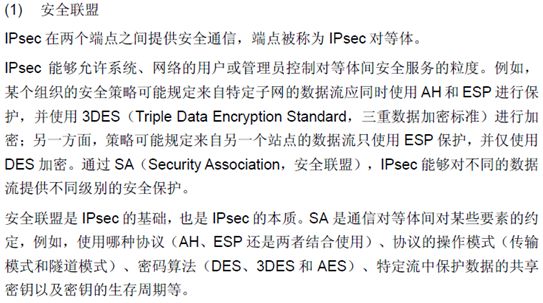
一、基本原理及相关知识的介绍!
相关知识:
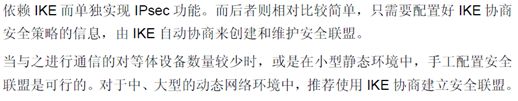
二、案例:(利用IKE动态)
1. 作业要求:
在公司与分支机构之间实现跨Internet的通信。用Ipsec 实现 *** 在总部与公司建立隧道来实现!
2. 拓扑图:
IP 地址分配情况:
R7 Loopback 1 192.168.1.1 /24
Ethernet 1 200.100.1.1 /24
S1 Ethernet 0/1 200.100.1.2/24 (中间的交换机)
Ehternet 0/2 200.100.2.1/24
Ethernet 0/3 200.100.3.1/24
F1 Ethernet 0/1 200.100.2.2/24
Ethernet 0/2 192.168.2.1 /24
F2 Ethernet 0/1 200.100.3.2/24
Ethernet 0/2 192.168.3.1 /24
3. 设备描述:
路由器: H3C Quidway R2621
交换机: H3C Quidway S3526E
防火墙: H3C SecPath F100-c
4. 配置如下:
路由器配置:
- 配ip
[Router]sysname r7
[r7]int loopback 1
[r7-LoopBack1]ip add 192.168.1.1 255.255.255.0
[r7-LoopBack1]int e1
[r7-Ethernet1]ip add 200.100.1.1 255.255.255.0
- 配默认路由:
[r7]ip route 0.0.0.0 0.0.0.0 200.100.1.2
- 配访问控制列表:
[r7]acl 3000
[r7-acl-3000]rule permit ip source 192.168.1.0 0.0.0.255 destination 192.168.2.0 0.0.0.255
[r7-acl-3000]rule deny ip source any dest any
[r7]acl 3001
[r7-acl-3001]rule permit ip source 192.168.1.0 0.0.0.255 destination 192.168.3.0 0.0.0.255
[r7-acl-3001]rule deny ip source any dest any
- 配安全提议:
[r7]ipsec proposal gjp1 名称随意
[r7-ipsec-proposal-gjp1]encapsulation tunnel
[r7-ipsec-proposal-gjp1]transform esp-new
[r7-ipsec-proposal-gjp1]esp encryp des
[r7-ipsec-proposal-gjp1]esp auth md5
[r7-ipsec-proposal-gjp1]dis ipsec propo //显示配置的提议
proposal set name: gjp1
proposal set mode: tunnel
transform: esp-new
ESP protocol: authentication md5-hmac-96, encryption-algorithm des
[r7]ipsec policy py1 10 isakmp //动态
[r7-ipsec-policy-py1-10]security acl 3000
[r7-ipsec-policy-py1-10]proposal gjp1 //安全协议采用 ESP协议
[r7-ipsec-policy-py1-10]tunnel remote 200.100.2.2 使用隧道的对端IP
[r7-ipsec-policy-py1-10]ike pre-shared-key abc remote 200.100.2.2
[r7-ipsec-policy-py1-10]quit
[r7]int e1
[r7-Ethernet1]ipsec policy py1
[r7]dis ipsec policy all
ipsec policy name: py1
ipsec policy sequence: 10
negotiation mode: isakmp
security acl: 3000
remote address 0: 200.100.2.2
Proposal name: gjp1
ipsec sa duration: 3600 seconds
ipsec sa duration: 1843200 kilobytes
OutBound SA has NOT been established.
InBound SA has NOT been established.
[r7]ipsec policy py1 11 isakmp
[r7-ipsec-policy-py1-11]sec acl 3001
[r7-ipsec-policy-py1-11]proposal gjp1
[r7-ipsec-policy-py1-11]tunnel remote 200.100.3.2
[r7]ike pre-shared-key abc remote 200.100.3.2 //钥匙双方要一致
交换机配置:
[Quidway]vlan 10 建vlan
[Quidway-vlan10]port e0/1 加接口
[Quidway-vlan10]vlan 20
[Quidway-vlan20]port e0/2
[Quidway-vlan20]vlan 30
[Quidway-vlan30]port e0/3
[Quidway-vlan30]quit
[Quidway]int vlan 10 进入接口
[Quidway-Vlan-interface10]ip add 200.100.1.2 255.255.255.0 配ip
[Quidway-Vlan-interface10]int vlan 20
[Quidway-Vlan-interface20]ip add 200.100.2.1 255.255.255.0
[Quidway-Vlan-interface20]int vlan 30
[Quidway-Vlan-interface30]ip add 200.100.3.1 255.255.255.0
第一个防火墙(f1) 配置:
- 配IP:
H3C] int eth0/1
[H3C-Ethernet0/1]ip add 200.100.2.2 255.255.255.0
[H3C-Ethernet0/1]int et0/2
[H3C-Ethernet0/2]ip add 192.168.2.1 255.255.255.0
- 添加区域:
[H3C]firewall zone untrust
[H3C-zone-untrust]add interface eth0/1
[H3C-zone-untrust]quit
[H3C]firewall zone trust
[H3C-zone-trust]add interface eth0/2
- Acl
[H3C]acl number 3000
[H3C-acl-adv-3000]rule permit ip source 192.168.2.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
[H3C-acl-adv-3000]rule deny ip source any dest any
[H3C-acl-adv-3000]QUIT
- 默认路由:
[H3C]ip route-static 0.0.0.0 0.0.0.0 200.100.2.1
创建名为gjp2的安全提议:
[H3C]ipsec proposal gjp2
[H3C-ipsec-proposal-gjp2]encapsulation-mode tunnel //报文封装形式采用隧道模式
[H3C-ipsec-proposal-gjp2]transform esp //安全协议采用 ESP协议
[H3C-ipsec-proposal-gjp2]esp encryption-algorithm des //选择算法
[H3C-ipsec-proposal-gjp2]esp authentication-algorithm md5 //选择认证
- 配IKE对等体
[H3C]ike peer r1 (名字可随意)
[H3C-ike-peer-r1]pre-shared-key abc //双方要一致
[H3C-ike-peer-r1]remote-address 200.100.1.1 //隧道对端的ip
- 创建一条安全策略,协商方式为isakmp
[H3C]ipsec policy py2 10 isakmp
[H3C-ipsec-policy-isakmp-py2-10]security acl 3000 //引用访问控制列表
[H3C-ipsec-policy-isakmp-py2-10]proposal gjp2 // 引用安全提议
[H3C-ipsec-policy-isakmp-py2-10]ike-peer r1 //引用IKE对等体
[H3C]int et0/1
[H3C-Ethernet0/1]ipsec policy py2 //应用安全策略
测试:使用一台PC
C:\Users\Administrator>ping 192.168.1.1 //公司总部的IP
正在 Ping 192.168.1.1 具有 32 字节的数据:
请求超时。
来自 192.168.1.1 的回复: 字节=32 时间=8ms TTL=254
来自 192.168.1.1 的回复: 字节=32 时间=8ms TTL=254
第二个防火墙(f2)配置:
[H3C]int eth0/1
[H3C-Ethernet0/1]ip add 200.100.3.2 24
[H3C-Ethernet0/1]int eth0/2
[H3C-Ethernet0/2]ip add 192.168.3.1 24
[H3C-Ethernet0/2]qu
[H3C]firewall zone trust
[H3C-zone-trust]add interface eth0/2
[H3C-zone-trust]qu
[H3C]firewall zone untrust
[H3C-zone-untrust]add interface eth0/1
[H3C-zone-untrust]qu
[H3C]acl number 3000
[H3C-acl-adv-3000]rule permit ip source 192.168.3.0 0.0.0.255 dest 192.168.1.0 0.0.0.255
[H3C-acl-adv-3000]rule deny ip source any dest any
[H3C-acl-adv-3000]qu
[H3C]ip route-static 0.0.0.0 0.0.0.0 200.100.3.1
(其他的参考第一个防火墙的配置)
测试:使用一台PC
C:\Users\Administrator>ping 192.168.1.1
正在 Ping 192.168.1.1 具有 32 字节的数据:
请求超时。
来自 192.168.1.1 的回复: 字节=32 时间=9ms TTL=254
来自 192.168.1.1 的回复: 字节=32 时间=7ms TTL=254
来自 192.168.1.1 的回复: 字节=32 时间=9ms TTL=254