OMAP Wireless Connectivity NLCP WiFi Direct Configuration Scripts
本文转载至:http://processors.wiki.ti.com/index.php/OMAP_Wireless_Connectivity_NLCP_WiFi_Direct_Configuration_Scripts
Glossary
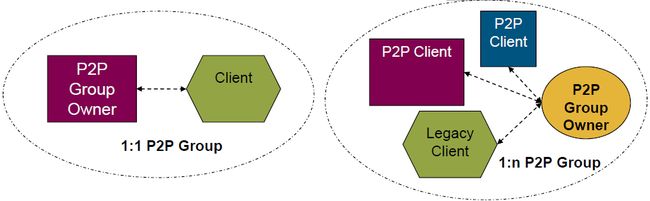
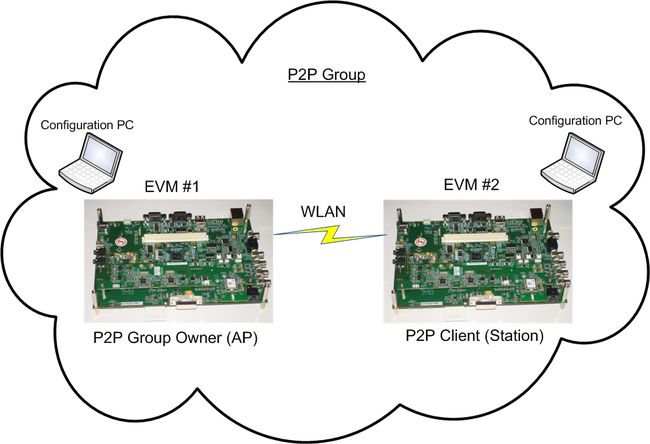
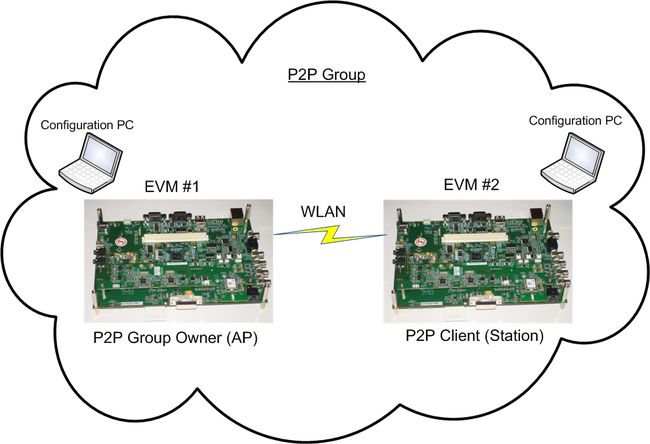
- A P2P Group is a Wi-Fi P2P network that may include two types of devices:
-
- P2P Device –Wi-Fi CERTIFIED™ device that is compliant with the Wi-Fi P2P specification
- Legacy device –Wi-Fi CERTIFIED™ device that is not compliant with the Wi-Fi P2P specification
- P2P devices must be capable of two different roles in a P2P Group:
-
- P2P Group Owner : An “AP-like” capability that controls a Wi-Fi P2P Group and enables P2P Device connectivity
- P2P Client : A Wi-Fi P2P-compliant device that may connect to a P2P Group Owner
-
- Legacy devices may only function as client in a P2P Group.
P2P commands
The basics commands: Discovery, connection etc.
| Command | Description |
|---|---|
| p2p_find [timeout (seconds)] [type <social \ progressive>] | Enables discovery – start sending probe request frames |
| p2p_stop_find | Stops discovery, or whatever you are doing (listen mode, connection process etc.) |
| P2p_connect <device address> <PBC \ PIN> [GO_intent=<0-15> \ auth \ join] | GO_intent – initiate connection to another device (using entered group intent) Auth – WPS authorize incoming connection Join – connect to an existing GO No input – initiate connection using default GO intent |
| P2p_listen [timeout (seconds)] | Enable listen mode |
| P2p_group_remove <interface> | Remove device from group, return to device mode if acting as GO or autonomous GO |
| P2p_group_add | Become an autonomous GO |
Managing discovered peers: Using the discovered peers list
| Command | Description |
|---|---|
| P2p_peers [discovered] | Shows list of discovered peers (with ‘discovered’ – shows only fully discovered peers) |
| P2p_peer <address> | Show detailed information about discovered peers |
| P2p_flush | Flush p2p_state, and clears the discovered peer list |
GO WPS authorizations:When devices try to connect to GOUT
| Command | Description |
|---|---|
| Wps_pbc | pushbutton to accept incoming connections |
| Wps_pin <PIN> <UUID> | Enable WPS enrollee PIN |
Others
| Command | Description |
|---|---|
| p2p_prov_disc <address> <method> | Request provision discovery |
| p2p_serv_disc_req <addr> <TLVs> | Send service discovery request |
| p2p_serv_disc_cancel_req <id> | Cancel service discovery request |
| p2p_serv_disc_resp <freq> <addr> <dialog token> <TLVs> | Service discovery response |
| p2p_service_add <bonjour\upnp> <query\version> <response\service> | Add a local service |
| p2p_service_del <bonjour\upnp> <query\version> [service] | Remove a local service |
| p2p_invite <cmd> [address] | Send invitation to device |
| Reconfigure | Wpa_supplicant will re-read configuration file |
| Ping | Ping wpa_supplicant (only) |
P2P usecases
The WPA Supplicant has a configuration file located under /etc/wpa_supplicant.conf.
This configuration file can be used to allow automatic connection once the WPA Supplicant process is running.
In order to connect a WPA2 secured network using the configuration file, we need the following steps:
Please note that from R8.2 release, we use two interfaces: one for STA ('wlan0') and one for WiFi Direct ('p2p0'). From R8.2 release, the configuration file will be: /etc/p2p_supplicant.conf
Detailed below are the steps required for both versions.
Steps prior to R8.2 release
1. Back up the original configuration file:
mv /etc/wpa_supplicant.conf /etc/wpa_supplicant.conf.bak
2. Create a new wpa_supplicant.conf with the following content:
ctrl_interface=/var/run/wpa_supplicant update_config=1
optional for debug only, can be useful for monitoring, forces the wpa_supplicant to use only channel 1 rather than 1, 6 and 11.
for that add the following in the wpa_supplicant.conf file
p2p_listen_reg_class=81 p2p_listen_channel=1 p2p_oper_reg_class=81 p2p_oper_channel=1
In order to support 802.11n for GO, please also add the following line:
p2p_go_ht40=1
The editing above can be done by vi editor as follows:
-
vi /etc/wpa_supplicant.conf
- The editor will be opened. Type the character 'i' to switch to editing mode.
- Copy and paste the above content into the editor.
- Hit 'esc' button to stop editing.
- Type the sequence ":wq" in order to save and quit.
3. Run the WPA Supplicant:
wpa_supplicant -d -Dnl80211 -c /etc/wpa_supplicant.conf -iwlan0 -B
4. config the WLAN IP address
ifconfig wlan0 192.168.3.3 netmask 255.255.255.0 up
Make sure that the WLAN got the proper IP address
root@am37x-evm:~# ifconfig
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
UP LOOPBACK RUNNING MTU:16436 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:0 (0.0 B) TX bytes:0 (0.0 B)
wlan0 Link encap:Ethernet HWaddr 00:11:22:44:88:FF
inet addr:192.168.3.3 Bcast:192.168.3.255 Mask:255.255.255.0
UP BROADCAST MULTICAST MTU:1500 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:0 (0.0 B) TX bytes:0 (0.0 B)
Comment: Make sure that all the EVMS that participate in the WiFi Direct network has unique MAC Address, and that all has IP Address that is in the same Subnet.
5. Run WPA Supplicant CLI to get to the WiFi direct commands
wpa_cli
Steps from R8.2 release onwards
1. Create the p2p0 interface using the below command:
iw phy `ls /sys/class/ieee80211/` interface add p2p0 type managed
2. Ensure that /etc/p2p_supplicant.conf file exists with the below values(default)
ctrl_interface=/var/run/wpa_supplicant update_config=0 device_name=TI-SITARA-P2P device_type=1-0050F204-1 config_methods=virtual_push_button physical_display keypad p2p_go_intent=0 country=US driver_param=use_multi_chan_concurrent=1 use_p2p_group_interface=1 p2p_go_max_inactivity=60 p2p_go_ht40=1 p2p_multi_chan=1 disassoc_low_ack=1 concurrent_sched_scan=1
3. Run the wpa_supplicant:
wpa_supplicant -iwlan0 -Dnl80211 -c/etc/wpa_supplicant.conf -N -ip2p0 -Dnl80211 -c/etc/p2p_supplicant.conf &
4. Configure the WLAN IP address
ifconfig p2p0 192.168.3.3 netmask 255.255.255.0 up
Make sure that the p2p0 interface got the proper IP address
root@am335x-evm:~# ifconfig -a
eth0 Link encap:Ethernet HWaddr 00:18:31:8E:F7:A4
UP BROADCAST MULTICAST MTU:1500 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:0 (0.0 B) TX bytes:0 (0.0 B)
Interrupt:56
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
UP LOOPBACK RUNNING MTU:65536 Metric:1
RX packets:117 errors:0 dropped:0 overruns:0 frame:0
TX packets:117 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:248528 (242.7 KiB) TX bytes:248528 (242.7 KiB)
p2p0 Link encap:Ethernet HWaddr 34:B1:F7:DF:37:5F
inet addr:192.168.3.3 Bcast:192.168.3.255 Mask:255.255.255.0
UP BROADCAST MULTICAST MTU:1500 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:0 (0.0 B) TX bytes:0 (0.0 B)
wlan0 Link encap:Ethernet HWaddr 34:B1:F7:DF:37:5E
UP BROADCAST MULTICAST MTU:1500 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:0 (0.0 B) TX bytes:0 (0.0 B)
5. Run WPA Supplicant CLI to get to the WiFi direct commands
wpa_cli -ip2p0
Connect in pbc (Push button Control)
| Step # | EVM #1 | EVM #2 | Comments |
|---|---|---|---|
| 1 | p2p_find | p2p_find | |
| 2 | p2p_peers | p2p_peers | verify p2p candidates MAC ADDRESS |
| 3 | p2p_connect EVM#2_MAC_ADDRESS pbc go_intent=7 | go_intent=7 means that there a same chance for both EVMs to become GO go_intent= 15 means that EVM will become GO go_intent= 0 means that EVM will become Client |
|
| 4 | p2p_connect EVM#1_MAC_ADDRESS pbc |
Connect in pbc (Push button Control) where EVM #1 is defined as the group owner
| Step # | EVM #1 | EVM #2 | Comments |
|---|---|---|---|
| 1 | p2p_find | p2p_find | |
| 2 | p2p_peers | p2p_peers | verify p2p candidates MAC ADDRESS |
| 3 | p2p_group_add | Define EVM #1 as GO | |
| 4 | wps_pbc | ||
| 5 | p2p_connect EVM#1_MAC_ADDRESS pbc join |
Connect in Pin (PIN Number) where EVM #1 is defined as the group owner
| Step # | EVM #1 | EVM #2 | Comments |
|---|---|---|---|
| 1 | p2p_find | p2p_find | |
| 2 | p2p_peers | p2p_peers | verify p2p candidates MAC ADDRESS |
| 3 | p2p_group_add | Define EVM #1 as GO | |
| 4 | wps_pin any | verify the EVM#1_PIN_NUMBER, will appear on the terminal | |
| 5 | p2p_connect EVM#1_MAC_ADDRESS EVM#1_PIN_NUMBER join |
Connection using PIN code
| Step # | EVM #1 | EVM #2 | Comments |
|---|---|---|---|
| 1 | p2p_find | p2p_find | |
| 2 | p2p_peers | p2p_peers | verify p2p candidates MAC ADDRESS |
| 3 | p2p_connect EVM#2_MAC_ADDRESS pin auth | That command will print EVM#1 pin code in the follwoing line | |
| 4 | p2p_connect EVM#1_MAC_ADDRESS EVM#1_PIN_CODE | getting EVM#1_PIN_CODE from previous EVM#1 command |
P2P Demo usecases
Following are several WiFi Direct Demos.
Note: The below steps are based on R8.1 release. The commands will vary from R8.2 release onwards.As mentioned, R8.2 + releases uses "p2p0" interface
For R8.2+ release use the below commands to start wpa_supplicant & wpa_cli.
wpa_supplicant: wpa_supplicant -iwlan0 -Dnl80211 -c/etc/wpa_supplicant.conf -N -ip2p0 -Dnl80211 -c/etc/p2p_supplicant.conf &
wpa_cli: wpa_cli -ip2p0
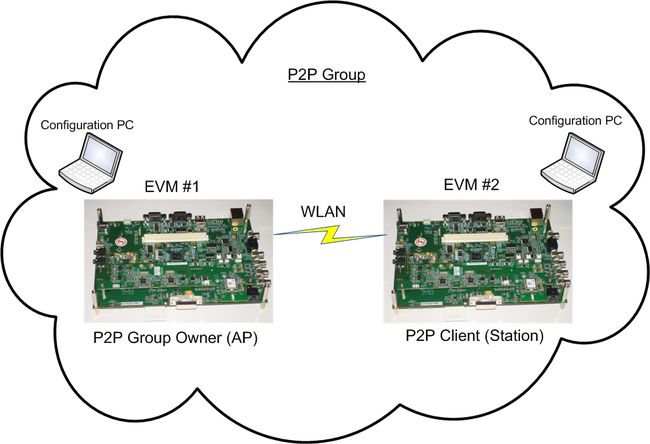
Create 1:2 P2P Group - Connect in pbc (Push button Control)
The Flow of commands in that usecase is as follows:
| Step # | EVM #1 | EVM #2 | Comments |
|---|---|---|---|
| 1 | bring up WLAN and Set static IP Address | bring up WLAN and Set static IP Address | |
| 2 | run WPA Supplicant and WPA CLI | run WPA Supplicant and WPA CLI | R8.2 and before wpa_supplicant -d -Dnl80211 -c /etc/wpa_supplicant.conf -iwlan0 -B Post R8.2 wpa_supplicant -iwlan0 -Dnl80211 -c/etc/wpa_supplicant.conf -N -ip2p0 -Dnl80211 -c/etc/p2p_supplicant.conf |
| 3 | p2p_find | p2p_find | |
| 4 | p2p_peers | p2p_peers | verify p2p candidates MAC ADDRESS |
| 5 | p2p_connect EVM#2_MAC_ADDRESS pbc auth go_intent=7 | go_intent=7 means that there a same chance for both EVMs to become GO go_intent= 15 means that EVM will become GO go_intent= 0 means that EVM will become Client |
|
| 6 | p2p_connect EVM#1_MAC_ADDRESS pbc | ||
| 7 | Verify connection with Ping traffic |
EVM #1
root@am37x-evm:~# ifconfig wlan0 192.168.3.3
root@am37x-evm:~#
root@am37x-evm:~#
root@am37x-evm:~# ifconfig
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
UP LOOPBACK RUNNING MTU:16436 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:0 (0.0 B) TX bytes:0 (0.0 B)
wlan0 Link encap:Ethernet HWaddr 00:11:22:44:88:FF
inet addr:192.168.3.3 Bcast:192.168.3.255 Mask:255.255.255.0
UP BROADCAST MULTICAST MTU:1500 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:0 (0.0 B) TX bytes:0 (0.0 B)
wpa_cli
wpa_cli v0.8.x Copyright (c) 2004-2011, Jouni Malinen <[email protected]> and contributors This program is free software. You can distribute it and/or modify it under the terms of the GNU General Public License version 2. Alternatively, this software may be distributed under the terms of the BSD license. See README and COPYING for more details. Selected interface 'wlan0' Interactive mode > >
EVM #2
root@am37x-evm:~# ifconfig wlan0 192.168.3.4 up
root@am37x-evm:~#
root@am37x-evm:~# ifconfig
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
UP LOOPBACK RUNNING MTU:16436 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:0 (0.0 B) TX bytes:0 (0.0 B)
wlan0 Link encap:Ethernet HWaddr 00:12:34:56:78:90
inet addr:192.168.3.4 Bcast:192.168.3.255 Mask:255.255.255.0
UP BROADCAST MULTICAST MTU:1500 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:0 (0.0 B) TX bytes:0 (0.0 B)
root@am37x-evm:~# wpa_cli wpa_cli v0.8.x Copyright (c) 2004-2011, Jouni Malinen <[email protected]> and contributors This program is free software. You can distribute it and/or modify it under the terms of the GNU General Public License version 2. Alternatively, this software may be distributed under the terms of the BSD license. See README and COPYING for more details. Selected interface 'wlan0' Interactive mode > >
EVM #1
> p2p_find OK <3>P2P-DEVICE-FOUND 00:12:34:56:78:90 p2p_dev_addr=00:12:34:56:78:90 pri_dev_type=0-00000000-0 name='' config_methods=0x188 dev_capab=0x23 group_capab=0x0
EVM #2
> p2p_find OK <3>P2P-DEVICE-FOUND 00:11:22:44:88:ff p2p_dev_addr=00:11:22:44:88:ff pri_dev_type=0-00000000-0 name='' config_methods=0x188 dev_capab=0x23 group_capab=0x0
> p2p_peers 00:11:22:44:88:ff
EVM #1
> p2p_peers 00:12:34:56:78:90
> p2p_connect 00:12:34:56:78:90 pbc auth go_intent=7 OK
EVM #2
> p2p_connect 00:11:22:44:88:ff pbc OK <3>P2P-GO-NEG-SUCCESS <3>CTRL-EVENT-SCAN-RESULTS <3>WPS-AP-AVAILABLE <3>CTRL-EVENT-SCAN-RESULTS <3>WPS-AP-AVAILABLE-PBC <3>SME: Trying to authenticate with 00:11:22:44:88:ff (SSID='DIRECT-84' freq=2412 MHz) [ 1444.193328] wl1271: down [ 1444.788909] wl1271: firmware booted (Rev 6.3.1.0.79_S12) [ 1444.830566] wlan0: authenticate with 00:11:22:44:88:ff (try 1) [ 1444.839416] wlan0: authenticated <3>CTRL-EVENT-SCAN-RESULTS <3>WPS-AP-AVAILABLE-PBC <3>SME: Trying to authenticate with 00:11:22:44:88:ff (SSID='DIRECT-84' freq=2412 MHz) [ 1444.918395] wlan0: deauthenticating from 00:11:22:44:88:ff by local choice (reason=2) [ 1444.926879] wl1271: ERROR invalid hlid. dropping skb 0xceed3ec0 <3>CTRL-EVENT-DISCONNECTED bssid=00:11:22:44:88:ff reason=2 [ 1444.947692] wlan0: authenticate with 00:11:22:44:88:ff (try 1) [ 1444.956420] wlan0: authenticated <3>Trying to associate with 00:11:22:44:88:ff (SSID='DIRECT-84' freq=2412 MHz) [ 1444.986816] wlan0: associate with 00:11:22:44:88:ff (try 1) [ 1444.998138] wlan0: RX AssocResp from 00:11:22:44:88:ff (capab=0x411 status=0 aid=1) [ 1445.006256] wlan0: associated <4>Failed to initiate AP scan <3>Associated with 00:11:22:44:88:ff <3>CTRL-EVENT-EAP-STARTED EAP authentication started <3>CTRL-EVENT-EAP-PROPOSED-METHOD vendor=14122 method=1 <3>CTRL-EVENT-EAP-METHOD EAP vendor 14122 method 1 (WSC) selected <3>WPS-CRED-RECEIVED <3>WPS-SUCCESS <3>P2P-GROUP-FORMATION-SUCCESS <3>CTRL-EVENT-EAP-FAILURE EAP authentication failed [ 1448.597106] wlan0: deauthenticating from 00:11:22:44:88:ff by local choice (reason=3) [ 1448.641387] cfg80211: Calling CRDA to update world regulatory domain <3>CTRL-EVENT-DISCONNECTED bssid=00:00:00:00[ 1448.688751] cfg80211: World regulatory domain updated: [ 1448.695007] cfg80211: (start_freq - end_freq @ bandwidth), (max_antenna_gain, max_eirp) [ 1448.705139] cfg80211: (2402000 KHz - 2472000 KHz @ 40000 KHz), (300 mBi, 2000 mBm) [ 1448.713531] cfg80211: (2457000 KHz - 2482000 KHz @ 20000 KHz), (300 mBi, 2000 mBm) [ 1448.721862] cfg80211: (2474000 KHz - 2494000 KHz @ 20000 KHz), (300 mBi, 2000 mBm) [ 1448.730194] cfg80211: (5170000 KHz - 5250000 KHz @ 40000 KHz), (300 mBi, 2000 mBm) [ 1448.738525] cfg80211: (5735000 KHz - 5835000 KHz @ 40000 KHz), (300 mBi, 2000 mBm) <4>Failed to initiate AP scan <3>CTRL-EVENT-SCAN-RESULTS <3>WPS-AP-AVAILABLE <3>SME: Trying to authenticate with 00:11:22:44:88:ff (SSID='DIRECT-84' freq=2412 MHz) [ 1449.213409] wlan0: authenticate with 00:11:22:44:88:ff (try 1) [ 1449.221588] wlan0: authenticated <3>Trying to associate with 00:11:22:44:88:ff (SSID='DIRECT-84' freq=2412 MHz) [ 1449.252441] wlan0: associate with 00:11:22:44:88:ff (try 1) [ 1449.262084] wlan0: RX ReassocResp from 00:11:22:44:88:ff (capab=0x411 status=0 aid=1) [ 1449.270355] wlan0: associated <3>Associated with 00:11:22:44:88:ff <3>WPA: Key negotiation completed with 00:11:22:44:88:ff [PTK=CCMP GTK=CCMP] <3>CTRL-EVENT-CONNECTED - Connection to 00:11:22:44:88:ff completed (auth) [id=0 id_str=] [ 1449.338287] wl1271: Association completed. <3>P2P-GROUP-STARTED wlan0 client ssid="DIRECT-84" freq=0 psk=00fa7decc5dab9f9f92dd0e959bc74bcd1c94d423f448ff5a0ce2b284c7a2ddc go_dev_addr=00:11:22:44:88:ff
EVM #1
<3>P2P-GO-NEG-SUCCESS [ 1447.211730] wl1271: down [ 1447.767883] wl1271: firmware booted (Rev 6.3.1.0.79_S11) <3>CTRL-EVENT-CONNECTED - Connection to 00:11:22:44:88:ff completed (auth) [id=0 id_str=] <3>CTRL-EVENT-CONNECTED - Connection to 00:00:00:00:00:00 completed (reauth) [id=0 id_str=] <3>WPS-ENROLLEE-SEEN 00:12:34:56:78:90 e8f01f99-6eb1-5234-bf7b-31bad179f7e8 [ 1448.068054] NOHZ: local_softirq_pending 08 0-00000000-0 0x2388 4 1 [ ] [ 1448.786254] NOHZ: local_softirq_pending 08 <3>WPS-ENROLLEE-SEEN 00:12:34:56:78:90 e8f01f99-6eb1-5234-bf7b-31bad179f7e8 [ 1448.811950] NOHZ: local_softirq_pending 08 0-00000000-0 0x2388 4 1 [ ] <3>WPS-ENROLLEE-SEEN 00:12:34:56:78:90 e8f01f99-6eb1-5234-bf7b-31bad179f7e8 0-00000000-0 0x2388 4 1 [ ] [ 1448.903167] NOHZ: local_softirq_pending 08 [ 1448.944885] NOHZ: local_softirq_pending 08 <3>CTRL-EVENT-EAP-STARTED 00[ 1448.954986] NOHZ: local_softirq_pending 08 :12:34:56:78:90 <3>CTRL-EVENT-EAP-PROPOSED-METHOD vendor=0 method=1 <3>CTRL-EVENT-EAP-PROPOSED-METHOD vendor=14122 method=254 [ 1452.306701] NOHZ: local_softirq_pending 08 [ 1452.467498] NOHZ: local_softirq_pending 08 [ 1452.481903] NOHZ: local_softirq_pending 08 [ 1452.491973] NOHZ: local_softirq_pending 08 <3>WPS-REG-SUCCESS 00:12:34:56:78:90 e8f01f99-6eb1-5234-bf7b-31bad179f7e8 <3>P2P-GROUP-FORMATION-SUCCESS <3>P2P-GROUP-STARTED wlan0 GO ssid="DIRECT-84" freq=2412 passphrase="H1heFTGz" go_dev_addr=00:11:22:44:88:ff <3>CTRL-EVENT-EAP-FAILURE 00:12:34:56:78:90 <3>WPS-ENROLLEE-SEEN 00:12:34:56:78:90 e8f01f99-6eb1-5234-bf7b-31bad179f7e8 0-00000000-0 0x2388 0 0 [ ] <3>AP-STA-CONNECTED 00:12:34:56:78:90
> ping 192.168.3.4 PONG
use ping command to verify connection. exit the wpa supplicant CLI by hitting "q"
> > q
use ping command to verify connection
root@am37x-evm:~# ping 192.168.3.3 PING 192.168.3.3 (192.168.3.3): 56 data bytes 64 bytes from 192.168.3.3: seq=0 ttl=64 time=11.810 ms 64 bytes from 192.168.3.3: seq=1 ttl=64 time=2.137 ms 64 bytes from 192.168.3.3: seq=2 ttl=64 time=2.442 ms 64 bytes from 192.168.3.3: seq=3 ttl=64 time=2.227 ms 64 bytes from 192.168.3.3: seq=4 ttl=64 time=2.106 ms
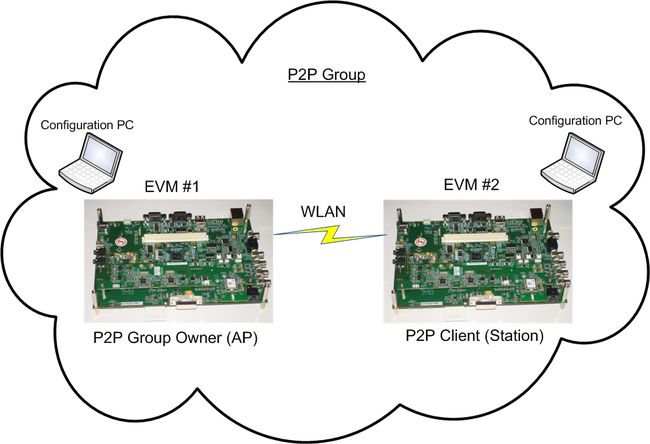
Create Autonomous 1:2 P2P Group (Push button Control)
Autonomous P2P Group is a group were the Group Owners may be determined
The Flow of commands in that usecase is as follows:
| Step # | EVM #1 | EVM #2 | Comments |
|---|---|---|---|
| 1 | Run WPA Supplicant | Run WPA Supplicant | R8.2 and before wpa_supplicant -d -Dnl80211 -c /etc/wpa_supplicant.conf -iwlan0 -B Post R8.2 wpa_supplicant -iwlan0 -Dnl80211 -c/etc/wpa_supplicant.conf -N -ip2p0 -Dnl80211 -c/etc/p2p_supplicant.conf |
| 2 | wpa_cli | wpa_cli | Run WPA Supplicant CLI |
| 3 | p2p_find | p2p_find | |
| 4 | p2p_peers | p2p_peers | verify p2p candidates MAC ADDRESS |
| 5 | p2p_group_add | define EVM#1 as Group Owner (GO) | |
| 6 | wps_pbc | work in Push Button mode | |
| 7 | p2p_connect EVM#1_MAC_ADDRESS pbc join | ||
| 9 | exit wpa_cli | exit wpa_cli | type: quit |
| 10 | Acquire IP address for wlan0 | Acquire IP address for wlan0 | ifconfig wlan0 192.168.1.108 |
| 11 | Verify connection with ping |
In order to configure the IP address to the Group Owner (GO) and the Clients there are 2 methods:
- Static IP
- Enable the DHCP server at the GO EVM, which will provide IP address to the clients using DHCP session
DHCP method
at the Group Owver EVM Run the following:
- Configure the udhcpd configuration file
- Run the dhcp server
- Define the iptables to enable the NAT (Network Address Translation)
Configuring udhcpd.confFirst, we will back up the existing udhcpd.conf file by invoking:
mv /etc/udhcpd.conf /etc/udhcpd.conf.bak
Create a new udhcpd.conf with the following content:
# Sample udhcpd configuration file (/etc/udhcpd.conf) # The start and end of the IP lease block start 192.168.0.20 #default: 192.168.0.20 end 192.168.0.254 #default: 192.168.0.254 # The interface that udhcpd will use interface wlan0 #default: eth0 #Examles opt dns 8.8.8.8 8.8.4.4 # public google dns servers option subnet 255.255.255.0 opt router 192.168.0.1 option lease 864000 # 10 days of
The editing above can be done by vi editor as follows:
-
vi /etc/udhcpd.conf
- The editor will be opened. Type the character 'i' to switch to editing mode.
- Copy and paste the above content into the editor.
- Hit 'esc' button to stop editing.
- Type the sequence ":wq" in order to save and quit.
Run the following
- udhcpd to operate the dhcp server
- iptables to enable the NAT (Network Address Translation)
The commands to do the above, are:
echo 1 > /proc/sys/net/ipv4/ip_forward ifconfig wlan0 192.168.0.1 udhcpd /etc/udhcpd.conf iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADE
The IP address assigned for wlan0 interface (ifconfig wlan0 192.168.0.1) should match the "router" field IP in the udhcpd.conf file we edited above.
At Client side
to get IP address using DHCP procedure run the following:
udhcpc -i wlan0
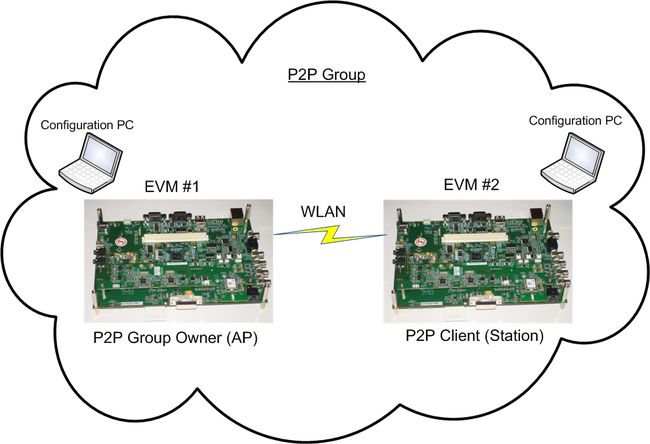
Create 1:2 P2P Group - Connect with PIN code
The Flow of commands in that use case is as follows:
comment: in that case we call the commands with wpa_cli before, instead of entering the wpa_cli menu first.
| Step # | EVM #1 | EVM #2 | Comments |
|---|---|---|---|
| 1 | run WPA Supplicant and WPA CLI | run WPA Supplicant and WPA CLI | R8.2 and before wpa_supplicant -d -Dnl80211 -c /etc/wpa_supplicant.conf -iwlan0 -B Post R8.2 wpa_supplicant -iwlan0 -Dnl80211 -c/etc/wpa_supplicant.conf -N -ip2p0 -Dnl80211 -c/etc/p2p_supplicant.conf |
| 2 | wpa_cli p2p_find | wpa_cli p2p_find | use wpa_cli prefix to run wpa cli commands (instead of entering wpa_cli utility) |
| 3 | wpa_cli p2p_peers | wpa_cli p2p_peers | verify p2p candidates MAC ADDRESS |
| 4 | wpa_cli p2p_connect EVM#2_MAC_ADDRESS pin auth | That command will print EVM#1 PIN-code in the follwoing line to that command | |
| 5 | wpa_cli p2p_connect EVM#2_MAC_ADDRESS EVM#1_PIN_CODE | getting EVM#1_PIN_CODE from previous EVM#1 command | |
| 6 | Define IP Address | Define IP Address | |
| 7 | Verify connection using ping |
Run the WPA supplicant in both EVMs
EVM #1
R8.2 and before: root@am37x-evm:~# wpa_supplicant -d -Dnl80211 -c /etc/wpa_supplicant.conf -iwlan0 -B Post R8.2: root@am37x-evm:~# wpa_supplicant -iwlan0 -Dnl80211 -c/etc/wpa_supplicant.conf -N -ip2p0 -Dnl80211 -c/etc/p2p_supplicant.conf &
EVM #2
R8.2 and before: root@am37x-evm:~# wpa_supplicant -d -Dnl80211 -c /etc/wpa_supplicant.conf -iwlan0 -B Post R8.2: root@am37x-evm:~# wpa_supplicant -iwlan0 -Dnl80211 -c/etc/wpa_supplicant.conf -N -ip2p0 -Dnl80211 -c/etc/p2p_supplicant.conf &
EVM #1
root@am37x-evm:~# wpa_cli p2p_find Selected interface 'wlan0' OK
EVM #2
root@am37x-evm:~# wpa_cli p2p_find Selected interface 'wlan0' OK
root@am37x-evm:~# wpa_cli p2p_peers Selected interface 'wlan0' 00:11:22:44:88:ff
EVM #1
root@am37x-evm:~# wpa_cli p2p_peers Selected interface 'wlan0' 00:12:34:56:78:90
EVM#1 defines the EVM#2 MAC Address in the connection commands, and as a response to that command we get the EVM#1 Pin-Code (in that example it is 33503165)
root@am37x-evm:~# wpa_cli p2p_connect 00:12:34:56:78:90 pin auth Selected interface 'wlan0' 33503165 root@am37x-evm:~#
EVM #2
EVM#2 attempt to connect EVM#1 with EVM#1 MAC Address and Pin-Code
root@am37x-evm:~# wpa_cli p2p_connect 00:11:22:44:88:ff 33503165 Selected interface 'wlan0' OK root@am37x-evm:~# [ 442.177673] wl1271: down [ 442.765930] wl1271: firmware booted (Rev 6.3.1.0.79_S88) [ 442.822906] wlan0: authenticate with 00:11:22:44:88:ff (try 1) [ 442.833923] wlan0: authenticated [ 442.934112] wlan0: deauthenticating from 00:11:22:44:88:ff by local choice (reason=2) [ 442.942535] wl1271: ERROR invalid hlid. dropping skb 0xced5fb40 [ 442.979156] wlan0: authenticate with 00:11:22:44:88:ff (try 1) [ 442.988433] wlan0: authenticated [ 443.033843] wlan0: associate with 00:11:22:44:88:ff (try 1) [ 443.045806] wlan0: RX AssocResp from 00:11:22:44:88:ff (capab=0x411 status=0 aid=1) [ 443.053924] wlan0: associated [ 443.745635] wlan0: deauthenticating from 00:11:22:44:88:ff by local choice (reason=3) [ 443.789825] cfg80211: Calling CRDA to update world regulatory domain [ 443.836059] cfg80211: World regulatory domain updated: [ 443.841552] cfg80211: (start_freq - end_freq @ bandwidth), (max_antenna_gain, max_eirp) [ 443.850341] cfg80211: (2402000 KHz - 2472000 KHz @ 40000 KHz), (300 mBi, 2000 mBm) [ 443.858703] cfg80211: (2457000 KHz - 2482000 KHz @ 20000 KHz), (300 mBi, 2000 mBm) [ 443.867034] cfg80211: (2474000 KHz - 2494000 KHz @ 20000 KHz), (300 mBi, 2000 mBm) [ 443.875366] cfg80211: (5170000 KHz - 5250000 KHz @ 40000 KHz), (300 mBi, 2000 mBm) [ 443.883697] cfg80211: (5735000 KHz - 5835000 KHz @ 40000 KHz), (300 mBi, 2000 mBm) [ 444.291687] wlan0: authenticate with 00:11:22:44:88:ff (try 1) [ 444.315979] wlan0: authenticated [ 444.346343] wlan0: associate with 00:11:22:44:88:ff (try 1) [ 444.383911] wlan0: RX ReassocResp from 00:11:22:44:88:ff (capab=0x411 status=0 aid=1) [ 444.392181] wlan0: associated [ 444.533752] wl1271: Association completed.
EVM #1
m37x-evm:~# [ 446.219635] wl1271: down [ 446.775390] wl1271: firmware booted (Rev 6.3.1.0.79_S88)
ifconfig wlan0 192.168.1.108 netmask 255.255.255.0 up
EVM #2
ifconfig wlan0 192.168.1.109 netmask 255.255.255.0 up
use ping command to verify connection
root@am37x-evm:~# ping 192.168.1.108 PING 192.168.1.108 (192.168.1.108): 56 data bytes 64 bytes from 192.168.1.108: seq=0 ttl=64 time=23.925 ms 64 bytes from 192.168.1.108: seq=1 ttl=64 time=2.929 ms 64 bytes from 192.168.1.108: seq=2 ttl=64 time=3.662 ms 64 bytes from 192.168.1.108: seq=3 ttl=64 time=4.242 ms 64 bytes from 192.168.1.108: seq=4 ttl=64 time=14.587 ms
P2P Invitation Procedure - Create Autonomous 1:2 P2P Group, (Push button Control)
- P2P Invitation Request frame is transmitted by a P2P Group Owner or a P2P Client in that P2P Group
- Upon receipt of the P2P Invitation Request, a P2P Device that supports the P2P Invitation Procedure signaling mechanism transmits a P2P Invitation Response frame.
- The decision to accept the invitation is left to the invited P2P Device
The Flow of commands shows a case where the EVM#1 is the GO and invites EVM#2:
| Step # | EVM #1 | EVM #2 | Comments |
|---|---|---|---|
| 1 | Run WPA Supplicant | Run WPA Supplicant | R8.2 and before wpa_supplicant -d -Dnl80211 -c /etc/wpa_supplicant.conf -iwlan0 -B Post R8.2 wpa_supplicant -iwlan0 -Dnl80211 -c/etc/wpa_supplicant.conf -N -ip2p0 -Dnl80211 -c/etc/p2p_supplicant.conf |
| 2 | wpa_cli | wpa_cli | Run WPA Supplicant CLI |
| 3 | p2p_group_add freq=2412 | ||
| 4 | wps_pbc | ||
| 5 | wait after the remote "p2p_find" | ||
| 6 | p2p_find | ||
| 7 | p2p_invite group=wlan0 peer=EVM#2_MAC_ADDRESS | ||
| 8 | p2p_connect EVM#1_MAC_ADDRESS pbc auth join | ||
| 9 | exit wpa_cli | exit wpa_cli | type: quit |
| 10 | Acquire IP address for wlan0 | Acquire IP address for wlan0 | ifconfig wlan0 192.168.1.108 |
| 11 | Verify connection with ping |
Detailed information
p2p_find
Start P2P device discovery. Optional parameter can be used to specify the duration for the discovery in seconds (e.g., "P2P_FIND 5"). If the duration is not specified, discovery will be started for indefinite time, i.e., until it is terminated by P2P_STOP_FIND or P2P_CONNECT (to start group formation with a discovered peer). The default search type is to first run a full scan of all channels and then continue scanning only social channels (1, 6, 11). This behavior can be changed by specifying a different search type: social (e.g., "P2P_FIND 5 type=social") will skip the initial full scan and only search social channels; progressive (e.g., "P2P_FINDtype=progressive") starts with a full scan and then searches progressively through all channels one channel at the time with the social channel scans. Progressive device discovery can be used to find new groups (and groups that were not found during the initial scan,e.g., due to the GO being asleep) over time without adding considerable extra delay for every Search state round.
p2p_connect
Start P2P group formation with a discovered P2P peer. This includes group owner negotiation, group interface setup, provisioning, and establishing data connection.P2P_CONNECT <peer device address> <pbc|pin|PIN#> [label|display|keypad] [persistent] [join|auth] [go_intent=<0..15>] [freq=<in MHz>]Start P2P group formation with a discovered P2P peer. This includes optional group owner negotiation, group interface setup, provisioning, and establishing data connection.The <pbc|pin|PIN#> parameter specifies the WPS provisioning method. "pbc" string starts pushbutton method, "pin" string start PIN method using an automatically generated PIN (which will be returned as the command return code), PIN# means that a pre-selected PIN can be used (e.g., 12345670). [label|display|keypad] is used with PIN method to specify which PIN is used (label=PIN from local label, display=dynamically generated random PIN from local display, keypad=PIN entered from peer device label or display).
"persistent" parameter can be used to request a persistent group to be formed.
"join" indicates that this is a command to join an existing group as a client. It skips the GO Negotiation part.
"auth" indicates that the WPS parameters are authorized for the peer device without actually starting GO Negotiation (i.e., the peer is expected to initiate GO Negotiation). This is mainly for testing purposes.The optional "go_intent" parameter can be used to override the default GO Intent value.
p2p_listen
Start Listen-only state. Optional parameter can be used to specify the duration for the Listen operation in seconds. This command may not be of that much use during normal operations and is mainly designed for testing. It can also be used to keep the device discoverable without having to maintain a group.
p2p_group_add
Set up a P2P group owner manually (i.e., without group owner negotiation with a specific peer). This is also known as autonomous GO. P2P_GROUP_ADD [persistent] [freq=<in MHz>]
Optional persistent=<network id> can be used to specify restart of a persistent group.Optional freq is channel frequency in MHz for the group.
p2p_group_remove
Terminate a P2P group. If a new virtual network interface was used for the group, it will also be removed. The network interface name of the group interface is used as a parameter for this command.
P2P_GROUP_REMOVE <ifname>
<ifname> is network interface name of the group interface or "*" to remove all.
p2p_peer
Fetch information about a discovered peer. Show information about known P2P peer(s).
P2P_PEER [addr] [FIRST] [NEXT-<P2P Device Address>]
This command takes in an argument specifying which peer to select: P2P Device Address of the peer, "FIRST" to indicate the first peer in the list, or "NEXT-<P2P Device Address>" to indicate the entry following the specified peer (to allow for iterating through the list).
p2p_invite
Invite a peer to join a group or to (re)start a persistent group.P2P_INVITE <cmd> [peer=addr]
<cmd> format is:<persistent=id> [peer=addr] to restart persistent group where id is a unique network identifier<group= > <peer=addr> [go_dev_addr=addr] to invite peer to join an active group
P2P EVENTS
Following events can be received from wpa_supplicant via control interface.The events are specified in hostap/src/common/wpa_ctrl.h
P2P_EVENT_DEVICE_FOUND
Indication of a discovered P2P device with information about that device.For example:
P2P-DEVICE-FOUND 02:b5:64:63:30:63 p2p_dev_addr=02:b5:64:63:30:63pri_dev_type=1-0050f204-1 name='Wireless Client' config_methods=0x84dev_capab=0x21 group_capab=0x0
P2P_EVENT_GO_NEG_REQUEST
A P2P device requested GO negotiation, but we were not ready to start the negotiation.For example:
P2P-GO-NEG-REQUEST 02:40:61:c2:f3:b7 dev_passwd_id=4
P2P_EVENT_GO_NEG_SUCCESS
Indication of successfully complete group owner negotiation.P2P-GO-NEG-SUCCESS
P2P_EVENT_GO_NEG_FAILURE
Indication of failed group owner negotiation. Additional parameter is status.
P2P-GO-NEG-FAILURE status=1
P2P_EVENT_GROUP_FORMATION_SUCCESS
Indication that P2P group formation has been completed successfully.
P2P-GROUP-FORMATION-SUCCESS
P2P_EVENT_GROUP_FORMATION_FAILURE
Indication that P2P group formation failed (e.g., due to provisioning failure or timeout).
P2P-GROUP-FORMATION-FAILURE
P2P_EVENT_GROUP_STARTED =
Indication of a new P2P group having been started. Additional parameters: network interface name for the group, role (GO/client), SSID, frequency. The passphrase used in the group is also indicated here if known (on GO) or PSK (on client). If the group is a persistent one, a flag indicating that is included.For example:
P2P-GROUP-STARTED wlan0-p2p-0 GO ssid="DIRECT-3F Testing" freq=2412passphrase="12345678" go_dev_addr=02:40:61:c2:f3:b7 [PERSISTENT]
P2P_EVENT_GROUP_REMOVED
Indication of a P2P group having been removed. Additional parameters: network interface name for the group, role (GO/client).For example:
P2P-GROUP-REMOVED wlan0-p2p-0 GO
P2P_EVENT_CROSS_CONNECT_ENABLE
Indication of allowing of P2P cross connection with uplink network interface. Additional parameters: network interface name for the group, cross connect uplink network interface name.For example:
P2P-CROSS-CONNECT-ENABLE wlan0-p2p-0 wan0
P2P_EVENT_CROSS_CONNECT_DISABLE
Indication of disabling of P2P cross-connection with uplink network interface. Additional parameters: network interface name for the group, cross connect uplink network interface name.For example:
P2P-CROSS-CONNECT- DISABLE wlan0-p2p-0 wan0
P2P_EVENT_PROV_DISC_SHOW_PIN
Request from the peer for local p2p device to display a PIN that will be entered on the peer. The following parameters are included after the event prefix: peer_address, PIN. The PIN is a random PIN generated for this connection. P2P_CONNECT command can be used to accept the request with the same PIN configured for the connection.For example:
P2P-PROV-DISC-SHOW-PIN 02:40:61:c2:f3:b7 12345670 p2p_dev_addr=02:40:61:c2:f3:b7 pri_dev_type=1-0050F204-1 name='Test' config_methods=0x188 dev_capab=0x21 group_capab=0x0
P2P_EVENT_PROV_DISC_ENTER_PIN
Request from the peer for local p2p device to enter a PIN displayed on the peer. The following parameter is included after the event prefix: peer address, device type, name and capabilities.For example:
P2P-PROV-DISC-ENTER-PIN 02:40:61:c2:f3:b7 p2p_dev_addr=02:40:61:c2:f3:b7pri_dev_type=1-0050F204-1 name='Test' config_methods=0x188 dev_capab=0x21 group_capab=0x0
P2P_EVENT_PROV_DISC_PBC_REQ
Request from the peer for local p2p device to connect using PBC. The following parameters are included after the event prefix: peer_address, device type, name and capabilities. P2P_CONNECT command can be used to accept the request.
For example:
P2P-PROV-DISC-PBC-REQ 02:40:61:c2:f3:b7 p2p_dev_addr=02:40:61:c2:f3:b7pri_dev_type=1-0050F204-1 name='Test' config_methods=0x188 dev_capab=0x21 group_capab=0x0
P2P_EVENT_PROV_DISC_PBC_RESP
The peer accepted our provision discovery request to connect using PBC. The following parameters are included after the event prefix: peer_address. P2P_CONNECT command can be used to start GO Negotiation after this.For example:
P2P-PROV-DISC-PBC-RESP 02:40:61:c2:f3:b7
P2P_EVENT_SERV_DISC_REQ
Indicate reception of a P2P service discovery request. The following parameters are included after the event prefix: frequency in MHz, source address, dialog token, service update indicator, Service Query TLV(s) as hexdump.For example:
P2P-SERV-DISC-REQ 2412 02:40:61:c2:f3:b7 0 0 02000001
P2P_EVENT_SERV_DISC_RESP
Indicate reception of a P2P service discovery response. The following parameters are included after the event prefix: source address, dialog token, service update indicator, Service Responce TLV(s) as hexdump.For example:
P2P-SERV-DISC-RESP 02:40:61:c2:f3:b7 0 0 0300000101
P2P_EVENT_INVITATION_RECEIVED
Indicate reception of a P2P Invitation Request. For persistent groups, the parameter after the event prefix indicates which network block includes the persistent group data.For example:
P2P-INVITATION-RECEIVED sa=02:40:61:c2:f3:b7 persistent=0
P2P_EVENT_INVITATION_RESULT
Indicate result of a P2P invitation that was requested with P2P_INVITE command. The parameter status=<value> shows the status code returned by the peer (or -1 on local failure or timeout).For example:
P2P-INVITATION-RESULT status=1