wctf逆向两道write up
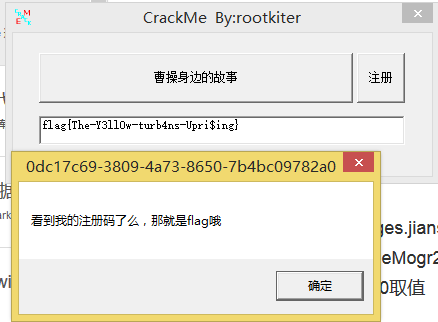
crackme
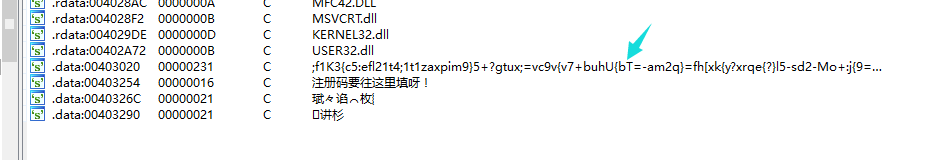
逆向学习中字符串查询是个非常好的工具:
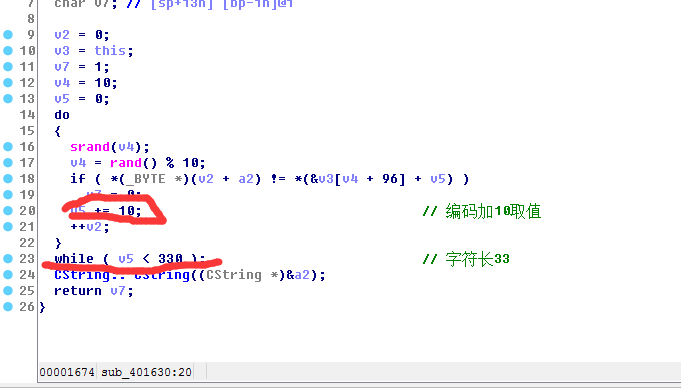
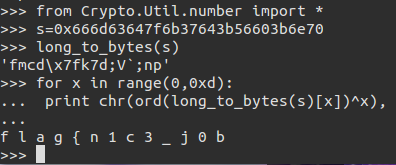
于是把这些字符串从f开始加10取值
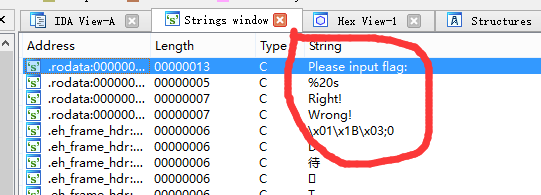
babyre:
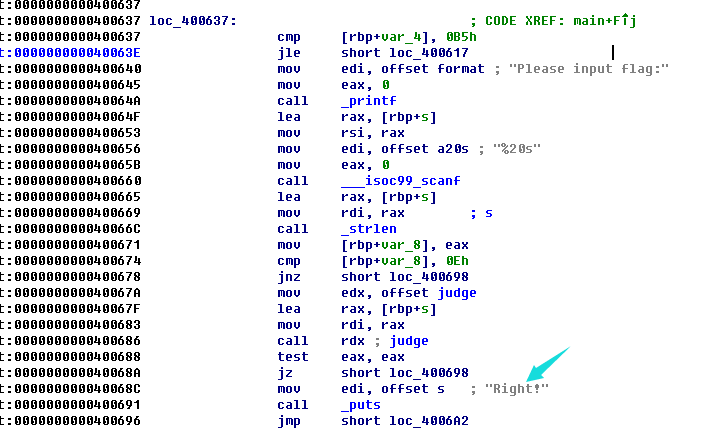
找到对应主函数:
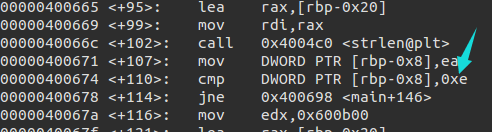
在0000400686处下断点,动态调试:
由图flag字长14
0x0000000000600b00 <+0>: push rbp
0x0000000000600b01 <+1>: mov rbp,rsp
0x0000000000600b04 <+4>: mov QWORD PTR [rbp-0x28],rdi
0x0000000000600b08 <+8>: mov BYTE PTR [rbp-0x20],0x66
0x0000000000600b0c <+12>: mov BYTE PTR [rbp-0x1f],0x6d
0x0000000000600b10 <+16>: mov BYTE PTR [rbp-0x1e],0x63
0x0000000000600b14 <+20>: mov BYTE PTR [rbp-0x1d],0x64
0x0000000000600b18 <+24>: mov BYTE PTR [rbp-0x1c],0x7f
0x0000000000600b1c <+28>: mov BYTE PTR [rbp-0x1b],0x6b
0x0000000000600b20 <+32>: mov BYTE PTR [rbp-0x1a],0x37
0x0000000000600b24 <+36>: mov BYTE PTR [rbp-0x19],0x64
0x0000000000600b28 <+40>: mov BYTE PTR [rbp-0x18],0x3b
0x0000000000600b2c <+44>: mov BYTE PTR [rbp-0x17],0x56
0x0000000000600b30 <+48>: mov BYTE PTR [rbp-0x16],0x60
0x0000000000600b34 <+52>: mov BYTE PTR [rbp-0x15],0x3b
0x0000000000600b38 <+56>: mov BYTE PTR [rbp-0x14],0x6e
0x0000000000600b3c <+60>: mov BYTE PTR [rbp-0x13],0x70
0x0000000000600b40 <+64>: mov DWORD PTR [rbp-0x4],0x0
0x0000000000600b47 <+71>: jmp 0x600b71
0x0000000000600b49 <+73>: mov eax,DWORD PTR [rbp-0x4]
0x0000000000600b4c <+76>: movsxd rdx,eax
0x0000000000600b4f <+79>: mov rax,QWORD PTR [rbp-0x28]
0x0000000000600b53 <+83>: add rax,rdx
0x0000000000600b56 <+86>: mov edx,DWORD PTR [rbp-0x4]
0x0000000000600b59 <+89>: movsxd rcx,edx
0x0000000000600b5c <+92>: mov rdx,QWORD PTR [rbp-0x28]
0x0000000000600b60 <+96>: add rdx,rcx
0x0000000000600b63 <+99>: movzx edx,BYTE PTR [rdx]
0x0000000000600b66 <+102>: mov ecx,DWORD PTR [rbp-0x4]
0x0000000000600b69 <+105>: xor edx,ecx
0x0000000000600b6b <+107>: mov BYTE PTR [rax],dl
0x0000000000600b6d <+109>: add DWORD PTR [rbp-0x4],0x1
0x0000000000600b71 <+113>: cmp DWORD PTR [rbp-0x4],0xd
0x0000000000600b75 <+117>: jle 0x600b49
0x0000000000600b77 <+119>: mov DWORD PTR [rbp-0x4],0x0
0x0000000000600b7e <+126>: jmp 0x600ba9
0x0000000000600b80 <+128>: mov eax,DWORD PTR [rbp-0x4]
0x0000000000600b83 <+131>: movsxd rdx,eax
0x0000000000600b86 <+134>: mov rax,QWORD PTR [rbp-0x28]
0x0000000000600b8a <+138>: add rax,rdx
0x0000000000600b8d <+141>: movzx edx,BYTE PTR [rax]
0x0000000000600b90 <+144>: mov eax,DWORD PTR [rbp-0x4]
0x0000000000600b93 <+147>: cdqe
0x0000000000600b95 <+149>: movzx eax,BYTE PTR [rbp+rax*1-0x20]
0x0000000000600b9a <+154>: cmp dl,al
0x0000000000600b9c <+156>: je 0x600ba5
0x0000000000600b9e <+158>: mov eax,0x0
0x0000000000600ba3 <+163>: jmp 0x600bb4
0x0000000000600ba5 <+165>: add DWORD PTR [rbp-0x4],0x1
0x0000000000600ba9 <+169>: cmp DWORD PTR [rbp-0x4],0xd
0x0000000000600bad <+173>: jle 0x600b80
0x0000000000600baf <+175>: mov eax,0x1
0x0000000000600bb4 <+180>: pop rbp
0x0000000000600bb5 <+181>: ret
两次循环:
1.将输入异或,输入的数组与其次序异或
2.将异或后的数组与原数组进行比较
关于Crypto.Util.number用法:
https://www.dlitz.net/software/pycrypto/api/current/Crypto.Util.number-module.html
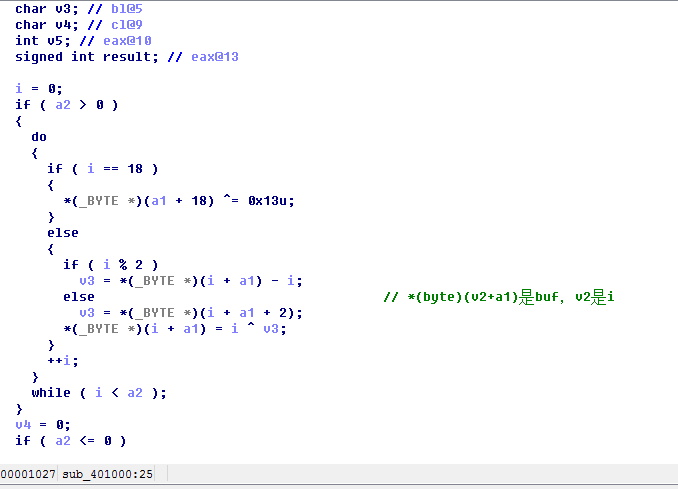
第三道逆向题:
buf = [ord(i) for i in '616A79676B466D2E7F5F7E2D53567B386D4C6E00'.decode('hex')]
buf[18] ^= 0x13
for i in range(17, -1, -1):
v3 = i ^ buf[i]
if i % 2:
buf[i] = v3 + i
else:
buf[i+2] = v3
print ''.join(chr(i) for i in buf)
whctf 之write up: