运维笔记
Linux运维及使用mariadb数据库
简单来说,MariaDB被视为MySQL的一个社区驱动的分支,它保留了MySQL的许多特性和功能,同时引入了一些新的特性和改进。许多用户和组织选择使用MariaDB,因为它提供了更多的自由度和对未来许可证变更的保护。而对于一些需要特定Oracle支持或特定MySQL功能的用例,依然使用MySQL是首选。这里不对两者间的差异做任何介绍,仅介绍如何在AlpineLinux下安装MariaDB。在Alp
- `docker-compose` 安装 Neo4j 的详细步骤
MonkeyKing.sun
dockerneo4j容器
docker-compose安装Neo4j的详细步骤,适用于本地开发或测试环境(适配Neo4j5.x或4.x版本):一、准备环境1.安装Docker和DockerCompose如果尚未安装,请根据系统安装:Linux/macOS推荐安装DockerDesktop(已集成DockerCompose)Windows安装DockerDesktop验证安装:docker-vdocker-compose-v
- Ubuntu下安装Moodle平台
swy520
ubuntuMoodleubuntuMoodle
一前言Moodle是一个开源课程管理系统(CMS),也被称为学习管理系统(LMS)或虚拟学习环境(VLE),它通常用来播放符合SCORM标准的课件,但功能远不止课程管理,作业模块等功能。这里主要介绍moodle的安装方法。二安装准备Moodle通常在Linux操作系统上,基于Apache,PostgreSQL/MySQL/MariaDB和PHP进行开发。为了平台的稳定性,我们选择Linux操作系统
- linux安装elasticsearch-head(快速,详细)
Dyansts
linuxelasticsearch运维npmcentos
前提见此文章https://blog.csdn.net/rj2012001/article/details/121816878?spm=1001.2014.3001.55011.下载zip格式在elasticsearch文件夹wgethttps://codeload.github.com/mobz/elasticsearch-head/zip/refs/heads/master2.解压zip文件u
- 如何在linux系统重启或启动时执行命令或脚本
jghhh01
linux运维服务器
在Linux系统中,有多种方法可以在系统启动或重启时执行命令或脚本。以下是一些常见的方法:使用crontab:Crontab是一个用于设置周期性被执行的任务的工具。在crontab中,有一个特殊的时间字符串@reboot,它可以用来设置在系统启动时运行的任务。例如,如果你想在每次系统启动时运行/home/user/myscript.sh,你可以在crontab文件中添加以下行:@reboot/ho
- vmvare如何给centos7 设置静态IP地址
Roc-xb
服务器tcp/ipphp服务器
本章教程,主要介绍如何在vmvare中如何给虚拟机中设置静态IP地址。本章教程中使用的linux发行版是centos7。目前没有静态IP地址,并且不能联网,此时我们需要给它配置一个静态IP,并且可以实现联网功能。一、前置步骤1、网络设置2、添加网络添加一个虚拟机网络,选择VMnet8,如果被占用了,可以选择其他的名字。3、选择NAT模式
- 设计与实现淘客返利APP的数据安全与隐私保护:架构师的实践经验
设计与实现淘客返利APP的数据安全与隐私保护:架构师的实践经验大家好,我是阿可,微赚淘客系统及省赚客APP创始人,是个冬天不穿秋裤,天冷也要风度的程序猿!数据安全与隐私保护的重要性在淘客返利APP中,数据安全与隐私保护是至关重要的。用户数据不仅涉及个人隐私,还可能包含敏感信息,如身份证号、银行卡号等。一旦数据泄露,不仅会损害用户利益,还会对平台的声誉造成严重影响。因此,设计和实现一个安全可靠的数据
- centos 7+hadoop 2.7.3
mozhw
c/c++linu/unixjava
安装JDK版本:jdk-8u131-linux-x64.tar.gz需要先删除系统自带的openjdk先查找java再移除[hadoop@localhost~]$rpm-qa|grepjavajava-1.7.0-openjdk-1.7.0.111-2.6.7.8.el7.x86_64python-javapackages-3.4.1-11.el7.noarchtzdata-java-2016g-
- Linux学习笔记:PCIe内核篇(1):初始化与枚举流程
ZH_2025
嵌入式协议篇PCIE
根据system.map查看内核中PCIe加载流程:root@zh-vm:~#cat/boot/System.map-5.15.0-130-generic|greppci|grepinitcallffffffff8350ff68d__initcall__kmod_pci__453_6907_pci_realloc_setup_params0ffffffff83510098d__initcall__
- C2远控篇&Golang&Rust&冷门语言&Loader加载器&对抗优势&减少熵值特征
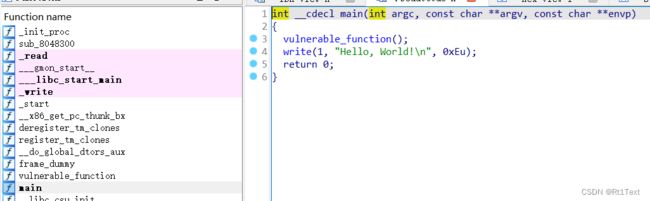
#C2远控-ShellCode-认知&环境1.创建工程时关闭SDL检查2.属性->C/C++->代码生成->运行库->多线程(/MT)如果是debug则设置成MTD3.属性->C/C++->代码生成->禁用安全检查GS4.关闭生成清单属性->链接器->清单文件->生成清单选择否#C2远控-ShellCode-分析&提取ShellCode的本质其实就是一段可以自主运行的代码。它没有任何文件结构,它不
- 鸿蒙(HarmonyOS)应用开发实战——自定义安全键盘案例
CTrup
HarmonyOS移动开发鸿蒙开发harmonyos安全音视频移动开发鸿蒙开发组件化
往期知识点整理鸿蒙(HarmonyOS)北向开发知识点记录~被裁员后,踏上了鸿蒙开发求职之路持续更新中……介绍金融类应用在密码输入时,一般会使用自定义安全键盘。本示例介绍如何使用TextInput组件实现自定义安全键盘场景,主要包括TextInput.customKeyboard绑定自定义键盘、自定义键盘布局和状态更新等知识点。效果图预览实现思路1.使用TextInput的customKeyboa
- Linux运维需要学多久?学习方式有哪些?
老男孩IT教育
linux运维
Linux运维工程师是一个融合多学科的综合性技术岗位,除了掌握相关技术之外,还需要具备沟通、销售、管理等非技术能力,因此也给运维工程师提供了非常广阔的发展空间。那么Linux运维工程师要学多久?以下是详细的内容介绍。Linux运维工程师要学多久?Linux运维工程师学习周期需结合学习方式来决定,不同的学习方式,周期是不同的。现在学习Linux运维技术分为两种情况。一种是自学,如果选择自学的话,学习
- linux学习第五周
运维小杨
linux学习运维
目录1、总结rocky系统的启动流程,grub工作流程1.1系统启动整体流程(基于BIOS/UEFI)1.2硬件初始化阶段1.2.1BIOS(传统模式)1.2.2UEFI(新模式)1.3引导加载程序(GRUB2)阶段1.4内核加载与初始化阶段1.5用户空间初始化(systemd阶段)2、总结内核设计流派及特点。3、总结systemd服务配置文件4、总结DNS域名三级结构,DNS服务工作原理,涉及递
- 第二十五节:Linux 运维职业规划与学习路径指南
厚衣服_3
Linux基本操作详解运维linux学习
第二十五节:Linux运维职业规划与学习路径指南随着云计算、容器化、自动化运维的快速发展,Linux运维工程师已经成为技术岗位中的重要角色之一。要想在运维领域长期发展,不仅要掌握扎实的基础技能,更要有清晰的职业规划和学习路径。一、Linux运维职业方向概览职业方向技术关键词基础运维工程师Linux、Shell、网络、服务部署、安全配置自动化运维/DevOpsAnsible、Docker、Jenki
- Linux运维学习路线
沉默的八哥
Linux运维linux学习
以下是一个Linux运维详细学习路线:一、Linux基础入门(第1-2个月)操作系统安装与基本概念学习Linux系统的安装,包括常见发行版(如Ubuntu、CentOS、Debian等)的选择。了解安装过程中的分区设置(如根分区、交换分区)、文件系统类型(如ext4、xfs)的选择及其对系统性能的影响。熟悉Linux的基本概念,如内核、shell、文件系统层次结构(FHS)标准。掌握文件系统的目录
- ZLG嵌入式笔记 | rootfs镜像制作其实没那么难
ZLG 致远电子
边缘计算ZLG嵌入式开发应用笔记个人开发物联网
在嵌入式Linux开发中,文件系统的打包和镜像制作是关键步骤。本文介绍了Linux核心板文件系统的打包与镜像制作方法,适合嵌入式开发人员快速上手。 前言致远电子Linux核心板提供的系统固件里,除了镜像文件之外,通常还会提供文件系统压缩包。镜像文件可以直接用于烧写到目标板,而文件系统压缩包则可以进行部分修改,修改后重新制作镜像文件烧写。这里只讲直接用编译好的二进制文件对文件系
- Linux程序设计:什么时候选择开发内核模块?
mzhan017
kernel笔记linux网络设计
最近看一个CPU使用率高的问题,从perf里看,是下面的一个占用的比较多是下面一个OverheadSource:LineSymbolSharedObject-8.48%[vdso][1129]0x1129B[.]0x0000000000001129
- 在新设备上部署Git:完整教程与常见问题分析
马里马里奥-
gitgit容易见的一些问题
在现代软件开发中,Git是必不可少的版本控制工具。无论是个人项目还是团队协作,在新设备上快速部署Git都能提高效率。本博客将提供一份结构清晰的教程,指导你如何在新设备上完成Git部署,并分析部署过程中可能遇到的常见问题。教程基于标准实践,适用于Windows、macOS和Linux系统。让我们一步步来!1.引言Git是一个分布式版本控制系统,用于跟踪代码变更、协作开发。在新设备上部署Git包括安装
- 借助 Wisdom SSH,实现 Linux 用户组与权限的精细化智能管控
qinyia
sshlinux人工智能服务器运维运维开发后端
WisdomSSH(官网ssh.wisdomheart.cn)凭借AI助手,为Linux用户组与权限管理带来智能便捷体验。用户组智能管理按需创建:如输入“为projectX项目建组,含开发、测试、运维人员”,AI助手创“projectX_group”组,生成groupaddprojectX_group命令。权限调整:输入“调projectX_group对代码目录读写,测试报告目录读权限”,AI助手
- EasyFeature软件特性四:星云空天大模型
智绘中勘
人工智能深度学习信息可视化
随着智能遥感进入新纪元,数据处理与模型效率的挑战日益成为应用落地的关键瓶颈。EasyFeature软件以星云空天大模型为核心,构建了基于人机智能提示学习的多模态系统。通过海量高质量数据预训练,集成了包括遥感场景分类、快速目标检测、地物分类、变化检测等在内的丰富模型库,提供端到端的智能解译能力。EasyFeature完全实现国产化自主可控,涵盖全栈软硬件支撑与训推一体化流程,确保高效安全。其极简安装
- 八股文——JAVA基础:字符串拼接用“+” 还是 StringBuilder?
Hellyc
八股文自用java开发语言
java中仅有两个操作符的重载就是用于字符串的拼接操作的:+与+=操作符+底层使用的是StringBuilder来进行实现的,+用于拼接的缺陷在于使用StringBuilder,本身线程不安全,其次在循环中使用+来拼接,会导致重复创建StringBuilder对象,导致空间的浪费。而在循环中使用StringBuilder就不会出现这个问题。
- String字符串与StringBuffer、StringBuilder的区别以及String的不可变性是什么
Hellyc
java开发语言
String字符串是八个基本数据类型之一,其底层实现是通过字符数组来进行实现的,也就是abc的字符数组与abc的字符串是完全相等的。StringBuilder与StringBuffer都继承相同的父类AbstractStringBuilder,这两个方法都提供了一些字符串的基本操作,比如append()使两个字符串进行相加。其中String与StringBuffer是线程安全的,StringBui
- 什么是对称加密和非对称加密
MonkeyKing.sun
网络服务器运维
对称加密和非对称加密是现代密码学中的两大核心技术体系,它们用于保护数据的机密性、完整性和安全性,是构建区块链、电子支付、SSL、VPN、数字签名等系统的基础。一、什么是对称加密(SymmetricEncryption)?定义:加密和解密使用同一把密钥,称为“对称密钥”。工作原理:明文+密钥→加密算法→密文密文+同样密钥→解密算法→明文示例算法:算法简要说明AES(高级加密标准)最常用、快速、安全D
- Python爬虫实战:研究MarkupSafe库相关技术
ylfhpy
爬虫项目实战python爬虫开发语言MarkupSafe
1.引言1.1研究背景与意义随着互联网数据量的爆炸式增长,网页内容自动提取与分析技术在信息检索、舆情监控、数据挖掘等领域的需求日益凸显。网络爬虫作为获取网页内容的核心工具,能够自动化采集互联网信息。然而,直接渲染爬取的网页内容存在安全隐患,特别是跨站脚本攻击(XSS)风险。攻击者可能通过注入恶意脚本窃取用户信息或破坏网站功能。MarkupSafe作为Python的安全字符串处理库,能够有效处理不可
- Python爬虫实战:研究sanitize库相关技术
ylfhpy
爬虫项目实战python爬虫网络开发语言安全sanitize
1.引言1.1研究背景与意义在当今数字化时代,互联网已成为人们获取信息、交流互动的重要平台。随着Web2.0技术的发展,用户生成内容(UGC)、社交媒体嵌入、第三方插件等功能极大丰富了网页的内容和交互性,但也带来了严峻的安全挑战。根据Web应用安全联盟(WAS)的统计数据,2025年全球范围内因网页安全漏洞导致的数据泄露事件超过15万起,造成的经济损失高达250亿美元。其中,跨站脚本攻击(XSS)
- python网络安全实战_基于Python网络爬虫实战
weixin_39907850
python网络安全实战
文件的操作:一般都要使用os模块和os.path模块importos.pathos.path.exists('D:\\Python\\1.txt')#判断文件是否存在abspath(path)#返回path所在的绝对路径dirname(p)#返回目录的路径exists(path)#判断文件是否存在getatime(filename)#返回文件的最后访问时间getctime(filename)#返回
- 零信任架构——重构企业安全边界的新范式
月_o9
网络安全
零信任架构——重构企业安全边界的新范式(字数:998)传统边界的崩塌与信任危机防火墙与VPN构筑的“城堡护城河”模型在云原生与远程办公时代彻底瓦解。当数据散布于公有云、边缘设备与SaaS平台,当供应链攻击可穿透层层防护,“内部可信”的假设已成为最大安全漏洞。零信任(ZeroTrust)的核心哲学正是:永不信任,持续验证(NeverTrust,AlwaysVerify)。它并非单一技术,而是以身份为
- TOMCAT在POST方法提交参数丢失问题
357029540
javatomcatjsp
摘自http://my.oschina.net/luckyi/blog/213209
昨天在解决一个BUG时发现一个奇怪的问题,一个AJAX提交数据在之前都是木有问题的,突然提交出错影响其他处理流程。
检查时发现页面处理数据较多,起初以为是提交顺序不正确修改后发现不是由此问题引起。于是删除掉一部分数据进行提交,较少数据能够提交成功。
恢复较多数据后跟踪提交FORM DATA ,发现数
- 在MyEclipse中增加JSP模板 删除-2008-08-18
ljy325
jspxmlMyEclipse
在D:\Program Files\MyEclipse 6.0\myeclipse\eclipse\plugins\com.genuitec.eclipse.wizards_6.0.1.zmyeclipse601200710\templates\jsp 目录下找到Jsp.vtl,复制一份,重命名为jsp2.vtl,然后把里面的内容修改为自己想要的格式,保存。
然后在 D:\Progr
- JavaScript常用验证脚本总结
eksliang
JavaScriptjavaScript表单验证
转载请出自出处:http://eksliang.iteye.com/blog/2098985
下面这些验证脚本,是我在这几年开发中的总结,今天把他放出来,也算是一种分享吧,现在在我的项目中也在用!包括日期验证、比较,非空验证、身份证验证、数值验证、Email验证、电话验证等等...!
&nb
- 微软BI(4)
18289753290
微软BI SSIS
1)
Q:查看ssis里面某个控件输出的结果:
A MessageBox.Show(Dts.Variables["v_lastTimestamp"].Value.ToString());
这是我们在包里面定义的变量
2):在关联目的端表的时候如果是一对多的关系,一定要选择唯一的那个键作为关联字段。
3)
Q:ssis里面如果将多个数据源的数据插入目的端一
- 定时对大数据量的表进行分表对数据备份
酷的飞上天空
大数据量
工作中遇到数据库中一个表的数据量比较大,属于日志表。正常情况下是不会有查询操作的,但如果不进行分表数据太多,执行一条简单sql语句要等好几分钟。。
分表工具:linux的shell + mysql自身提供的管理命令
原理:使用一个和原表数据结构一样的表,替换原表。
linux shell内容如下:
=======================开始
- 本质的描述与因材施教
永夜-极光
感想随笔
不管碰到什么事,我都下意识的想去探索本质,找寻一个最形象的描述方式。
我坚信,世界上对一件事物的描述和解释,肯定有一种最形象,最贴近本质,最容易让人理解
&
- 很迷茫。。。
随便小屋
随笔
小弟我今年研一,也是从事的咱们现在最流行的专业(计算机)。本科三流学校,为了能有个更好的跳板,进入了考研大军,非常有幸能进入研究生的行业(具体学校就不说了,怕把学校的名誉给损了)。
先说一下自身的条件,本科专业软件工程。主要学习就是软件开发,几乎和计算机没有什么区别。因为学校本身三流,也就是让老师带着学生学点东西,然后让学生毕业就行了。对专业性的东西了解的非常浅。就那学的语言来说
- 23种设计模式的意图和适用范围
aijuans
设计模式
Factory Method 意图 定义一个用于创建对象的接口,让子类决定实例化哪一个类。Factory Method 使一个类的实例化延迟到其子类。 适用性 当一个类不知道它所必须创建的对象的类的时候。 当一个类希望由它的子类来指定它所创建的对象的时候。 当类将创建对象的职责委托给多个帮助子类中的某一个,并且你希望将哪一个帮助子类是代理者这一信息局部化的时候。
Abstr
- Java中的synchronized和volatile
aoyouzi
javavolatilesynchronized
说到Java的线程同步问题肯定要说到两个关键字synchronized和volatile。说到这两个关键字,又要说道JVM的内存模型。JVM里内存分为main memory和working memory。 Main memory是所有线程共享的,working memory则是线程的工作内存,它保存有部分main memory变量的拷贝,对这些变量的更新直接发生在working memo
- js数组的操作和this关键字
百合不是茶
js数组操作this关键字
js数组的操作;
一:数组的创建:
1、数组的创建
var array = new Array(); //创建一个数组
var array = new Array([size]); //创建一个数组并指定长度,注意不是上限,是长度
var arrayObj = new Array([element0[, element1[, ...[, elementN]]]
- 别人的阿里面试感悟
bijian1013
面试分享工作感悟阿里面试
原文如下:http://greemranqq.iteye.com/blog/2007170
一直做企业系统,虽然也自己一直学习技术,但是感觉还是有所欠缺,准备花几个月的时间,把互联网的东西,以及一些基础更加的深入透析,结果这次比较意外,有点突然,下面分享一下感受吧!
&nb
- 淘宝的测试框架Itest
Bill_chen
springmaven框架单元测试JUnit
Itest测试框架是TaoBao测试部门开发的一套单元测试框架,以Junit4为核心,
集合DbUnit、Unitils等主流测试框架,应该算是比较好用的了。
近期项目中用了下,有关itest的具体使用如下:
1.在Maven中引入itest框架:
<dependency>
<groupId>com.taobao.test</groupId&g
- 【Java多线程二】多路条件解决生产者消费者问题
bit1129
java多线程
package com.tom;
import java.util.LinkedList;
import java.util.Queue;
import java.util.concurrent.ThreadLocalRandom;
import java.util.concurrent.locks.Condition;
import java.util.concurrent.loc
- 汉字转拼音pinyin4j
白糖_
pinyin4j
以前在项目中遇到汉字转拼音的情况,于是在网上找到了pinyin4j这个工具包,非常有用,别的不说了,直接下代码:
import java.util.HashSet;
import java.util.Set;
import net.sourceforge.pinyin4j.PinyinHelper;
import net.sourceforge.pinyin
- org.hibernate.TransactionException: JDBC begin failed解决方案
bozch
ssh数据库异常DBCP
org.hibernate.TransactionException: JDBC begin failed: at org.hibernate.transaction.JDBCTransaction.begin(JDBCTransaction.java:68) at org.hibernate.impl.SessionImp
- java-并查集(Disjoint-set)-将多个集合合并成没有交集的集合
bylijinnan
java
import java.util.ArrayList;
import java.util.Arrays;
import java.util.HashMap;
import java.util.HashSet;
import java.util.Iterator;
import java.util.List;
import java.util.Map;
import java.ut
- Java PrintWriter打印乱码
chenbowen00
java
一个小程序读写文件,发现PrintWriter输出后文件存在乱码,解决办法主要统一输入输出流编码格式。
读文件:
BufferedReader
从字符输入流中读取文本,缓冲各个字符,从而提供字符、数组和行的高效读取。
可以指定缓冲区的大小,或者可使用默认的大小。大多数情况下,默认值就足够大了。
通常,Reader 所作的每个读取请求都会导致对基础字符或字节流进行相应的读取请求。因
- [天气与气候]极端气候环境
comsci
环境
如果空间环境出现异变...外星文明并未出现,而只是用某种气象武器对地球的气候系统进行攻击,并挑唆地球国家间的战争,经过一段时间的准备...最大限度的削弱地球文明的整体力量,然后再进行入侵......
那么地球上的国家应该做什么样的防备工作呢?
&n
- oracle order by与union一起使用的用法
daizj
UNIONoracleorder by
当使用union操作时,排序语句必须放在最后面才正确,如下:
只能在union的最后一个子查询中使用order by,而这个order by是针对整个unioning后的结果集的。So:
如果unoin的几个子查询列名不同,如
Sql代码
select supplier_id, supplier_name
from suppliers
UNI
- zeus持久层读写分离单元测试
deng520159
单元测试
本文是zeus读写分离单元测试,距离分库分表,只有一步了.上代码:
1.ZeusMasterSlaveTest.java
package com.dengliang.zeus.webdemo.test;
import java.util.ArrayList;
import java.util.List;
import org.junit.Assert;
import org.j
- Yii 截取字符串(UTF-8) 使用组件
dcj3sjt126com
yii
1.将Helper.php放进protected\components文件夹下。
2.调用方法:
Helper::truncate_utf8_string($content,20,false); //不显示省略号 Helper::truncate_utf8_string($content,20); //显示省略号
&n
- 安装memcache及php扩展
dcj3sjt126com
PHP
安装memcache tar zxvf memcache-2.2.5.tgz cd memcache-2.2.5/ /usr/local/php/bin/phpize (?) ./configure --with-php-confi
- JsonObject 处理日期
feifeilinlin521
javajsonJsonOjbectJsonArrayJSONException
写这边文章的初衷就是遇到了json在转换日期格式出现了异常 net.sf.json.JSONException: java.lang.reflect.InvocationTargetException 原因是当你用Map接收数据库返回了java.sql.Date 日期的数据进行json转换出的问题话不多说 直接上代码
&n
- Ehcache(06)——监听器
234390216
监听器listenerehcache
监听器
Ehcache中监听器有两种,监听CacheManager的CacheManagerEventListener和监听Cache的CacheEventListener。在Ehcache中,Listener是通过对应的监听器工厂来生产和发生作用的。下面我们将来介绍一下这两种类型的监听器。
- activiti 自带设计器中chrome 34版本不能打开bug的解决
jackyrong
Activiti
在acitivti modeler中,如果是chrome 34,则不能打开该设计器,其他浏览器可以,
经证实为bug,参考
http://forums.activiti.org/content/activiti-modeler-doesnt-work-chrome-v34
修改为,找到
oryx.debug.js
在最头部增加
if (!Document.
- 微信收货地址共享接口-终极解决
laotu5i0
微信开发
最近要接入微信的收货地址共享接口,总是不成功,折腾了好几天,实在没办法网上搜到的帖子也是骂声一片。我把我碰到并解决问题的过程分享出来,希望能给微信的接口文档起到一个辅助作用,让后面进来的开发者能快速的接入,而不需要像我们一样苦逼的浪费好几天,甚至一周的青春。各种羞辱、谩骂的话就不说了,本人还算文明。
如果你能搜到本贴,说明你已经碰到了各种 ed
- 关于人才
netkiller.github.com
工作面试招聘netkiller人才
关于人才
每个月我都会接到许多猎头的电话,有些猎头比较专业,但绝大多数在我看来与猎头二字还是有很大差距的。 与猎头接触多了,自然也了解了他们的工作,包括操作手法,总体上国内的猎头行业还处在初级阶段。
总结就是“盲目推荐,以量取胜”。
目前现状
许多从事人力资源工作的人,根本不懂得怎么找人才。处在人才找不到企业,企业找不到人才的尴尬处境。
企业招聘,通常是需要用人的部门提出招聘条件,由人
- 搭建 CentOS 6 服务器 - 目录
rensanning
centos
(1) 安装CentOS
ISO(desktop/minimal)、Cloud(AWS/阿里云)、Virtualization(VMWare、VirtualBox)
详细内容
(2) Linux常用命令
cd、ls、rm、chmod......
详细内容
(3) 初始环境设置
用户管理、网络设置、安全设置......
详细内容
(4) 常驻服务Daemon
- 【求助】mongoDB无法更新主键
toknowme
mongodb
Query query = new Query(); query.addCriteria(new Criteria("_id").is(o.getId())); &n
- jquery 页面滚动到底部自动加载插件集合
xp9802
jquery
很多社交网站都使用无限滚动的翻页技术来提高用户体验,当你页面滑到列表底部时候无需点击就自动加载更多的内容。下面为你推荐 10 个 jQuery 的无限滚动的插件:
1. jQuery ScrollPagination
jQuery ScrollPagination plugin 是一个 jQuery 实现的支持无限滚动加载数据的插件。
2. jQuery Screw
S