07-k8s中secret资源02-玩转secret
一、回顾secret资源的简单实用
第一步:将想要的数据信息【key:value】中的value值,使用base64编码后,写入secret资源清单中;
第二步:创建secret资源;
第三步:pod资源引用secret资源;
二、实战secret资源
1,第一步:将数据base64编码
[root@k8s231 ~]# echo xinjizhiwa | base64
eGluaml6aGl3YQo=
2,编辑secret资源清单
[root@k8s231 secrets]# vim secret.yaml
apiVersion: v1
kind: Secret
metadata:
name: secret-01#用户自定义的任意数据类型;(还有别的类型。。。)
type: Opaque
data:
k8s: eGluaml6aGl3YQo=
3,创建secret资源
[root@k8s231 secrets]# kubectl apply -f secret.yaml
4,pod引用secret资源
· 编辑资源清单
[root@k8s231 secrets]# cat pod.yaml
#pod资源env环境变量方式引用secret
apiVersion: v1
kind: Pod
metadata:
name: pod-secret-01
spec:
containers:
- name: c1
image: nginx:1.20.1-alpine
env:
- name: k8s
valueFrom:
#声明引用secret资源
secretKeyRef:
name: secret-01
#声明使用secret资源中的那一个key
key: k8s---
#vomlume方式引用
apiVersion: v1
kind: Pod
metadata:
name: pod-secret-02
spec:
#声明存储卷
volumes:
- name: vol-secret
#声明存储卷的类型是secret
secret:
#指定secret资源的名称(使用哪个secret资源?)
secretName: secret-01
containers:
- name: c2
image: nginx:1.24.0-alpine
volumeMounts:
- name: vol-secret
#挂载到容器的哪个位置路径?
mountPath: /secret/
· 创建pod资源
[root@k8s231 secrets]# kubectl apply -f pod.yaml
5,进入容器查看是否引用成功
· env应用的pod容器
[root@k8s231 secrets]# kubectl exec pod-secret-01 -it -- sh
/ # env
k8s=xinjizhiwa
· volumes引用的pod容器
[root@k8s231 secrets]# kubectl exec pod-secret-02 -it -- sh
/ # cat /secret/k8s
xinjizhiwa
三、pod资源清单指定key引用secret
1,编辑pod资源清单
[root@k8s231 secrets]# cat pod.yaml
apiVersion: v1
kind: Pod
metadata:
name: pod-secret-02
spec:
#声明存储卷
volumes:
- name: vol-secret
#声明存储卷的类型是secret
secret:
#1,指定secret资源的名称(使用哪个secret资源?)
secretName: secret-01
#2,指定secret资源中要引用的key
items:
- key: k8s
path: xjzw.log
containers:
- name: c2
image: nginx:1.24.0-alpine
volumeMounts:
- name: vol-secret
#挂载到容器的哪个位置路径?
mountPath: /secret/xjzw.log
#只挂在文件,不清空容器原有文件夹
subPath: xjzw.log
2,创建pod
[root@k8s231 secrets]# kubectl apply -f pod.yaml
3,进入pod查看
[root@k8s231 secrets]# kubectl exec pod-secret-02 -it -- sh
/ # ls /secret/
xjzw.log
/ # cat /secret/xjzw.log
xinjizhiwa
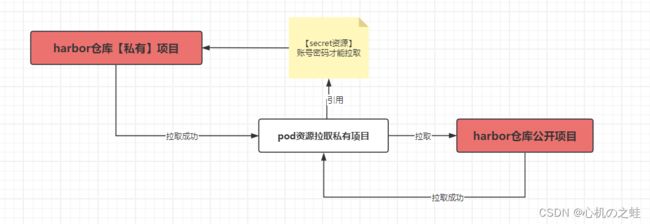
四、secret类型之-私有镜像仓库使用
创建Docker harbor的secret信息:
因为,k8s拉取镜像与Docker拉取镜像是不同的方式,所以k8s需要创建一个属于自己的来气镜像的方式;
1>docker-registry:创建一个给Docker registry容器镜像仓库使用的secret
2>generic: 从本地file, directory或者literal value创建一个 secret(这是大多数情况使用的)也就是资源清单中的type:Opaque是一个意思;
3>tls: 创建一个TLS secret
1,harbor创建私有仓库
harbor创建私有仓库
2,推送镜像到私有仓库
[root@k8s233 ~]# docker push harbor.xinjizhiwa.com/xinjizhiwa01/nginx:1.20.1-alpine
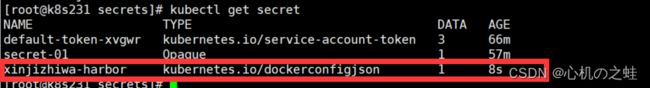
3,创建拉取镜像的secret资源
· 响应式创建secret资源
docker 拉取镜像的secret账号密码资源
[root@k8s231 secrets]# kubectl create secret docker-registry xinjizhiwa-harbor --docker-username=admin --docker-password=1 --docker-email=123@qq.com --docker-server=harbor.xinjizhiwa.com
4,创建pod引用拉取镜像的secret资源
[root@k8s231 secrets]# cat pod.yaml
apiVersion: v1
kind: Pod
metadata:
name: pod-secret-02
spec:
#指定镜像拉取的secret资源(secret的拉取镜像类型);
imagePullSecrets:
- name: xinjizhiwa-harbor
containers:
- name: c3
image: harbor.xinjizhiwa.com/xinjizhiwa01/nginx:1.20.1-alpine
五、拓展,如何声明式创建docker registry类型的secret资源
1,【-o yaml】模仿系统声明式的写法
就是将已经创建好的docker registry资源方向使用yaml格式查看;
[root@k8s231 secrets]# kubectl get secrets xinjizhiwa-harbor -o yaml
apiVersion: v1
data:
.dockerconfigjson: eyJhdXRocyI6eyJoYXJib3IueGluaml6aGl3YS5jb20iOnsidXNlcm5hbWUiOiJhZG1pbiIsInBhc3N3b3JkIjoiMSIsImVtYWlsIjoiMTIzQHFxLmNvbSIsImF1dGgiOiJZV1J0YVc0Nk1RPT0ifX19
kind: Secret
metadata:
creationTimestamp: "2024-02-14T05:08:30Z"
name: xinjizhiwa-harbor
namespace: default
resourceVersion: "597638"
uid: 33a3d025-047f-4d22-be5e-b92ed97b3310
type: kubernetes.io/dockerconfigjson
2,base64反向编译查看内容
[root@k8s231 ~]# echo eyJhdXRocyI6eyJoYXJib3IueGluaml6aGl3YS5jb20iOnsidXNlcm5hbWUiOiJhZG1pbiIsInBhc3N3b3JkIjoiMSIsImVtYWlsIjoiMTIzQHFxLmNvbSIsImF1dGgiOiJZV1J0YVc0Nk1RPT0ifX19 | base64 -d
{"auths":{"harbor.xinjizhiwa.com":{"username":"admin","password":"1","email":"123@qq.com","auth":"YWRtaW46MQ=="}}}
[root@k8s231 ~]# echo YWRtaW46MQ== | base64 -d
admin:1
也就是说,dacker registy使用了两次base64的编码;
3,根据上述信息,自己编辑secret声明式资源清单
[root@k8s231 ~]# vim docker.yaml
apiVersion: v1
kind: Secret
metadata:
name: xinjizhiwa-harbor02
type: kubernetes.io/dockerconfigjson
data:
.dockerconfigjson: eyJhdXRocyI6eyJoYXJib3IueGluaml6aGl3YS5jb20iOnsidXNlcm5hbWUiOiJhZG1pbiIsInBhc3N3b3JkIjoiMSIsImVtYWlsIjoiMTIzQHFxLmNvbSIsImF1dGgiOiJZV1J0YVc0Nk1RPT0ifX19
了解到:私有仓库的镜像拉取secret资源的使用即可;
#######################################################################3
编译过程:二次base64编译方向过程
[root@k8s233 ~]# echo -n eyJhdXRocyI6eyJoYXJib3IueGluaml6aGl3YS5jb20iOnsidXNlcm5hbWUiOiJhZG1pbiIsInBhc3N3b3JkIjoiMSIsImVtYWlsIjoiMTIzQHFxLmNvbSIsImF1dGgiOiJZV1J0YVc0Nk1RPT0ifX19 |base64 -d
{"auths":{"harbor.xinjizhiwa.com":{"username":"admin","password":"1","email":"123@qq.com","auth":"YWRtaW46MQ=="}}}
[root@k8s233 ~]# echo -n YWRtaW46MQ== | base64 -d
admin:1
[root@k8s233 ~]# echo -n '{"auths":{"harbor.xinjizhiwa.com":{"username":"admin","password":"1","email":"123@qq.com","auth":"YWRtaW46MQ=="}}}' | base64
eyJhdXRocyI6eyJoYXJib3IueGluaml6aGl3YS5jb20iOnsidXNlcm5hbWUiOiJhZG1pbiIsInBh
c3N3b3JkIjoiMSIsImVtYWlsIjoiMTIzQHFxLmNvbSIsImF1dGgiOiJZV1J0YVc0Nk1RPT0ifX19