SpringCloud Day12---SpringCloud Alibaba Sentinel 服务熔断与限流
文章目录
- 15. SpringCloud Alibaba Sentinel实现熔断与限流
-
- 15.1 概述
-
- 15.1.1 官网
- 15.1.2 介绍
- 15.1.3 去哪下
- 15.1.4 能干嘛
- 15.1.5 怎么玩
- 15.2 安装Sentinel控制台
-
- 15.2.1 sentinel组件由2部分构成
- 15.2.2 安装步骤
- 15.3 初始化演示工程
-
- 15.3.1 前提条件
- 15.3.2 建立sentinel8041
- 15.3.3 测试结果
- 15.4 流控规则
-
- 15.4.1 基本介绍
- 15.4.2 流控模式
- 15.4.3 流控效果
- 15.5 降级规则
-
- 15.5.1 官网
- 15.5.2 基本介绍
- 15.5.3 降级策略实战
- 15.6 热点key限流
-
- 15.6.1 基本介绍
- 15.6.2 官网
- 15.6.3 承上启下复习start
- 15.6.4 修改Controller
- 15.6.5 配置
- 15.6.6 测试
- 15.6.7 参数例外项
- 15.6.8 其他---添加异常看看(后面详细介绍)
- 15.7 系统规则
-
- 15.7.1 是什么
- 15.7.2 各项配置参数说明
- 15.7.3 配置全局QPS
- 15.8 @SentinelResource
-
- 15.8.1 按资源名称限流+后续处理
- 15.8.2 按照Url地址限流+后续处理
- 15.8.3 上面兜底方案面临的问题
- 15.8.4 客户自定义限流处理逻辑
- 15.8.5 更多注解属性说明
- 15.9 服务熔断功能
-
- 15.9.1 sentinel整合+Ribbon+fallback
- 15.9.2 sentinel整合+Feign+fallback
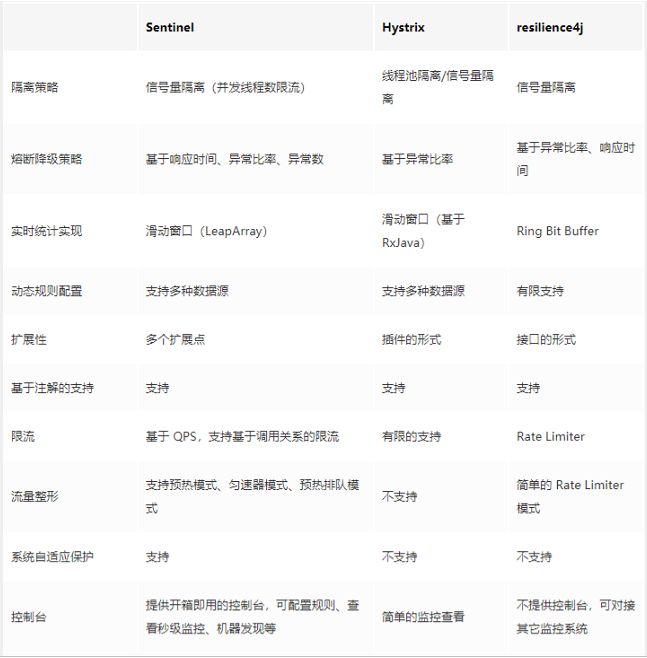
- 15.9.3 熔断框架比较
- 15.10 规则持久化
-
- 15.10.1 是什么
- 15.10.2 怎么玩
- 15.10.3 实现步骤
- 15.10.4 测试
15. SpringCloud Alibaba Sentinel实现熔断与限流
15.1 概述
15.1.1 官网
英文: https://github.com/alibaba/Sentinel
中文: https://github.com/alibaba/Sentinel/wiki/%E4%BB%8B%E7%BB%8D
15.1.2 介绍
一句话解释,之前我们讲解过的Hystrix
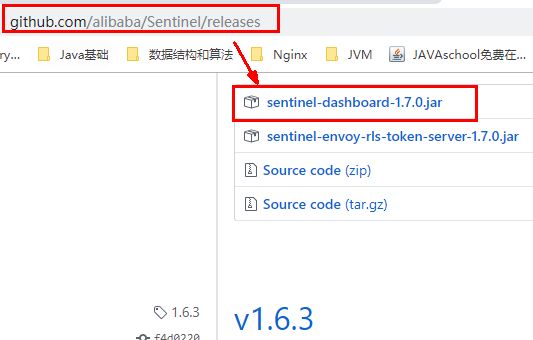
15.1.3 去哪下
https://github.com/alibaba/Sentinel/releases
15.1.4 能干嘛
15.1.5 怎么玩
官网:https://spring-cloud-alibaba-group.github.io/github-pages/greenwich/spring-cloud-alibaba.html#_spring_cloud_alibaba_sentinel
服务使用中的各种问题:
- 服务雪崩
- 服务降级
- 服务熔断
- 服务限流
15.2 安装Sentinel控制台
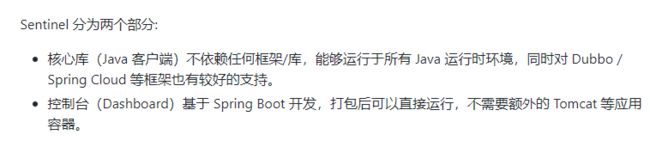
15.2.1 sentinel组件由2部分构成
15.2.2 安装步骤
1.下载
https://github.com/alibaba/Sentinel/releases
2.运行命令
前提:
-
java8环境OK
-
8080端口不能被占用,sentinel内部有Tomcat…
启动:
java -jar sentinel-dashboard-1.7.0.jar
如果端口被占用可以: java -Dserver.port=8888 -jar sentinel-dashboard-1.7.0.jar
3.访问sentinel管理界面
访问: http://localhost:端口号 ,登录账号密码均为sentinel
15.3 初始化演示工程
15.3.1 前提条件
启动Nacos,访问http://192.168.174.128:8848/nacos/#/login 访问成功
15.3.2 建立sentinel8041
- 建Module—cloudalibaba-sentinel-service8401
- POM
<dependencies>
<dependency>
<groupId>com.alibaba.cloudgroupId>
<artifactId>spring-cloud-starter-alibaba-nacos-discoveryartifactId>
dependency>
<dependency>
<groupId>com.alibaba.cspgroupId>
<artifactId>sentinel-datasource-nacosartifactId>
dependency>
<dependency>
<groupId>com.alibaba.cloudgroupId>
<artifactId>spring-cloud-starter-alibaba-sentinelartifactId>
dependency>
<dependency>
<groupId>org.springframework.cloudgroupId>
<artifactId>spring-cloud-starter-openfeignartifactId>
dependency>
<dependency>
<groupId>org.springframework.bootgroupId>
<artifactId>spring-boot-starter-webartifactId>
dependency>
<dependency>
<groupId>org.springframework.bootgroupId>
<artifactId>spring-boot-starter-actuatorartifactId>
dependency>
<dependency>
<groupId>org.springframework.bootgroupId>
<artifactId>spring-boot-devtoolsartifactId>
<scope>runtimescope>
<optional>trueoptional>
dependency>
<dependency>
<groupId>cn.hutoolgroupId>
<artifactId>hutool-allartifactId>
<version>4.6.3version>
dependency>
<dependency>
<groupId>org.projectlombokgroupId>
<artifactId>lombokartifactId>
<optional>trueoptional>
dependency>
<dependency>
<groupId>org.springframework.bootgroupId>
<artifactId>spring-boot-starter-testartifactId>
<scope>testscope>
dependency>
dependencies>
- YML
server:
port: 8401
spring:
application:
name: cloudalibaba-sentinel-service
cloud:
nacos:
discovery:
server-addr: 192.168.174.128:8848 #Nacos服务注册中心地址
sentinel:
transport:
dashboard: localhost:8080 #配置Sentinel dashboard地址
port: 8719 #默认8719端口,假如被占用会自动从8719开始依次+1扫描,直至找到未被占用的端口
management:
endpoints:
web:
exposure:
include: '*'
- 主启动
@EnableDiscoveryClient
@SpringBootApplication
public class MainApp8401
{
public static void main(String[] args) {
SpringApplication.run(MainApp8401.class, args);
}
}
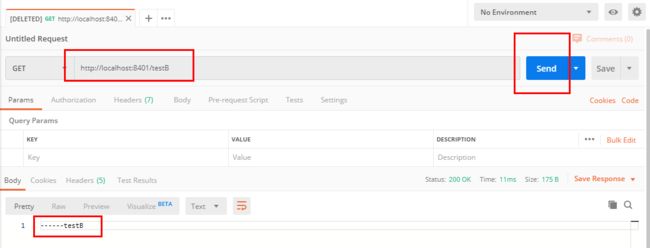
- 业务类FlowLimitController
@RestController
public class FlowLimitController
{
@GetMapping("/testA")
public String testA()
{
return "------testA";
}
@GetMapping("/testB")
public String testB()
{
return "------testB";
}
}
15.3.3 测试结果
- 启动Sentinel8888
- 启动微服务8401
- 启动8401微服务,查看sentienl控制台
空空如也,啥都没有
原因在于:Sentinel采用的懒加载
执行一次访问即可: 访问http://localhost:8401/testA 和http://localhost:8401/testB
结论:sentinel8080正在监控微服务8401
15.4 流控规则
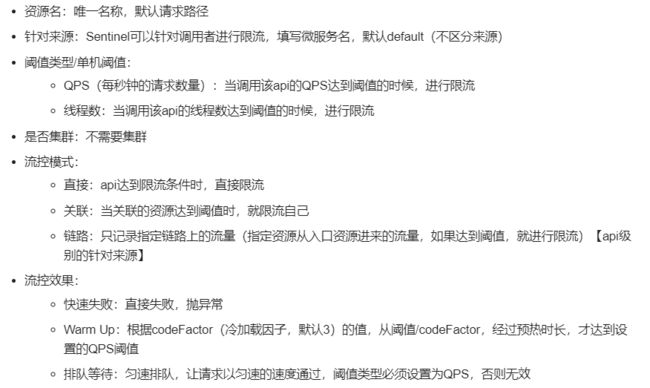
15.4.1 基本介绍
进一步说明
QPS和线程数的区别
QPS:御敌于国门之外,即一次只能有QPS个请求数.
线程数:进来之后关门打狗,一次只能有线程数个任务被处理,多余的不进行处理…
15.4.2 流控模式
1.直接(默认)
直接->快速失败
- 配置及说明:
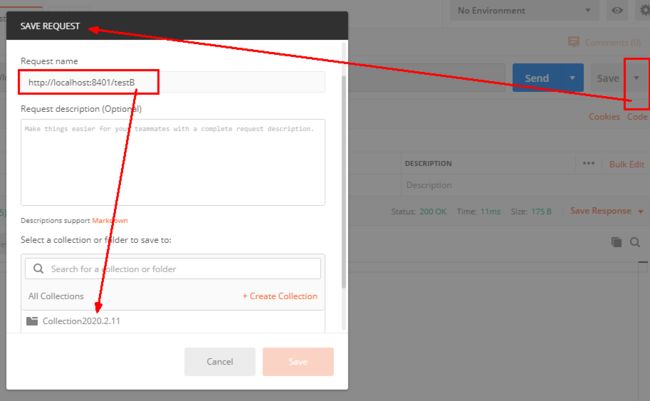
表示1秒钟内查询1次就是OK,若超过次数1,就直接-快速失败,报默认错误
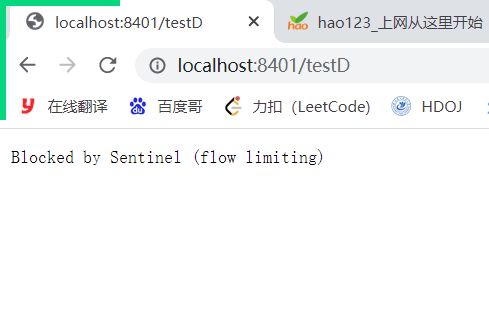
- 测试:
快速点击访问http://localhost:8401/testA
结果:Blocked by Sentinel (flow limiting)
- 思考
直接调用默认报错信息,技术方面OK。 but,是否应该有我们自己的后续处理?类似有个fallback的兜底方法?
2.关联
- 是什么
当关联的资源达到阈值时,就限流自己
当与A关联的资源B达到阀值后,就限流A自己
B惹事,A挂了,如:支付接口达到阈值限制下订单的接口
- 配置A
当关联资源/testB的qps阀值超过1时,就限流/testA的Rest访问地址,当关联资源到阈值后限制配置好的资源名
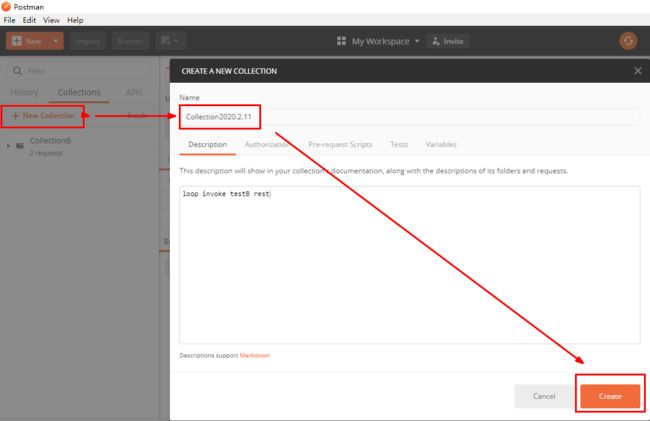
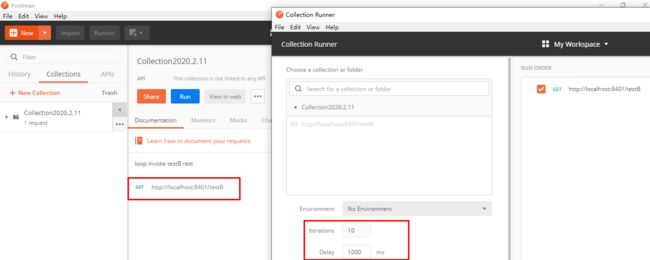
- postman模拟并发密集访问testB
正常访问testB成功
postman里新建多线程集合组
将访问地址添加进新新线程组
RUN
- 点击访问http://localhost:8401/testA ,进行测试
结果:由于大批量线程高并发访问B,发现testA挂了
3.链路.
多个请求调用了同一个微服务…
15.4.3 流控效果
1.直接->快速失败(默认的流控处理)
直接失败,抛出异常: Blocked by Sentinel (flow limiting)
源码:com.alibaba.csp.sentinel.slots.block.flow.controller.DefaultController
2.预热
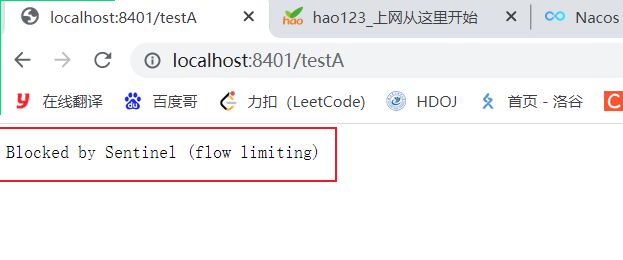
-
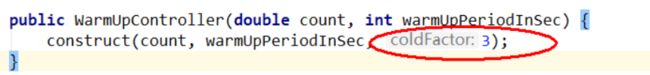
公式:阈值除以coldFactor(默认值为3),经过预热时长后才会达到阈值
-
官网:https://github.com/alibaba/Sentinel/wiki/%E6%B5%81%E9%87%8F%E6%8E%A7%E5%88%B6
默认coldFactor为3,即请求 QPS 从 threshold / 3 开始,经预热时长逐渐升至设定的 QPS 阈值。
限流 冷启动: https://github.com/alibaba/Sentinel/wiki/%E9%99%90%E6%B5%81—%E5%86%B7%E5%90%AF%E5%8A%A8
- 源码
com.alibaba.csp.sentinel.slots.block.flow.controller.WarmUpController
- WarmUp配置
默认 coldFactor(系统初始化的阀值) 为 3,即请求QPS从(threshold / 3) 开始,经多少预热时长才逐渐升至设定的 QPS 阈值。
案例,阀值为10,预热时长设置5秒。
系统初始化的阀值为10 / 3 约等于3,即阀值刚开始为3;然后过了5秒后阀值才慢慢升高恢复到10
- 测试
访问:多次点击http://localhost:8401/testB, 刚开始不行,后续慢慢OK
- 应用场景
如:秒杀系统在开启的瞬间,会有很多流量上来,很有可能把系统打死,预热方式就是把为了保护系统,可慢慢的把流量放进来,慢慢的把阀值增长到设置的阀值。
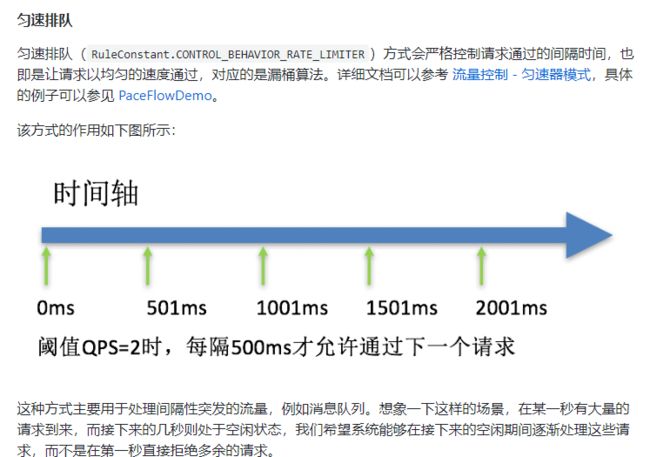
3.排队等待
- 匀速排队,让请求以均匀的速度通过,阀值类型必须设成QPS,否则无效。
设置含义:/testA每秒1次请求,超过的话就排队等待,等待的超时时间为20000毫秒
- 官网:
https://github.com/alibaba/Sentinel/wiki/%E6%B5%81%E9%87%8F%E6%8E%A7%E5%88%B6
- 源码
com.alibaba.csp.sentinel.slots.block.flow.controller.RateLimiterController
- 测试
在后台打印日志,可以看到1s请求被执行一次.
15.5 降级规则
15.5.1 官网
https://github.com/alibaba/Sentinel/wiki/%E7%86%94%E6%96%AD%E9%99%8D%E7%BA%A7
15.5.2 基本介绍
RT(平均响应时间,秒级)
平均响应时间 超出阈值 且 在时间窗口内通过的请求>=5,两个条件同时满足后触发降级
窗口期过后关闭断路器
RT最大4900(更大的需要通过-Dcsp.sentinel.statistic.max.rt=XXXX才能生效)
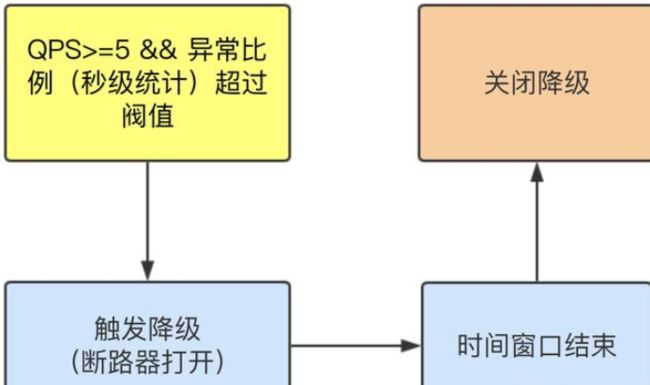
异常比列(秒级)
QPS >= 5 且异常比例(秒级统计)超过阈值时,触发降级;时间窗口结束后,关闭降级
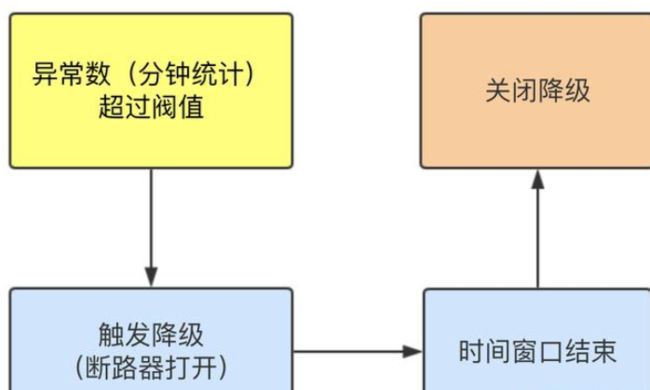
异常数(分钟级)
异常数(分钟统计)超过阈值时,触发降级;时间窗口结束后,关闭降级
- 进一步说明
Sentinel 熔断降级会在调用链路中某个资源出现不稳定状态时(例如调用超时或异常比例升高),对这个资源的调用进行限制,让请求快速失败,避免影响到其它的资源而导致级联错误。
当资源被降级后,在接下来的降级时间窗口之内,对该资源的调用都自动熔断(默认行为是抛出 DegradeException)。
- Sentinel的断路器是没有半开状态的
半开的状态系统自动去检测是否请求有异常,没有异常就关闭断路器恢复使用,有异常则继续打开断路器不可用。具体可以参考Hystrix
15.5.3 降级策略实战
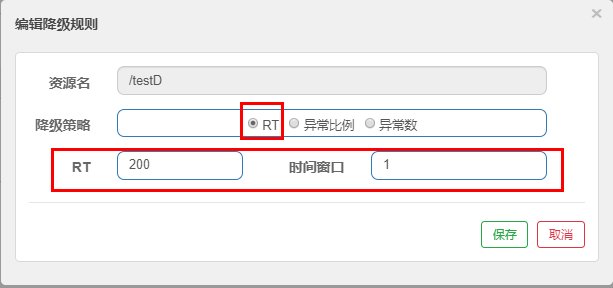
1.RT
- 是什么?
- 测试
Controller代码添加
@GetMapping("/testD")
public String testD()
{
//暂停几秒钟线程
try { TimeUnit.SECONDS.sleep(1); } catch (InterruptedException e) { e.printStackTrace(); }
log.info("testD 测试RT");
return "------testD";
}
配置
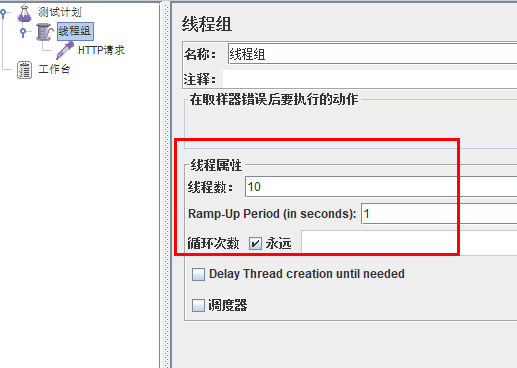
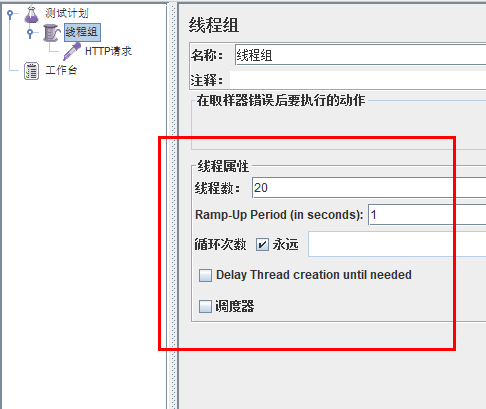
jmeter压测
访问testD
结论:
按照上述配置,永远一秒钟打进来10个线程(大于5个了)调用testD,我们希望200毫秒处理完本次任务,
如果超过200毫秒还没处理完,在未来1秒钟的时间窗口内,断路器打开(保险丝跳闸)微服务不可用,保险丝跳闸断电了. 后续我停止jmeter,没有这么大的访问量了,断路器关闭(保险丝恢复),微服务恢复OK
2.异常比例
- 是什么
- 测试
代码修改:
@GetMapping("/testD")
public String testD()
{
log.info("testD 测试RT");
int age = 10/0;
return "------testD";
}
配置
jmeter
结论:
按照上述配置,单独访问一次,必然来一次报错一次(int age = 10/0),调一次错一次;
开启jmeter后,直接高并发发送请求,多次调用达到我们的配置条件了。断路器开启(保险丝跳闸),微服务不可用了,不再报错error而是进行服务降级了。
3.异常数
- 是什么
时间窗口一定要大于等于60秒。
- 测试
代码:
@GetMapping("/testE")
public String testE()
{
log.info("testE 测试异常比例");
int age = 10/0;
return "------testE 测试异常比例";
}
配置:
![]()
结论:
访问: http://localhost:8401/testE,第一次访问绝对报错,因为除数不能为零,
我们看到error窗口,但是达到5次报错后,进入熔断后降级。
15.6 热点key限流
15.6.1 基本介绍
何为热点
热点即经常访问的数据,很多时候我们希望统计或者限制某个热点数据中访问频次最高的TopN数据,并对其访问进行限流或者其它操作
15.6.2 官网
https://github.com/alibaba/Sentinel/wiki/%E7%83%AD%E7%82%B9%E5%8F%82%E6%95%B0%E9%99%90%E6%B5%81
15.6.3 承上启下复习start
兜底方法分为系统默认和客户自定义两种
-
之前的case,限流出问题后,都是用sentinel系统默认的提示:Blocked by Sentinel (flow limiting)
-
我们能不能自定?类似hystrix,某个方法出问题了,就找对应的兜底降级方法?
结论: 从HystrixCommand 到@SentinelResource
15.6.4 修改Controller
@GetMapping("/testHotKey")
@SentinelResource(value = "testHotKey",blockHandler = "dealHandler_testHotKey")
public String testHotKey(@RequestParam(value = "p1",required = false) String p1,
@RequestParam(value = "p2",required = false) String p2){
return "------testHotKey";
}
public String dealHandler_testHotKey(String p1,String p2,BlockException exception)
{
return "-----dealHandler_testHotKey";
}
sentinel系统默认的提示:Blocked by Sentinel (flow limiting).
底层源码:com.alibaba.csp.sentinel.slots.block.BlockException
15.6.5 配置
限流模式只支持QPS模式,固定写死了。(这才叫热点)
@SentinelResource注解的方法参数索引,0代表第一个参数,1代表第二个参数,以此类推
单机阀值以及统计窗口时长表示在此窗口时间超过阀值就限流。
上面的抓图就是第一个参数有值的话,1秒的QPS为1,超过就限流,限流后调用dealHandler_testHotKey支持方法。
使用blockHandler前后对比:
- @SentinelResource(value = “testHotKey”): 异常打到了前台用户界面看到,不友好
- @SentinelResource(value = “testHotKey”,blockHandler = “dealHandler_testHotKey”),方法testHotKey里面第一个参数只要QPS超过每秒1次,马上降级处理.而且用了我们自己定义的,更加灵活.
15.6.6 测试
以下访问都是不停的进行访问
-
访问http://localhost:8401/testHotKey?p1=abc ===> error ×
-
访问http://localhost:8401/testHotKey?p1=abc&p2=33 ===> error ×
-
访问 http://localhost:8401/testHotKey?p2=abc ===> right √
结论:第一个参数p1,当QPS超过1秒1次点击后马上被限流.
15.6.7 参数例外项
1.上述案例演示了第一个参数p1,当QPS超过1秒1次点击后马上被限流
2.特例情况
普通 超过1秒钟一个后,达到阈值1后马上被限流
我们期望p1参数当它是某个特殊值时,它的限流值和平时不一样
假如当p1的值等于5时,它的阈值可以达到200
3.配置
点击添加按钮
4.测试
访问:http://localhost:8401/testHotKey?p1=5 ,无论方式是否超过1s一次,系统都未报错
访问:http://localhost:8401/testHotKey?p1=3 ,当方式超过1s一次,进行报错…
原因:当p1等于5的时候,阈值变为200.当p1不等于5的时候,阈值就是平常的1
5.前提条件
热点参数的注意点,参数必须是基本类型或者String
15.6.8 其他—添加异常看看(后面详细介绍)
@SentinelResource
处理的是Sentinel控制台配置的违规情况,有blockHandler方法配置的兜底处理;
RuntimeException
int age = 10/0,这个是java运行时报出的运行时异常RunTimeException,@SentinelResource不管
总结
@SentinelResource主管配置出错,运行出错该走异常走异常
15.7 系统规则
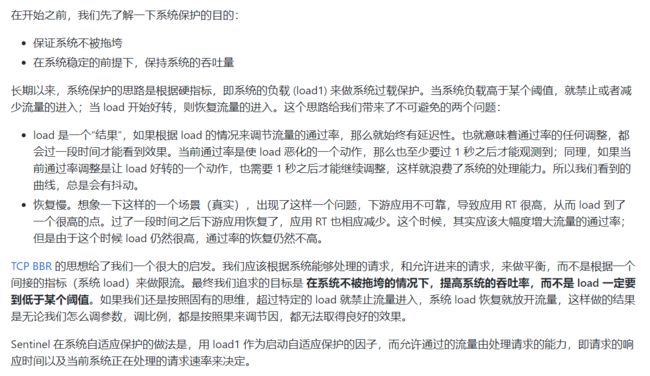
因为全局配置是对系统所有的请求生效的,所以本章使用的场景较少.
15.7.1 是什么
https://github.com/alibaba/Sentinel/wiki/%E7%B3%BB%E7%BB%9F%E8%87%AA%E9%80%82%E5%BA%94%E9%99%90%E6%B5%81
Sentinel 系统自适应限流从整体维度对应用入口流量进行控制,结合应用的 Load、CPU 使用率、总体平均 RT、入口 QPS 和并发线程数等几个维度的监控指标,通过自适应的流控策略,让系统的入口流量和系统的负载达到一个平衡,让系统尽可能跑在最大吞吐量的同时保证系统整体的稳定性。
15.7.2 各项配置参数说明
15.7.3 配置全局QPS
…略
15.8 @SentinelResource
15.8.1 按资源名称限流+后续处理
1.修改Module—cloudalibaba-sentinel-service8401
- POM
<dependency>
<groupId>com.rg.springcloudgroupId>
<artifactId>cloud-api-commonsartifactId>
<version>${project.version}version>
dependency>
- 业务类RateLimitController
@RestController
public class RateLimitController
{
@GetMapping("/byResource")
@SentinelResource(value = "byResource",blockHandler = "handleException")
public CommonResult byResource(){
return new CommonResult(200, "按资源名称限流测试OK", new Payment(2020L, "serial001"));
}
public CommonResult handleException(BlockException exception){
return new CommonResult(444, exception.getClass().getCanonicalName() + "\t服务不可用");
}
2.配置流控规则
- 配置步骤
- 图形配置和代码关系
- 表示1秒钟内查询次数大于1,就跑到我们自定义的方法,进行限流
3.测试
- 1秒钟点击1下,OK
- 超过上述,疯狂点击,返回了自己定义的限流处理信息,限流发生
4.额外问题
此时关闭问服务8401看看,Sentinel控制台,流控规则消失了===> 说明 在sentinel上的配置是临时的
15.8.2 按照Url地址限流+后续处理
通过访问的URL来限流,会返回Sentinel自带默认的限流处理信息
- 业务类RateLimitController:
@GetMapping("/rateLimit/byUrl")
@SentinelResource(value = "byUrl")
public CommonResult byUrl()
{
return new CommonResult(200,"按url限流测试OK",new Payment(2020L,"serial002"));
}
- 配置:
- 测试
疯狂点击http://localhost:8401/rateLimit/byUrl
会返回Sentinel自带的限流处理结果
15.8.3 上面兜底方案面临的问题
1 系统默认的,没有体现我们自己的业务要求。
2 依照现有条件,我们自定义的处理方法又和业务代码耦合在一块,不直观。
3 每个业务方法都添加一个兜底的,那代码膨胀加剧。
4 全局统一的处理方法没有体现。
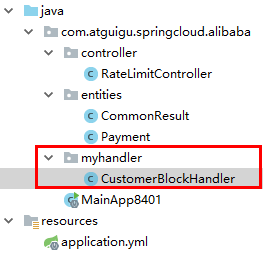
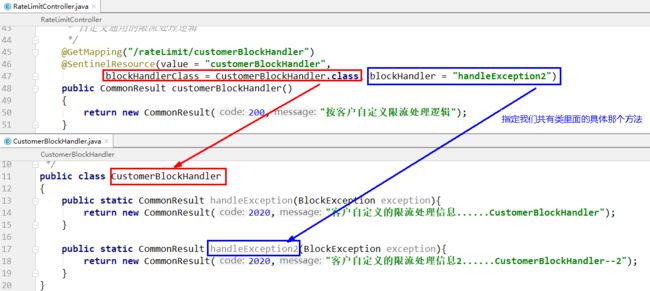
15.8.4 客户自定义限流处理逻辑
- 创建CustomerBlockHandler类用于自定义限流处理逻辑
public class CustomerBlockHandler
{
public static CommonResult handleException(BlockException exception){
return new CommonResult(2020,"自定义的限流处理信息......CustomerBlockHandler");
}
}
- 修改RateLimitController
/**
* 自定义通用的限流处理逻辑,
blockHandlerClass = CustomerBlockHandler.class
blockHandler = handleException2
上述配置:找CustomerBlockHandler类里的handleException2方法进行兜底处理
*/
/**
* 自定义通用的限流处理逻辑
*/
@GetMapping("/rateLimit/customerBlockHandler")
@SentinelResource(value = "customerBlockHandler",
blockHandlerClass = CustomerBlockHandler.class, blockHandler = "handleException2")
public CommonResult customerBlockHandler()
{
return new CommonResult(200,"按客户自定义限流处理逻辑");
}
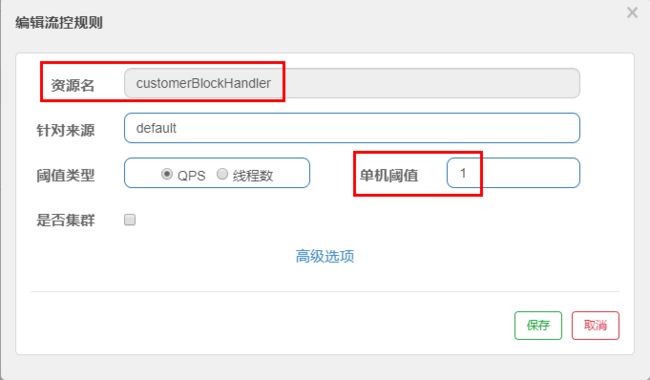
- Sentinel控制台配置:
- 测试:
疯狂访问:http://localhost:8401/rateLimit/customerBlockHandler ,测试后我们自定义的出来了.
- 进一步说明
15.8.5 更多注解属性说明
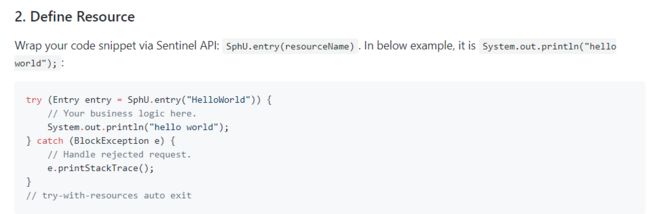
1.Sentinel主要有三个核心Api
- SphU定义资源
- Tracer定义统计
- ContextUtil定义了上下文
2.自定义Resource
所有的代码都要用try-catch-finally方式进行处理,o(╥﹏╥)o
15.9 服务熔断功能
15.9.1 sentinel整合+Ribbon+fallback
1.启动nacos和sentinel
2.构建提供者9003/9004
- 建Module—cloudalibaba-provider-payment9003/9004
- POM
<dependencies>
<dependency>
<groupId>com.alibaba.cloudgroupId>
<artifactId>spring-cloud-starter-alibaba-nacos-discoveryartifactId>
dependency>
<dependency>
<groupId>com.rg.springcloudgroupId>
<artifactId>cloud-api-commonsartifactId>
<version>${project.version}version>
dependency>
<dependency>
<groupId>org.springframework.bootgroupId>
<artifactId>spring-boot-starter-webartifactId>
dependency>
<dependency>
<groupId>org.springframework.bootgroupId>
<artifactId>spring-boot-starter-actuatorartifactId>
dependency>
<dependency>
<groupId>org.springframework.bootgroupId>
<artifactId>spring-boot-devtoolsartifactId>
<scope>runtimescope>
<optional>trueoptional>
dependency>
<dependency>
<groupId>org.projectlombokgroupId>
<artifactId>lombokartifactId>
<optional>trueoptional>
dependency>
<dependency>
<groupId>org.springframework.bootgroupId>
<artifactId>spring-boot-starter-testartifactId>
<scope>testscope>
dependency>
dependencies>
- YML
server:
port: 9003
spring:
application:
name: nacos-payment-provider
cloud:
nacos:
discovery:
server-addr: 192.168.174.128:8848 #配置Nacos地址
management:
endpoints:
web:
exposure:
include: '*'
- 主启动
@SpringBootApplication
@EnableDiscoveryClient
public class PaymentMain9003
{
public static void main(String[] args) {
SpringApplication.run(PaymentMain9003.class, args);
}
}
- 业务类
@RestController
public class PaymentController
{
@Value("${server.port}")
private String serverPort;
public static HashMap<Long,Payment> hashMap = new HashMap<>();
static
{
hashMap.put(1L,new Payment(1L,"28a8c1e3bc2742d8848569891fb42181"));
hashMap.put(2L,new Payment(2L,"bba8c1e3bc2742d8848569891ac32182"));
hashMap.put(3L,new Payment(3L,"6ua8c1e3bc2742d8848569891xt92183"));
}
@GetMapping(value = "/paymentSQL/{id}")
public CommonResult<Payment> paymentSQL(@PathVariable("id") Long id)
{
Payment payment = hashMap.get(id);
CommonResult<Payment> result = new CommonResult(200,"from mysql,serverPort: "+serverPort,payment);
return result;
}
}
- 测试地址:http://localhost:9003/paymentSQL/1 ,可以正常访问
3.消费者84
- 建Module—cloudalibaba-consumer-nacos-order84
- POM
<dependencies>
<dependency>
<groupId>com.alibaba.cloudgroupId>
<artifactId>spring-cloud-starter-alibaba-nacos-discoveryartifactId>
dependency>
<dependency>
<groupId>com.alibaba.cloudgroupId>
<artifactId>spring-cloud-starter-alibaba-sentinelartifactId>
dependency>
<dependency>
<groupId>com.rg.springcloudgroupId>
<artifactId>cloud-api-commonsartifactId>
<version>${project.version}version>
dependency>
<dependency>
<groupId>org.springframework.bootgroupId>
<artifactId>spring-boot-starter-webartifactId>
dependency>
<dependency>
<groupId>org.springframework.bootgroupId>
<artifactId>spring-boot-starter-actuatorartifactId>
dependency>
<dependency>
<groupId>org.springframework.bootgroupId>
<artifactId>spring-boot-devtoolsartifactId>
<scope>runtimescope>
<optional>trueoptional>
dependency>
<dependency>
<groupId>org.projectlombokgroupId>
<artifactId>lombokartifactId>
<optional>trueoptional>
dependency>
<dependency>
<groupId>org.springframework.bootgroupId>
<artifactId>spring-boot-starter-testartifactId>
<scope>testscope>
dependency>
dependencies>
- YML
server:
port: 84
spring:
application:
name: nacos-order-consumer
cloud:
nacos:
discovery:
server-addr: 192.168.174.128:8848
sentinel:
transport:
#配置Sentinel dashboard地址
dashboard: localhost:8888
#默认8719端口,假如被占用会自动从8719开始依次+1扫描,直至找到未被占用的端口
port: 8719
##消费者将要去访问的微服务名称(注册成功进nacos的微服务提供者)
service-url:
nacos-user-service: http://nacos-payment-provider
- 主启动
@EnableDiscoveryClient
@SpringBootApplication
public class OrderNacosMain84
{
public static void main(String[] args) {
SpringApplication.run(OrderNacosMain84.class, args);
}
}
- 业务类
ApplicationContextConfig
@Configuration
public class ApplicationContextConfig
{
@Bean
@LoadBalanced
public RestTemplate getRestTemplate()
{
return new RestTemplate();
}
}
4.CircleBreakerController +测试
目的:验证fallback管运行异常,blockHandler管配置违规
- 编写基础代码
@RestController
@Slf4j
public class CircleBreakerController {
public static final String SERVICE_URL = "http://nacos-payment-provider";
@Resource
private RestTemplate restTemplate;
@RequestMapping("/consumer/fallback/{id}")
@SentinelResource(value = "fallback")
public CommonResult <Payment> fallback(@PathVariable Long id){
CommonResult result = restTemplate.getForObject(SERVICE_URL + "/paymentSQL/" + id, CommonResult.class, id);
if(id==4){
System.out.println("44444444444");
throw new IllegalArgumentException("IllegalArgumentException,非法参数异常...");
}else if(result.getData()==null){
System.out.println("111111111111111");
throw new NullPointerException("NullPointerException,该ID没有对应记录,空指针异常...");
}
return result;
}
}
- 访问: http://localhost:84/consumer/fallback/1 进行测试,测试成功! 访问 http://localhost:84/consumer/fallback/4 跳转至到错误页面.但是这个error页面对用户很不友好
- 只配置fallback
编码:
@RequestMapping("/consumer/fallback/{id}")
@SentinelResource(value = "fallback",fallback = "handlerFallback") //fallback负责业务异常
public CommonResult <Payment> fallback(@PathVariable Long id){
CommonResult result = restTemplate.getForObject(SERVICE_URL + "/paymentSQL/" + id, CommonResult.class, id);
if(id==4){
throw new IllegalArgumentException("IllegalArgumentException,非法参数异常...");
}else if(result.getData()==null){
throw new NullPointerException("NullPointerException,该ID没有对应记录,空指针异常...");
}
return result;
}
public CommonResult handlerFallback(@PathVariable Long id,Throwable e){
Payment payment = new Payment(id, "null");
return new CommonResult(444, "兜底异常handlerFallback,exception内容:" + e.getMessage(), payment);
}
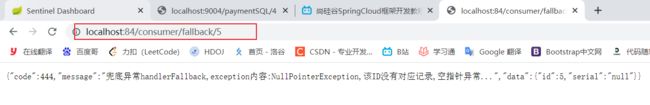
结果:
图说:
- 只配置blockHandler
编码:
@RequestMapping("/consumer/fallback/{id}")
//@SentinelResource(value = "fallback",fallback = "handlerFallback") //fallback负责业务异常
@SentinelResource(value = "fallback",blockHandler = "blockHandler") //blockHandler负责在sentinel里面配置的降级限流
public CommonResult <Payment> fallback(@PathVariable Long id){
CommonResult result = restTemplate.getForObject(SERVICE_URL + "/paymentSQL/" + id, CommonResult.class, id);
if(id==4){
throw new IllegalArgumentException("IllegalArgumentException,非法参数异常...");
}else if(result.getData()==null){
throw new NullPointerException("NullPointerException,该ID没有对应记录,空指针异常...");
}
return result;
}
public CommonResult handlerFallback(@PathVariable Long id,Throwable e){
Payment payment = new Payment(id, "null");
return new CommonResult(444, "兜底异常handlerFallback,exception内容:" + e.getMessage(), payment);
}
public CommonResult blockHandler(@PathVariable Long id, BlockException blockException) {
Payment payment = new Payment(id,"null");
return new CommonResult<>(445,"blockHandler-sentinel限流,无此流水: blockException "+blockException.getMessage(),payment);
}
本例sentinel需配置:
异常超过2次后,断路器打开,断电跳闸,系统被保护
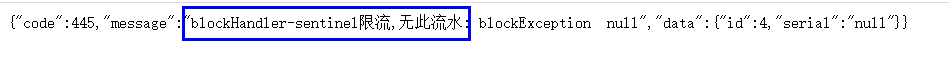
结果:
图说:
- fallback和blockHandler都配置
编码:
@RequestMapping("/consumer/fallback/{id}")
//@SentinelResource(value = "fallback")
//@SentinelResource(value = "fallback",fallback = "handlerFallback") //fallback负责业务异常
//@SentinelResource(value = "fallback",blockHandler = "blockHandler") //blockHandler负责在sentinel里面配置的降级限流
@SentinelResource(value = "fallback",fallback = "handlerFallback",blockHandler = "blockHandler")
public CommonResult <Payment> fallback(@PathVariable Long id){
CommonResult result = restTemplate.getForObject(SERVICE_URL + "/paymentSQL/" + id, CommonResult.class, id);
if(id==4){
System.out.println("44444444444");
throw new IllegalArgumentException("IllegalArgumentException,非法参数异常...");
}else if(result.getData()==null){
System.out.println("111111111111111");
throw new NullPointerException("NullPointerException,该ID没有对应记录,空指针异常...");
}
return result;
}
public CommonResult handlerFallback(@PathVariable Long id,Throwable e){
Payment payment = new Payment(id, "null");
return new CommonResult(444, "兜底异常handlerFallback,exception内容:" + e.getMessage(), payment);
}
public CommonResult blockHandler(@PathVariable Long id, BlockException blockException) {
Payment payment = new Payment(id,"null");
return new CommonResult<>(445,"blockHandler-sentinel限流,无此流水: blockException "+blockException.getMessage(),payment);
}
本例sentinel需配置:
结果:
若 blockHandler 和 fallback 都进行了配置,则被限流降级而抛出 BlockException 时只会进入 blockHandler 处理逻辑。如果没有超出限流规则,则走fallback 逻辑.
图说:
- 忽略属性—exceptionsToIgnore
编码:
@RequestMapping("/consumer/fallback/{id}")
//@SentinelResource(value = "fallback")
//@SentinelResource(value = "fallback",fallback = "handlerFallback") //fallback负责业务异常
//@SentinelResource(value = "fallback",blockHandler = "blockHandler") //blockHandler负责在sentinel里面配置的降级限流
@SentinelResource(value = "fallback",fallback = "handlerFallback",blockHandler = "blockHandler",exceptionsToIgnore = {IllegalArgumentException.class})
public CommonResult <Payment> fallback(@PathVariable Long id){
CommonResult result = restTemplate.getForObject(SERVICE_URL + "/paymentSQL/" + id, CommonResult.class, id);
if(id==4){
System.out.println("44444444444");
throw new IllegalArgumentException("IllegalArgumentException,非法参数异常...");
}else if(result.getData()==null){
System.out.println("111111111111111");
throw new NullPointerException("NullPointerException,该ID没有对应记录,空指针异常...");
}
return result;
}
public CommonResult handlerFallback(@PathVariable Long id,Throwable e){
Payment payment = new Payment(id, "null");
return new CommonResult(444, "兜底异常handlerFallback,exception内容:" + e.getMessage(), payment);
}
public CommonResult blockHandler(@PathVariable Long id, BlockException blockException) {
Payment payment = new Payment(id,"null");
return new CommonResult<>(445,"blockHandler-sentinel限流,无此流水: blockException "+blockException.getMessage(),payment);
}
本例sentinel无配置
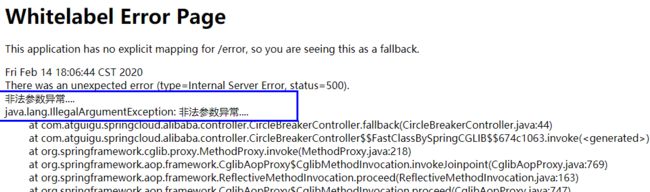
图说:
结果: 程序异常打到前台了,对用户不友好
15.9.2 sentinel整合+Feign+fallback
1.修改84模块:84消费者调用提供者9003,Feign组件一般是消费侧
2.修改代码
- POM
<dependency>
<groupId>org.springframework.cloudgroupId>
<artifactId>spring-cloud-starter-openfeignartifactId>
dependency>
- YML—激活Sentinel对Feign的支持
server:
port: 84
spring:
application:
name: nacos-order-consumer
cloud:
nacos:
discovery:
server-addr: 192.168.174.128:8848
sentinel:
transport:
#配置Sentinel dashboard地址
dashboard: localhost:8888
#默认8719端口,假如被占用会自动从8719开始依次+1扫描,直至找到未被占用的端口
port: 8719
##消费者将要去访问的微服务名称(注册成功进nacos的微服务提供者)
service-url:
nacos-user-service: http://nacos-payment-provider
# 激活Sentinel对Feign的支持
management:
endpoints:
web:
exposure:
include: '*'
feign:
sentinel:
enabled: true
- 业务类
带@FeignClient注解的业务接口
@FeignClient(value = "nacos-payment-provider",fallback = PaymentFallbackService.class)//调用中关闭9003服务提供者
public interface PaymentService
{
@GetMapping(value = "/paymentSQL/{id}")
public CommonResult<Payment> paymentSQL(@PathVariable("id") Long id);
}
PaymentFallbackService类
@Component
public class PaymentFallbackService implements PaymentService
{
@Override
public CommonResult<Payment> paymentSQL(Long id)
{
return new CommonResult<>(444,"服务降级返回,没有该流水信息",new Payment(id, "errorSerial......"));
}
}
controller
@RestController
@Slf4j
public class CircleBreakerController
{
//========================Sentinel结合OpenFeign
@Resource
private PaymentService paymentService;
@GetMapping(value = "/consumer/paymentSQL/{id}")
public CommonResult<Payment> paymentSQL(@PathVariable("id") Long id){
// if(id==4){
// throw new RuntimeException("没有该id");
// }
return paymentService.paymentSQL(id);
}
}
- 主启动—添加@EnableFeignClients启动Feign的功能
@EnableDiscoveryClient
@SpringBootApplication
@EnableFeignClients
public class OrderNacosMain84
{
public static void main(String[] args) {
SpringApplication.run(OrderNacosMain84.class, args);
}
}
3.测试
访问: http://localhost:84/consumer/paymentSQL/1
测试84调用9003,此时故意关闭9003微服务提供者,可以看到84消费侧自动降级,不会被耗死
15.9.3 熔断框架比较
15.10 规则持久化
15.10.1 是什么
一旦我们重启应用,sentinel规则将消失,生产环境需要将配置规则进行持久化
15.10.2 怎么玩
将限流配置规则持久化进Nacos保存,只要刷新8401某个rest地址,sentinel控制台的流控规则就能看到,只要Nacos里面的配置不删除,针对8401上sentinel上的流控规则持续有效
15.10.3 实现步骤
- 修改cloudalibaba-sentinel-service8401
- POM
<dependency>
<groupId>com.alibaba.cspgroupId>
<artifactId>sentinel-datasource-nacosartifactId>
dependency>
- YML—添加Nacos数据源配置
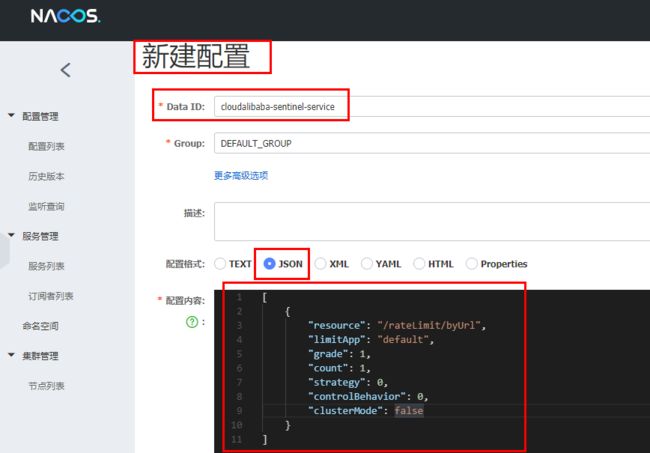
- 添加Nacos业务规则配置
内容解析:
[
{
"resource": "/rateLimit/byUrl",
"limitApp": "default",
"grade": 1,
"count": 1,
"strategy": 0,
"controlBehavior": 0,
"clusterMode": false
}
]
resource:资源名称;
limitApp:来源应用;
grade:阈值类型,0表示线程数,1表示QPS;
count:单机阈值;
strategy:流控模式,0表示直接,1表示关联,2表示链路;
controlBehavior:流控效果,0表示快速失败,1表示Warm Up,2表示排队等待;
clusterMode:是否集群。
- 启动8401后刷新sentinel发现业务规则有了
15.10.4 测试
- 快速访问测试接口,http://localhost:8401/rateLimit/byUrl ,显示: Blocked By Sentinel(flow limiting)错误 ,说明配置文件生效了
- 停止8401再看sentinel
-
重新启动8401再看sentinel .
乍一看还是没有,稍等一会儿.多次调用 http://localhost:8401/rateLimit/byUrl 重新配置出现了,持久化验证通过