- Cisco SD-WAN (Viptela) 20.15.1 发布,新增功能概览
sysin.org
CiSCOCiscoSD-WANViptela思科SDN软件定义广域网
CiscoSD-WAN(Viptela)version20.15.1ED-软件定义广域网CiscoSD-WANpoweredbyViptela请访问原文链接:https://sysin.org/blog/cisco-sd-wan-20/,查看最新版。原创作品,转载请保留出处。作者主页:sysin.org支持SASE的架构,其集成了面向多云、安全、统一通信和应用优化的各种功能,可用于轻松安全地将任何
- 思科路由器交换机密码破解过程详解
zhane_hao
路由启动过程加电自检(POST)加载bootstrap代码检查配置寄存器寻找CiscoIOS加载CiscoIOS寻找配置文件加载配置文件若没有配置文件,进入Setup模式,进行初始化配置运行路由器操作系统查看命令•showversion:检查配置寄存器的值,硬件配置,IOS版本•showflash:检查Flash中的IOS,或是flash大小,使用情况(占用多少,剩下多少)•showstartup
- CTF——web方向学习攻略
一则孤庸
CTF网络安全CTF
1计算机基础操作系统:熟悉Linux命令,方便使用Kali。网络技术:HCNA、CCNA。编程能力:拔高项,有更好。2web应用HTTP协议:必须掌握web开发框架web安全测试3数据库数据库基本操作SQL语句数据库优化4刷题
- 掌握Cisco Packet Tracer:实现不同VLAN间的无缝通信
小柒笔记
网络协议
在当今的网络环境中,虚拟局域网(VLAN)已经成为网络设计和管理的核心部分。VLAN技术允许我们在物理网络上创建多个逻辑网络,提高网络性能和安全性。本篇文章将详细介绍如何使用CiscoPacketTracer软件进行不同VLAN间的通信配置。实验目标理解VLAN的基本概念:包括VLAN的作用、如何创建和分配VLAN。配置交换机以支持VLAN:学习如何在交换机上创建VLAN,并将端口分配给特定VLA
- 思科协作2018-IPT大项目随想
taoza
今年还有IPT的大项目,不容易。呵呵。CiscoIPPhone8800SeriesAdministrationGuideforCiscoUnifiedCommunicationsManagerhttps://www.cisco.com/c/en/us/td/docs/voice_ip_comm/cuipph/8800-series/english/adminguide/P881_BK_C13678
- Amqp协议的说明和使用场景
猰貐的新时代
python开发语言
引言本文围绕Amqp协议,为大家详细解析Amqp协议、核心技术亮点、多协议之间的对比以及使用实践,并介绍华为云IoT通过Amqp协议如何为开发者和企业提供了更加灵活和高效的通信方式,使得物联网应用得以在各个领域得到更广泛的推广和应用。AMQP协议,全称为AdvancedMessageQueuingProtocol。在2006年6月,由Cisco、Redhat、iMatrix等联合制定了AMQP的消
- 华为、Cisco、锐捷三家网络设备供应商的常用网络命令对比
Network_Engineer
RS网络华为服务器
对比华为、思科和锐捷三家网络设备厂商的常用配置命令,能帮助网络工程师和技术人员在选择设备和配置时做出更明智的决策。这种对比不仅有助于了解各厂商设备的功能和命令差异,还能提高配置效率,减少学习和适应时间,从而优化网络管理和维护。此外,深入理解这些配置命令的优缺点,有助于更好地进行网络架构设计和性能优化。华为设备常用配置命令进入全局配置模式system-view配置接口interfaceGigabit
- cisco Switching-以太通道配置
凯歌响起
问题企业需要增加带宽和网络可用性,以太通道可以同时满足这两个条件,而又无需购买新设备。方案以太通道也称为以太端口捆绑、端口聚集或以太链路聚集,通过端口聚集协议(PAgP)建立以太通道.最多可以捆绑8条物理链路,可以是双绞线,也可以是光纤。前提要求参与捆绑的端口必须属于同一个VLAN,或者都是中继模式如果端口配置是中继模式,则链路中的两个端口必须都是中继模式所有参与捆绑的端口的物理参数必须相同,例如
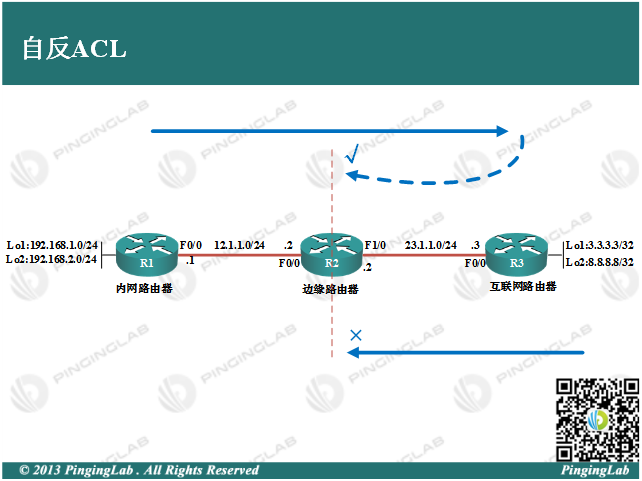
- ACL访问控制列表
期待未来的男孩
安全设备路由交换网络安全
ciscoACL分类:标准访问控制列表(调用在接近源设备上)1-99只能对源进行控管扩展访问控制列表(调用在接近目标设备上)100-199命名访问控制列表时间访问控制列表acl运行规则:一.依据序列号对ACL进行逐条匹配(顺序性)二.匹配中ACL中的一条列表既结束ACL过滤动作(匹配任意一条,就跳出ACL动作)三.列表尾部隐式拒绝所有(ACL默认拒绝所有流量通过)四.不能过滤本地产生的流量(ACL
- 思科、华为认证考试详细介绍
小云晓云
思科认证:思科认证报名网站:https://home.pearsonvue.com/ciscoCCNA认证——思科认证网络支持工程师考一个科目:200-301考试时间是120分钟,考题分为四部分:选择、拖拽、模拟、实验,总分1000分,通过分数825分,考试费为195美元。CCNA认证的有效期CCNA证书的有效期为3年,3年之内需要参加重认证(Recertification)的考试。CCNP认证—
- Cisco ACI Leaf交换机日志怎么查看
funnycoffee123
前端服务器运维
SSH命令行登录Leaf交换机后切换到/var/log/external这个目录下,下面的messege文件就是日志文件ACI-93180#cd/var/log/externalACI-93180#pwd/var/log/externalACI-93180#ls-ltotal18100lrwxrwxrwx1rootroot31Mar302023dmesg->/mnt/pss/bootlogs/cu
- 用usb更新Cisco IOS 示例与命令,不需要用tftp
hu5566798
服务器运维
UsingaUSBflashdrivetocopyIOStoCiscodevicesAlittlebackgroundBeforewegetstarted,let’sreviewsomeofthespecificsyouneedtoknowaboutusingUSBflashandCFcardswithCiscorouters.TheCiscoIOScanonlyreadFAT-formatted
- 【学网攻】 第(28)节 -- OSPF虚链路
可惜已不在
网络攻击网络安全
系列文章目录目录系列文章目录文章目录前言一、什么是OSPF虚链路?二、实验1.引入实验目标实验背景技术原理实验步骤实验设备实验拓扑图实验配置扩展实验拓扑图实验配置实验验证文章目录【学网攻】第(1)节--认识网络【学网攻】第(2)节--交换机认识及使用【学网攻】第(3)节--交换机配置聚合端口【学网攻】第(4)节--交换机划分Vlan【学网攻】第(5)节--CiscoVTP的使用【学网攻】第(6)节
- 计网实验三 路由器和交换机配置实验
柠檬茶五元
智能路由器网络
一、实验目的1.了解路由器和交换机的工作模式和使用方法;2.熟悉Cisco网络设备的基本配置命令;3.掌握Cisco路由器的基本配置方式及配置命令;4.掌握路由器和交换机的基本配置与管理方法。二、实验要求1.按网络应用需求设计网络拓扑结构;2.按网络设计要求完成路由器和交换机的基本配置;3.配置PC机的IP地址、子网掩码及默认网关;4.进行网络连通性测试;5.在实验报告上详细记录实验的每一个步骤和
- 【学网攻】 第(27)节 -- HSRP(热备份路由器协议)
可惜已不在
网络攻击网络安全
系列文章目录目录系列文章目录文章目录前言一、HSRP(热备份路由器协议)是什么?二、实验1.引入实验目标实验背景技术原理实验步骤实验设备实验拓扑图实验配置实验验证文章目录【学网攻】第(1)节--认识网络【学网攻】第(2)节--交换机认识及使用【学网攻】第(3)节--交换机配置聚合端口【学网攻】第(4)节--交换机划分Vlan【学网攻】第(5)节--CiscoVTP的使用【学网攻】第(6)节--三层
- 【学网攻】 第(29)节 -- 综合实验二
可惜已不在
网络攻击网络安全
系列文章目录目录系列文章目录文章目录前言一、综合实验二、实验1.引入实验目标实验设备实验拓扑图实验配置实验验证文章目录【学网攻】第(1)节--认识网络【学网攻】第(2)节--交换机认识及使用【学网攻】第(3)节--交换机配置聚合端口【学网攻】第(4)节--交换机划分Vlan【学网攻】第(5)节--CiscoVTP的使用【学网攻】第(6)节--三层交换机实现VLAN间路由【学网攻】第(7)节--生成
- Cisco Secure Client 5.1.2.42 (macOS, Linux, Windows & iOS, Andrord) - 远程访问客户端
sysin.org
CiSCOmacoslinuxwindowsanyconnect
CiscoSecureClient5.1.2.42(macOS,Linux,Windows&iOS,Andrord)-远程访问客户端思科安全客户端(包括AnyConnect)06-Feb-2024请访问原文链接:CiscoSecureClient5.1.2.42(macOS,Linux,Windows&iOS,Andrord)-VPN和远程访问客户端,查看最新版。原创作品,转载请保留出处。作者主页
- 【学网攻】 第(26)节 -- 综合网络实验一
可惜已不在
网络攻击网络
系列文章目录目录系列文章目录文章目录前言一、综合实验二、实验1.引入实验目标实验设备实验拓扑图实验配置文章目录【学网攻】第(1)节--认识网络【学网攻】第(2)节--交换机认识及使用【学网攻】第(3)节--交换机配置聚合端口【学网攻】第(4)节--交换机划分Vlan【学网攻】第(5)节--CiscoVTP的使用【学网攻】第(6)节--三层交换机实现VLAN间路由【学网攻】第(7)节--生成树配置【
- 【学网攻】 第(25)节 -- 帧中继(多对一)
可惜已不在
网络攻击网络安全
系列文章目录目录系列文章目录文章目录前言一、帧中继是什么?二、实验1.引入实验目标理解帧中继在广域网中的原理及功能;实验背景技术原理实验步骤实验设备实验拓扑图编辑实验配置实验验证文章目录【学网攻】第(1)节--认识网络【学网攻】第(2)节--交换机认识及使用【学网攻】第(3)节--交换机配置聚合端口【学网攻】第(4)节--交换机划分Vlan【学网攻】第(5)节--CiscoVTP的使用【学网攻】第
- 【解决方案】pyspark 初次连接mongo 时报错Class not found exception:com.mongodb.spark.sql.DefaultSource
能白话的程序员♫
Sparkspark
部分报错如下:Traceback(mostrecentcalllast): File"/home/cisco/spark-mongo-test.py",line7,in df=spark.read.format("com.mongodb.spark.sql.DefaultSource").load() File"/home/cisco/spark-2.4.1-bin-hadoop2.
- Chapter 8 - 9. Congestion Management in TCP Storage Networks
mounter625
Linuxkernel网络tcp/ip服务器
EstimatingI/OFlowPerformancefromTCPFlowPerformanceAsmentionedearlier,atthetimeofthiswriting,performancemonitoringofI/OflowsisnotavailableinEthernetswitches.However,someswitches(suchasCiscoNexus9000)ca
- cisco Switching-密码恢复
凯歌响起
密码恢复断开交换机的电源并重新给交换机加电,在给交换机加电的同时按住交换机前面板上的“模式(Mode)”按钮几秒钟,仔细观察超级终端程序中显示的交换机启动信息。待出现交换机提示符switch:后,输入flash_init命令。待上述命令执行完成后,输入load_helper命令。(有的不需要如果显示flash_initboot则不需要)待上述命令执行完成后,输入dirflash:命令查看闪存中的文
- Cisco 模块4 - 7:以太网的概念考试
临风.
Cisco网络网络协议
Cisco模块4-7:以太网的概念考试文章目录Cisco模块4-7:以太网的概念考试1、拖拽题2、网络管理员正在测量一个任务关键型财务应用通过公司主干网络传输位的情况。管理员注意到网络吞吐量似乎低于预期的带宽。下列哪三个因素可能会影响吞吐量差异?(选择三项。)3、下列哪两项是光缆的特征?(选择两项。)4、在网络上传输数据的过程中,物理层的主要作用是什么?5、在网络中使用未屏蔽的双绞线铜线时,是什么
- Cisco 模块 1 - 3:基本网络连接和通信考试
临风.
Cisco网络运维服务器
Cisco模块1-3:基本网络连接和通信考试文章目录Cisco模块1-3:基本网络连接和通信考试第一类:网络组件一、主机第53题第55题二、点对点三、终端设备四、中间设备五、网络介质第6题第二类:网络框架的四个基本特性一、容错能力二、可扩展性三、服务质量(QoS)第7题第58题四、安全性第1题第4题第三类:常见网络类型一、按网络规格分类第54题二、按网络基础设施类型分类三、按访问类型分类第2题第5
- Cisco Packet Tracer 4.7.2 连接物理层
临风.
Cisco网络运维服务器
连接物理层文章目录连接物理层背景信息第1部分:确定网络互连设备的物理特征步骤1:识别思科路由器的管理端口。步骤2:识别思科路由器的LAN和WAN接口。步骤3:识别模块扩展插槽。第2部分:选择正确的模块进行连接步骤1:确定哪些模块提供了所需的连接。步骤2:添加正确的模块并启动设备。第3部分:连接设备第4部分:检查连接性步骤1:检查East中接口的状态。步骤2:连接无线设备:笔记本电脑和平板电脑。步骤
- IT行业有哪些证书含金量高?
youmatech
经验分享
在IT行业,有一些证书被广泛认可并被认为具有较高的含金量。以下是一些在IT行业中被认为有价值的证书:Cisco认证(CCNA、CCNP、CCIE):Cisco的网络认证是网络领域最受尊重的证书之一。CCNA(CiscoCertifiedNetworkAssociate)、CCNP(CiscoCertifiedNetworkProfessional)和CCIE(CiscoCertifiedInter
- 话题:IT行业有哪些证书含金量高?
小桥流水---人工智能
机器学习算法人工智能深度学习
IT行业有哪些证书含金量高?1.以下是一些在IT行业中我认为具有高含金量的证书:思科认证(CiscoCertifications):思科认证是由网络领域的著名厂商——Cisco公司推出的,是互联网领域的国际权威认证。这个认证体系包含了多个不同级别、不同内容、不同方向的各种认证,如CCNA、CCDA、CCNP、CCDP、CCSP、CCIP、CCVP、CCIE等。其中,CCIE是专家级认证,具有极高的
- 有关网络安全的课程学习网页
Passion-优
学习
1.思科网络学院免费学习skillsforall的课程课程链接:IntroductiontoCybersecuritybyCisco:FreeOnlineCourse(skillsforall.com)2.斯坦福大学计算机和网络安全基础该证书对于初学者来说最有价值,它由最著名的大学之一斯坦福大学提供。您可以免费学习它。它提供了有关安全基础知识、计算机网络及其执行方式的基本概念。课程链接:Cyber
- 【学网攻】 第(21)节 -- DHCP配置
可惜已不在
网络攻击网络安全
系列文章目录目录系列文章目录文章目录前言二、实验1.引入实验目的实验步骤实验设备实验拓扑图实验配置实验验证总结文章目录【学网攻】第(1)节--认识网络【学网攻】第(2)节--交换机认识及使用【学网攻】第(3)节--交换机配置聚合端口【学网攻】第(4)节--交换机划分Vlan【学网攻】第(5)节--CiscoVTP的使用【学网攻】第(6)节--三层交换机实现VLAN间路由【学网攻】第(7)节--生成
- 【学网攻】 第(24)节 -- 帧中继(点对点)
可惜已不在
网络攻击网络安全
系列文章目录目录系列文章目录文章目录前言一、帧中继是什么?二、实验1.引入实验拓扑图实验配置在帧中继中配置通信链路编辑实验验证文章目录【学网攻】第(1)节--认识网络【学网攻】第(2)节--交换机认识及使用【学网攻】第(3)节--交换机配置聚合端口【学网攻】第(4)节--交换机划分Vlan【学网攻】第(5)节--CiscoVTP的使用【学网攻】第(6)节--三层交换机实现VLAN间路由【学网攻】第
- 桌面上有多个球在同时运动,怎么实现球之间不交叉,即碰撞?
换个号韩国红果果
html小球碰撞
稍微想了一下,然后解决了很多bug,最后终于把它实现了。其实原理很简单。在每改变一个小球的x y坐标后,遍历整个在dom树中的其他小球,看一下它们与当前小球的距离是否小于球半径的两倍?若小于说明下一次绘制该小球(设为a)前要把他的方向变为原来相反方向(与a要碰撞的小球设为b),即假如当前小球的距离小于球半径的两倍的话,马上改变当前小球方向。那么下一次绘制也是先绘制b,再绘制a,由于a的方向已经改变
- 《高性能HTML5》读后整理的Web性能优化内容
白糖_
html5
读后感
先说说《高性能HTML5》这本书的读后感吧,个人觉得这本书前两章跟书的标题完全搭不上关系,或者说只能算是讲解了“高性能”这三个字,HTML5完全不见踪影。个人觉得作者应该首先把HTML5的大菜拿出来讲一讲,再去分析性能优化的内容,这样才会有吸引力。因为只是在线试读,没有机会看后面的内容,所以不胡乱评价了。
- [JShop]Spring MVC的RequestContextHolder使用误区
dinguangx
jeeshop商城系统jshop电商系统
在spring mvc中,为了随时都能取到当前请求的request对象,可以通过RequestContextHolder的静态方法getRequestAttributes()获取Request相关的变量,如request, response等。 在jshop中,对RequestContextHolder的
- 算法之时间复杂度
周凡杨
java算法时间复杂度效率
在
计算机科学 中,
算法 的时间复杂度是一个
函数 ,它定量描述了该算法的运行时间。这是一个关于代表算法输入值的
字符串 的长度的函数。时间复杂度常用
大O符号 表述,不包括这个函数的低阶项和首项系数。使用这种方式时,时间复杂度可被称为是
渐近 的,它考察当输入值大小趋近无穷时的情况。
这样用大写O()来体现算法时间复杂度的记法,
- Java事务处理
g21121
java
一、什么是Java事务 通常的观念认为,事务仅与数据库相关。 事务必须服从ISO/IEC所制定的ACID原则。ACID是原子性(atomicity)、一致性(consistency)、隔离性(isolation)和持久性(durability)的缩写。事务的原子性表示事务执行过程中的任何失败都将导致事务所做的任何修改失效。一致性表示当事务执行失败时,所有被该事务影响的数据都应该恢复到事务执行前的状
- Linux awk命令详解
510888780
linux
一. AWK 说明
awk是一种编程语言,用于在linux/unix下对文本和数据进行处理。数据可以来自标准输入、一个或多个文件,或其它命令的输出。它支持用户自定义函数和动态正则表达式等先进功能,是linux/unix下的一个强大编程工具。它在命令行中使用,但更多是作为脚本来使用。
awk的处理文本和数据的方式:它逐行扫描文件,从第一行到
- android permission
布衣凌宇
Permission
<uses-permission android:name="android.permission.ACCESS_CHECKIN_PROPERTIES" ></uses-permission>允许读写访问"properties"表在checkin数据库中,改值可以修改上传
<uses-permission android:na
- Oracle和谷歌Java Android官司将推迟
aijuans
javaoracle
北京时间 10 月 7 日,据国外媒体报道,Oracle 和谷歌之间一场等待已久的官司可能会推迟至 10 月 17 日以后进行,这场官司的内容是 Android 操作系统所谓的 Java 专利权之争。本案法官 William Alsup 称根据专利权专家 Florian Mueller 的预测,谷歌 Oracle 案很可能会被推迟。 该案中的第二波辩护被安排在 10 月 17 日出庭,从目前看来
- linux shell 常用命令
antlove
linuxshellcommand
grep [options] [regex] [files]
/var/root # grep -n "o" *
hello.c:1:/* This C source can be compiled with:
- Java解析XML配置数据库连接(DOM技术连接 SAX技术连接)
百合不是茶
sax技术Java解析xml文档dom技术XML配置数据库连接
XML配置数据库文件的连接其实是个很简单的问题,为什么到现在才写出来主要是昨天在网上看了别人写的,然后一直陷入其中,最后发现不能自拔 所以今天决定自己完成 ,,,,现将代码与思路贴出来供大家一起学习
XML配置数据库的连接主要技术点的博客;
JDBC编程 : JDBC连接数据库
DOM解析XML: DOM解析XML文件
SA
- underscore.js 学习(二)
bijian1013
JavaScriptunderscore
Array Functions 所有数组函数对参数对象一样适用。1.first _.first(array, [n]) 别名: head, take 返回array的第一个元素,设置了参数n,就
- plSql介绍
bijian1013
oracle数据库plsql
/*
* PL/SQL 程序设计学习笔记
* 学习plSql介绍.pdf
* 时间:2010-10-05
*/
--创建DEPT表
create table DEPT
(
DEPTNO NUMBER(10),
DNAME NVARCHAR2(255),
LOC NVARCHAR2(255)
)
delete dept;
select
- 【Nginx一】Nginx安装与总体介绍
bit1129
nginx
启动、停止、重新加载Nginx
nginx 启动Nginx服务器,不需要任何参数u
nginx -s stop 快速(强制)关系Nginx服务器
nginx -s quit 优雅的关闭Nginx服务器
nginx -s reload 重新加载Nginx服务器的配置文件
nginx -s reopen 重新打开Nginx日志文件
- spring mvc开发中浏览器兼容的奇怪问题
bitray
jqueryAjaxspringMVC浏览器上传文件
最近个人开发一个小的OA项目,属于复习阶段.使用的技术主要是spring mvc作为前端框架,mybatis作为数据库持久化技术.前台使用jquery和一些jquery的插件.
在开发到中间阶段时候发现自己好像忽略了一个小问题,整个项目一直在firefox下测试,没有在IE下测试,不确定是否会出现兼容问题.由于jquer
- Lua的io库函数列表
ronin47
lua io
1、io表调用方式:使用io表,io.open将返回指定文件的描述,并且所有的操作将围绕这个文件描述
io表同样提供三种预定义的文件描述io.stdin,io.stdout,io.stderr
2、文件句柄直接调用方式,即使用file:XXX()函数方式进行操作,其中file为io.open()返回的文件句柄
多数I/O函数调用失败时返回nil加错误信息,有些函数成功时返回nil
- java-26-左旋转字符串
bylijinnan
java
public class LeftRotateString {
/**
* Q 26 左旋转字符串
* 题目:定义字符串的左旋转操作:把字符串前面的若干个字符移动到字符串的尾部。
* 如把字符串abcdef左旋转2位得到字符串cdefab。
* 请实现字符串左旋转的函数。要求时间对长度为n的字符串操作的复杂度为O(n),辅助内存为O(1)。
*/
pu
- 《vi中的替换艺术》-linux命令五分钟系列之十一
cfyme
linux命令
vi方面的内容不知道分类到哪里好,就放到《Linux命令五分钟系列》里吧!
今天编程,关于栈的一个小例子,其间我需要把”S.”替换为”S->”(替换不包括双引号)。
其实这个不难,不过我觉得应该总结一下vi里的替换技术了,以备以后查阅。
1
所有替换方案都要在冒号“:”状态下书写。
2
如果想将abc替换为xyz,那么就这样
:s/abc/xyz/
不过要特别
- [轨道与计算]新的并行计算架构
comsci
并行计算
我在进行流程引擎循环反馈试验的过程中,发现一个有趣的事情。。。如果我们在流程图的每个节点中嵌入一个双向循环代码段,而整个流程中又充满着很多并行路由,每个并行路由中又包含着一些并行节点,那么当整个流程图开始循环反馈过程的时候,这个流程图的运行过程是否变成一个并行计算的架构呢?
- 重复执行某段代码
dai_lm
android
用handler就可以了
private Handler handler = new Handler();
private Runnable runnable = new Runnable() {
public void run() {
update();
handler.postDelayed(this, 5000);
}
};
开始计时
h
- Java实现堆栈(list实现)
datageek
数据结构——堆栈
public interface IStack<T> {
//元素出栈,并返回出栈元素
public T pop();
//元素入栈
public void push(T element);
//获取栈顶元素
public T peek();
//判断栈是否为空
public boolean isEmpty
- 四大备份MySql数据库方法及可能遇到的问题
dcj3sjt126com
DBbackup
一:通过备份王等软件进行备份前台进不去?
用备份王等软件进行备份是大多老站长的选择,这种方法方便快捷,只要上传备份软件到空间一步步操作就可以,但是许多刚接触备份王软件的客用户来说还原后会出现一个问题:因为新老空间数据库用户名和密码不统一,网站文件打包过来后因没有修改连接文件,还原数据库是好了,可是前台会提示数据库连接错误,网站从而出现打不开的情况。
解决方法:学会修改网站配置文件,大多是由co
- github做webhooks:[1]钩子触发是否成功测试
dcj3sjt126com
githubgitwebhook
转自: http://jingyan.baidu.com/article/5d6edee228c88899ebdeec47.html
github和svn一样有钩子的功能,而且更加强大。例如我做的是最常见的push操作触发的钩子操作,则每次更新之后的钩子操作记录都会在github的控制板可以看到!
工具/原料
github
方法/步骤
- ">的作用" target="_blank">JSP中的作用
蕃薯耀
JSP中<base href="<%=basePath%>">的作用
>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>
- linux下SAMBA服务安装与配置
hanqunfeng
linux
局域网使用的文件共享服务。
一.安装包:
rpm -qa | grep samba
samba-3.6.9-151.el6.x86_64
samba-common-3.6.9-151.el6.x86_64
samba-winbind-3.6.9-151.el6.x86_64
samba-client-3.6.9-151.el6.x86_64
samba-winbind-clients
- guava cache
IXHONG
cache
缓存,在我们日常开发中是必不可少的一种解决性能问题的方法。简单的说,cache 就是为了提升系统性能而开辟的一块内存空间。
缓存的主要作用是暂时在内存中保存业务系统的数据处理结果,并且等待下次访问使用。在日常开发的很多场合,由于受限于硬盘IO的性能或者我们自身业务系统的数据处理和获取可能非常费时,当我们发现我们的系统这个数据请求量很大的时候,频繁的IO和频繁的逻辑处理会导致硬盘和CPU资源的
- Query的开始--全局变量,noconflict和兼容各种js的初始化方法
kvhur
JavaScriptjquerycss
这个是整个jQuery代码的开始,里面包含了对不同环境的js进行的处理,例如普通环境,Nodejs,和requiredJs的处理方法。 还有jQuery生成$, jQuery全局变量的代码和noConflict代码详解 完整资源:
http://www.gbtags.com/gb/share/5640.htm jQuery 源码:
(
- 美国人的福利和中国人的储蓄
nannan408
今天看了篇文章,震动很大,说的是美国的福利。
美国医院的无偿入院真的是个好措施。小小的改善,对于社会是大大的信心。小孩,税费等,政府不收反补,真的体现了人文主义。
美国这么高的社会保障会不会使人变懒?答案是否定的。正因为政府解决了后顾之忧,人们才得以倾尽精力去做一些有创造力,更造福社会的事情,这竟成了美国社会思想、人
- N阶行列式计算(JAVA)
qiuwanchi
N阶行列式计算
package gaodai;
import java.util.List;
/**
* N阶行列式计算
* @author 邱万迟
*
*/
public class DeterminantCalculation {
public DeterminantCalculation(List<List<Double>> determina
- C语言算法之打渔晒网问题
qiufeihu
c算法
如果一个渔夫从2011年1月1日开始每三天打一次渔,两天晒一次网,编程实现当输入2011年1月1日以后任意一天,输出该渔夫是在打渔还是在晒网。
代码如下:
#include <stdio.h>
int leap(int a) /*自定义函数leap()用来指定输入的年份是否为闰年*/
{
if((a%4 == 0 && a%100 != 0
- XML中DOCTYPE字段的解析
wyzuomumu
xml
DTD声明始终以!DOCTYPE开头,空一格后跟着文档根元素的名称,如果是内部DTD,则再空一格出现[],在中括号中是文档类型定义的内容. 而对于外部DTD,则又分为私有DTD与公共DTD,私有DTD使用SYSTEM表示,接着是外部DTD的URL. 而公共DTD则使用PUBLIC,接着是DTD公共名称,接着是DTD的URL.
私有DTD
<!DOCTYPErootSYST