CCNP实验:GRE隧道流量的IPSEC加密
CCNP实验:GRE隧道流量及ipsec配置
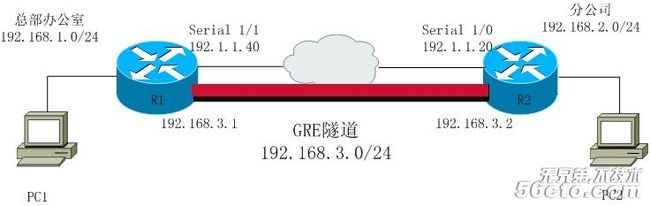
由于IPSEC只支持对单播流量的加密,所以我们使用GRE隧道可以将广播、组播包封装在一个单播包中,再用IPSEC进行加密。
在进行IPSEC配置前应首先配置好GRE隧道,下面是R1上的GRE隧道配置:
R1:
interface tunnel0
ip address 192.168.3.1 255.255.255.0
tunnel source s1/1
tunnel destination 192.1.1.20
exit
interface s1/1
ip address 192.1.1.40 255.255.255.0
ip access-group perimeter in
exit
interface lo0
ip address 192.168.1.1 255.255.255.0
exit
ip route 0.0.0.0 0.0.0.0 192.1.1.20
ip address 192.168.3.1 255.255.255.0
tunnel source s1/1
tunnel destination 192.1.1.20
exit
interface s1/1
ip address 192.1.1.40 255.255.255.0
ip access-group perimeter in
exit
interface lo0
ip address 192.168.1.1 255.255.255.0
exit
ip route 0.0.0.0 0.0.0.0 192.1.1.20
!在这里我将总公司内部的骨干网络设为Area0,隧道部分和分公司内部网络设为Area1
router ospf 1
network 192.168.1.0 0.0.0.255 area 0
network 192.168.3.0 0.0.0.255 area 1
exit
router ospf 1
network 192.168.1.0 0.0.0.255 area 0
network 192.168.3.0 0.0.0.255 area 1
exit
ip access-list extended perimeter
permit udp host 192.1.1.20 host 192.1.1.40 eq 500
permit esp host 193.1.1.20 host 192.1.1.40
permit gre host 193.1.1.20 host 192.1.1.40
deny ip any any
exit
permit udp host 192.1.1.20 host 192.1.1.40 eq 500
permit esp host 193.1.1.20 host 192.1.1.40
permit gre host 193.1.1.20 host 192.1.1.40
deny ip any any
exit
R2:
interface tunnel0
ip address 192.168.3.2 255.255.255.0
tunnel source s1/0
tunnel destination 192.1.1.40
exit
interface s1/0
ip address 192.1.1.20 255.255.255.0
ip access-group perimeter in
exit
interface lo0
ip address 192.168.2.1 255.255.255.0
exit
ip route 0.0.0.0 0.0.0.0 192.1.1.40
ip address 192.168.3.2 255.255.255.0
tunnel source s1/0
tunnel destination 192.1.1.40
exit
interface s1/0
ip address 192.1.1.20 255.255.255.0
ip access-group perimeter in
exit
interface lo0
ip address 192.168.2.1 255.255.255.0
exit
ip route 0.0.0.0 0.0.0.0 192.1.1.40
router ospf 1
network 192.168.2.0 0.0.0.255 area 1
network 192.168.3.0 0.0.0.255 area 1
exit
network 192.168.2.0 0.0.0.255 area 1
network 192.168.3.0 0.0.0.255 area 1
exit
ip access-list extended perimeter
permit udp host 192.1.1.40 host 192.1.1.20 eq 500
permit esp host 192.1.1.40 host 192.1.1.20
permit gre host 192.1.1.40 host 192.1.1.20
deny ip any any
exit
permit udp host 192.1.1.40 host 192.1.1.20 eq 500
permit esp host 192.1.1.40 host 192.1.1.20
permit gre host 192.1.1.40 host 192.1.1.20
deny ip any any
exit
GRE隧道建立好后,就可以进行IPSEC配置了:
R1上的配置:
crypto isakmp enable
crypto isakmp identity address
crypto isakmp policy 10
encryption aes
authentication pre-share
group 2
hash sha
exit
crypto isakmp identity address
crypto isakmp policy 10
encryption aes
authentication pre-share
group 2
hash sha
exit
crypto isakmp key cisco123 address 192.1.1.20 no-xauth
!IPSEC只对进入GRE隧道的流量进行加密
ip access-list extended ToR2
permit gre host 192.1.1.40 host 192.1.1.20
exit
ip access-list extended ToR2
permit gre host 192.1.1.40 host 192.1.1.20
exit
!这里的GRE隧道是点对点模式的,所以传输集应使用传输模式
crypto ipsec transform-set trans esp-aes esp-sha-hmac
mode transport
exit
crypto ipsec transform-set trans esp-aes esp-sha-hmac
mode transport
exit
crypto map mymap 10 ipsec-isakmp
match address ToR2
set transform-set trans
set peer 192.1.1.20
exit
match address ToR2
set transform-set trans
set peer 192.1.1.20
exit
interface s1/1
crypto map mymap
exit
crypto map mymap
exit
!最后别忘记删除测试隧道时建立的流量:
ip access-list extended perimeter
no permit gre host 192.1.1.20 host 192.1.1.40
ip access-list extended perimeter
no permit gre host 192.1.1.20 host 192.1.1.40
R2上的配置:
crypto isakmp enable
crypto isakmp identity address
crypto isakmp policy 10
encryption aes
authentication pre-share
group 2
hash sha
exit
crypto isakmp key cisco123 address 192.1.1.40 no-xauth
ip access-list extended ToR1
permit gre host 192.1.1.20 host 192.1.1.40
exit
crypto ipsec transform-set trans esp-aes esp-sha-hmac
mode transport
exit
crypto map mymap 10 ipsec-isakmp
match address ToR1
set transform-set trans
set peer 192.1.1.40
exit
interface s1/0
crypto map mymap
exit
ip access-list extended perimeter
no permit gre host 192.1.1.40 host 192.1.1.20
测试实验结果:
r1#sh ip route
Codes: C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route
Codes: C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route
Gateway of last resort is 192.1.1.20 to network 0.0.0.0
C 192.1.1.0/24 is directly connected, Serial1/1
C 192.168.1.0/24 is directly connected, Loopback0
192.168.2.0/32 is subnetted, 1 subnets
O 192.168.2.1 [110/11112] via 192.168.3.2, 00:00:17, Tunnel0
C 192.168.3.0/24 is directly connected, Tunnel0
S* 0.0.0.0/0 [1/0] via 192.1.1.20
C 192.168.1.0/24 is directly connected, Loopback0
192.168.2.0/32 is subnetted, 1 subnets
O 192.168.2.1 [110/11112] via 192.168.3.2, 00:00:17, Tunnel0
C 192.168.3.0/24 is directly connected, Tunnel0
S* 0.0.0.0/0 [1/0] via 192.1.1.20
R1上ping PC2:
r1#ping 192.168.2.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.2.1, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 36/56/84 ms
Sending 5, 100-byte ICMP Echos to 192.168.2.1, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 36/56/84 ms
PC1上ping PC2:
r1#ping 192.168.2.1 source lo0
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.2.1, timeout is 2 seconds:
Packet sent with a source address of 192.168.1.1
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 36/55/104 ms
Sending 5, 100-byte ICMP Echos to 192.168.2.1, timeout is 2 seconds:
Packet sent with a source address of 192.168.1.1
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 36/55/104 ms
本文出自 “直至网规” 博客,谢绝转载!