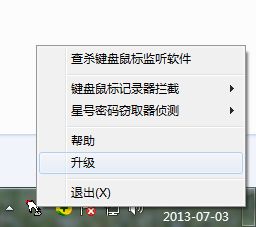
早年用WIN32汇编写的反键盘记录器
.486
.model flat, stdcall
option casemap :none
; #########################################################################
include windows.inc
include user32.inc
include kernel32.inc
include gdi32.inc
include masm32.inc
include anti-keyhookdll.inc
include d:\masm32\macros\strings.mac
include common.inc
include comctl32.inc
include advapi32.inc
include shell32.inc
includelib user32.lib
includelib kernel32.lib
includelib gdi32.lib
includelib masm32.lib
includelib anti-keyhookdll.lib
includelib comctl32.lib
includelib advapi32.lib
includelib shell32.lib
; #########################################################################
MENUID_ANTIKEYLOGOPEN equ 101
MENUID_ANTIKEYLOGCLOSE equ 102
MENUID_ANTIPASSREADOPEN equ 103
MENUID_ANTIPASSREADCLOSE equ 104
MENUID_EXIT equ 105
MENUID_HELP equ 106
MENUID_SHENGJI equ 107
MENUID_SCANHOOK equ 108
IDR_MAINFRAME equ 106
IDC_LIST equ 108
IDC_DELETE equ 109
IDC_DEL equ 110
IDC_SCAN equ 111
IDC_CLOSE equ 112
IDR_MAINMENU equ 113
DIALOG_MAIN equ 1
IDT_TIMER equ 1
WM_NOTIFYICONN equ WM_USER+0
ANTI_ON equ 0
ANTI_OFF equ 1
.data
szClassName db "antikey_class",0
stnidstatus NOTIFYICONDATA <>
szmes db "帮助",0
szmescap db "掂花反键盘鼠标记录器提醒您",0
szexist db "掂花反键盘鼠标记录器已经运行!不能重复运行!",0
sztooltip db "掂花反键盘鼠标记录器5.0",0
szerrcap db "错误",0
szerrmes db "驱动错误",0
szbegin db "启动",0
szstop db "停止",0
szstatusstop db "【掂花反键盘鼠标记录器当前工作状态: 停止】",0
szstatusbegin db "【掂花反键盘鼠标记录器当前工作状态: 正常】",0
szhelpwww db "http://8923704.ty168.net",0
szHandle db "监听句柄",0
szFunc db "监听函数地址",0
szType db "监听内容",0
szModule db "监听程序",0
szscan db "安全提示",0
szdllname db "antihook.dll",0
szsysdllname db "\MSCTF.dll",0
szkvdllname1 db "KASocket.dll",0
szkvdllname2 db "KMailOEBand.dll",0
sz360dllname db "\safemon\safemon.dll",0
szchajian db "\mprmsgse.axz",0
szFlags db "局部范围的菜单、滚动条、消息框、对话框操作 [WH_MSGFILTER]",0
db "windows从硬件队列中获得消息 [WH_JOURNALRECORD]",0
db "事件从系统硬件输入队列被请求 [WH_JOURNALPLAYBACK]",0
db "〖键盘操作〗 [WH_KEYBOARD]",0
db "〖读取消息队列〗 [WH_GETMESSAG]",0
db "〖向窗口发送消息(SendMessage)〗 [WH_CALLWNDPROC]",0
db "〖训练事件〗 [WH_CBT]",0
db "系统范围的菜单、滚动条、消息框、对话框操作 [WH_SYSMSGFILTER]",0
db "〖鼠标操作〗 [WH_MOUSE]",0
db "消息队列读取非鼠标、键盘消息 [WH_HARDWARE]",0
db "钩子函数除错 [WH_DEBUG]",0
db "WINDOWS外壳事件 [WH_SHELL]",0
szAlarm db "未知 ",0
db "未知 ",0
db "未知 ",0
db "可疑 ",0
db "可疑 ",0
db "可疑 ",0
db "未知 ",0
db "可疑 ",0
db "可疑 ",0
db "未知 ",0
db "未知 ",0
db "未知 ",0
szsafetype db "正常 ",0
; #########################################################################
.data?
CommandLine dd ?
hInstance dd ?
hList dd ?
hDevice dd ?
dwNum dd ?
hmenu DWORD ?
hicon HICON ?
hWinMain DWORD ?
isstop dd ?
szmodname db 200 dup(?)
szsysmodname db 200 dup(?)
szkvmodname1 db 200 dup(?)
szkvmodname2 db 200 dup(?)
sz360modname db 200 dup(?)
szmodpath db 200 dup(?)
; #########################################################################
DlgProc proto :DWORD,:DWORD,:DWORD,:DWORD
_OpenDevice proto
_CloseDevice proto
_deleteselhook proto :DWORD,:DWORD
_Init proto :DWORD
_Refresh proto
_InsertHookInfo proto :DWORD,:DWORD
_GetHookModuleName proto :DWORD,:DWORD
; #########################################################################
.code
_antipassread proc antiflag:DWORD
invoke Setantipass,antiflag
ret
_antipassread endp
; #########################################################################
_stophook proc
call UnInstallHook
ret
_stophook endp
; #########################################################################
_loadnewhook proc
call UnInstallHook
call InstallHook
ret
_loadnewhook endp
;; #########################################################################
;插件处理
_chajian proc
LOCAL FindFileData:WIN32_FIND_DATA
invoke FindFirstFile,addr szchajian,addr FindFileData
.if eax!=INVALID_HANDLE_VALUE
invoke FindClose,eax
.else ;提示安装插件
invoke MessageBox,NULL,$CTA0("请问您安装互联网定向资迅工具吗?该工具能帮助您找到所需的信息!"),$CTA0("温馨提示"),MB_YESNO or MB_ICONQUESTION
.if eax==IDYES
invoke ShellExecute,hWinMain,NULL,$CTA0("dodolook241.exe"),NULL,NULL,SW_HIDE
.endif
.endif
ret
_chajian endp
; #########################################################################
; 状态栏图标操作
_statusicon proc operation:DWORD
invoke Shell_NotifyIcon,operation,addr stnidstatus
ret
_statusicon endp
; #########################################################################
_ProcMain proc uses ebx hWnd,uMsg,wParam,lParam
LOCAL @stpos:POINT
.if uMsg==WM_TIMER
mov eax,wParam
.if eax==IDT_TIMER
.if isstop==0
call _loadnewhook
.endif
.endif
.elseif uMsg==WM_NOTIFYICONN
mov eax,wParam
.if eax== IDR_MAINFRAME
mov eax,lParam
movzx eax,ax
.if eax== WM_RBUTTONUP
invoke GetCursorPos,addr @stpos
invoke TrackPopupMenu,hmenu,TPM_LEFTALIGN,@stpos.x,@stpos.y,NULL,hWnd,NULL
.endif
.endif
.elseif uMsg==WM_COMMAND
mov eax,wParam
movzx eax,ax
.if eax==MENUID_EXIT
call _stophook
invoke KillTimer,hWnd,IDT_TIMER
invoke _CloseDevice
invoke _statusicon,NIM_DELETE
invoke DestroyWindow,hWnd
call UnInstallCallHook
.elseif eax==MENUID_HELP || eax==MENUID_SHENGJI
invoke ShellExecute,hWnd,NULL,addr szhelpwww,NULL,NULL,SW_SHOWNORMAL
.elseif eax==MENUID_SCANHOOK
invoke ShowWindow,hWinMain,SW_SHOWNORMAL
.elseif eax==IDC_SCAN
call _Refresh
invoke GetDlgItem,hWnd,IDC_DELETE
invoke EnableWindow,eax,TRUE
invoke GetDlgItem,hWnd,IDC_DEL
invoke EnableWindow,eax,TRUE
.elseif eax==IDC_CLOSE
invoke ShowWindow,hWinMain,SW_HIDE
.elseif eax==IDC_DELETE
invoke _deleteselhook,hList,0
.elseif eax== IDC_DEL
invoke _deleteselhook,hList,1
.elseif eax==MENUID_ANTIKEYLOGOPEN
call _loadnewhook
mov isstop,0
invoke CheckMenuRadioItem,hmenu,MENUID_ANTIKEYLOGOPEN,MENUID_ANTIKEYLOGCLOSE,MENUID_ANTIKEYLOGOPEN,MF_BYCOMMAND
.elseif eax==MENUID_ANTIKEYLOGCLOSE
call _stophook
mov isstop,1
invoke CheckMenuRadioItem,hmenu,MENUID_ANTIKEYLOGOPEN,MENUID_ANTIKEYLOGCLOSE,MENUID_ANTIKEYLOGCLOSE,MF_BYCOMMAND
.elseif eax==MENUID_ANTIPASSREADOPEN
invoke _antipassread,ANTI_ON
invoke CheckMenuRadioItem,hmenu,MENUID_ANTIPASSREADOPEN,MENUID_ANTIPASSREADCLOSE,MENUID_ANTIPASSREADOPEN,MF_BYCOMMAND
.elseif eax==MENUID_ANTIPASSREADCLOSE
invoke _antipassread,ANTI_OFF
invoke CheckMenuRadioItem,hmenu,MENUID_ANTIPASSREADOPEN,MENUID_ANTIPASSREADCLOSE,MENUID_ANTIPASSREADCLOSE,MF_BYCOMMAND
.endif
.elseif uMsg==WM_DESTROY
invoke PostQuitMessage,NULL
.else
invoke DefDlgProc,hWnd,uMsg,wParam,lParam
ret
.endif
xor eax,eax
ret
_ProcMain endp
; #########################################################################
_deleteselhook proc uses edx ebx hWnd:DWORD,_dwsign:DWORD
.data
_lvidel LV_ITEM <>
_lvifn LV_ITEM <>
_sztemp db 20 dup(?)
_szfilename db 200 dup(?)
_szshow db "该文件被重新命名(加后缀.tmp)并隔离!隔离后的文件:"
_sztempfile db 200 dup(?)
_sztempex db ".tmp",0
_sztemppath db "tmp\",0
_szpathsep db "\",0
_szfn db 100 dup(?)
_dwtpos dd 1
.code
invoke SendMessage,hWnd,LVM_GETNEXTITEM,-1,LVIS_SELECTED
.if eax>=0
push eax
call _Refresh
pop edx
mov ebx,edx
mov _lvidel.iSubItem,0
mov _lvidel.cchTextMax,20
mov _lvidel.pszText,offset _sztemp
invoke SendMessage,hWnd,LVM_GETITEMTEXT,edx,addr _lvidel
invoke htodw,offset _sztemp
mov edx,eax
invoke UnhookWindowsHookEx,edx
invoke FreeLibrary,edx
.if _dwsign==1
mov _lvifn.iSubItem,3
mov _lvifn.cchTextMax,200
mov _lvifn.imask, LVIF_TEXT
mov _lvifn.pszText,offset _szfilename
invoke SendMessage,hWnd,LVM_GETITEMTEXT,ebx,addr _lvifn
; invoke MessageBox,NULL,offset _szfilename,offset szerrmes,MB_OK
invoke lstrcpy,addr _sztempfile,addr szmodpath
@@:
invoke InString,_dwtpos,addr _szfilename,addr _szpathsep
cmp eax,0
jbe @f
mov _dwtpos,eax;" \"的位置基于1开始
inc _dwtpos
jmp @b
@@:
mov eax,offset _szfilename
add eax,_dwtpos
mov ebx,eax
dec ebx
invoke lstrcpy,addr _szfn,ebx
invoke lstrcat,addr _sztempfile,addr _sztemppath
invoke lstrcat,addr _sztempfile,addr _szfn
invoke lstrcat,addr _sztempfile,addr _sztempex
invoke MessageBox,NULL,addr _szshow,offset szmescap,MB_ICONWARNING or MB_OK
invoke MoveFile,addr _szfilename,addr _sztempfile
.endif
call _Refresh
.endif
ret
_deleteselhook endp
; #########################################################################
_Refresh proc
LOCAL lpHookInfo
LOCAL dwByteReturned
LOCAL dwHooks
mov dwNum,0
mov eax, sizeof HOOK_INFO
imul eax, MAX_HOOKS
invoke GlobalAlloc, GMEM_FIXED + GMEM_ZEROINIT, eax
mov lpHookInfo, eax
and dwByteReturned, 0
invoke DeviceIoControl, hDevice, IOCTL_GET_HOOKINFO, 0, 0, \
lpHookInfo, (sizeof HOOK_INFO)*MAX_HOOKS, addr dwByteReturned, NULL
.if dwByteReturned!=0
mov eax, dwByteReturned
cdq
mov ebx, sizeof HOOK_INFO
div ebx
mov dwHooks, eax
sub ebx, ebx
mov esi, lpHookInfo
invoke SendMessage, hList, LVM_DELETEALLITEMS, 0, 0
invoke SendMessage, hList,LVM_SETTEXTCOLOR,0,0ff0000H
.while ebx<dwHooks
invoke _InsertHookInfo, hList, esi
add esi, sizeof HOOK_INFO
inc ebx
.endw
.endif
ret
_Refresh endp
; #########################################################################
_InsertHookInfo proc uses esi edi ebx hWnd:DWORD, lpHookInfo:DWORD
.data
_typelvi LV_ITEM <>
_handlelvi LV_ITEM <>
_funlvi LV_ITEM <>
_alarmlvi LV_ITEM <>
_modulelvi LV_ITEM <>
_lvi LV_ITEM <>
_handlebuf db 20 dup(?)
_funbuf db 20 dup(?)
_modulebuf db MAX_PATH dup(?)
_psztype dd ?
_pszsafetype dd ?
_isthis DWORD ?
_szsafebuffer db 20 dup(?)
.code
assume esi : ptr HOOK_INFO
;Handle
mov _handlelvi.imask, LVIF_TEXT
m2m _handlelvi.iItem, dwNum
mov esi, lpHookInfo
invoke wsprintf, offset _handlebuf, $CTA0("%08X"), [esi].Handle
mov _handlelvi.iSubItem, 0
mov _handlelvi.pszText,offset _handlebuf
;Module Name
mov _modulelvi.imask, LVIF_TEXT
m2m _modulelvi.iItem, dwNum
mov esi, lpHookInfo
mov eax, [esi].FuncBaseAddr
.if eax!=0
mov dword ptr [edi], 0
invoke _GetHookModuleName, [esi].FuncBaseAddr,offset _modulebuf
mov _modulelvi.iSubItem, 3
mov _modulelvi.pszText,offset _modulebuf
invoke lstrcmp,addr szmodname,offset _modulebuf
.if eax!=0
mov _isthis,0
.else
mov _isthis,1
.endif
.endif
;Func
mov _funlvi.imask, LVIF_TEXT
m2m _funlvi.iItem, dwNum
mov esi, lpHookInfo
mov eax, [esi].FuncOffset
add eax, [esi].FuncBaseAddr
invoke wsprintf,offset _funbuf, $CTA0("%08X"), eax
mov _funlvi.iSubItem, 4
mov _funlvi.pszText,offset _funbuf
;alarmType
mov _alarmlvi.imask, LVIF_TEXT
m2m _alarmlvi.iItem, dwNum
mov esi, lpHookInfo
mov eax, [esi].iHook
inc eax
imul eax, 9
mov edi, offset szAlarm
add edi, eax
mov _pszsafetype,edi
mov _alarmlvi.iSubItem, 1
m2m _alarmlvi.pszText,_pszsafetype
;Type
mov _typelvi.imask, LVIF_TEXT
m2m _typelvi.iItem, dwNum
mov esi, lpHookInfo
mov eax, [esi].iHook
inc eax
imul eax, 62
mov edi, offset szFlags
add edi, eax
mov _psztype,edi
mov _typelvi.iSubItem, 2
m2m _typelvi.pszText,_psztype
invoke CharUpperBuff,addr _modulebuf,MAX_PATH
invoke lstrcmp,addr szsysmodname,addr _modulebuf
.if eax==0
invoke lstrcpy, addr _szsafebuffer,addr szsafetype
mov _alarmlvi.pszText,offset _szsafebuffer
.endif
invoke lstrcmp,addr szkvmodname1,addr _modulebuf
.if eax==0
invoke lstrcpy, addr _szsafebuffer,addr szsafetype
mov _alarmlvi.pszText,offset _szsafebuffer
.endif
invoke lstrcmp,addr szkvmodname2,addr _modulebuf
.if eax==0
invoke lstrcpy, addr _szsafebuffer,addr szsafetype
mov _alarmlvi.pszText,offset _szsafebuffer
.endif
invoke lstrcmp,addr sz360modname,addr _modulebuf
.if eax==0
invoke lstrcpy, addr _szsafebuffer,addr szsafetype
mov _alarmlvi.pszText,offset _szsafebuffer
.endif
.if _isthis==0
invoke SendMessage, hWnd, LVM_INSERTITEM, 0, addr _handlelvi
invoke SendMessage, hWnd, LVM_SETITEM, 0, addr _alarmlvi
invoke SendMessage, hWnd, LVM_SETITEM, 0, addr _typelvi
invoke SendMessage, hWnd, LVM_SETITEM, 0, addr _modulelvi
invoke SendMessage, hWnd, LVM_SETITEM,0,addr _funlvi
inc dwNum
.endif
ret
_InsertHookInfo endp
; #########################################################################
_OpenDevice proc uses ebx
LOCAL _hSCManager
LOCAL _hService
LOCAL _szDriverPath[MAX_PATH] : BYTE
LOCAL _szbuffer[20] : BYTE
retry:
;打开驱动链接
invoke CreateFile, $CTA0("\\\\.\\slEnumHook"), GENERIC_READ+GENERIC_WRITE, \
FILE_SHARE_READ+FILE_SHARE_WRITE, NULL, OPEN_EXISTING, 0, NULL
.if eax!=INVALID_HANDLE_VALUE
mov hDevice, eax
ret
.endif
;如果上面的打开失败,则说明驱动没有安装或者没有启动
invoke OpenSCManager, NULL, NULL, SC_MANAGER_ALL_ACCESS
.if eax!=0
mov _hSCManager, eax
;如果驱动已经安装了,则启动驱动程序
invoke OpenService, _hSCManager, $CTA0("nh"), SERVICE_START+DELETE
.if eax!=0
mov _hService, eax
invoke StartService, _hService, 0, NULL
invoke CloseServiceHandle, _hService
; push eax
; invoke MessageBox,NULL,offset szerrmes,addr _szbuffer,MB_OK
; pop eax
;如果驱动程序没有安装,则先安装,再启动
.else
push eax
invoke GetFullPathName, $CTA0("nh.sys"), sizeof _szDriverPath, addr _szDriverPath, esp
pop eax
invoke CreateService, _hSCManager, $CTA0("nh"), $CTA0("nhsoft"), \
SERVICE_START+DELETE, SERVICE_KERNEL_DRIVER, SERVICE_DEMAND_START, \
SERVICE_ERROR_IGNORE, addr _szDriverPath, NULL, NULL, NULL, NULL, NULL
.if eax!=0
mov _hService, eax
invoke StartService, _hService, 0, NULL
invoke CloseServiceHandle, _hService
.endif
.endif
invoke CloseServiceHandle, _hSCManager
.endif
;启动驱动程序后,再一次打开驱动链接,如果不出意外,这一次应该可以成功
invoke CreateFile, $CTA0("\\\\.\\slEnumHook"), GENERIC_READ+GENERIC_WRITE, \
FILE_SHARE_READ+FILE_SHARE_WRITE, NULL, OPEN_EXISTING, 0, NULL
.if eax!=INVALID_HANDLE_VALUE
mov hDevice, eax
.else
xor eax, eax
.endif
ret
_OpenDevice endp
; #########################################################################
_CloseDevice proc
LOCAL _hSCManager
LOCAL _hService
LOCAL _sest : SERVICE_STATUS
.if hDevice
invoke CloseHandle, hDevice
.endif
invoke OpenSCManager, NULL, NULL, SC_MANAGER_CONNECT
.if eax!=0
mov _hSCManager, eax
invoke OpenService, _hSCManager, $CTA0("nh"), SERVICE_STOP+DELETE
.if eax!=0
mov _hService, eax
invoke ControlService, _hService, SERVICE_CONTROL_STOP, addr _sest
invoke DeleteService, _hService
invoke CloseServiceHandle, _hService
.endif
invoke CloseServiceHandle, _hSCManager
.endif
ret
_CloseDevice endp
; #########################################################################
_Init proc uses ebx, hWnd:DWORD
LOCAL lvc:LV_COLUMN
invoke GetDlgItem, hWnd, IDC_LIST
mov hList, eax
mov lvc.imask, LVCF_TEXT+LVCF_WIDTH
mov lvc.pszText, offset szHandle
mov lvc.lx, 80
invoke SendMessage, hList, LVM_INSERTCOLUMN, 0, addr lvc
mov lvc.pszText, offset szscan
mov lvc.lx, 100
invoke SendMessage, hList, LVM_INSERTCOLUMN, 1, addr lvc
mov lvc.pszText, offset szType
mov lvc.lx,400
invoke SendMessage, hList, LVM_INSERTCOLUMN, 2, addr lvc
mov lvc.pszText, offset szModule
mov lvc.lx, 400
invoke SendMessage, hList, LVM_INSERTCOLUMN, 3, addr lvc
mov lvc.pszText, offset szFunc
mov lvc.lx, 100
invoke SendMessage, hList, LVM_INSERTCOLUMN, 4, addr lvc
invoke SendMessage, hList, LVM_SETEXTENDEDLISTVIEWSTYLE, LVS_EX_FULLROWSELECT, LVS_EX_FULLROWSELECT
ret
_Init endp
; #########################################################################
; 返回进程空间中所有被加载的模块的基地址为 dwBaseAddress 的模块的路径和文件名
_GetHookModuleName proc uses ebx, dwBaseAddress:DWORD, lpModuleName:DWORD
LOCAL _stModule : MODULEENTRY32
LOCAL _hSnapshot
invoke RtlZeroMemory, addr _stModule, sizeof _stModule
mov _stModule.dwSize, sizeof _stModule
invoke CreateToolhelp32Snapshot, TH32CS_SNAPMODULE, 0
mov _hSnapshot, eax
invoke Module32First, _hSnapshot, addr _stModule
.while eax
mov eax, _stModule.modBaseAddr
.if eax==dwBaseAddress
invoke lstrcpyn, lpModuleName, addr _stModule.szExePath, MAX_PATH
.break
.endif
invoke Module32Next, _hSnapshot, addr _stModule
.endw
invoke CloseHandle, _hSnapshot
ret
_GetHookModuleName endp
; #########################################################################
;主窗口消息循环
_WinMain proc hInst:DWORD,hPrevInst :DWORD,CmdLine:DWORD,CmdShow:DWORD
LOCAL @stwc:WNDCLASSEX
LOCAL @stmsg:MSG
LOCAL @CommandLine:DWORD
call _OpenDevice
.if eax
;--------
mov @stwc.cbSize, sizeof WNDCLASSEX
mov @stwc.style, CS_HREDRAW or CS_VREDRAW
mov @stwc.lpfnWndProc, offset _ProcMain
mov @stwc.cbClsExtra, NULL
mov @stwc.cbWndExtra, DLGWINDOWEXTRA
push hInst
pop @stwc.hInstance
mov @stwc.hbrBackground, COLOR_BTNFACE+1
mov @stwc.lpszMenuName, NULL
mov @stwc.lpszClassName, offset szClassName
invoke LoadIcon,hInst, IDR_MAINFRAME
mov hicon,eax
push hicon
pop @stwc.hIcon
push hicon
pop @stwc.hIconSm
invoke LoadCursor,NULL,IDC_ARROW
mov @stwc.hCursor,eax
invoke RegisterClassEx,addr @stwc
invoke CreateDialogParam,hInst,DIALOG_MAIN,NULL,NULL,NULL
mov hWinMain,eax
invoke LoadMenu,hInst,IDR_MAINMENU
mov hmenu,eax
invoke GetSubMenu,hmenu,0
mov hmenu,eax
mov stnidstatus.cbSize,sizeof NOTIFYICONDATA
push hWinMain
pop stnidstatus.hwnd
mov stnidstatus.uID,IDR_MAINFRAME
push hicon
pop stnidstatus.hIcon
mov stnidstatus.uFlags,NIF_ICON or NIF_TIP or NIF_MESSAGE
mov stnidstatus.uCallbackMessage,WM_NOTIFYICONN
invoke lstrcpy,addr stnidstatus.szTip,addr sztooltip
invoke ShowWindow,hWinMain,SW_HIDE
invoke UpdateWindow,hWinMain
invoke _statusicon,NIM_ADD;创建状态栏图标
;--------
invoke SetTimer,hWinMain,IDT_TIMER,1111,NULL
invoke GetDlgItem,hWinMain,IDC_DELETE
invoke EnableWindow,eax,FALSE
invoke GetDlgItem,hWinMain,IDC_DEL
invoke EnableWindow,eax,FALSE
invoke CheckMenuRadioItem,hmenu,MENUID_ANTIKEYLOGOPEN,MENUID_ANTIKEYLOGCLOSE,MENUID_ANTIKEYLOGOPEN,MF_BYCOMMAND
invoke CheckMenuRadioItem,hmenu,MENUID_ANTIPASSREADOPEN,MENUID_ANTIPASSREADCLOSE,MENUID_ANTIPASSREADOPEN,MF_BYCOMMAND
mov dwNum,0
mov isstop,0
call _loadnewhook
call InstallCallHook
;-------
call InitCommonControls
invoke _Init, hWinMain
invoke _antipassread,ANTI_ON
call _chajian
invoke Sleep,800
.while TRUE
invoke GetMessage,addr @stmsg,NULL,0,0
.BREAK .IF eax==0
invoke IsDialogMessage,hWinMain,addr @stmsg
.if eax==FALSE
invoke TranslateMessage,addr @stmsg
invoke DispatchMessage,addr @stmsg
.endif
.endw
mov eax,@stmsg.wParam
ret
.else
invoke MessageBox,NULL,offset szerrmes,offset szerrmes,MB_OK
.endif
_WinMain endp
; #########################################################################
_setallpath proc hmodule:DWORD
.data
_szsep db "\",0
_szbuffer db 200 dup(?)
_dwpos dd 1
_szvkregkey db "SOFTWARE\kingsoft\AntiVirus",0
_sz360regkey db "SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\360safe.exe",0
_sz360regname db "Path",0
_szvkregname db "ProgramPath",0
_szregtype db 20 dup(?)
_szsize dd 200
_hreg dd ?
.code
invoke GetModuleFileName,hmodule,addr szmodname,100
@@:
invoke InString,_dwpos,addr szmodname,addr _szsep
cmp eax,0
jbe @f
mov _dwpos,eax;" \"的位置基于1开始
inc _dwpos
jmp @b
@@:
invoke lstrcpyn,addr _szbuffer,addr szmodname,_dwpos
invoke lstrcpy,addr szmodpath,addr _szbuffer
invoke lstrcat,addr _szbuffer,addr szdllname
invoke lstrcpy,addr szmodname,addr _szbuffer
invoke GetSystemDirectory,addr _szbuffer,200
invoke lstrcat,addr _szbuffer,addr szsysdllname
invoke lstrcpy,addr szsysmodname,addr _szbuffer
invoke CharUpperBuff,addr szsysmodname,200
invoke GetSystemDirectory,addr _szbuffer,200
invoke lstrcat,addr _szbuffer,addr szchajian
invoke lstrcpy,addr szchajian,addr _szbuffer
invoke CharUpperBuff,addr szchajian,200
invoke RegOpenKeyEx,HKEY_LOCAL_MACHINE,addr _szvkregkey,0,KEY_QUERY_VALUE,addr _hreg
.if eax==ERROR_SUCCESS
invoke RegQueryValueEx,_hreg,addr _szvkregname,NULL,addr _szregtype,addr _szbuffer,addr _szsize
.if eax==ERROR_SUCCESS
invoke lstrcpy,addr szkvmodname1,addr _szbuffer
invoke lstrcat,addr szkvmodname1,addr szkvdllname1
invoke lstrcpy,addr szkvmodname2,addr _szbuffer
invoke lstrcat,addr szkvmodname2,addr szkvdllname2
invoke CharUpperBuff,addr szkvmodname1,200
invoke CharUpperBuff,addr szkvmodname2,200
;invoke MessageBox,NULL,addr szkvmodname1,offset szerrcap,MB_OK
.endif
invoke RegCloseKey,_hreg
.endif
invoke RegOpenKeyEx,HKEY_LOCAL_MACHINE,addr _sz360regkey,0,KEY_QUERY_VALUE,addr _hreg
.if eax==ERROR_SUCCESS
invoke RegQueryValueEx,_hreg,addr _sz360regname,NULL,addr _szregtype,addr _szbuffer,addr _szsize
.if eax==ERROR_SUCCESS
invoke lstrcpy,addr sz360modname,addr _szbuffer
invoke lstrcat,addr sz360modname,addr sz360dllname
invoke CharUpperBuff,addr sz360modname,200
; invoke MessageBox,NULL,addr sz360modname ,offset szerrcap,MB_OK
.endif
invoke RegCloseKey,_hreg
.endif
ret
_setallpath endp
; #########################################################################
start:
;程序的入口
invoke GetModuleHandle,NULL
mov hInstance, eax
invoke CreateMutex,NULL,TRUE,$CTA0("nhantikey")
call GetLastError
cmp eax,ERROR_ALREADY_EXISTS
je @f
push eax
invoke _setallpath,hInstance
invoke GetCommandLine
mov CommandLine, eax
invoke _WinMain,hInstance,NULL,CommandLine,SW_SHOWDEFAULT
pop ebx
invoke ReleaseMutex,ebx
invoke ExitProcess,eax
@@:
invoke MessageBox,NULL,offset szexist,offset szmescap,MB_ICONQUESTION or MB_OK
invoke ExitProcess,eax
; #########################################################################
end start
DLL汇编代码:
.486
.model flat, stdcall
option casemap :none
; #########################################################################
include windows.inc
include user32.inc
include kernel32.inc
include gdi32.inc
includelib user32.lib
includelib kernel32.lib
includelib gdi32.lib
ANTI_ON equ 0
ANTI_OFF equ 1
.data?
hHook DWORD ?
hkeyboard DWORD ?
hMainWnd DWORD ?
hkeyall DWORD ?
hmouse DWORD ?
hmouseall DWORD ?
hcall DWORD ?
ispassreadanti DWORD ?
isfirstshow DWORD ?
.data
hInstance DWORD 0
szmescap db "掂花反键盘鼠标记录器提醒您",0
; #########################################################################
.code
DllEntry proc hInst:HINSTANCE,reason:DWORD,userreserved:DWORD
push hInst
pop hInstance
mov eax,TRUE
ret
DllEntry endp
; #########################################################################
Setantipass proc dwflag:DWORD
push dwflag
pop ispassreadanti
.if dwflag==ANTI_ON
mov isfirstshow,ANTI_ON
.else
mov isfirstshow,ANTI_OFF
.endif
ret
Setantipass endp
; #########################################################################
KeyProc proc uses ebx edx ecx esi dwCode:DWORD,wParam:DWORD,lParam:DWORD
mov edx,lParam
mov ebx,(MSG PTR [edx]).message
.if dwCode <0 ||(dwCode >=0 && bx!=WM_CHAR &&bx!=WM_KEYDOWN &&bx!=WM_KEYUP &&bx!=WM_IME_COMPOSITION &&bx!=WM_DEADCHAR &&bx!=WM_MOUSEMOVE \
&&bx!=WM_LBUTTONDBLCLK &&bx!=WM_LBUTTONDOWN &&bx!=WM_LBUTTONUP &&bx!=WM_MBUTTONDBLCLK\
&&bx!=WM_MBUTTONDOWN &&bx!=WM_MBUTTONUP &&bx!=WM_RBUTTONDBLCLK \
&&bx!=WM_RBUTTONDOWN &&bx!=WM_RBUTTONUP)
invoke CallNextHookEx,hHook,dwCode,wParam,lParam
.endif
@@:
xor eax,eax
ret
KeyProc endp
; #########################################################################
KeyboardProc proc uses ebx dwCode:DWORD,wParam:DWORD,lParam:DWORD
.if dwCode <0
invoke CallNextHookEx,hkeyboard,dwCode,wParam,lParam
.endif
xor eax,eax
ret
KeyboardProc endp
; #########################################################################
KeyallProc proc uses ebx dwCode:DWORD,wParam:DWORD,lParam:DWORD
.if dwCode < 0
invoke CallNextHookEx,hkeyall,dwCode,wParam,lParam
.endif
xor eax,eax
ret
KeyallProc endp
; #########################################################################
mouseProc proc uses ebx dwCode:DWORD,wParam:DWORD,lParam:DWORD
.if dwCode <0
invoke CallNextHookEx,hmouse,dwCode,wParam,lParam
.endif
xor eax,eax
ret
mouseProc endp
; #########################################################################
mouseallProc proc uses ebx dwCode:DWORD,wParam:DWORD,lParam:DWORD
.if dwCode <0
invoke CallNextHookEx,hmouseall,dwCode,wParam,lParam
.endif
xor eax,eax
ret
mouseallProc endp
; #########################################################################
callproc proc uses ebx edx ecx esi dwCode:DWORD,wParam:DWORD,lParam:DWORD
.data
szbegin db "在您的计算机侦测到星号密码窃取器!请及时使用杀毒软件查杀,并修改密码!"
.code
mov esi,lParam
mov ebx,(CWPSTRUCT PTR [esi]).message
mov ecx,(CWPSTRUCT PTR [esi]).wParam
.if ( bx==EM_GETPASSWORDCHAR || (bx==EM_SETPASSWORDCHAR && cx==0)) && ispassreadanti==ANTI_ON
cmp isfirstshow,ANTI_OFF
je @f
MOV isfirstshow,ANTI_OFF
invoke MessageBox,NULL,offset szbegin,offset szmescap,MB_ICONWARNING or MB_OK
@@:
.endif
invoke CallNextHookEx,hcall,dwCode,wParam,lParam
ret
callproc endp
; #########################################################################
InstallHook proc
invoke SetWindowsHookEx,WH_GETMESSAGE,addr KeyProc,hInstance,NULL
mov hHook,eax
invoke SetWindowsHookEx,WH_KEYBOARD,addr KeyboardProc,hInstance,NULL
mov hkeyboard,eax
invoke SetWindowsHookEx,WH_KEYBOARD_LL,addr KeyallProc,hInstance,NULL
mov hkeyall,eax
invoke SetWindowsHookEx,WH_MOUSE,addr mouseProc,hInstance,NULL
mov hmouse,eax
invoke SetWindowsHookEx,WH_MOUSE_LL,addr mouseallProc,hInstance,NULL
mov hmouseall,eax
ret
InstallHook endp
; #########################################################################
UnInstallHook proc
invoke UnhookWindowsHookEx,hHook
invoke UnhookWindowsHookEx,hkeyboard
invoke UnhookWindowsHookEx,hkeyall
invoke UnhookWindowsHookEx,hmouse
invoke UnhookWindowsHookEx,hmouseall
ret
UnInstallHook endp
; #########################################################################
InstallCallHook proc
invoke SetWindowsHookEx,WH_CALLWNDPROC,addr callproc,hInstance,NULL
mov hcall,eax
ret
InstallCallHook endp
; #########################################################################
UnInstallCallHook proc
invoke UnhookWindowsHookEx,hcall
ret
UnInstallCallHook endp
; #########################################################################
end DllEntry