企业网络架构规划及实施案例,很实用
介绍:
本文为企业网络架构规划、实施进行详细说明。
对企业网络中涉及到的各设备中vlan划分、无线AC初始化,AP上线以及业务下发、防火墙的安全策略、服务器服务的映射以及内网之间的互访都做了相关具体介绍以及测试结果。
以eNSP模拟器对其分享~
- 各部门、服务器、无线都独立一个网段。
- 无线网络采用旁挂直接转发模式。3. 无线网络不能访问公司内网资源、只允许上网。
设备:
外网防火墙:USG6000
核心: S5700
接入: S3700
无线控制器:AC6005
无线AP: AP6010DN-AGN
- 防火墙配置。
sysname FW_01
interface GigabitEthernet0/0/0
alias Lan
ip address 10.10.10.1 255.255.255.0
interface GigabitEthernet0/0/1
alias Wan
ip address 202.100.1.1 255.255.255.0
firewall zone trust
add interface GigabitEthernet0/0/0
firewall zone untrust
add interface GigabitEthernet0/0/1
ip route-static 0.0.0.0 0.0.0.0 202.100.1.2
ip route-static 192.168.0.0 255.255.0.0 10.10.10.254
nat-policy
rule name SourceNat
egress-interface GigabitEthernet0/0/1
action source-nat easy-ip
security-policy
rule name Trust_Untrust_Out //允许内网到外网访问的安全策略
source-zone trust
destination-zone untrust
action permit
// 默认情况下安全策略拒绝所有,可按照自己实际使用情况配置安全策略开通需要放行的流量。
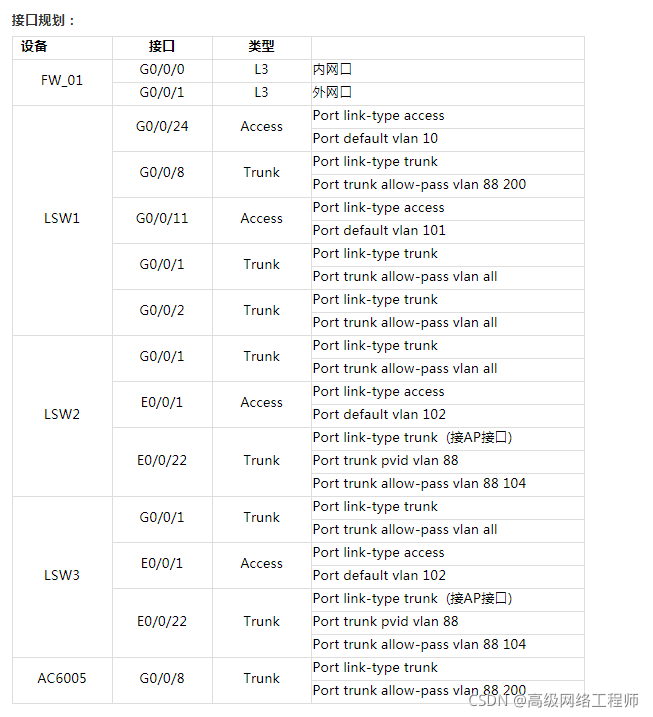
2. LSW配置。
sysname LSW1
vlan batch 10 88 101 to 104 200
dhcp enable
interface Vlanif10
ip address 10.10.10.254 255.255.255.0
interface Vlanif101
description Server
ip address 192.168.101.254 255.255.255.0
interface Vlanif102
ip address 192.168.102.254 255.255.255.0
interface Vlanif103
ip address 192.168.103.254 255.255.255.0
interface Vlanif104
description WLAN-STA
ip address 192.168.104.254 255.255.255.0
dhcp select interface
dhcp server dns-list 192.168.101.2
interface Vlanif200
description Manager
ip address 192.168.200.254 255.255.255.0
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan all
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan all
interface GigabitEthernet0/0/8
port link-type trunk
port trunk allow-pass vlan 88 200
interface GigabitEthernet0/0/11
port link-type access
port default vlan 101
interface GigabitEthernet0/0/24
port link-type access
port default vlan 10
ip route-static 0.0.0.0 0.0.0.0 10.10.10.1
- LSW2配置。
sysname LSW2
vlan batch 88 102 to 104 200
interface Vlanif200
ip address 192.168.200.2 255.255.255.0
interface Ethernet0/0/1
port link-type access
port default vlan 102
interface Ethernet0/0/22
port link-type trunk
port trunk pvid vlan 88
port trunk allow-pass vlan 88 104
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan all
ip route-static 0.0.0.0 0.0.0.0 192.168.200.254
- LSW3配置。
sysname LSW3
vlan batch 88 102 to 104 200
interface Vlanif200
ip address 192.168.200.3 255.255.255.0
interface Ethernet0/0/1
port link-type access
port default vlan 103
interface Ethernet0/0/22
port link-type trunk
port trunk pvid vlan 88
port trunk allow-pass vlan 88 104
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan all
ip route-static 0.0.0.0 0.0.0.0 192.168.200.254
- AC6005配置
Vlan 88为无线AP管理网段、配置DHCP为AP分配地址。
sysname AC6005
vlan batch 88200
dhcp enable
interface Vlanif88
ip address 192.168.88.6 255.255.255.0
dhcp select interface
interface Vlanif200
ip address 192.168.200.6 255.255.255.0
interface GigabitEthernet0/0/8
port link-type trunk
port trunk allow-pass vlan 88 200
capwap sourceinterface vlanif88
wlan
ap-auth-mode no-auth
ssid-profile name HUAWEI
ssidHUAWEI
vap-profile name HUAWEI
ssid HUAWEI
service-vlan 104
等待AP上线注册到无线控制后;AP上线后默认归属于AP组default中,将VAP配置绑定在AP组default中2.4G和5G射频下。
ap-group name default
radio 0
vap-profile HUAWEI wlan 1
radio 1
vap-profile HUAWEI wlan 1

6. 内网服务器映射到外网、供互联网用户访问。(80端口正常需要运营商备案开通)
nat server httpprotocol tcp global 202.100.1.1 80 inside 192.168.101.2 80 no-reverse
需要在防火墙上配置安全策略,允许外网访问内网服务器。
security-policy
rule name NAT_http
source-zone untrust
destination-zone trust
destination-address 192.168.101.2 mask 255.255.255.255
service http
action permit
测试用户从外网访问企业内部服务器对外提供的服务。
 8. 各部门之间访问做限制、无线接入用户无法访问销售部门、技术部门和服务器。
8. 各部门之间访问做限制、无线接入用户无法访问销售部门、技术部门和服务器。
该访问限制配置在核心交换机上:
(ACL中前3条禁止访问企业内部资源,最后rule1000允许访问其它,比如上网)
acl number 3000
rule 10 deny ip source 192.168.104.00.0.0.255 destination 192.168.101.0 0.0.0.255
rule 20 deny ip source 192.168.104.00.0.0.255 destination 192.168.102.0 0.0.0.255
rule 30 deny ip source 192.168.104.00.0.0.255 destination 192.168.103.0 0.0.0.255
rule 1000 permit ip
trafficclassifier tc1
if-match acl 3000
traffic behaviortb1
permit
traffic policy tp1
classifier tc1 behavior tb1
vlan 104
traffic-policy tp1 inbound
配置策略后测试: