openssl生成CA证书
什么是x509证书链
- x509证书一般会用到三类文件,key,csr,crt。
- key是私用密钥,openssl格式,通常是rsa算法。
- csr是证书请求文件,用于申请证书。在制作csr文件的时候,必须使用自己的私钥来签署申请,还可以设定一个密钥。
- crt是CA认证后的证书文件(windows下面的csr,其实是crt),签署人用自己的key给你签署的凭证。
概念
证书类别
- 根证书 生成服务器证书,客户端证书的基础。自签名。
- 服务器证书 由根证书签发。配置在服务器上。
- 客户端证书 由根证书签发。配置在服务器上,并发送给客户,让客户安装在浏览器里。
要注意
- 服务器证书的cn要和servername一致,否则启动httpd时有警告。
- 浏览器安装客户端证书时,需要用pkcs12转换成pfx格式,否则可以安装但无效。
- 把根证书安装到浏览器的受信CA中,访问服务器时就不会出警告了。
首先要有一个CA根证书,然后用CA根证书来签发用户证书。用户进行证书申请:一般先生成一个私钥,然后用私钥生成证书请求(证书请求里应含有公钥信息),再利用证书服务器的CA根证书来签发证书。
openssl中有如下后缀名的文件
-
.key格式:私有的密钥
-
.csr格式:证书签名请求(证书请求文件),含有公钥信息,certificate signing request的缩写
-
.crt格式:证书文件,certificate的缩写
-
.crl格式:证书吊销列表,Certificate Revocation List的缩写
-
.pem格式:用于导出,导入证书时候的证书的格式,有证书开头,结尾的格式
-
.p12 "或者 “.pfx” : 用于实现存储许多加密对象在一个单独的文件中。通常用它来打包一个私钥及有关的 X.509 证书,或者打包信任链的全部项目。
CA根证书的生成步骤
生成CA私钥(.key)–>生成CA证书请求(.csr)–>自签名得到根证书(.crt)(CA给自已颁发的证书)。
# Generate CA private key (制作ca.key 私钥)
openssl genrsa -out ca.key 2048
# Generate CSR
openssl req -new -key ca.key -out ca.csr
#OpenSSL创建的自签名证书在chrome端无法信任,需要添加如下
echo "subjectAltName=DNS:rojao.test.com,IP:10.10.2.137" > cert_extensions
# Generate Self Signed certificate(CA 根证书)
openssl x509 -req -days 365 -in ca.csr -signkey ca.key -extfile cert_extensions -out ca.crt
整个提示将如下所示:
OutputCountry Name (2 letter code) [AU]:CN
State or Province Name (full name) [Some-State]:Guangdong
Locality Name (eg, city) []:Guangzhou
Organization Name (eg, company) [Internet Widgits Pty Ltd]:Rojao, Inc.
Organizational Unit Name (eg, section) []:R&D Department
Common Name (e.g. server FQDN or YOUR name) []:Rojao CA ROOT
Email Address []:[email protected]
在实际的软件开发工作中,往往服务器就采用这种自签名的方式,因为毕竟找第三方签名机构是要给钱的,也是需要花时间的。
用户证书的生成步骤
生成私钥(.key)–>生成证书请求(.csr)–>用CA根证书签名得到证书(.crt)
服务器端用户证书
# private key
openssl genrsa -des3 -out server.key 2048
# generate csr
openssl req -new -key server.key -out server.csr
#OpenSSL创建的自签名证书在chrome端无法信任,需要添加如下
echo "subjectAltName=DNS:rojao.test.com,IP:10.10.2.137" > cert_extensions
# generate certificate
openssl ca -in server.csr -out server.crt -extfile cert_extensions -cert ca.crt -keyfile ca.key
最重要的一行是Common Name (e.g. server FQDN or YOUR name)那一行。您需要输入与服务器关联的域名,或者是您服务器的公共IP地址。
整个提示将如下所示:
OutputCountry Name (2 letter code) [AU]:CN
State or Province Name (full name) [Some-State]:Guangdong
Locality Name (eg, city) []:Guangzhou
Organization Name (eg, company) [Internet Widgits Pty Ltd]:Rojao, Inc.
Organizational Unit Name (eg, section) []:R&D Department
Common Name (e.g. server FQDN or YOUR name) []:10.10.2.137
Email Address []:[email protected]
假如报错:/etc/pki/CA/index.txt: No such file or directory
unable to open '/etc/pki/CA/index.txt解决:创建/etc/pki/CA/index.txt文件
mkdir -p CA/newcerts
touch CA/index.txt
touch CA/serial
echo “01” > CA/serial
客户端用户证书
openssl genrsa -des3 -out client.key 1024
openssl req -new -key client.key -out client.csr
openssl ca -in client.csr -out client.crt -cert ca.crt -keyfile ca.key
报错:failed to update database
TXT_DB error number 2删除之前创建的 index.txt serial 文件后重建
证书导出
生成pem格式证书
有时需要用到pem格式的证书,可以用以下方式合并证书文件(crt)和私钥文件(key)来生成
cat client.crt client.key> client.pem
cat server.crt server.key > server.pem
结果:
服务端证书:ca.crt, server.key, server.crt, server.pem
客户端证书:ca.crt, client.key, client.crt, client.pem
生成pfx(p12)格式 证书
openssl pkcs12 -export -in server.crt -out server.p12 -inkey server.key
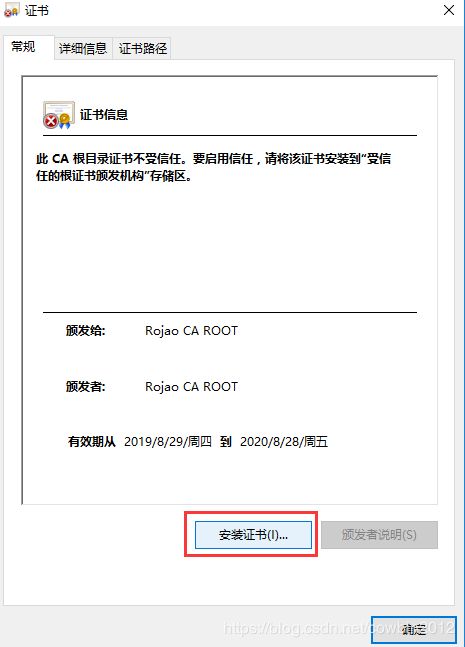
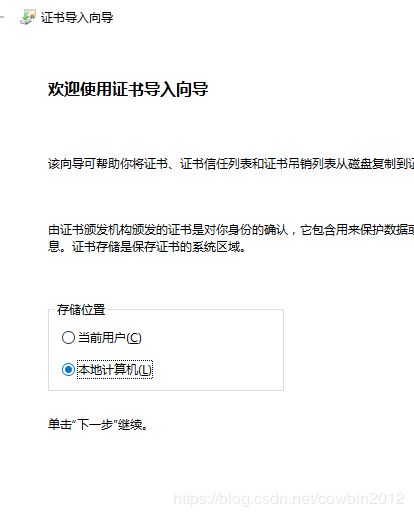
浏览器导入根证书(window10)
服务端证书配置
nginx配置
修改配置文件nginx.conf
server {
listen 443 ssl;
server_name localhost;
ssl_certificate /opt/ssl/server.crt;
ssl_certificate_key /opt/ssl/server.key;
ssl_session_cache shared:SSL:1m;
ssl_session_timeout 5m;
ssl_ciphers HIGH:!aNULL:!MD5;
ssl_prefer_server_ciphers on;
location / {
root html;
index index.html index.htm;
}
}
Nginx 配置Http和Https共存
server {
listen 80 default backlog=2048;
listen 443 ssl;
server_name localhost;
ssl_certificate /opt/ssl/server.crt;
ssl_certificate_key /opt/ssl/server.key;
ssl_session_cache shared:SSL:1m;
ssl_session_timeout 5m;
ssl_ciphers HIGH:!aNULL:!MD5;
ssl_prefer_server_ciphers on;
location / {
root html;
index index.html index.htm;
}
}
Nginx SSL性能调优
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
ssl_ciphers ECDHE-RSA-AES256-SHA384:AES256-SHA256:RC4:HIGH:!MD5:!aNULL:!eNULL:!NULL:!DH:!EDH:!AESGCM;
ssl_prefer_server_ciphers on;
ssl_session_cache shared:SSL:10m;
ssl_session_timeout 10m;
springboot2
server:
port: 8443
ssl:
key-store: classpath:server.p12
key-store-password: 123456
key-store-type: PKCS12