使用iptables与firewalld防火墙
iptables:在早期的Linux系统中,使用的是iptables防火墙管理服务来配置防火墙的策略与规则链
iptables服务把用于处理或过滤流量的策略条目称之为规则,多条规则可以组成一个规则链,而规则链则依据数据包处理位置的不同进行分类
1.在进行路由选择前处理数据包(PREROUTING)
2.处理流入的数据包(INPUT)
3.处理流出的数据包(OUTPUT)
4.处理转发的数据包(FORWARD)
5.在进行路由选择后处理数据包(POSTROUTING)
iptables中常用的参数及作用
-P:设置默认策略
-F:清空规则链
-L:查看规则链
-A:在规则链的末尾加入新的规则
-I num:在规则链的头部加入新规则
-D num:删除某一条规则
-s:匹配来源地址IP/MASK,加感叹号"!"表示除了这个IP外
-d:匹配目标地址
-i 网卡名称:匹配从这块网卡流入的数据
-o 网卡名称:匹配从这块网卡流出的数据
-p:匹配协议,如TCP、UDP、ICMP
--dport num:匹配目标端口号
--sport num:匹配来源端口号
//查看已有的规则链
[root@localhost ~]# iptables -L
Chain INPUT (policy ACCEPT)//处理流入的数据包
target prot opt source destination
ACCEPT udp -- anywhere anywhere udp dpt:domain
ACCEPT tcp -- anywhere anywhere tcp dpt:domain
ACCEPT udp -- anywhere anywhere udp dpt:bootps
ACCEPT tcp -- anywhere anywhere tcp dpt:bootps
Chain FORWARD (policy ACCEPT)//处理转发的数据包
target prot opt source destination
ACCEPT all -- anywhere 192.168.122.0/24 ctstate RELATED,ESTABLISHED
ACCEPT all -- 192.168.122.0/24 anywhere
ACCEPT all -- anywhere anywhere
REJECT all -- anywhere anywhere reject-with icmp-port-unreachable
REJECT all -- anywhere anywhere reject-with icmp-port-unreachable
Chain OUTPUT (policy ACCEPT)//处理流出的数据包
target prot opt source destination
ACCEPT udp -- anywhere anywhere udp dpt:bootpc//清空已有的防火墙规则链
[root@localhost ~]# iptables -F
[root@localhost ~]# iptables -L
Chain INPUT (policy ACCEPT)
target prot opt source destinationChain FORWARD (policy ACCEPT)
target prot opt source destinationChain OUTPUT (policy ACCEPT)
target prot opt source destination//把INPUT规则链的默认策略设置为拒绝
//规则链的默认拒绝动作只能是DROP,而不能是REJECT
[root@localhost ~]# iptables -P INPUT DROP
[root@localhost ~]# iptables -L
Chain INPUT (policy DROP)
target prot opt source destinationChain FORWARD (policy ACCEPT)
target prot opt source destinationChain OUTPUT (policy ACCEPT)
target prot opt source destination//向INPUT规则链中添加允许ICMP流量进入的策略规则(ping命令使用的是ICMP协议)
[root@localhost ~]# iptables -I input -p icmp -j ACCEPT//拿出INPUT规则链中刚刚加入的那条策略(允许ICMP流量,并把默认策略设置为允许)
[root@localhost ~]# iptables -D INPUT 1
[root@localhost ~]# iptables -P INPUT ACCEPT
[root@localhost ~]# iptables -L
Chain INPUT (policy ACCEPT)
target prot opt source destinationChain FORWARD (policy ACCEPT)
target prot opt source destinationChain OUTPUT (policy ACCEPT)
target prot opt source destination//将INPUT的规则链设置为只允许指定网段的主机访问本机的22端口,拒绝来自其他所有主机的流量
[root@localhost ~]# iptables -I INPUT -s 192.168.0.0/16 -p tcp --dport 22 -j ACCEPT
[root@localhost ~]# iptables -A INPUT -p tcp --dport 22 -j REJECT
[root@localhost ~]# iptables -L
Chain INPUT (policy ACCEPT)
target prot opt source destination
REJECT udp -- anywhere anywhere udp dpt:italk reject-with icmp-port-unreachable
REJECT tcp -- anywhere anywhere tcp dpt:italk reject-with icmp-port-unreachable
ACCEPT tcp -- 192.168.0.0/16 anywhere tcp dpt:ssh
REJECT tcp -- anywhere anywhere tcp dpt:ssh reject-with icmp-port-unreachable//向INPUT规则链中添加拒绝192.168.10.5主机访问本机80端口(Web服务)的策略规则
[root@localhost ~]# iptables -I INPUT -p tcp -s 192.168.10.5 --dport 80 -j REJECT
[root@localhost ~]# iptables -L
Chain INPUT (policy ACCEPT)
target prot opt source destination
REJECT tcp -- 192.168.10.5 anywhere tcp dpt:http reject-with icmp-port-unreachable
REJECT udp -- anywhere anywhere udp dpt:italk reject-with icmp-port-unreachable
REJECT tcp -- anywhere anywhere tcp dpt:italk reject-with icmp-port-unreachable
ACCEPT tcp -- 192.168.0.0/16 anywhere tcp dpt:ssh
REJECT tcp -- anywhere anywhere tcp dpt:ssh reject-with icmp-port-unreachable//向INPUT规则链中添加拒绝所有主机访问本机100~1024端口的策略规则
[root@localhost ~]# iptables -A INPUT -p tcp --dport 1000:1024 -j REJECT
[root@localhost ~]# iptables -A INPUT -p udp --dport 1000:1024 -j REJECT
[root@localhost ~]# iptables -L
Chain INPUT (policy ACCEPT)
target prot opt source destination
REJECT tcp -- 192.168.10.5 anywhere tcp dpt:http reject-with icmp-port-unreachable
REJECT udp -- anywhere anywhere udp dpt:italk reject-with icmp-port-unreachable
REJECT tcp -- anywhere anywhere tcp dpt:italk reject-with icmp-port-unreachable
ACCEPT tcp -- 192.168.0.0/16 anywhere tcp dpt:ssh
REJECT tcp -- anywhere anywhere tcp dpt:ssh reject-with icmp-port-unreachable
REJECT tcp -- anywhere anywhere tcp dpts:cadlock2:1024 reject-with icmp-port-unreachable
REJECT udp -- anywhere anywhere udp dpts:cadlock2:1024 reject-with icmp-port-unreachable//保存命令
[root@localhost ~]# iptables-save
# Generated by iptables-save v1.8.4 on Wed Jun 14 16:24:10 2023//5/6/7之前的版本
[root@localhost ~]# service iptables save
firewalld
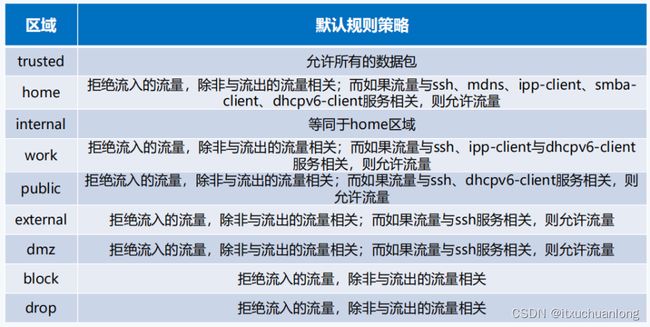
firewalld中常用的区域名称及策略规则
使用firewalld配置的防火墙策略默认为运行时(Runtime)模式,又称为当前生效模式,而且会随着系统的重启而失效。如果想让配置策略一直存在,就需要使用永久(Permanent)模式
方法是在用firewall-cmd命令正常设置防火墙策略是添加一个--permanent参数,需要进行重启,如果要立即生效,手动执行firewall-cmd --reload命令
//查看firewalld服务当前所使用的区域
//在配置防火墙策略前,必须查看当前生效的是哪个区域,否则配置的防火墙策略将不会立即生效
[root@localhost ~]# firewall-cmd --get-default-zone
public//查询指定网卡在firewalld服务中绑定的区域
[root@localhost ~]# firewall-cmd --get-zone-of-interface=ens192
public//把网卡默认区域修改为external,并在系统重启后生效
[root@localhost ~]# firewall-cmd --permanent --zone=external --change-interface=ens192
The interface is under control of NetworkManager, setting zone to 'external'.
success//把firewalld服务的默认区域设置为public
//默认规则优先级小于网卡优先级
[root@localhost ~]# firewall-cmd --set-default-zone=public
Warning: ZONE_ALREADY_SET: public
success
[root@localhost ~]# firewall-cmd --get-default-zone
public
[root@localhost ~]# firewall-cmd --get-zone-of-interface=ens192
external//启动和关闭firewalld防火墙服务的应急状况模式
[root@localhost ~]# firewall-cmd --panic-on
success
[root@localhost ~]# firewall-cmd --panic-off
success//查询SSH和HTTPS协议的流量是否允许放行
[root@localhost ~]# firewall-cmd --zone=public --query-service=ssh
yes
[root@localhost ~]# firewall-cmd --zone=public --query-service=https
no//把HTTPS协议的流量设置为永久允许放行,并立即生效
[root@localhost ~]# firewall-cmd --permanent --zone=public --add-service=https
success
[root@localhost ~]# firewall-cmd --reload
success
[root@localhost ~]# firewall-cmd --zone=public --query-service=https
yes
//把HTTP协议的流量设置为永久拒绝,并立即生效
[root@localhost ~]# firewall-cmd --permanent --zone=public --remove-service=http
Warning: NOT_ENABLED: http
success
[root@localhost ~]# firewall-cmd --reload
success//把访问8080和8081端口的流量策略设置为允许,但仅限当前生效
[root@localhost ~]# firewall-cmd --zone=public --add-port=8080-8081/tcp
success
[root@localhost ~]# firewall-cmd --zone=public --list-ports
8080-8081/tcp
//把原本访问本机888端口的流量转发到22端口,而且要求当前和长期均有效
[root@localhost ~]# firewall-cmd --permanent --zone=<区域> --add-forward-port=port=<源端口号>:proto=<协议>:toport=<目标端口>:toaddr=<目标地址>
succes//富规则也叫复规则,优先级在所有的防火墙策略中也是最高的。比如我妈在firewalld服务中配置一条富规则,使其拒绝192.168.10.0/24网段的所有用户访问本机的ssh服务
[root@localhost ~]# firewall-cmd --zone=public --add-rich-rule="rule family="ipv4" source address="192.168.10.0/24" service name="ssh" reject"
success
[root@localhost ~]# firewall-cmd --reload
success