使用kubeadm部署Kubernetes 1.27
kubeadm是Kubernetes官方提供的用于快速安部署Kubernetes集群的工具。伴随Kubernetes每个版本的发布,kubeadm可能会对集群配置方面的一些实践做调整,通过实验kubeadm可以学习到Kubernetes官方在集群配置上一些新的最佳实践。
1.准备
1.1 系统配置
在安装之前,需要先做好如下准备。
3台Ubuntu 22.04主机如下:
1cat /etc/hosts
2192.168.96.151 node1
3192.168.96.152 node2
4192.168.96.153 node3
在各个主机上完成下面的系统配置。
如果各个主机启用了防火墙策略,需要开放Kubernetes各个组件所需要的端口,可以查看Ports and Protocols中的内容, 开放相关端口或者关闭主机的防火墙。
创建/etc/modules-load.d/containerd.conf配置文件,确保在系统启动时自动加载所需的内核模块,以满足容器运行时的要求:
1cat << EOF > /etc/modules-load.d/containerd.conf
2overlay
3br_netfilter
4EOF
执行以下命令使配置生效:
1modprobe overlay
2modprobe br_netfilter
创建/etc/sysctl.d/99-kubernetes-cri.conf配置文件:
1cat << EOF > /etc/sysctl.d/99-kubernetes-cri.conf
2net.bridge.bridge-nf-call-ip6tables = 1
3net.bridge.bridge-nf-call-iptables = 1
4net.ipv4.ip_forward = 1
5user.max_user_namespaces=28633
6EOF
执行以下命令使配置生效:
1sysctl -p /etc/sysctl.d/99-kubernetes-cri.conf
在文件名
/etc/sysctl.d/99-kubernetes-cri.conf中,“99” 代表文件的优先级或顺序。sysctl是Linux内核参数的配置工具,它可以通过修改/proc/sys/目录下的文件来设置内核参数。在/etc/sysctl.d/目录中,可以放置一系列的配置文件,以便在系统启动时自动加载这些参数。这些配置文件按照文件名的字母顺序逐个加载。数字前缀用于指定加载的顺序,较小的数字表示较高的优先级。
1.2 配置服务器支持开启ipvs的前提条件
由于ipvs已经加入到了内核的主干,所以为kube-proxy开启ipvs的前提需要加载以下的内核模块:
1ip_vs
2ip_vs_rr
3ip_vs_wrr
4ip_vs_sh
5nf_conntrack_ipv4
创建/etc/modules-load.d/ipvs.conf文件,保证在节点重启后能自动加载所需模块:
1cat > /etc/modules-load.d/ipvs.conf <执行以下命令使配置立即生效:
1modprobe ip_vs
2modprobe ip_vs_rr
3modprobe ip_vs_wrr
4modprobe ip_vs_sh
使用lsmod | grep -e ip_vs -e nf_conntrack命令查看是否已经正确加载所需的内核模块。
接下来还需要确保各个节点上已经安装了ipset软件包,为了便于查看ipvs的代理规则,最好安装一下管理工具ipvsadm。
1apt install -y ipset ipvsadm
如果不满足以上前提条件,则即使kube-proxy的配置开启了ipvs模式,也会退回到iptables模式。
1.3 部署容器运行时Containerd
在各个服务器节点上安装容器运行时Containerd。
下载Containerd的二进制包, 需要注意cri-containerd-(cni-)-VERSION-OS-ARCH.tar.gz发行包自containerd 1.6版本起已经被弃用,在某些 Linux 发行版上无法正常工作,并将在containerd 2.0版本中移除,这里下载containerd-的发行包,后边在单独下载安装runc和CNI plugins:
1wget https://github.com/containerd/containerd/releases/download/v1.7.2/containerd-1.7.2-linux-amd64.tar.gz
将其解压缩到/usr/local下:
1tar Cxzvf /usr/local containerd-1.7.2-linux-amd64.tar.gz
2
3bin/
4bin/containerd-shim-runc-v1
5bin/containerd-shim-runc-v2
6bin/containerd-stress
7bin/containerd
8bin/containerd-shim
9bin/ctr
接下来从runc的github上单独下载安装runc,该二进制文件是静态构建的,并且应该适用于任何Linux发行版。
1wget https://github.com/opencontainers/runc/releases/download/v1.1.7/runc.amd64
2install -m 755 runc.amd64 /usr/local/sbin/runc
接下来生成containerd的配置文件:
1mkdir -p /etc/containerd
2containerd config default > /etc/containerd/config.toml
根据文档Container runtimes中的内容,对于使用systemd作为init system的Linux的发行版,使用systemd作为容器的cgroup driver可以确保服务器节点在资源紧张的情况更加稳定,因此这里配置各个节点上containerd的cgroup driver为systemd。
修改前面生成的配置文件/etc/containerd/config.toml:
1[plugins."io.containerd.grpc.v1.cri".containerd.runtimes.runc]
2 ...
3 [plugins."io.containerd.grpc.v1.cri".containerd.runtimes.runc.options]
4 SystemdCgroup = true
再修改/etc/containerd/config.toml中的
1[plugins."io.containerd.grpc.v1.cri"]
2 ...
3 # sandbox_image = "registry.k8s.io/pause:3.8"
4 sandbox_image = "registry.aliyuncs.com/google_containers/pause:3.9"
为了通过systemd启动containerd,请还需要从https://raw.githubusercontent.com/containerd/containerd/main/containerd.service下载containerd.service单元文件,并将其放置在 /etc/systemd/system/containerd.service中。 配置containerd开机启动,并启动containerd,执行以下命令:
1systemctl daemon-reload
2systemctl enable containerd --now
下载安装crictl工具:
1wget https://github.com/kubernetes-sigs/cri-tools/releases/download/v1.27.0/crictl-v1.27.0-linux-amd64.tar.gz
2tar -zxvf crictl-v1.27.0-linux-amd64.tar.gz
3install -m 755 crictl /usr/local/bin/crictl
使用crictl测试一下,确保可以打印出版本信息并且没有错误信息输出:
1crictl --runtime-endpoint=unix:///run/containerd/containerd.sock version
2
3Version: 0.1.0
4RuntimeName: containerd
5RuntimeVersion: v1.7.2
6RuntimeApiVersion: v1
2.使用kubeadm部署Kubernetes
2.1 安装kubeadm和kubelet
下面在各节点安装kubeadm和kubelet:
1apt-get update
2apt-get install -y apt-transport-https ca-certificates curl
3
4curl -s https://mirrors.aliyun.com/kubernetes/apt/doc/apt-key.gpg | sudo apt-key add -
5
6
7tee /etc/apt/sources.list.d/kubernetes.list <<-'EOF'
8deb https://mirrors.aliyun.com/kubernetes/apt/ kubernetes-xenial main
9EOF
10
11apt-get update
12
13apt install kubelet kubeadm kubectl
14
15apt-mark hold kubelet kubeadm kubectl
上面的命令在安装kubeadm, kubectl, kubelet 时,会自动安装依赖项conntrack, cri-tools, ebtables, kubernetes-cni, soca
运行kubelet --help可以看到原来kubelet的绝大多数命令行flag参数都被DEPRECATED了,官方推荐我们使用--config指定配置文件,并在配置文件中指定原来这些flag所配置的内容。具体内容可以查看这里Set Kubelet parameters via a config file。最初Kubernetes这么做是为了支持动态Kubelet配置(Dynamic Kubelet Configuration),但动态Kubelet配置特性从k8s 1.22中已弃用,并在1.24中被移除。如果需要调整集群汇总所有节点kubelet的配置,还是推荐使用ansible等工具将配置分发到各个节点。
kubelet的配置文件必须是json或yaml格式,具体可查看这里。
Kubernetes 1.8开始要求关闭系统的Swap,如果不关闭,默认配置下kubelet将无法启动。 关闭系统的Swap方法如下:
1swapoff -a
修改/etc/fstab文件,注释掉 SWAP 的自动挂载,使用free -m确认swap已经关闭。
swappiness参数调整,修改/etc/sysctl.d/99-kubernetes-cri.conf添加下面一行:
1vm.swappiness=0
执行sysctl -p /etc/sysctl.d/99-kubernetes-cri.conf使修改生效。
2.2 使用kubeadm init初始化集群
在各节点开机启动kubelet服务:
1systemctl enable kubelet.service
使用kubeadm config print init-defaults --component-configs KubeletConfiguration可以打印集群初始化默认的使用的配置:
1apiVersion: kubeadm.k8s.io/v1beta3
2bootstrapTokens:
3- groups:
4 - system:bootstrappers:kubeadm:default-node-token
5 token: abcdef.0123456789abcdef
6 ttl: 24h0m0s
7 usages:
8 - signing
9 - authentication
10kind: InitConfiguration
11localAPIEndpoint:
12 advertiseAddress: 1.2.3.4
13 bindPort: 6443
14nodeRegistration:
15 criSocket: unix:///var/run/containerd/containerd.sock
16 imagePullPolicy: IfNotPresent
17 name: node
18 taints: null
19---
20apiServer:
21 timeoutForControlPlane: 4m0s
22apiVersion: kubeadm.k8s.io/v1beta3
23certificatesDir: /etc/kubernetes/pki
24clusterName: kubernetes
25controllerManager: {}
26dns: {}
27etcd:
28 local:
29 dataDir: /var/lib/etcd
30imageRepository: registry.k8s.io
31kind: ClusterConfiguration
32kubernetesVersion: 1.27.0
33networking:
34 dnsDomain: cluster.local
35 serviceSubnet: 10.96.0.0/12
36scheduler: {}
37---
38apiVersion: kubelet.config.k8s.io/v1beta1
39authentication:
40 anonymous:
41 enabled: false
42 webhook:
43 cacheTTL: 0s
44 enabled: true
45 x509:
46 clientCAFile: /etc/kubernetes/pki/ca.crt
47authorization:
48 mode: Webhook
49 webhook:
50 cacheAuthorizedTTL: 0s
51 cacheUnauthorizedTTL: 0s
52cgroupDriver: systemd
53clusterDNS:
54- 10.96.0.10
55clusterDomain: cluster.local
56containerRuntimeEndpoint: ""
57cpuManagerReconcilePeriod: 0s
58evictionPressureTransitionPeriod: 0s
59fileCheckFrequency: 0s
60healthzBindAddress: 127.0.0.1
61healthzPort: 10248
62httpCheckFrequency: 0s
63imageMinimumGCAge: 0s
64kind: KubeletConfiguration
65logging:
66 flushFrequency: 0
67 options:
68 json:
69 infoBufferSize: "0"
70 verbosity: 0
71memorySwap: {}
72nodeStatusReportFrequency: 0s
73nodeStatusUpdateFrequency: 0s
74resolvConf: /run/systemd/resolve/resolv.conf
75rotateCertificates: true
76runtimeRequestTimeout: 0s
77shutdownGracePeriod: 0s
78shutdownGracePeriodCriticalPods: 0s
79staticPodPath: /etc/kubernetes/manifests
80streamingConnectionIdleTimeout: 0s
81syncFrequency: 0s
82volumeStatsAggPeriod: 0s
从默认的配置中可以看到,可以使用imageRepository定制在集群初始化时拉取k8s所需镜像的地址。基于默认配置定制出本次使用kubeadm初始化集群所需的配置文件kubeadm.yaml:
1apiVersion: kubeadm.k8s.io/v1beta3
2kind: InitConfiguration
3localAPIEndpoint:
4 advertiseAddress: 192.168.96.151
5 bindPort: 6443
6nodeRegistration:
7 criSocket: unix:///run/containerd/containerd.sock
8 taints:
9 - effect: PreferNoSchedule
10 key: node-role.kubernetes.io/master
11---
12apiVersion: kubeadm.k8s.io/v1beta3
13kind: ClusterConfiguration
14kubernetesVersion: 1.27.2
15imageRepository: registry.aliyuncs.com/google_containers
16networking:
17 podSubnet: 10.244.0.0/16
18---
19apiVersion: kubelet.config.k8s.io/v1beta1
20kind: KubeletConfiguration
21cgroupDriver: systemd
22failSwapOn: false
23---
24apiVersion: kubeproxy.config.k8s.io/v1alpha1
25kind: KubeProxyConfiguration
26mode: ipvs
这里定制了imageRepository为阿里云的registry,避免因gcr被墙,无法直接拉取镜像。criSocket设置了容器运行时为containerd。 同时设置kubelet的cgroupDriver为systemd,设置kube-proxy代理模式为ipvs。
在开始初始化集群之前可以使用kubeadm config images pull --config kubeadm.yaml预先在各个服务器节点上拉取所k8s需要的容器镜像。
1kubeadm config images pull --config kubeadm.yaml
2W0605 14:18:31.911654 46106 images.go:80] could not find officially supported version of etcd for Kubernetes v1.27.2, falling back to the nearest etcd version (3.5.7-0)
3[config/images] Pulled registry.aliyuncs.com/google_containers/kube-apiserver:v1.27.2
4[config/images] Pulled registry.aliyuncs.com/google_containers/kube-controller-manager:v1.27.2
5[config/images] Pulled registry.aliyuncs.com/google_containers/kube-scheduler:v1.27.2
6[config/images] Pulled registry.aliyuncs.com/google_containers/kube-proxy:v1.27.2
7[config/images] Pulled registry.aliyuncs.com/google_containers/pause:3.9
8[config/images] Pulled registry.aliyuncs.com/google_containers/etcd:3.5.7-0
9[config/images] Pulled registry.aliyuncs.com/google_containers/coredns:v1.10.1
注意,在pull镜像时报了一个警告,could not find officially supported version of etcd,这是因为当前阿里云镜像仓库中没有对应的etcd版本,自动回退到了3.5.7,这里测试kubeadm的工作影响不大。
接下来使用kubeadm初始化集群,选择node1作为Master Node,在node1上执行下面的命令:
1kubeadm init --config kubeadm.yaml
2
3[init] Using Kubernetes version: v1.27.2
4[preflight] Running pre-flight checks
5 [WARNING Swap]: swap is enabled; production deployments should disable swap unless testing the NodeSwap feature gate of the kubelet
6[preflight] Pulling images required for setting up a Kubernetes cluster
7[preflight] This might take a minute or two, depending on the speed of your internet connection
8[preflight] You can also perform this action in beforehand using 'kubeadm config images pull'
9W0605 14:22:31.238068 46342 images.go:80] could not find officially supported version of etcd for Kubernetes v1.27.2, falling back to the nearest etcd version (3.5.7-0)
10[certs] Using certificateDir folder "/etc/kubernetes/pki"
11[certs] Generating "ca" certificate and key
12[certs] Generating "apiserver" certificate and key
13[certs] apiserver serving cert is signed for DNS names [kubernetes kubernetes.default kubernetes.default.svc kubernetes.default.svc.cluster.local node1] and IPs [10.96.0.1 192.168.96.151]
14[certs] Generating "apiserver-kubelet-client" certificate and key
15[certs] Generating "front-proxy-ca" certificate and key
16[certs] Generating "front-proxy-client" certificate and key
17[certs] Generating "etcd/ca" certificate and key
18[certs] Generating "etcd/server" certificate and key
19[certs] etcd/server serving cert is signed for DNS names [localhost node1] and IPs [192.168.96.151 127.0.0.1 ::1]
20[certs] Generating "etcd/peer" certificate and key
21[certs] etcd/peer serving cert is signed for DNS names [localhost node1] and IPs [192.168.96.151 127.0.0.1 ::1]
22[certs] Generating "etcd/healthcheck-client" certificate and key
23[certs] Generating "apiserver-etcd-client" certificate and key
24[certs] Generating "sa" key and public key
25[kubeconfig] Using kubeconfig folder "/etc/kubernetes"
26[kubeconfig] Writing "admin.conf" kubeconfig file
27[kubeconfig] Writing "kubelet.conf" kubeconfig file
28[kubeconfig] Writing "controller-manager.conf" kubeconfig file
29[kubeconfig] Writing "scheduler.conf" kubeconfig file
30[kubelet-start] Writing kubelet environment file with flags to file "/var/lib/kubelet/kubeadm-flags.env"
31[kubelet-start] Writing kubelet configuration to file "/var/lib/kubelet/config.yaml"
32[kubelet-start] Starting the kubelet
33[control-plane] Using manifest folder "/etc/kubernetes/manifests"
34[control-plane] Creating static Pod manifest for "kube-apiserver"
35[control-plane] Creating static Pod manifest for "kube-controller-manager"
36[control-plane] Creating static Pod manifest for "kube-scheduler"
37[etcd] Creating static Pod manifest for local etcd in "/etc/kubernetes/manifests"
38W0605 14:22:40.007760 46342 images.go:80] could not find officially supported version of etcd for Kubernetes v1.27.2, falling back to the nearest etcd version (3.5.7-0)
39[wait-control-plane] Waiting for the kubelet to boot up the control plane as static Pods from directory "/etc/kubernetes/manifests". This can take up to 4m0s
40[apiclient] All control plane components are healthy after 29.005604 seconds
41[upload-config] Storing the configuration used in ConfigMap "kubeadm-config" in the "kube-system" Namespace
42[kubelet] Creating a ConfigMap "kubelet-config" in namespace kube-system with the configuration for the kubelets in the cluster
43[upload-certs] Skipping phase. Please see --upload-certs
44[mark-control-plane] Marking the node node1 as control-plane by adding the labels: [node-role.kubernetes.io/control-plane node.kubernetes.io/exclude-from-external-load-balancers]
45[mark-control-plane] Marking the node node1 as control-plane by adding the taints [node-role.kubernetes.io/master:PreferNoSchedule]
46[bootstrap-token] Using token: ytoxup.raf7bk63jpbm88ne
47[bootstrap-token] Configuring bootstrap tokens, cluster-info ConfigMap, RBAC Roles
48[bootstrap-token] Configured RBAC rules to allow Node Bootstrap tokens to get nodes
49[bootstrap-token] Configured RBAC rules to allow Node Bootstrap tokens to post CSRs in order for nodes to get long term certificate credentials
50[bootstrap-token] Configured RBAC rules to allow the csrapprover controller automatically approve CSRs from a Node Bootstrap Token
51[bootstrap-token] Configured RBAC rules to allow certificate rotation for all node client certificates in the cluster
52[bootstrap-token] Creating the "cluster-info" ConfigMap in the "kube-public" namespace
53[kubelet-finalize] Updating "/etc/kubernetes/kubelet.conf" to point to a rotatable kubelet client certificate and key
54[addons] Applied essential addon: CoreDNS
55[addons] Applied essential addon: kube-proxy
56
57Your Kubernetes control-plane has initialized successfully!
58
59To start using your cluster, you need to run the following as a regular user:
60
61 mkdir -p $HOME/.kube
62 sudo cp -i /etc/kubernetes/admin.conf $HOME/.kube/config
63 sudo chown $(id -u):$(id -g) $HOME/.kube/config
64
65Alternatively, if you are the root user, you can run:
66
67 export KUBECONFIG=/etc/kubernetes/admin.conf
68
69You should now deploy a pod network to the cluster.
70Run "kubectl apply -f [podnetwork].yaml" with one of the options listed at:
71 https://kubernetes.io/docs/concepts/cluster-administration/addons/
72
73Then you can join any number of worker nodes by running the following on each as root:
74
75kubeadm join 192.168.96.151:6443 --token ytoxup.raf7bk63jpbm88ne \
76 --discovery-token-ca-cert-hash sha256:14da9f26f8eb63bbb727030e57829f4b1b06fb9099cb43b5b59784d2c462d93c
上面记录了完成的初始化输出的内容,根据输出的内容基本上可以看出手动初始化安装一个Kubernetes集群所需要的关键步骤。 其中有以下关键内容:
[certs]生成相关的各种证书[kubeconfig]生成相关的kubeconfig文件[kubelet-start]生成kubelet的配置文件"/var/lib/kubelet/config.yaml"[control-plane]使用/etc/kubernetes/manifests目录中的yaml文件创建apiserver、controller-manager、scheduler的静态pod[bootstraptoken]生成token记录下来,后边使用kubeadm join往集群中添加节点时会用到[addons]安装基本插件:CoreDNS,kube-proxy- 下面的命令是配置常规用户如何使用kubectl访问集群:
1mkdir -p $HOME/.kube 2sudo cp -i /etc/kubernetes/admin.conf $HOME/.kube/config 3sudo chown $(id -u):$(id -g) $HOME/.kube/config - 最后给出了将另外2个节点加入集群的命令:
1kubeadm join 192.168.96.151:6443 --token ytoxup.raf7bk63jpbm88ne \
2 --discovery-token-ca-cert-hash sha256:14da9f26f8eb63bbb727030e57829f4b1b06fb9099cb43b5b59784d2c462d93c
查看一下集群状态,确认个组件都处于healthy状态,结果出现了错误:
1kubectl get cs
2
3Warning: v1 ComponentStatus is deprecated in v1.19+
4NAME STATUS MESSAGE ERROR
5controller-manager Healthy ok
6scheduler Healthy ok
7etcd-0 Healthy {"health":"true","reason":""}
集群初始化如果遇到问题,可以使用kubeadm reset命令进行清理。
2.3 安装包管理器helm 3
Helm是Kubernetes的包管理器,后续流程也将使用Helm安装Kubernetes的常用组件。 这里先在master节点node1上安装helm。
1wget https://get.helm.sh/helm-v3.12.0-linux-amd64.tar.gz
2tar -zxvf helm-v3.12.0-linux-amd64.tar.gz
3mv linux-amd64/helm /usr/local/bin/
执行helm list确认没有错误输出。
2.4 部署Pod Network组件Calico
选择calico作为k8s的Pod网络组件,下面使用helm在k8s集群中安装calico。
下载tigera-operator的helm chart:
1wget https://github.com/projectcalico/calico/releases/download/v3.26.0/tigera-operator-v3.26.0.tgz
查看这个chart的中可定制的配置:
1helm show values tigera-operator-v3.26.0.tgz
2
3imagePullSecrets: {}
4
5installation:
6 enabled: true
7 kubernetesProvider: ""
8
9apiServer:
10 enabled: true
11
12certs:
13 node:
14 key:
15 cert:
16 commonName:
17 typha:
18 key:
19 cert:
20 commonName:
21 caBundle:
22
23# Resource requests and limits for the tigera/operator pod.
24resources: {}
25
26# Tolerations for the tigera/operator pod.
27tolerations:
28- effect: NoExecute
29 operator: Exists
30- effect: NoSchedule
31 operator: Exists
32
33# NodeSelector for the tigera/operator pod.
34nodeSelector:
35 kubernetes.io/os: linux
36
37# Custom annotations for the tigera/operator pod.
38podAnnotations: {}
39
40# Custom labels for the tigera/operator pod.
41podLabels: {}
42
43# Image and registry configuration for the tigera/operator pod.
44tigeraOperator:
45 image: tigera/operator
46 version: v1.30.0
47 registry: quay.io
48calicoctl:
49 image: docker.io/calico/ctl
50 tag: v3.26.0
定制的values.yaml如下:
1# 可针对上面的配置进行定制,例如calico的镜像改成从私有库拉取。
2# 这里只是个人本地环境测试k8s新版本,因此只有下面几行配置
3apiServer:
4 enabled: false
5installation:
6 kubeletVolumePluginPath: None
使用helm安装calico:
1helm install calico tigera-operator-v3.26.0.tgz -n kube-system --create-namespace -f values.yaml
等待并确认所有pod处于Running状态:
1kubectl get pod -n kube-system | grep tigera-operator
2tigera-operator-5fb55776df-wxbph 1/1 Running 0 5m10s
3
4kubectl get pods -n calico-system
5NAME READY STATUS RESTARTS AGE
6calico-kube-controllers-68884f975d-5d7p9 1/1 Running 0 5m24s
7calico-node-twbdh 1/1 Running 0 5m24s
8calico-typha-7b4bdd99c5-ssdn2 1/1 Running 0 5m24s
查看一下calico向k8s中添加的api资源:
1kubectl api-resources | grep calico
2bgpconfigurations crd.projectcalico.org/v1 false BGPConfiguration
3bgpfilters crd.projectcalico.org/v1 false BGPFilter
4bgppeers crd.projectcalico.org/v1 false BGPPeer
5blockaffinities crd.projectcalico.org/v1 false BlockAffinity
6caliconodestatuses crd.projectcalico.org/v1 false CalicoNodeStatus
7clusterinformations crd.projectcalico.org/v1 false ClusterInformation
8felixconfigurations crd.projectcalico.org/v1 false FelixConfiguration
9globalnetworkpolicies crd.projectcalico.org/v1 false GlobalNetworkPolicy
10globalnetworksets crd.projectcalico.org/v1 false GlobalNetworkSet
11hostendpoints crd.projectcalico.org/v1 false HostEndpoint
12ipamblocks crd.projectcalico.org/v1 false IPAMBlock
13ipamconfigs crd.projectcalico.org/v1 false IPAMConfig
14ipamhandles crd.projectcalico.org/v1 false IPAMHandle
15ippools crd.projectcalico.org/v1 false IPPool
16ipreservations crd.projectcalico.org/v1 false IPReservation
17kubecontrollersconfigurations crd.projectcalico.org/v1 false KubeControllersConfiguration
18networkpolicies crd.projectcalico.org/v1 true NetworkPolicy
19networksets crd.projectcalico.org/v1 true NetworkSet
这些api资源是属于calico的,因此不建议使用kubectl来管理,推荐按照calicoctl来管理这些api资源。 将calicoctl安装为kubectl的插件:
1cd /usr/local/bin
2curl -o kubectl-calico -O -L "https://github.com/projectcalico/calicoctl/releases/download/v3.21.5/calicoctl-linux-amd64"
3chmod +x kubectl-calico
验证插件正常工作:
1kubectl calico -h
2.5 验证k8s DNS是否可用
1kubectl run curl --image=radial/busyboxplus:curl -it
2If you don't see a command prompt, try pressing enter.
3[ root@curl:/ ]$
进入后执行nslookup kubernetes.default确认解析正常:
1nslookup kubernetes.default
2Server: 10.96.0.10
3Address 1: 10.96.0.10 kube-dns.kube-system.svc.cluster.local
4
5Name: kubernetes.default
6Address 1: 10.96.0.1 kubernetes.default.svc.cluster.local
2.6 向Kubernetes集群中添加Node节点
下面将node2, node3添加到Kubernetes集群中,分别在node2, node3上执行:
1kubeadm join 192.168.96.151:6443 --token ytoxup.raf7bk63jpbm88ne \
2 --discovery-token-ca-cert-hash sha256:14da9f26f8eb63bbb727030e57829f4b1b06fb9099cb43b5b59784d2c462d93c
node2和node3加入集群很是顺利,在master节点上执行命令查看集群中的节点(需要等待新加入节点上的calico-node pod启动正常):
1kubectl get node
2NAME STATUS ROLES AGE VERSION
3node1 Ready control-plane 29m v1.27.2
4node2 Ready 31s v1.27.2
5node3 Ready 19s v1.27.2
3.Kubernetes常用组件部署
3.1 使用Helm部署ingress-nginx
为了便于将集群中的服务暴露到集群外部,需要使用Ingress。接下来使用Helm将ingress-nginx部署到Kubernetes上。 Nginx Ingress Controller被部署在Kubernetes的边缘节点上。
这里将node1(192.168.96.151)作为边缘节点,打上Label:
1kubectl label node node1 node-role.kubernetes.io/edge=
下载ingress-nginx的helm chart:
1wget https://github.com/kubernetes/ingress-nginx/releases/download/helm-chart-4.7.0/ingress-nginx-4.7.0.tgz
查看ingress-nginx-4.7.0.tgz这个chart的可定制配置:
1helm show values ingress-nginx-4.7.0.tgz
对values.yaml配置定制如下:
1controller:
2 ingressClassResource:
3 name: nginx
4 enabled: true
5 default: true
6 controllerValue: "k8s.io/ingress-nginx"
7 admissionWebhooks:
8 enabled: false
9 replicaCount: 1
10 image:
11 # registry: registry.k8s.io
12 # image: ingress-nginx/controller
13 # tag: "v1.8.0"
14 registry: docker.io
15 image: unreachableg/registry.k8s.io_ingress-nginx_controller
16 tag: "v1.8.0"
17 digest: sha256:626fc8847e967dc06049c0eda9e093d77a08feff80179ae97538ba8b118570f3
18 hostNetwork: true
19 nodeSelector:
20 node-role.kubernetes.io/edge: ''
21 affinity:
22 podAntiAffinity:
23 requiredDuringSchedulingIgnoredDuringExecution:
24 - labelSelector:
25 matchExpressions:
26 - key: app
27 operator: In
28 values:
29 - nginx-ingress
30 - key: component
31 operator: In
32 values:
33 - controller
34 topologyKey: kubernetes.io/hostname
35 tolerations:
36 - key: node-role.kubernetes.io/master
37 operator: Exists
38 effect: NoSchedule
39 - key: node-role.kubernetes.io/master
40 operator: Exists
41 effect: PreferNoSchedule
nginx ingress controller的副本数replicaCount为1,将被调度到node1这个边缘节点上。这里并没有指定nginx ingress controller service的externalIPs,而是通过hostNetwork: true设置nginx ingress controller使用宿主机网络。 因为registry.k8s.io被墙,这里替换成unreachableg/registry.k8s.io_ingress-nginx_controller提前拉取一下镜像:
1crictl --runtime-endpoint=unix:///run/containerd/containerd.sock pull unreachableg/registry.k8s.io_ingress-nginx_controller:v1.8.0
1helm install ingress-nginx ingress-nginx-4.7.0.tgz --create-namespace -n ingress-nginx -f values.yaml
1kubectl get pod -n ingress-nginx
2NAME READY STATUS RESTARTS AGE
3ingress-nginx-controller-7c96f857f-cbmhx 1/1 Running 0 39s
测试访问http://192.168.96.151返回默认的nginx 404页,则部署完成。
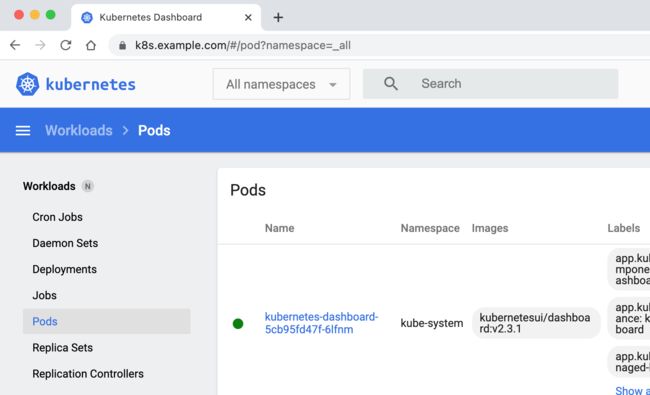
3.2 使用Helm部署dashboard
先部署metrics-server:
1wget https://github.com/kubernetes-sigs/metrics-server/releases/download/v0.6.3/components.yaml
修改components.yaml中的image为docker.io/unreachableg/k8s.gcr.io_metrics-server_metrics-server:v0.6.3。 修改components.yaml中容器的启动参数,加入--kubelet-insecure-tls。
1kubectl apply -f components.yaml
metrics-server的pod正常启动后,等一段时间就可以使用kubectl top查看集群和pod的metrics信息:
1kubectl top node
2NAME CPU(cores) CPU% MEMORY(bytes) MEMORY%
3node1 509m 12% 3654Mi 47%
4node2 133m 3% 1786Mi 23%
5node3 117m 2% 1810Mi 23%
6
7kubectl top pod -n kube-system
8NAME CPU(cores) MEMORY(bytes)
9coredns-74586cf9b6-575nl 6m 16Mi
10coredns-74586cf9b6-mbn8s 5m 17Mi
11etcd-node1 49m 91Mi
12kube-apiserver-node1 142m 490Mi
13kube-controller-manager-node1 38m 54Mi
14kube-proxy-k5lzs 26m 19Mi
15kube-proxy-rb5pf 9m 15Mi
16kube-proxy-w5zpk 27m 16Mi
17kube-scheduler-node1 7m 18Mi
18metrics-server-8dfd488f5-r8pbh 8m 21Mi
19tigera-operator-5fb55776df-wxbph 10m 38Mi
接下来使用helm部署k8s的dashboard,添加chart repo:
1helm repo add kubernetes-dashboard https://kubernetes.github.io/dashboard/
2helm repo update
查看chart的可定制配置:
1helm show values kubernetes-dashboard/kubernetes-dashboard
对values.yaml定制配置如下:
1image:
2 repository: kubernetesui/dashboard
3 tag: v2.7.0
4ingress:
5 enabled: true
6 annotations:
7 nginx.ingress.kubernetes.io/ssl-redirect: "true"
8 nginx.ingress.kubernetes.io/backend-protocol: "HTTPS"
9 hosts:
10 - k8s.example.com
11 tls:
12 - secretName: example-com-tls-secret
13 hosts:
14 - k8s.example.com
15metricsScraper:
16 enabled: true
以上配置中, 部署的dashboard将通过ingress以域名k8s.example.com暴露出来, 并为此域名开启HTTPS。
为了开启HTTPS,需要为此域名申请SSL证书或使用自签证书,这里使用的证书和私钥文件分别为example.com+5.pem和example.com+5-key.pem。
先创建存放k8s.example.comssl证书的secret:
1kubectl create secret tls example-com-tls-secret \
2 --cert=example.com+5.pem \
3 --key=example.com+5-key.pem \
4 -n kube-system
使用helm部署dashboard:
1helm install kubernetes-dashboard kubernetes-dashboard/kubernetes-dashboard \
2-n kube-system \
3-f values.yaml
确认上面的命令部署成功。
创建管理员sa:
1kubectl create serviceaccount kube-dashboard-admin-sa -n kube-system
2
3kubectl create clusterrolebinding kube-dashboard-admin-sa \
4--clusterrole=cluster-admin --serviceaccount=kube-system:kube-dashboard-admin-sa
创建集群管理员登录dashboard所需token:
1kubectl create token kube-dashboard-admin-sa -n kube-system --duration=87600h
2
3eyJhbGciOiJSUzI1NiIsImtpZCI6IlU1SlpSTS1YekNuVzE0T1k5TUdTOFFqN25URWxKckt6OUJBT0xzblBsTncifQ.eyJhdWQiOlsiaHR0cHM6Ly9rdWJlcm5ldGVzLmRlZmF1bHQuc3ZjLmNsdXN0ZXIubG9jYWwiXSwiZXhwIjoxOTY4OTA4MjgyLCJpYXQiOjE2NTM1NDgyODIsImlzcyI6Imh0dHBzOi8va3ViZXJuZXRlcy5kZWZhdWx0LnN2Yy5jbHVzdGVyLmxvY2FsIiwia3ViZXJuZXRlcy5pbyI6eyJuYW1lc3BhY2UiOiJrdWJlLXN5c3RlbSIsInNlcnZpY2VhY2NvdW50Ijp7Im5hbWUiOiJrdWJlLWRhc2hib2FyZC1hZG1pbi1zYSIsInVpZCI6IjY0MmMwMmExLWY1YzktNDFjNy04Mjc5LWQ1ZmI3MGRjYTQ3ZSJ9fSwibmJmIjoxNjUzNTQ4MjgyLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6a3ViZS1zeXN0ZW06a3ViZS1kYXNoYm9hcmQtYWRtaW4tc2EifQ.Xqxlo2vJ9Hb6UUVIqwvc8I5bahdxKzSRSaQI_67Yt7_YEHmkkHApxUGlwJYTKF9ufww3btlCmM8PtRn5_Q1yv-HAFyTOYKo8WHZ9UCm1bT3X8V8g4GQwZIl2dwmlUmKb1unBz2-em2uThQ015bMPDE8a42DV_bOwWjljVXat0nwV14nGorC8vKLjXbohrIJ3G1pgCJvlBn99F1RelmSUSQLlolUFoxpN6MamYTElwR6FfD-AGmFXvZSbcFaqVW0oxJHV70Gjs2igOtpqHFxxPlHT8aQzlRiybPtFyBf9Ll87TmVJimT89z8wv2si2Nee8bB2jhsApLn8TJyUSlbTXA
使用上面的token登录k8s dashboard。
参考
- Installing kubeadm
- Creating a cluster with kubeadm
- https://github.com/containerd/containerd/blob/main/docs/getting-started.md
- v1beta2 package - k8s.io/kubernetes/cmd/kubeadm/app/apis/kubeadm/v1beta2 - Go Packages
- Calico Documentation | Calico Documentation