第八题 WTF
给出的字符忘了截图了,是一长串base64,解码得到
通过观察发现是二维码的数字串,一共65536个字符,正好256*256.
用processing工具转换成二维码,扫码得到flag。
15 证明自己吧
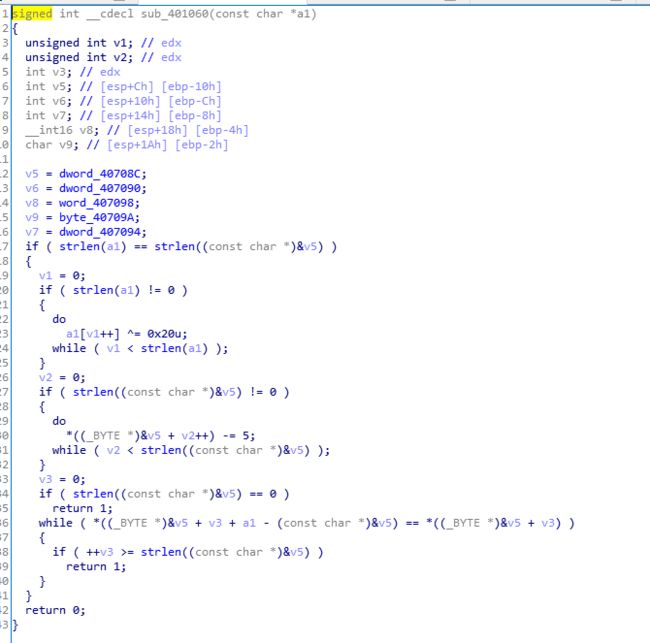
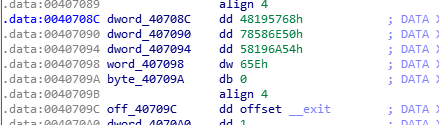
定位到关键代码,a1是程序要求输入的flag,也就是v5每个字节-5 等于 a1与上0x20的值。注意IDA里的大端和小端的问题就好了
buffer = [0x68,0x57,0x19,0x48,0x50,0x6e,0x58,0x78,0x54,0x6a,0x19,0x58,0x5e,0x6]
res = []
ls = ''
for i in buffer:
te = (i-5)^0x20
res.append(te)
ls += chr(te)
print(res)
print(ls)
百度看这是道原题,大佬们用动态调试直接就出来了
py逆向
给了个pyc文件
直接百度pyc 反编译 在线反编译一下得到源码
写个脚本就跑出来了,注意加减和位于的优先级问题就行
def encrypt(key, seed, string):
rst = []
for v in string:
rst.append((ord(v) + seed ^ ord(key[seed])) % 255)
seed = (seed + 1) % len(key)
return rst
if __name__ == '__main__':
print 'Welcome to python crackme'
flag = ''
KEY1 = 'Maybe you are good at decryptint Byte Code, have a try!'
KEY2 = [111,52,24,28,120,50,37,62,67,52,48,6,1,122,3,22,72,1,1,14,46,27,22]
en_out = encrypt(KEY1, 5, KEY2)
if KEY2 == en_out:
print 'You Win,FLAG IS flag{%s}' % flag
else:
print 'Try Again !'
------------------
seed = 5
key1 = "Maybe you are good at decryptint Byte Code, have a try!"
key2 = [111,52,24,28,120,50,37,62,67,52,48,6,1,122,3,22,72,1,1,14,46,27,22]
res = ''
n = len(key1)
l = len(key2)
print(n)
res = []
for i in range(l):
tem = ((key2[i] ^ ord(key1[seed]))-seed) % 255
res.append(tem)
seed = (seed + 1) % n
print(res)
ls = ""
for i in res :
ls += chr(i)
print(ls)
REIF
源程序找不到了,先放脚本了
v3 = [3765,3301,7803,10323,5712,3845,5218,1968,4237,1696,704,7713,4746,6517,2339,4192,354,6454,6137,5015,6396,942,2825,8129,448,1760,9863,778,6617,432]
v33 = [297,169,431,229,423,257,465,288,437,86,364,123,390,485,232,352,244,469,54,359,16,110,355,244,256,94,187,19,242,432]
v63 = [34,29,76,98,43,52,97,24,40,23,4,69,44,52,43,80,1,63,79,48,55,8,26,95,4,34,82,11,51,81]
res = []
print(len(v3),len(v33),len(v63))
for i in range(len(v3)):
tem = (v3[i] - v33[i]) / v63[i]
res.append(tem)
ls = ''
for i in res:
ls += chr(int(i))
print(res)
print(ls)
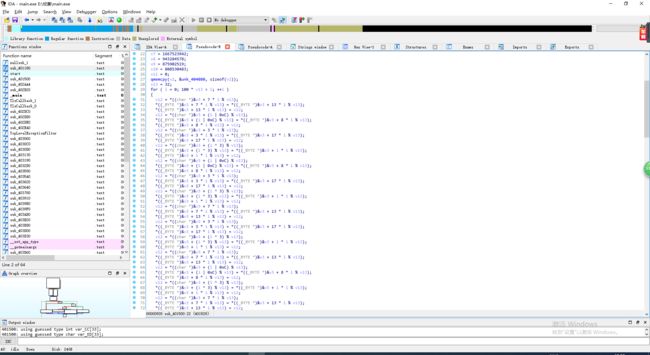
19 打个气
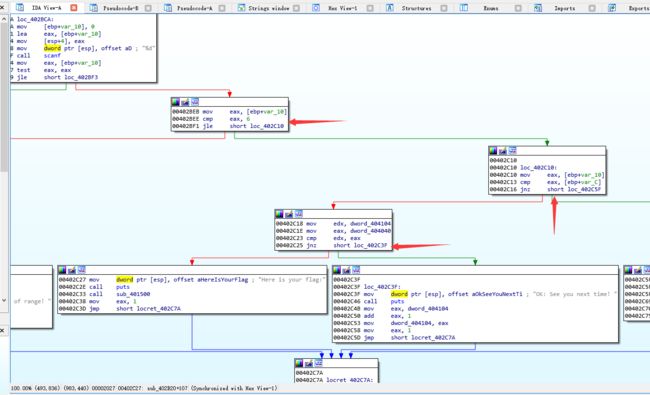
先通过找字符串定位到关键代码位置
然后发现超乎想象的复杂,改用od试一试
根据汇编代码的走向,确定下断点的位置
在相应的地方下断点,通过修改z标志位来改变跳转位置。程序就会自动跑出来flag。