扫描与抓包分析
扫描与抓包分析
问题
本案例要求熟悉Linux主机环境下的常用安全工具,完成以下任务操作:
1)使用NMAP扫描来获取指定主机/网段的相关信息
2)使用EtterCAP截获明文通信的密码、检测非加密通信的脆弱性
3)使用Tcpdump分析FTP访问中的明文交换信息
方案
使用两台RHEL6虚拟机,其中svr5作为扫描、嗅探、抓包的操作用机,而mail作为测试用的靶机;另外准备一台Windows客户机pc120,也可以作为靶机,如图所示。
步骤
实现此案例需要按照如下步骤进行。
步骤一:使用NMAP扫描来获取指定主机/网段的相关信息
1)检查目标主机mail所开启的TCP服务
[root@svr5 ~]# nmap 192.168.4.100
Starting Nmap 5.51 ( http://nmap.org ) at 2015-05-17 17:55 CST
Nmap scan report for 192.168.4.100
Host is up (0.00028s latency).
Not shown: 990 closed ports
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
25/tcp open smtp
80/tcp open http
110/tcp open pop3
111/tcp open rpcbind
143/tcp open imap
443/tcp open https
993/tcp open imaps
995/tcp open pop3s
MAC Address: 00:0C:29:74:BE:21 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 1.31 seconds
2)检查192.168.4.0/24网段内哪些主机开启了FTP、SSH服务
[root@svr5 ~]# nmap -p 21-22 192.168.4.0/24
Starting Nmap 5.51 ( http://nmap.org ) at 2015-05-17 18:00 CST
Nmap scan report for 192.168.4.1
Host is up (0.000025s latency).
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
Nmap scan report for 192.168.4.5
Host is up.
PORT STATE SERVICE
21/tcp filtered ftp
22/tcp filtered ssh
Nmap scan report for 192.168.4.120
Host is up (0.00052s latency).
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
MAC Address: 00:0C:29:74:BE:21 (VMware)
Nmap scan report for pc110.tarena.com (192.168.4.110)
Host is up (0.00038s latency).
PORT STATE SERVICE
21/tcp closed ftp
22/tcp closed ssh
MAC Address: 00:50:56:C0:00:01 (VMware)
Nmap scan report for 192.168.4.120
Host is up (0.00051s latency).
PORT STATE SERVICE
21/tcp closed ftp
22/tcp closed ssh
MAC Address: 00:0C:29:DB:84:46 (VMware)
Nmap done: 256 IP addresses (5 hosts up) scanned in 4.88 seconds
3)检查192.168.4.0/24网段内哪些主机可以ping通
[root@svr5 ~]# nmap -n -sP 192.168.4.0/24
Starting Nmap 5.51 ( http://nmap.org ) at 2015-05-17 18:01 CST
Nmap scan report for 192.168.4.1
Host is up.
Nmap scan report for 192.168.4.5
Host is up.
Nmap scan report for 192.168.4.120
Host is up (0.00027s latency).
MAC Address: 00:0C:29:74:BE:21 (VMware)
Nmap scan report for 192.168.4.110
Host is up (0.00016s latency).
MAC Address: 00:50:56:C0:00:01 (VMware)
Nmap scan report for 192.168.4.120
Host is up (0.00046s latency).
MAC Address: 00:0C:29:DB:84:46 (VMware)
Nmap done: 256 IP addresses (5 hosts up) scanned in 3.57 seconds
4)全面分析目标主机192.168.4.100、192.168.4.120的操作系统信息
[root@svr5 ~]# nmap -A 192.168.4.100,120
Starting Nmap 5.51 ( http://nmap.org ) at 2015-05-17 18:03 CST
Nmap scan report for 192.168.4.100 //主机mail的扫描报告
Host is up (0.0016s latency).
Not shown: 990 closed ports
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 2.2.2
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| -rw-r--r-- 1 0 0 1719 Aug 17 13:33 UserB.pub
| -rw-r--r-- 1 0 0 122 Aug 13 05:27 dl.txt
| drwxr-xr-x 2 14 0 4096 Aug 13 09:07 pub
| -rw-rw-r-- 1 505 505 170 Aug 17 13:18 tools-1.2.3.tar.gz
|_-rw-rw-r-- 1 505 505 287 Aug 17 13:22 tools-1.2.3.tar.gz.sig
22/tcp open ssh OpenSSH 5.3 (protocol 2.0)
| ssh-hostkey: 1024 86:be:d6:89:c1:2d:d9:1f:57:2f:66:d1:af:a8:d3:c6 (DSA)
|_2048 16:0a:15:01:fa:bb:91:1d:cc:ab:68:17:58:f9:49:4f (RSA)
25/tcp open smtp Postfix smtpd
80/tcp open http Apache httpd 2.2.15 ((Red Hat))
|_http-methods: No Allow or Public header in OPTIONS response (status code 302)
| http-title: 302 Found
|_Did not follow redirect to https://192.168.4.100//
110/tcp open pop3 Dovecot pop3d
|_pop3-capabilities: USER CAPA UIDL TOP OK(K) RESP-CODES PIPELINING STLS SASL(PLAIN)
111/tcp open rpcbind
143/tcp open imap Dovecot imapd
|_imap-capabilities: LOGIN-REFERRALS STARTTLS IMAP4rev1 ENABLE AUTH=PLAIN LITERAL+ IDLE SASL-IR ID
443/tcp open ssl/http Apache httpd 2.2.15 ((Red Hat))
| http-methods: Potentially risky methods: TRACE
|_See http://nmap.org/nsedoc/scripts/http-methods.html
|_http-title: Site doesn't have a title (text/html; charset=UTF-8).
993/tcp open ssl/imap Dovecot imapd
|_imap-capabilities: IMAP4rev1 AUTH=PLAIN ENABLE ID LITERAL+ IDLE SASL-IR LOGIN-REFERRALS
995/tcp open ssl/pop3 Dovecot pop3d
|_pop3-capabilities: OK(K) CAPA RESP-CODES UIDL PIPELINING USER TOP SASL(PLAIN)
MAC Address: 00:0C:29:74:BE:21 (VMware)
No exact OS matches for host (If you know what OS is running on it, see http://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=5.51%D=8/19%OT=21%CT=1%CU=34804%PV=Y%DS=1%DC=D%G=Y%M=000C29%TM=52
OS:11ED90%P=x86_64-redhat-linux-gnu)SEQ(SP=106%GCD=1%ISR=10B%TI=Z%CI=Z%II=I
OS:%TS=A)OPS(O1=M5B4ST11NW6%O2=M5B4ST11NW6%O3=M5B4NNT11NW6%O4=M5B4ST11NW6%O
OS:5=M5B4ST11NW6%O6=M5B4ST11)WIN(W1=3890%W2=3890%W3=3890%W4=3890%W5=3890%W6
OS:=3890)ECN(R=Y%DF=Y%T=40%W=3908%O=M5B4NNSNW6%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O
OS:%A=S+%F=AS%RD=0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=
OS:0%Q=)T5(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%
OS:S=A%A=Z%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(
OS:R=Y%DF=N%T=40%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=
OS:N%T=40%CD=S)
Network Distance: 1 hop
Service Info: Host: mail.tarena.com; OS: Unix
TRACEROUTE
HOP RTT ADDRESS
1 1.55 ms 192.168.4.100
Nmap scan report for 192.168.4.120 //主机pc120的扫描报告
Host is up (0.00047s latency).
Not shown: 997 closed ports
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn
445/tcp open microsoft-ds Microsoft Windows XP microsoft-ds
MAC Address: 00:0C:29:DB:84:46 (VMware)
Device type: general purpose
Running: Microsoft Windows XP
OS details: Microsoft Windows XP SP2 - SP3
Network Distance: 1 hop
Service Info: OS: Windows
Host script results:
|_nbstat: NetBIOS name: PC-201307130328, NetBIOS user: , NetBIOS MAC: 00:0c:29:db:84:46 (VMware)
|_smbv2-enabled: Server doesn't support SMBv2 protocol
| smb-os-discovery:
| OS: Windows XP (Windows 2000 LAN Manager)
| Name: WORKGROUP\PC-201307130328
|_ System time: 2015-05-17 18:04:40 UTC+8
TRACEROUTE
HOP RTT ADDRESS
1 0.47 ms 192.168.4.120
OS and Service detection performed. Please report any incorrect results at http://nmap.org/submit/ .
Nmap done: 2 IP addresses (2 hosts up) scanned in 43.01 seconds
步骤二:使用EtterCAP截获明文通信的密码,检测非加密通信的脆弱性
1)安装EtterCAP嗅探工具
下载(或老师提供)软件包ettercap、依赖包libnet,执行rpm安装。
[root@svr5 ~]# cd /var/ftp/pub
[root@svr5 ~]# rpm -ivh libnet-1.1.5-1.el6.x86_64.rpm\
> ettercap-0.7.5-3.el6.1.20120906gitc796e5.x86_64.rpm
warning: libnet-1.1.5-1.el6.x86_64.rpm: Header V3 RSA/SHA256 Signature, key ID 0608b895: NOKEY
Preparing... ########################################### [100%]
1:libnet ########################################### [ 50%]
2:ettercap ########################################### [100%]
2)EtterCAP工具的命令行模式
执行ettercap命令,嗅探主机192.168.4.120与主机192.168.4.100的FTP服务(21端口)之间的数据通信,收集用户名、密码信息。
[root@svr5 ~]# ettercap -Tzq /192.168.4.100//21 /192.168.4.120//
ettercap 0.7.5 copyright 2001-2012 Ettercap Development Team
Listening on:
eth0 -> 00:0C:29:AA:77:15
192.168.4.5/255.255.255.0
fe80::20c:29ff:feaa:7715/64
SSL dissection needs a valid 'redir_command_on' script in the etter.conf file
Privileges dropped to UID 65534 GID 65534...
plugin ec_sslstrip.so cannot be loaded...
30 plugins
40 protocol dissectors
55 ports monitored
13861 mac vendor fingerprint
1766 tcp OS fingerprint
2183 known services
Starting Unified sniffing... //进入标准监听状态
Text only Interface activated...
Hit 'h' for inline help
处于监听状态以后,从测试机pc120访问主机mail的vsftpd服务,如图所示。
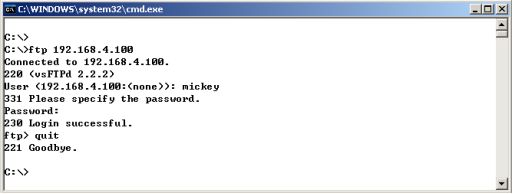
然后查看执行中的ettercap命令行界面,将会发现收集到的用户名、密码信息。
… …
Text only Interface activated...
Hit 'h' for inline help
FTP : 192.168.4.120:21 -> USER: mickey PASS: pwd123
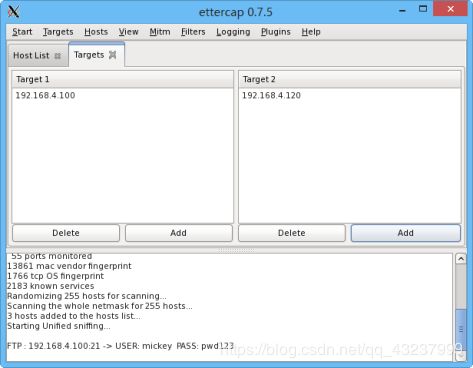
3)EtterCAP工具的图形模式
在GNOME桌面环境下, 执行ettercap -G即可打开窗口程序。选择菜单“Sniffer”–>“Unified Sniffer”监听,指定网卡eth0;然后添加两个主机192.168.4.100、192.168.4.120作为嗅探目标(Targets),选择“Start”–>“Sniffing“即可进入监听状态。
参考前面的测试操作,再次从客户机pc120访问主机mail的vsftpd服务。然后查看执行中的ettercap监听窗口程序,同样可以收集到用户名、密码信息,如图所示。
步骤三:使用Tcpdump分析FTP访问中的明文交换信息
1)启用tcpdump命令行抓包
执行tcpdump命令行,添加适当的过滤条件,只抓取访问主机192.168.4.100的21端口的数据通信 ,并转换为ASCII码格式的易读文本。
[root@svr5 ~]# tcpdump -A host 192.168.4.100 and tcp port 21
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on eth0, link-type EN10MB (Ethernet), capture size 65535 bytes
.. .. //进入等待捕获数据包的状态
2)执行FTP访问,并观察tcpdump抓包结果
参考前面的测试操作,再次从客户机pc120访问主机mail的vsftpd服务。然后查看执行中tcpdump程序的输出,仔细分析FTP连接的建立过程、确认收集到的用户名和口令信息。
.. ..
18:47:25.964110 IP 192.168.4.120.novation > 192.168.4.100.ftp: Flags [S], seq 1201822818, win 65535, options [mss 1460,nop,wscale 0,nop,nop,sackOK], length 0
E..4..@[email protected].*..G.\b........;...............
18:47:25.964268 IP 192.168.4.100.ftp > 192.168.4.120.novation: Flags [S.], seq 2284929633, ack 1201822819, win 14600, options [mss 1460,nop,nop,sackOK,nop,wscale 6], length 0
E..4..@[email protected]...*.1BaG.\c..9.7...............
18:47:25.964436 IP 192.168.4.120.novation > 192.168.4.100.ftp: Flags [.], ack 1, win 65535, length 0
E..(..@.@.. ...x...d.*..G.\c.1BbP.............
18:47:25.967592 IP 192.168.4.100.ftp > 192.168.4.120.novation: Flags [P.], seq 1:21, ack 1, win 229, length 20
E.. 192.168.4.100.ftp: Flags [.], ack 21, win 65515, length 0
E..(..@[email protected].*..G.\c.1BvP.............
18:47:27.960530 IP 192.168.4.120.novation > 192.168.4.100.ftp: Flags [P.], seq 1:14, ack 21, win 65515, length 13
E..5..@[email protected].*..G.\c.1BvP.......USER mickey
18:47:27.960544 IP 192.168.4.100.ftp > 192.168.4.120.novation: Flags [.], ack 14, win 229, length 0
E..(FK@[email protected]...*.1BvG.\pP.............
18:47:27.960783 IP 192.168.4.100.ftp > 192.168.4.120.novation: Flags [P.], seq 21:55, ack 14, win 229, length 34
E..JFL@[email protected]...*.1BvG.\pP...i~..331 Please specify the password.
18:47:28.085168 IP 192.168.4.120.novation > 192.168.4.100.ftp: Flags [.], ack 55, win 65481, length 0
E..(..@[email protected].*..G.\p.1B.P.............
18:47:29.657364 IP 192.168.4.120.novation > 192.168.4.100.ftp: Flags [P.], seq 14:27, ack 55, win 65481, length 13
E..5..@[email protected].*..G.\p.1B.P.......PASS pwd123
18:47:29.696968 IP 192.168.4.100.ftp > 192.168.4.120.novation: Flags [.], ack 27, win 229, length 0
E..(FM@[email protected]...*.1B.G.\}P.............
18:47:29.702671 IP 192.168.4.100.ftp > 192.168.4.120.novation: Flags [P.], seq 55:78, ack 27, win 229, length 23
E..?FN@[email protected]>...d...x...*.1B.G.\}P.......230 Login successful.
18:47:29.835258 IP 192.168.4.120.novation > 192.168.4.100.ftp: Flags [.], ack 78, win 65458, length 0
E..(..@[email protected].*..G.\}.1B.P.............
18:47:31.716375 IP 192.168.4.120.novation > 192.168.4.100.ftp: Flags [P.], seq 27:33, ack 78, win 65458, length 6
E.....@[email protected].*..G.\}.1B.P... ...QUIT
18:47:31.716532 IP 192.168.4.100.ftp > 192.168.4.120.novation: Flags [.], ack 33, win 229, length 0
E..(FO@[email protected]...*.1B.G.\.P....}........
18:47:31.716634 IP 192.168.4.100.ftp > 192.168.4.120.novation: Flags [P.], seq 78:92, ack 33, win 229, length 14
E..6FP@[email protected]...*.1B.G.\.P.......221 Goodbye.
18:47:31.716677 IP 192.168.4.100.ftp > 192.168.4.120.novation: Flags [F.], seq 92, ack 33, win 229, length 0
E..(FQ@[email protected]...*.1B.G.\.P....n........
18:47:31.717053 IP 192.168.4.120.novation > 192.168.4.100.ftp: Flags [.], ack 93, win 65444, length 0
E..(..@[email protected].*..G.\..1B.P.............
18:47:31.718796 IP 192.168.4.120.novation > 192.168.4.100.ftp: Flags [F.], seq 33, ack 93, win 65444, length 0
E..(..@[email protected].*..G.\..1B.P.............
18:47:31.719097 IP 192.168.4.100.ftp > 192.168.4.120.novation: Flags [.], ack 34, win 229, length 0
E..(..@[email protected]...*.1B.G.\.P....m........
