蓝奏云获取下载链接js逆向
本期地址如下,使用base64解密获得
aHR0cHM6Ly9meGpkLmxhbnpvdXcuY29tL2l6bkxrMTdncnkyZA==
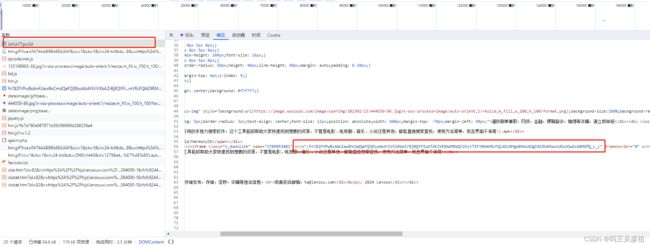
获取最终的下载链接需要经过三次请求获得,如下图
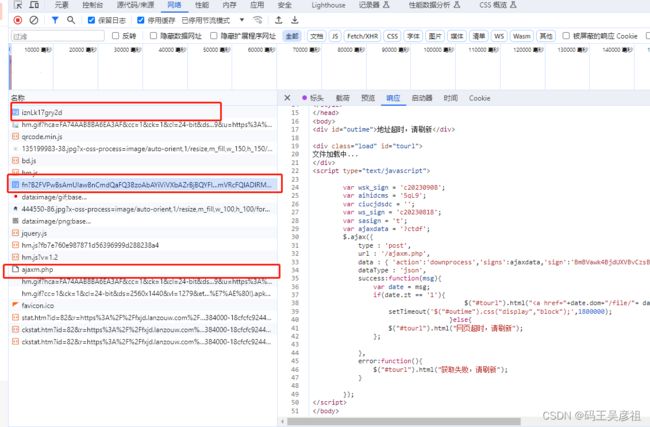
每个请求都包含下一次请求的信息,我们逐步分析请求
第一个请求直接包含了第二次请求的src

第二个请求直接包含了第三次post请求所需要传的data参数

第三个请求直接包含了文件下载的url
所以本质上,这里面没有js逆向的逻辑,只是请求的逻辑而已,python代码如下
import requests
import re
from bs4 import BeautifulSoup
session = requests.session()
headers = {
'Accept': 'application/json, text/javascript, */*',
'Accept-Language': 'zh-CN,zh;q=0.9',
'Cache-Control': 'no-cache',
'Connection': 'keep-alive',
'Content-Type': 'application/x-www-form-urlencoded',
# 'Cookie': 'codelen=1; Hm_lvt_fb7e760e987871d56396999d288238a4=1705051448; pc_ad1=1; uz_distinctid=18cfcfc9243e23-06f6015bb3f86a-26001951-384000-18cfcfc9244134c; STDATA82=czst_eid%3D130820850-3821-https%253A%252F%252Ffxjd.lanzouw.com%252F%26ntime%3D3821; Hm_lpvt_fb7e760e987871d56396999d288238a4=1705051547',
'Origin': 'https://fxjd.lanzouw.com',
'Pragma': 'no-cache',
'Referer': 'https://fxjd.lanzouw.com/fn?VzEGbAhkD2hWNQJlC2ZVbQRnAz4FaQQgBXZTaAVoBDJVZQVnCWRQMQVhAmUEZF1qA38CcVc1ATIFJFUkV25XNFckBjgIMg81VmsCMQsmVWkEawN3BRYEPw_c_c',
'Sec-Fetch-Dest': 'empty',
'Sec-Fetch-Mode': 'cors',
'Sec-Fetch-Site': 'same-origin',
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36',
'X-Requested-With': 'XMLHttpRequest',
'sec-ch-ua': '"Not_A Brand";v="8", "Chromium";v="120", "Google Chrome";v="120"',
'sec-ch-ua-mobile': '?0',
'sec-ch-ua-platform': '"Windows"',
}
host = "https://fxjd.lanzouw.com"
response = session.get('https://fxjd.lanzouw.com/iW8O40no7fni', headers=headers)
print(response)
soup = BeautifulSoup(response.text, 'html.parser')
divs = soup.find('div', {'class': 'n_downlink'})
src = soup.find(class_="n_downlink").get("src")
second_src = host + src
response = session.get(second_src, headers=headers)
print(response)
pattern = r']*>(.*?)'
matches = re.findall(pattern, response.text, re.DOTALL)
dowload_js = matches[1]
aihidcms = re.search(r"var aihidcms\s*=\s*'(.*?)';", dowload_js).group(1)
action = re.search(r"'action':'(.*?)'", dowload_js).group(1)
ajaxdata = re.search(r"var ajaxdata\s*=\s*'(.*?)';", dowload_js).group(1)
sign = re.search(r"'sign':'(.*?)'", dowload_js).group(1)
ciucjdsdc = re.search(r"var ciucjdsdc\s*=\s*'(.*?)';", dowload_js).group(1)
ves = re.search(r"'ves':(\d+)", dowload_js).group(1)
print("aihidcms:", aihidcms)
print("action:", action)
print("ajaxdata:", ajaxdata)
print("sign:", sign)
print("ciucjdsdc:", ciucjdsdc)
print("ves:", ves)
data = {
'action': action,
'signs': ajaxdata,
'sign': sign,
'websign': ciucjdsdc,
'websignkey': aihidcms,
'ves': ves,
}
response = session.post('https://fxjd.lanzouw.com/ajaxm.php', headers=headers, data=data)
print(response)
print(response.json())
data_src = 'https://developer-oss.lanrar.com/file/' + response.json().get('url')
response = session.get(data_src, headers=headers)
print(response)
print(len(response.content))
