X-Ray检测Android设备Root漏洞过程分析
本文章由Jack_Jia编写,转载请注明出处。
文章链接:http://blog.csdn.net/jiazhijun/article/details/8660226
作者:Jack_Jia 邮箱:[email protected]
一、序言
到目前为止Android已被发现大量的提权漏洞,虽然这些提权漏洞随着系统版本的升级已被解决,但是市场上还存在着大量使用老版本系统的设备。提权漏洞在被合法
软件利用(比如一键Root工具)的同时也被大量恶意软件利用,恶意软件可以利用这些提权漏洞获取系统Root权限,这样就可以在您不知情的情况下,后台静默下载安装
软件,发送付费短信,上传隐私信息等恶意行为。
用户如何检测自己设备是否存在已知提权漏洞呢?
X-Ray就是一个检测Android系统中是否存在已知提权漏洞的软件。目前支持对8种漏洞的检测。
X-Ray下载地址:http://www.xray.io/
本文将对X-Ray扫描漏洞原理进行分析。
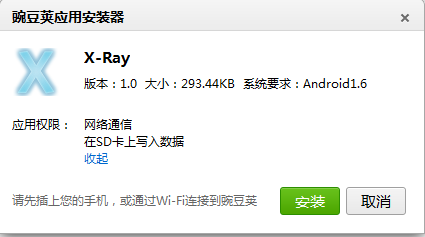
二、软件信息
package name: com.duosecurity.xray
三、分析检测原理
部分Android提权漏洞是一定需要执行在ELF文件中的。ELF文件就是关键的查找点。
1、安装包中是否存在ELF文件?
经观察程序安装包中并不存在ELF文件。
2、ELF文件是否在运行过程中动态下载?
运行程序,执行检测任务后,观察程序文件夹变化,发现程序文件夹并没有新增文件。
3、ELF文件是否在动态下载执行后被程序自动删除?
搜索Smali代码,查找删除文件操作,发现程序调用
invoke-virtual {v0, v2}, Lcom/duosecurity/xray/XRAY;->deleteFile(Ljava/lang/String;)Z。
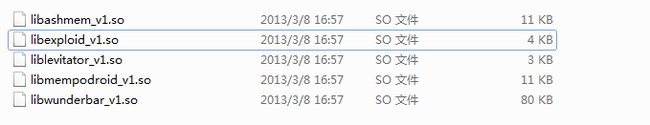
删除该段代码,重新打包签名后,运行程序后,观察程序文件夹变化,发现files文件夹新增如下文件:
从文件名即可看出,这些ELF文件用于不同的Android提权漏洞检测。如果需要看懂这些ELF文件,需对Android不同提权漏洞有所了解,这里不在对提权漏洞原理进行进一步解释。
通过对Log信息及代码的进一步分析,可以获知X-Ray扫描逻辑如下:
1、联网获取漏洞信息,漏洞信息包含客户端处理检测漏洞的方式
D/xray (28458): *********** BOOTSTRAP RESPONSE *********** D/xray (28458): latest_probes: 10 D/xray (28458): latest_app_version: 3 D/xray (28458): latest_app_uri: /xray/static/XRAY-1.0.apk D/xray (28458): ************************************** D/xray (28458): probeupdate: trying request 1 of 3 D/dalvikvm(28458): GC_CONCURRENT freed 257K, 48% free 3259K/6151K, external 481K/993K, paused 2ms+2m s D/xray (28458): *********** UPDATE PROBE RESPONSE *********** D/xray (28458): id: zimperlich D/xray (28458): type: static D/xray (28458): name: Zimperlich D/xray (28458): query_url: /xray/zimperlich/query D/xray (28458): probe_url: /xray/zimperlich/probe D/xray (28458): result_url: D/xray (28458): static_payload: /system/lib/libdvm.so D/xray (28458): dynamic_slot: D/xray (28458): dynamic_payload: D/xray (28458): dynamic_signature: D/xray (28458): ******************************************** D/xray (28458): id: gingerbreak D/xray (28458): type: static D/xray (28458): name: Gingerbreak D/xray (28458): query_url: /xray/gingerbreak/query D/xray (28458): probe_url: /xray/gingerbreak/probe D/xray (28458): result_url: D/xray (28458): static_payload: /system/bin/vold D/xray (28458): dynamic_slot: D/xray (28458): dynamic_payload: D/xray (28458): dynamic_signature: D/xray (28458): ******************************************** D/xray (28458): id: zergrush D/xray (28458): type: static D/xray (28458): name: ZergRush D/xray (28458): query_url: /xray/zergrush/query D/xray (28458): probe_url: /xray/zergrush/probe D/xray (28458): result_url: D/xray (28458): static_payload: /system/lib/libsysutils.so D/xray (28458): dynamic_slot: D/xray (28458): dynamic_payload: D/xray (28458): dynamic_signature: D/xray (28458): ******************************************** D/xray (28458): id: ashmem D/xray (28458): type: dynamic D/xray (28458): name: ASHMEM D/xray (28458): query_url: D/xray (28458): probe_url: D/xray (28458): result_url: /xray/ashmem/result D/xray (28458): static_payload: D/xray (28458): dynamic_slot: 01 D/xray (28458): dynamic_payload: /xray/static/libashmem_v1.so D/xray (28458): dynamic_signature: H+4S6nSomTdUnqUfDKZltq2Mm51VbQ2jnhbzstZ7bzt2dSQU7H6+BefWgCId1b 8gKYdDJrQk5FJ/6OWASVhS7FhNpH6HTN3ieeFbDIX9XYqFmBCzTj5ObFf2yIcQt9JAB3sP/wm7oqzktuX4N2/n+4jmaUOj7HUOgQ imDPB9qK4m866+ScIVXiwZHmR6oaLgr8eJVm9uiOLem/DOhcGMsxSEuFY/6mZPrqMKfXPVP2gUsMPbjY1JAHnCD7yUXlCU2Jby18 HvOH15fo6hkcEhIg1/FvTj+tvHmY64ckKhQdEOOYaBv/Nv2AABMglPQoj/89ntsc7nN1V0qg64u6JJtg== D/xray (28458): ******************************************** D/xray (28458): id: mempodroid D/xray (28458): type: dynamic D/xray (28458): name: Mempodroid D/xray (28458): query_url: D/xray (28458): probe_url: D/xray (28458): result_url: /xray/mempodroid/result D/xray (28458): static_payload: D/xray (28458): dynamic_slot: 02 D/xray (28458): dynamic_payload: /xray/static/libmempodroid_v1.so D/xray (28458): dynamic_signature: P9VL0j2UbuB94WA6gF9XuAmtEUQmPDOWyxDJDQR9wmIbGq1ixThNSl7bnG1rgV pj9M/AgAzxon4umr3FMQV3fLjmZG2QTbNFF7O622G2ssLxeBsCAH/9YC4b9RxVRBQP8cV5B078d+4DHmeOv6ey23omsIwMFoKhXn RHnyU4FhtWpA9rT1Bu2d5RCOkuu8HM+qu2w+ZqWlJlnVIMQUbdfDS4YjVpjjS84hloES/wFPGOh/K2NZe1VhKGLhoIDWt6ROQCcG 8bZ3hTYTq91JlCp+wqdV/D9XufKbBZVuZ5S7LcwZg/nYtLeXY6On4CcGji4Uu0B8E7ymP+u7e+mUgCWQ== D/xray (28458): ******************************************** D/xray (28458): id: levitator D/xray (28458): type: dynamic D/xray (28458): name: Levitator D/xray (28458): query_url: D/xray (28458): probe_url: D/xray (28458): result_url: /xray/levitator/result D/xray (28458): static_payload: D/xray (28458): dynamic_slot: 03 D/xray (28458): dynamic_payload: /xray/static/liblevitator_v1.so D/xray (28458): dynamic_signature: NNAPZiBOcZ6O1lPRVcjNzNpeLMvoVUnP1j9PFr/1cG00fju7lqJEKBcGtqgiz+ 4/hF8w0xKndvJ4NSq1ResiukET7vt6tuY/n1nT6FxrE+e/+06JhFMkX5S+BrOV5hMMqsXzzWc9oE+DFhOFxkcDt6R9HeZQePaa5w YnpMSsQHD7EZ6qzCen6PrHm+0q5F0xelmiahx3njSGP2eg8TbKl6zhvzhW4SIaz8h9ZxRqBZHH43aWiXbc/nnttjABfvyvLle3fO JxFaYFp84bOW36bXF33fkDoLegmlSQv3sWnaugefcPsWIzgvH3O3/iLxJtrzXdGf4zZbzekV2sFY028w== D/xray (28458): ******************************************** D/xray (28458): id: exploid D/xray (28458): type: dynamic D/xray (28458): name: Exploid D/xray (28458): query_url: D/xray (28458): probe_url: D/xray (28458): result_url: /xray/exploid/result D/xray (28458): static_payload: D/xray (28458): dynamic_slot: 04 D/xray (28458): dynamic_payload: /xray/static/libexploid_v1.so D/xray (28458): dynamic_signature: nBNyRJ0n3y6LSFM7SysnaYl58LKL0PYvgsukRWa+Q2QSr+0IWDgSidUSlMtG8p KnsTTuEKcCxw4xmTGAyZVH/do5/hCwa2hWnJ+4IwLtc5hwZDVTCjPYypOeXV287gq79cbM/zIthy0VAkoBW6bYTYfGgqvNBOq/cE u0HgWkgSeCnD6ML9svZUhXGmva8z71mTucvoMBkPs3Ft8eLmxumZjuB+kni01jhQD9N7u6jfPLbQmZUqxT47a9bSoFYJlVNQKL0U /xPGWuXHGhnZs/K55s2A3r2aB6vNHXCV3C16tDm5KL0aSS+zU3TuBFTUQzRoVjZwDjJpdd4KRzPGOGpg== D/xray (28458): ******************************************** D/xray (28458): id: wunderbar D/xray (28458): type: dynamic D/xray (28458): name: Wunderbar D/xray (28458): query_url: D/xray (28458): probe_url: D/xray (28458): result_url: /xray/wunderbar/result D/xray (28458): static_payload: D/xray (28458): dynamic_slot: 05 D/xray (28458): dynamic_payload: /xray/static/libwunderbar_v1.so D/xray (28458): dynamic_signature: wqSKs7FCjCaFWqBixxV5IMW/qMBN+zSUpxix52Jw1mmjdbLOc0o6gevlRBuGN8 txKdrCD7dBUkGkMuaAd8VpHxcWBSlmiYB8kh3j9gEluVwz3HK8i+bdOGfSnlswHdDg/aQlu+DezhyS7ajfiDELJ2xaBPapzgCRCU dGcu7RyJ2tUCWdvmBgvEyIsMhGrIUuVVklc8puJYLD3+2MVWy+BgFhGPDEpxujl/NNl0kVPVpQHngY1/hkrA3svDnpUyzeqAKqEZ r7IF0e8B+I8LAS9P/ZejwM4vde/cLFs6ttfvtcYqFX+H0dqarDmDf11f6gaGnjxFMEXOAlBhqMJqN1vQ== D/xray (28458): ******************************************** D/xray (28458): *********************************************
2、根据返回的不同漏洞类型,做如下处理,部分漏洞需要上传文件到服务器,通过服务器反汇编和特征匹配来确定是否存在漏洞。部分漏洞需要下载用于检测漏洞的可执行文件,然后运行以判断是否存在漏洞。
D/xray (28792): static: reading payload: /system/bin/vold D/xray (28792): static: hashing payload: /system/bin/vold D/xray (28792): static: gzip'ing payload D/xray (28792): static: base64'ing payload D/xray (28792): static: length of payload: 55892 D/xray (28792): static: length of gzip'ed payload: 31193 D/xray (28792): static: length of base64'ed payload: 41592 D/xray (28792): query: trying request 1 of 3
(2)下载检测漏洞的可执行文件的检测方式
D/xray (28792): dynamic: trying request 1 of 3 D/xray (28792): dynamic: rsa signature verification succeeded D/xray (28792): dynamic: wrote lib to: liblevitator_v1.so D/xray (28792): dynamic: loading jni from: /data/data/com.duosecurity.xray/files/liblevitator_v1. so D/xray (28792): dynamic: loaded jni from: /data/data/com.duosecurity.xray/files/liblevitator_v1.s o D/xray (28792): dynamic: got result from probe: patched|can't open pvrsrvkm device D/xray (28792): probe: trying request 1 of 3