0x00 开始
最近爬个站的数据,然后想扫一下其他网站的同一个账号名能否找到泄露的密码,然后在这个站嘿嘿一下...
在 sec-wiki 找到了这个密码泄露查询网站。
随便用了一下,发现网站虽然讲密码打码了,但是某些数据还是可以猜出来原始的内容,或者通过简单的计算拿到原始的内容。
but,我不能一个个输入然后看吧,数据虽然少,也有上千条啊,怎么说也是个python程序员,怎么也得鼓捣一下。
分析一下hxsec的查询接口,用python批量一下。
0x01 分析接口
hxsec查询界面如下:
其实接口很简单,f12,切换到network栏,然后随便输入什么,点击试试吧皆可以。
看到访问的网络接口如下:
Request URL:http://cha.hxsec.com/ajax.php?act=select
Request Method:POST
Status Code:200 OK
select_act:3
match_act:2
key:ll111
table:212300_cxhr_zhaopin_com
参数都特别简单,select_act表示User and Email/User/Emial,match_act表示模糊/精确查询,key就是输入的关键字。最后一个table比较重要了,表示在什么库中查询,扫描时看到进度变化,在什么库中进行了多少了,每次搜索都会在这所有库中搜索,直到结束。
这个数据应该存在了本地,或者初始化时服务器返回了。暂时不管,后面继续重点分析(有意思的就在这)。
请求返回数据,有下面几种情况:
没有返回空内容
//该库只有一条数据
addRow("ll111","[email protected]","202**962AC59075B964B07152D234B70","212300_cxhr_zhaopin_com");
//该库有多少数据
addRow("'fish13', '[email protected]', '**', 'mail_qq_sohu");addRow("fish13', '[email protected]', '**', 'mail_qq_sohu");addRow("fish13', '[email protected]', '**', 'mail_qq_sohu'], ['fish13', '', '176**1176671', 'qq_old_password'
0x02 分析table
其实接口很清楚了,但是还需要直到所有table的内容,然后才能完成所有数据搜索。
所以,table怎么找,在哪里呢!
还是要分析代码了...
看看表单所在位置代码,找找搜索按钮的响应函数(这里也可以看到上面说的参数的详情),很明显响应函数是getdata。
在html,js中一番搜索,tmd居然没有。
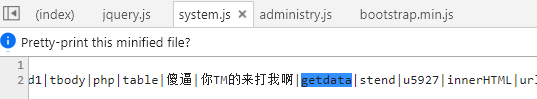
只在system.js中看到了这个!
傻逼|你TM的来打我啊|getdata|stend|u5927|
—-手工分割线——-
TMD的,我这暴脾气,这是挑衅啊,lz非搞你不可了!这已经上升到人身攻击了!!!
----手工分割线-------
很明显,tmd代码混淆了。怎么办,调试跟呗。
把system.js(用chrome格式化一下,不然...瞎眼)扒出来一看,其实也不复杂。
//jb 5/24修改
eval(function(p, a, c, k, e, d) {
e = function(c) {
return (c < a ? "" : e(parseInt(c / a))) + ((c = c % a) > 35 ? String.fromCharCode(c + 29) : c.toString(36))
}
;
if (!''.replace(/^/, String)) {
while (c--)
d[e(c)] = k[c] || e(c);
k = [function(e) {
return d[e]
}
];
e = function() {
return '\\w+'
}
;
c = 1;
}
;while (c--)
if (k[c])
p = p.replace(new RegExp('\\b' + e(c) + '\\b','g'), k[c]);
return p;
}('3o 2Y$=["",\'\',\'\\\\w+\',\'\\\\b\',\'\\\\b\',\'g\',\'d c$=["1W","#n","1T","1R","#n","\\\\2h\\\\2g\\\\k\\\\p"," \\\\2i\\\\2k\\\\1N","%","H","H","#n","\\\\k\\\\p\\\\T\\\\O!\\\\1q\\\\1t\\\\1j\\\\1k\\\\1g\\\\G\\\\D\\\\E\\\\U\\\\W \\\\z\\\\A: ","\\\\C\\\\B","#n","\\\\k\\\\p\\\\T\\\\O! \\\\U\\\\W\\\\1v:","\\\\1u \\\\z\\\\A:","\\\\C\\\\B","#n","\\\\k\\\\p\\\\T\\\\O! \\\\U\\\\W\\\\1v:","\\\\1u \\\\z\\\\A:","\\\\C\\\\B",\\\'2j\\\',"1D","1p=","&1o=","&I=","&2c=",\\\'1O.2b?2d=2f\\\',"#H","1T","1R","#I",\\\'\\\',"#I","\\\\Z\\\\2e\\\\2l\\\\k\\\\p\\\\1r\\\\1n/\\\\G\\\\D\\\\E/\\\\2s\\\\2r","\\\\G\\\\D\\\\E\\\\2t\\\\1N\\\\Z\\\\2v\\\\2u!!","#1p","#1o","1C","\\\\1q\\\\1t\\\\2n\\\\1g\\\\2m\\\\1j\\\\1k\\\\2o\\\\1r\\\\1n\\\\2q","2p|2a~!1X~!1Z|a|1Y|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b"];d o;d N;e 1D(1y,1U,1J,Y){d l=1C["2V"]();d 1A=l["q"](0);d 1I=l["q"](1);d 1V=l["q"](2);d 1M=l["q"](3);1A["w"]=1y;1I["w"]=1U;1V["w"]=1J;1M["w"]=Y};e 1x(){$( c$[0])["2U"]()};e 1Q(1l,1e,1b){$( c$[1])["1z"]( c$[2], c$[3]);d 1c=(1l/1e)*g;d M=X(1c,1);t["r"]( c$[4],M,g, c$[5]+1b+ c$[6]+M+ c$[7])};e 1L(){v=1F 1G()["1H"]()-N;d 1s=R["Q"]( c$[8]);d y=1s["P"]["f"];i(y==1){d 1i=R["Q"]( c$[9]);d 1m=1i["P"]["f"];i(1m==1){t["r"]( c$[10],g,g, c$[11]+(v)+ c$[12])}1h{t["r"]( c$[13],g,g, c$[14]+(y-1)+ c$[15]+(v)+ c$[16])}}1h{t["r"]( c$[17],g,g, c$[18]+(y-1)+ c$[19]+(v)+ c$[20])}};e X(1a,1d){d F=1f["2T"](10,1d);S 1f["2X"](1a*F)/F};e 1S(1P,s,1K,2W){$["1O"]({2D: c$[21],2C:1P,2E:s,2G:e(J){i(J["2F"]( c$[22])>=0){2B(J)};i(1K==V["f"]){1L()}}})};e 1E(j,u,x,m,h){1Q(h+1,m["f"],m[h]);d s= c$[23]+u+ c$[24]+x+ c$[25]+j+ c$[26]+m[h];1S( c$[27],s,o+1,m["f"]);o=o+1};e 2x(){$( c$[28])["1z"]( c$[29], c$[2w]);1x();d j=$( c$[2y])["K"]();i(j== c$[2A]){$( c$[2z])["2H"]();L( c$[2P]);S 1w};i(j["f"]<4){L( c$[2O]);S 1w};d u=$( c$[2Q])["K"]();d x=$( c$[2S])["K"]();N=1F 1G()["1H"]();o=0;2R(d h=0;h35?3i["4Z"](3a+29):3a["55"](36))};3h(! 2Y$[1]["3k"](/^/,3i)){3m(2Z--)3f[e(2Z)]=3c[2Z]||e(2Z);3c=[3e(3l){3b 3f[3l]}];e=3e(){3b 2Y$[2]};2Z=1};3m(2Z--)3h(3c[2Z])3g=3g["3k"](3j 4Y( 2Y$[3]+e(2Z)+ 2Y$[4], 2Y$[5]),3c[2Z]);3b 3g}( 2Y$[6],4W,4X, 2Y$[7]["4V"]( 2Y$[8]),0,{}))', 62, 352, '||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||_|somd5comf78518fb1|||||||||||somd5com21a288587|return|somd5com6d38bb14b|somd5com3de2f8f6d|function|somd5comd152c7b41|somd5comf3298c8c5|if|String|new|replace|somd5com8f18e7d16|while|eval|var|u7d22|somd5com16af76eea|somd5com6cd7bc889|somd5comed2bd7eb6|css|somd5comb9e3341a3|u5bb9|match_act|somd5com4d38b6944|select_act|u5185|u6ca1|false|get_del|u91cf|u6709|u6761|ajax|somd5come0b7918e1|somd5com4823e252c|u5ea6|get_jdt|display|somd5com811fa93b4|block|ajax_post|get_data|Date|value_tables|addRow|getTime|somd5com25f9df3a7|get_okcount|somd5com6d6674984|somd5comf49be7e59|u641c|key||somd5com9a3a7ef82|u5173|somd5_table|somd5com326e7999e|u6bd5|val|alert|somd5com956a89722|u8017|u65f6|somd5comd7f929c0a|somd5comf1d14de2e|u952e|u5b57|u79d2|u6beb|rows|somd5comf46beb405|somd5com738c8372f|somd5com3b1df0e8d|somd5comdcaedb43e|else|somd5com36f2c91c7|Math|u5230|u8bf7|u5b8c|u6570|getElementById|document|decimal|somd5com5b49d9f12|database|u636e|somd5comdd52905dc|pow|u8be2|for|somd5comb39f98f6a|round|empty|insertRow|gat_kong|focus|somd5comf53e662dd|indexOf|success|insertCell|somd5comea98952b0|progress|dataxxxx|length|SOMD5|somd5comb93c3a502|100|搜MD5|split|62|184|RegExp|fromCharCode|somd5com4af3e5365|parseInt|selecting|u67e5|somd5com490d63bb2|toString|somd5comf94f3be31|data|u5728|u6b63|u8f93|select|u8fdb|u5165|u603b|POST|act|来打我啊|SOMD55|somd5comeff53bcd1|tbody|php|table|傻逼|你TM的来打我啊|getdata|stend|u5927|innerHTML|url|type|somd5combdba21b9c|Administry|u4e8e4|u7684|操你妈|u60a8|u627e|u90ae|u957f|u5462|u7bb1'.split('|'), 0, {}));
不过直接看也挺闹人的,边调试边看吧。
参数是什么?
// p是字符串
// a 是62
// c 是 352数组大小, k 是Array[352]
// e 是0 , d 是{}
e函数干嘛了?具体返回数据暂时也不同看了,调试到了自然可以dump出来
e = function(c) {
//61以内的就返回字符,0-9,a-z(11-36),A-Z(36-61)
//62以上
//c.toString(36) 36进制转为字符
return (c < a ? "" : e(parseInt(c / a))) + ((c = c % a) > 35 ? String.fromCharCode(c + 29) : c.toString(36))
}
然后就解密那一长串字符了,用的e
while (c--)
d[e(c)] = k[c] || e(c);
解出来的数据大概是这样的一个object,
5y: 'u7684'
5x: 'u4e8e4'
5w: 'Administry'
5v: 'somd5combdba21b9c'
5u: 'type'
5t: 'url'
5s: 'innerHTML'
5r: 'u5927'
5q: 'stend'
5p: 'getdata'
5o: '你TM的来打我啊'
5n: '傻逼'
5m: 'table'
5l: 'php'
5k: 'tbody'
5j: 'somd5comeff53bcd1'
然后继续解,将结果返回给eval执行
while (c--)
if (k[c])
p = p.replace(new RegExp('\\b' + e(c) + '\\b','g'), k[c]);
直接dump结果,如下
var _$ = ["", '', '\\w+', '\\b', '\\b', 'g', 'd c$=["1W","#n","1T","1R","#n","\\2h\\2g\\k\\p"," \\2i\\2k\\1N","%","H","H","#n","\\k\\p\\T\\O!\\1q\\1t\\1j\\1k\\1g\\G\\D\\E\\U\\W \\z\\A: ","\\C\\B","#n","\\k\\p\\T\\O! \\U\\W\\1v:","\\1u \\z\\A:","\\C\\B","#n","\\k\\p\\T\\O! \\U\\W\\1v:","\\1u \\z\\A:","\\C\\B",\'2j\',"1D","1p=","&1o=","&I=","&2c=",\'1O.2b?2d=2f\',"#H","1T","1R","#I",\'\',"#I","\\Z\\2e\\2l\\k\\p\\1r\\1n/\\G\\D\\E/\\2s\\2r","\\G\\D\\E\\2t\\1N\\Z\\2v\\2u!!","#1p","#1o","1C","\\1q\\1t\\2n\\1g\\2m\\1j\\1k\\2o\\1r\\1n\\2q","2p|2a~!1X~!1Z|a|1Y|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b|a|b"];d o;d N;e 1D(1y,1U,1J,Y){d l=1C["2V"]();d 1A=l["q"](0);d 1I=l["q"](1);d 1V=l["q"](2);d 1M=l["q"](3);1A["w"]=1y;1I["w"]=1U;1V["w"]=1J;1M["w"]=Y};e 1x(){$( c$[0])["2U"]()};e 1Q(1l,1e,1b){$( c$[1])["1z"]( c$[2], c$[3]);d 1c=(1l/1e)*g;d M=X(1c,1);t["r"]( c$[4],M,g, c$[5]+1b+ c$[6]+M+ c$[7])};e 1L(){v=1F 1G()["1H"]()-N;d 1s=R["Q"]( c$[8]);d y=1s["P"]["f"];i(y==1){d 1i=R["Q"]( c$[9]);d 1m=1i["P"]["f"];i(1m==1){t["r"]( c$[10],g,g, c$[11]+(v)+ c$[12])}1h{t["r"]( c$[13],g,g, c$[14]+(y-1)+ c$[15]+(v)+ c$[16])}}1h{t["r"]( c$[17],g,g, c$[18]+(y-1)+ c$[19]+(v)+ c$[20])}};e X(1a,1d){d F=1f["2T"](10,1d);S 1f["2X"](1a*F)/F};e 1S(1P,s,1K,2W){$["1O"]({2D: c$[21],2C:1P,2E:s,2G:e(J){i(J["2F"]( c$[22])>=0){2B(J)};i(1K==V["f"]){1L()}}})};e 1E(j,u,x,m,h){1Q(h+1,m["f"],m[h]);d s= c$[23]+u+ c$[24]+x+ c$[25]+j+ c$[26]+m[h];1S( c$[27],s,o+1,m["f"]);o=o+1};e 2x(){$( c$[28])["1z"]( c$[29], c$[2w]);1x();d j=$( c$[2y])["K"]();i(j== c$[2A]){$( c$[2z])["2H"]();L( c$[2P]);S 1w};i(j["f"]<4){L( c$[2O]);S 1w};d u=$( c$[2Q])["K"]();d x=$( c$[2S])["K"]();N=1F 1G()["1H"]();o=0;2R(d h=0;h 35 ? String["fromCharCode"](somd5com21a288587 + 29) : somd5com21a288587["toString"](36))
}
;
if (!_$[1]["replace"](/^/, String)) {
while (somd5comf78518fb1--)
somd5comd152c7b41[e(somd5comf78518fb1)] = somd5com6d38bb14b[somd5comf78518fb1] || e(somd5comf78518fb1);
somd5com6d38bb14b = [function(somd5com8f18e7d16) {
return somd5comd152c7b41[somd5com8f18e7d16]
}
];
e = function() {
return _$[2]
}
;
somd5comf78518fb1 = 1
}
;while (somd5comf78518fb1--)
if (somd5com6d38bb14b[somd5comf78518fb1])
somd5comf3298c8c5 = somd5comf3298c8c5["replace"](new RegExp(_$[3] + e(somd5comf78518fb1) + _$[4],_$[5]), somd5com6d38bb14b[somd5comf78518fb1]);
return somd5comf3298c8c5
}(_$[6], 62, 184, _$[7]["split"](_$[8]), 0, {}))
有没有感觉很熟悉的结果,就是上面解密的哪个函数,参数变量真tmd
好看。不详细说了,跟前一次一样,最后返回一个解密的js代码,给eval执行。
这次dump出来看到了要的东西了!注释都有了,就不说了
function getdata() {
$(_$[28])["css"](_$[29], _$[30]);
get_del();
var somd5com490d63bb2 = $(_$[31])["val"]();//输入
if (somd5com490d63bb2 == _$[32]) {
$(_$[33])["focus"]();
alert(_$[34]);
return false
}
;if (somd5com490d63bb2["length"] < 4) {
alert(_$[35]); //"关键字长度请大于4!!"
return false
}
;var somd5combdba21b9c = $(_$[36])["val"](); //选择的搜索类型,1,2,3
var somd5comd7f929c0a = $(_$[37])["val"](); //匹配类型,1模糊,2精确
somd5com326e7999e = new Date()["getTime"](); //时间戳
somd5comdd52905dc = 0;
for (var somd5comb93c3a502 = 0; somd5comb93c3a502 < database["length"]; somd5comb93c3a502++) {
get_data(somd5com490d63bb2, somd5combdba21b9c, somd5comd7f929c0a, database, somd5comb93c3a502)
}
}
诶,忘了一件事,我们是找table的,在哪里呢?!
其实就是上面代码中的database了,这里循环每个table通过get_data(内部ajax访问)来搜索结果。
for (var somd5comb93c3a502 = 0; somd5comb93c3a502 < database["length"]; somd5comb93c3a502++) {
get_data(somd5com490d63bb2, somd5combdba21b9c, somd5comd7f929c0a, database, somd5comb93c3a502)
}
在dump出来的js代码中一搜,database没有找到定义,我靠!什么情况!调试到getdata时,确实是有值的,dump内容如下:
["06_cn_mumayi_jd_com","1010wan_beihaiw_duowan","12306_cn","131_xiu_tianya",
"17173_com","212300_cxhr_zhaopin_com","212300_cxhr_zhaopin_copy","24buy_cd","51cto_com_new",
...] //一部分
但是我能就这么算了吗?!database究竟哪里来的,真想只有一个,去html再看一眼,搜到如下内容,嗯,看来是了,服务器返回的database。
访问http://cha.hxsec.com/ajax.php?act=database,拿到返回的结果
var database = new Array("06_cn_mumayi_jd_com","1010wan_beihaiw_duowan","12306_cn","131_xiu_tianya","17173_com","212300_cxhr_zhaopin_com","212300_cxhr_zhaopin_copy","24buy_cd","51cto_com_new","51job_com","52pk_com","55_la","766_tuan800_wanmei_37","7k7k_com","admin5_apphan_07073_soyun","aipai_com","all_hack_website","av_creditcard_com_cn","ccidnet_lashou_com","cnnb_mop_qinbao_jiapin_qd315","cnzz_com","co188_com","csdn_net","damai_cn","dangdang_com","dodonew_com","gfan_com","hiapk_com","houdao_com","ipart_cn","jxjatv_073yx_moko_treo8_paojiao","jxrsrc_zhenai","kaixin001_com-ispeak_com","mail_126_com","mail_163_com","mail_qq_sina","mail_qq_sohu","pconline_com_cn","pingan_com","qiannao_dedecms_baofeng","qq_old_password","radius-qingdaonews_com","renren_com","seowhy_shooter-tatazu_book118_cs","sorry_unknown","sorry_unknown2","tgbus_com","tpy100_com-jia_com","uuu9_com","weibo_com","xda_comicdd_game","xiaohua_other","xiaomi_com");
也知道前面的database变量怎么来的了,为了database有效,ajax.php?act=database是在system.js加载完之后发送的请求。
0x03 总结
ok,分析告一段落,table拿到了,接口所有信息都弄清楚了,下面就是开始码代码了!
另外,我只想对写system.js的同志说,nmmmp!那一段中文啥用没有,只能激起fn!
有不敬之处,敬请见谅!
有一点小小的分析技巧:
.......
//想看这的请移步博客原文,自己想法看这个内容。嘎嘎,没找到请留言
封装了一套py的代码,有需要的请说!
https://github.com/anhkgg/hxsec_search
转载请注明出处,博客原文:https://anhkgg.github.io/hxsec-search-pwd-interface-analyze