班级:1518011
姓名:于沂渭
学号:151801100005
1. 测试网页已前置 Apache
2.安装并配置 ModSecurity 模块,搭建 WAF。
2.1 环境安装
安装 LAMP Server
$ sudo apt-get install apache2 mysql-server libapache2-mod-auth-mysql php-mysql php libapache2-mod-php php-mcrypt
安装 libapache2-modsecurity 模块及其依赖包
$ sudo apt-get install libxml2 libxml2-dev libxml2-utils libaprutil1 libaprutil1-dev libapache2-modsecurity
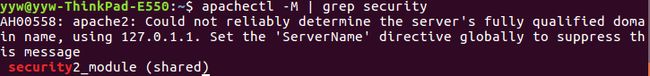
查看安装情况,如果一切正常,您应该看到以下输出:
2.2 配置mod_security
默认情况下,mod_security 不起作用,因为它需要规则才能工作。首先,需要重命名位于/etc/modsecurity目录下的 modsecurity.conf-recommended 文件示例:
$ sudo mv /etc/modsecurity/modsecurity.conf-recommended /etc/modsecurity/modsecurity.conf
然后修改配置文件
$ sudo vim /etc/modsecurity/modsecurity.conf
SecRuleEngine on
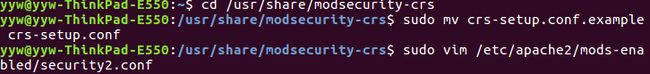
2.3 搭建 WAF
默认情况下,mod_security 附带位于 /usr/share/modsecurity-crs 目录的核心规则集(安全规则)。但建议从 GitHub 存储库下载 mod_security CRS 。
修改配置文件
$ sudo vim /etc/apache2/mods-enabled/security2.conf
SecDataDir /var/cache/modsecurity
IncludeOptional /etc/modsecurity/*.conf
IncludeOptional /usr/share/modsecurity-crs/*.conf
IncludeOptional /usr/share/modsecurity-crs/rules/*.conf
重启 Apache 服务
$ sudo systemctl restart apache2
3. 根据文档自行编写,或者在 OWASP ModSecurity CRS 规则库的基础上修改,对 SQL 注入攻击进行阻断并报警。
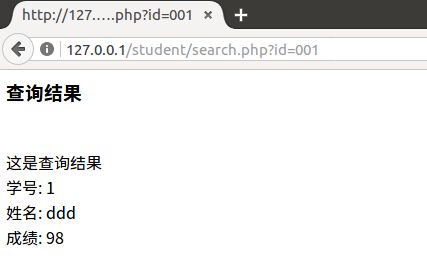
SQL 注入测试
测试 mod_security 如何保护 Apache Web 服务器免受 SQL 攻击
正常访问:
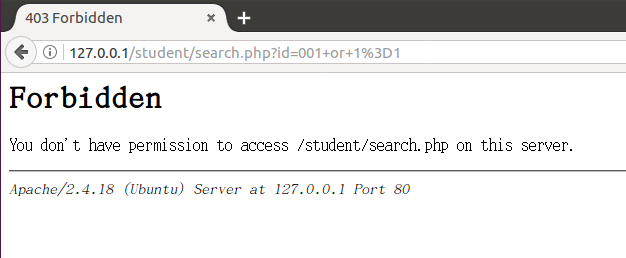
尝试 SQL 注入:
001 or 1=1
在以下输出中看到 403 Forbidden 响应:
查看日志文件,选择最下面的最新日志
$ sudo vim /var/log/apache2/modsec_audit.log
--adbda74e-A--
[11/Jul/2018:20:45:36 +0800] W0X78H8AAQEAACbUCz4AAAAA 127.0.0.1 33846 127.0.0.1 80
--adbda74e-B--
GET /student/search.php?id=15180110007+or+1%3D1 HTTP/1.1
Host: 127.0.0.1
User-Agent: curl/7.47.0
Accept: /
--adbda74e-F--
HTTP/1.1 403 Forbidden
Content-Length: 302
Content-Type: text/html; charset=iso-8859-1
--adbda74e-E--
403 Forbidden
Forbidden
You don't have permission to access /student/search.php
on this server.
Apache/2.4.18 (Ubuntu) Server at 127.0.0.1 Port 80
--adbda74e-H--
Message: Warning. Pattern match "^[\d.:]+$" at REQUEST_HEADERS:Host. [file "/usr/share/modsecurity-crs/rules/REQUEST-920-PROTOCOL-ENFORCEMENT.conf"] [line "810"] [id "920350"] [rev "2"] [msg "Host header is a numeric IP address"] [data "127.0.0.1"] [severity "WARNING"] [ver "OWASP_CRS/3.0.0"] [maturity "9"] [accuracy "9"] [tag "application-multi"] [tag "language-multi"] [tag "platform-multi"] [tag "attack-protocol"] [tag "OWASP_CRS/PROTOCOL_VIOLATION/IP_HOST"] [tag "WASCTC/WASC-21"] [tag "OWASP_TOP_10/A7"] [tag "PCI/6.5.10"]
Message: Warning. detected SQLi using libinjection with fingerprint '1&1' [file "/usr/share/modsecurity-crs/rules/REQUEST-942-APPLICATION-ATTACK-SQLI.conf"] [line "68"] [id "942100"] [rev "1"] [msg "SQL Injection Attack Detected via libinjection"] [data "Matched Data: 1&1 found within ARGS:id: 15180110007 or 1=1"] [severity "CRITICAL"] [ver "OWASP_CRS/3.0.0"] [maturity "1"] [accuracy "8"] [tag "application-multi"] [tag "language-multi"] [tag "platform-multi"] [tag "attack-sqli"] [tag "OWASP_CRS/WEB_ATTACK/SQL_INJECTION"] [tag "WASCTC/WASC-19"] [tag "OWASP_TOP_10/A1"] [tag "OWASP_AppSensor/CIE1"] [tag "PCI/6.5.2"]
Message: Access denied with code 403 (phase 2). Operator GE matched 5 at TX:anomaly_score. [file "/usr/share/modsecurity-crs/rules/REQUEST-949-BLOCKING-EVALUATION.conf"] [line "57"] [id "949110"] [msg "Inbound Anomaly Score Exceeded (Total Score: 8)"] [severity "CRITICAL"] [tag "application-multi"] [tag "language-multi"] [tag "platform-multi"] [tag "attack-generic"]
Message: Warning. Operator GE matched 5 at TX:inbound_anomaly_score. [file "/usr/share/modsecurity-crs/rules/RESPONSE-980-CORRELATION.conf"] [line "73"] [id "980130"] [msg "Inbound Anomaly Score Exceeded (Total Inbound Score: 8 - SQLI=5,XSS=0,RFI=0,LFI=0,RCE=0,PHPI=0,HTTP=0,SESS=0): SQL Injection Attack Detected via libinjection"] [tag "event-correlation"]
Action: Intercepted (phase 2)
Apache-Handler: application/x-httpd-php
Stopwatch: 1531313136934105 1209 (- - -)
Stopwatch2: 1531313136934105 1209; combined=920, p1=247, p2=600, p3=0, p4=0, p5=72, sr=8, sw=1, l=0, gc=0
Response-Body-Transformed: Dechunked
Producer: ModSecurity for Apache/2.9.0 ( http://www.modsecurity.org/); OWASP_CRS/3.0.2.
Server: Apache/2.4.18 (Ubuntu)
Engine-Mode: "ENABLED"
--adbda74e-Z--
4. 尝试对特定扫描器或发包工具(paros、w3af 等)的 User-Agent 进行检测和报警,并在单个 IP 访问数量超过一定门限后对来源 IP 进行封禁。
4.1 安装 W3AF
$ git clone https://github.com/andresriancho/w3af.git
$ cd w3af/
$ ./w3af_console
在执行 w3af_console 文件时,有时会提示系统未安装很多依赖环境,需要安装的环境,已经写在了 /tmp 目录下的 w3af_dependency_install.sh 文件里面,执行它即会自动下载安装所需的所有文件。
$ . /tmp/w3af_dependency_install.sh
上述步骤完成后可在终端中操作:
4.2 使用 W3AF 进行 SQL 注入
两次注入使用同一规则
$ w3af_console
w3af>>> plugins
w3af/plugins>>> audit sqli,xss
w3af/plugins>>> back
w3af>>> plugins
w3af/plugins>>> output htmlFile,console,gtkOutput
w3af/plugins>>> output config console
w3af/plugins/output/config:console>>> set verbose True
w3af/plugins/output/config:console>>> back
w3af/plugins>>> output config gtkOutput
w3af/plugins/output/config:gtkOutput>>> back
w3af/plugins>>> back
w3af>>> plugins
w3af/plugins>>> discovery webSpider
w3af/plugins>>> back
w3af>>> target
w3af/config:target>>> set target http://127.0.0.1/student/
w3af/config:target>>> back
w3af>>> start
此时关闭 ModSecurity 模块
`Enabling _dnsCache()
Called buildOpeners
keepalive: added one connection, len(self._hostmap["127.0.0.1"]): 1
DNS response from DNS server for domain: 127.0.0.1
GET http://127.0.0.1/student/ returned HTTP code "403" - id: 1
[thread manager] Successfully added function to threadpool. Work queue size: 1
[thread manager] Successfully added function to threadpool. Work queue size: 2
[thread manager] Successfully added function to threadpool. Work queue size: 3
[thread manager] Successfully added function to threadpool. Work queue size: 4
[thread manager] Successfully added function to threadpool. Work queue size: 5
[thread manager] Successfully added function to threadpool. Work queue size: 6
[thread manager] Successfully added function to threadpool. Work queue size: 7
[thread manager] Successfully added function to threadpool. Work queue size: 8
[thread manager] Successfully added function to threadpool. Work queue size: 9
[thread manager] Successfully added function to threadpool. Work queue size: 10
[thread manager] Successfully added function to threadpool. Work queue size: 11
[thread manager] Successfully added function to threadpool. Work queue size: 12
[thread manager] Successfully added function to threadpool. Work queue size: 13
[thread manager] Successfully added function to threadpool. Work queue size: 14
keepalive: added one connection, len(self._hostmap["127.0.0.1"]): 2
Cached DNS response for domain: 127.0.0.1
keepalive: added one connection, len(self._hostmap["127.0.0.1"]): 3
Cached DNS response for domain: 127.0.0.1
keepalive: added one connection, len(self._hostmap["127.0.0.1"]): 4
Cached DNS response for domain: 127.0.0.1
keepalive: added one connection, len(self._hostmap["127.0.0.1"]): 5
Cached DNS response for domain: 127.0.0.1
GET http://127.0.0.1/student/ww1yYZl9.htm returned HTTP code "403" - id: 2
No grep for: "http://127.0.0.1/student/ww1yYZl9.htm", the plugin sent grep=False.
GET http://127.0.0.1/student/UBd6Bxxt.py returned HTTP code "403" - id: 3
No grep for: "http://127.0.0.1/student/UBd6Bxxt.py", the plugin sent grep=False.
GET http://127.0.0.1/student/boQkOdd9.asp returned HTTP code "403" - id: 6
GET http://127.0.0.1/student/Kq9Kl3OI.do returned HTTP code "403" - id: 5
No grep for: "http://127.0.0.1/student/Kq9Kl3OI.do", the plugin sent grep=False.
No grep for: "http://127.0.0.1/student/boQkOdd9.asp", the plugin sent grep=False.
GET http://127.0.0.1/student/5HE5HJbF.gif returned HTTP code "403" - id: 7
GET http://127.0.0.1/student/wkOiP2IM. returned HTTP code "403" - id: 4
No grep for: "http://127.0.0.1/student/wkOiP2IM.", the plugin sent grep=False.
No grep for: "http://127.0.0.1/student/5HE5HJbF.gif", the plugin sent grep=False.
GET http://127.0.0.1/student/y2mbi09u.htmls returned HTTP code "403" - id: 8
No grep for: "http://127.0.0.1/student/y2mbi09u.htmls", the plugin sent grep=False.
GET http://127.0.0.1/student/TGc5v5NN.rb returned HTTP code "403" - id: 9
No grep for: "http://127.0.0.1/student/TGc5v5NN.rb", the plugin sent grep=False.
GET http://127.0.0.1/student/EQp6IMrI.php returned HTTP code "403" - id: 10
No grep for: "http://127.0.0.1/student/EQp6IMrI.php", the plugin sent grep=False.
GET http://127.0.0.1/student/JDu6xd51.cgi returned HTTP code "403" - id: 11
No grep for: "http://127.0.0.1/student/JDu6xd51.cgi", the plugin sent grep=False.
GET http://127.0.0.1/student/xbnERvIu.jsp returned HTTP code "403" - id: 12
No grep for: "http://127.0.0.1/student/xbnERvIu.jsp", the plugin sent grep=False.
GET http://127.0.0.1/student/8mlVHdU5.aspx returned HTTP code "403" - id: 13
No grep for: "http://127.0.0.1/student/8mlVHdU5.aspx", the plugin sent grep=False.
GET http://127.0.0.1/student/3dEV8D7t.pl returned HTTP code "403" - id: 15
GET http://127.0.0.1/student/OUUivLqI.xhtml returned HTTP code "403" - id: 14
No grep for: "http://127.0.0.1/student/OUUivLqI.xhtml", the plugin sent grep=False.
No grep for: "http://127.0.0.1/student/3dEV8D7t.pl", the plugin sent grep=False.
The 404 body result database has a length of 1.
"http://127.0.0.1/student/" (id:1) is a 404 [similarity_index > 0.9]
Called _discover_worker()
Starting plugin: webSpider
webSpider plugin is testing: http://127.0.0.1/student/
GET http://127.0.0.1/student/ returned HTTP code "403" - id: 16
[thread manager] Successfully added function to threadpool. Work queue size: 1
[thread manager] Successfully added function to threadpool. Work queue size: 2
GET http://127.0.0.1/student/ returned HTTP code "403" - id: 17
"http://127.0.0.1/student/" (id:17) is a 404 [similarity_index > 0.9]
GET http://127.0.0.1/ returned HTTP code "403" - id: 18
"http://127.0.0.1/" (id:18) is a 404 [similarity_index > 0.9]
The following is a list of broken links that were found by the webSpider plugin:
- http://127.0.0.1/ [ referenced from: http://127.0.0.1/student/ ]
- http://127.0.0.1/student/ [ referenced from: http://127.0.0.1/student/ ]
Called _bruteforce()
Found 1 URLs and 1 different points of injection.
The list of URLs is:- http://127.0.0.1/student/
The list of fuzzable requests is:- http://127.0.0.1/student/ | Method: GET
Called _audit()
Starting plugin: sqli
SQLi plugin is testing: http://127.0.0.1/student/
GET http://127.0.0.1/student/ returned HTTP code "403" - id: 19
Fuzzing query string
Starting plugin: xss
XSS plugin is testing: http://127.0.0.1/student/
Fuzzing query string
GET http://127.0.0.1/student/ returned HTTP code "403" - id: 20
Cleared urllib2 local cache.
Calling join on all daemon threads
Exiting setOutputPlugins()
Scan finished in 0 seconds.
w3af>>>
`
ModSecurity 模块开启后:
Exiting setOutputPlugins()
Called w3afCore.start()
Enabling _dnsCache()
Called buildOpeners
keepalive: added one connection, len(self._hostmap["127.0.0.1"]): 1
DNS response from DNS server for domain: 127.0.0.1
GET http://127.0.0.1/student/ returned HTTP code "403" - id: 1
[thread manager] Successfully added function to threadpool. Work queue size: 1
[thread manager] Successfully added function to threadpool. Work queue size: 2
[thread manager] Successfully added function to threadpool. Work queue size: 3
[thread manager] Successfully added function to threadpool. Work queue size: 4
[thread manager] Successfully added function to threadpool. Work queue size: 5
[thread manager] Successfully added function to threadpool. Work queue size: 6
[thread manager] Successfully added function to threadpool. Work queue size: 7
[thread manager] Successfully added function to threadpool. Work queue size: 8
[thread manager] Successfully added function to threadpool. Work queue size: 9
[thread manager] Successfully added function to threadpool. Work queue size: 10
[thread manager] Successfully added function to threadpool. Work queue size: 11
[thread manager] Successfully added function to threadpool. Work queue size: 12
[thread manager] Successfully added function to threadpool. Work queue size: 13
[thread manager] Successfully added function to threadpool. Work queue size: 14
keepalive: added one connection, len(self._hostmap["127.0.0.1"]): 2
Cached DNS response for domain: 127.0.0.1
keepalive: added one connection, len(self._hostmap["127.0.0.1"]): 3
keepalive: added one connection, len(self._hostmap["127.0.0.1"]): 4
Cached DNS response for domain: 127.0.0.1
Cached DNS response for domain: 127.0.0.1
GET http://127.0.0.1/student/Vg1vHrJO. returned HTTP code "403" - id: 2
No grep for: "http://127.0.0.1/student/Vg1vHrJO.", the plugin sent grep=False.
GET http://127.0.0.1/student/a2O3LyYI.do returned HTTP code "403" - id: 4
GET http://127.0.0.1/student/0eLnOV3J.asp returned HTTP code "403" - id: 3
No grep for: "http://127.0.0.1/student/a2O3LyYI.do", the plugin sent grep=False.
No grep for: "http://127.0.0.1/student/0eLnOV3J.asp", the plugin sent grep=False.
GET http://127.0.0.1/student/mAGEns7z.py returned HTTP code "403" - id: 6
No grep for: "http://127.0.0.1/student/mAGEns7z.py", the plugin sent grep=False.
GET http://127.0.0.1/student/khbMvzIG.htmls returned HTTP code "403" - id: 8
No grep for: "http://127.0.0.1/student/khbMvzIG.htmls", the plugin sent grep=False.
GET http://127.0.0.1/student/qMyT7lZ5.jsp returned HTTP code "403" - id: 9
GET http://127.0.0.1/student/SU7LbF3J.htm returned HTTP code "403" - id: 5
No grep for: "http://127.0.0.1/student/SU7LbF3J.htm", the plugin sent grep=False.
No grep for: "http://127.0.0.1/student/qMyT7lZ5.jsp", the plugin sent grep=False.
GET http://127.0.0.1/student/iJRJULzR.gif returned HTTP code "403" - id: 7
No grep for: "http://127.0.0.1/student/iJRJULzR.gif", the plugin sent grep=False.
GET http://127.0.0.1/student/jTrkFnpt.xhtml returned HTTP code "403" - id: 14
No grep for: "http://127.0.0.1/student/jTrkFnpt.xhtml", the plugin sent grep=False.
GET http://127.0.0.1/student/H0xoFI0S.cgi returned HTTP code "403" - id: 11
No grep for: "http://127.0.0.1/student/H0xoFI0S.cgi", the plugin sent grep=False.
GET http://127.0.0.1/student/lwzkMqkS.php returned HTTP code "403" - id: 13
No grep for: "http://127.0.0.1/student/lwzkMqkS.php", the plugin sent grep=False.
GET http://127.0.0.1/student/gW3XjZz8.rb returned HTTP code "403" - id: 10
No grep for: "http://127.0.0.1/student/gW3XjZz8.rb", the plugin sent grep=False.
GET http://127.0.0.1/student/zQ2qJZkl.aspx returned HTTP code "403" - id: 12
No grep for: "http://127.0.0.1/student/zQ2qJZkl.aspx", the plugin sent grep=False.
GET http://127.0.0.1/student/JAdleo2T.pl returned HTTP code "403" - id: 15
No grep for: "http://127.0.0.1/student/JAdleo2T.pl", the plugin sent grep=False.
The 404 body result database has a length of 1.
"http://127.0.0.1/student/" (id:1) is a 404 [similarity_index > 0.9]
Called _discover_worker()
Starting plugin: webSpider
webSpider plugin is testing: http://127.0.0.1/student/
GET http://127.0.0.1/student/ returned HTTP code "403" - id: 16
[thread manager] Successfully added function to threadpool. Work queue size: 1
[thread manager] Successfully added function to threadpool. Work queue size: 2
GET http://127.0.0.1/student/ returned HTTP code "403" - id: 17
"http://127.0.0.1/student/" (id:17) is a 404 [similarity_index > 0.9]
GET http://127.0.0.1/ returned HTTP code "403" - id: 18
"http://127.0.0.1/" (id:18) is a 404 [similarity_index > 0.9]
The following is a list of broken links that were found by the webSpider plugin:
- http://127.0.0.1/ [ referenced from: http://127.0.0.1/student/ ]
- http://127.0.0.1/student/ [ referenced from: http://127.0.0.1/student/ ]
Called _bruteforce()
Found 1 URLs and 1 different points of injection.
The list of URLs is:- http://127.0.0.1/student/
The list of fuzzable requests is:- http://127.0.0.1/student/ | Method: GET
Called _audit()
Starting plugin: sqli
SQLi plugin is testing: http://127.0.0.1/student/
GET http://127.0.0.1/student/ returned HTTP code "403" - id: 19
Fuzzing query string
Starting plugin: xss
XSS plugin is testing: http://127.0.0.1/student/
Fuzzing query string
GET http://127.0.0.1/student/ returned HTTP code "403" - id: 20
Cleared urllib2 local cache.
Calling join on all daemon threads
Exiting setOutputPlugins()
Scan finished in 0 seconds.
对比两次 SQL 注入的返回数据可观察出:
1.在关闭 ModSecurity 模块的情况下:HTTP 请求返回的都是 returned HTTP code "200"
2.在开启 ModSecurity 模块的情况下:HTTP 请求返回的都是 returned HTTP code "403"
ModSecurity有效的阻止了 SQL 注入