最优非对称加密填充(OAEP)
下面是从OPENSSL上截取的rsa_oaep.c的源码:
1 #if !defined(OPENSSL_NO_SHA) && !defined(OPENSSL_NO_SHA1) 2 #include <stdio.h> 3 #include "cryptlib.h" 4 #include <openssl/bn.h> 5 #include <openssl/rsa.h> 6 #include <openssl/evp.h> 7 #include <openssl/rand.h> 8 #include <openssl/sha.h> 9 10 static int MGF1(unsigned char *mask, long len, 11 const unsigned char *seed, long seedlen); 12 13 int RSA_padding_add_PKCS1_OAEP(unsigned char *to, int tlen, 14 const unsigned char *from, int flen, 15 const unsigned char *param, int plen) 16 { 17 int i, emlen = tlen - 1; 18 unsigned char *db, *seed; 19 unsigned char *dbmask, seedmask[SHA_DIGEST_LENGTH]; 20 21 if (flen > emlen - 2 * SHA_DIGEST_LENGTH - 1) 22 { 23 RSAerr(RSA_F_RSA_PADDING_ADD_PKCS1_OAEP, 24 RSA_R_DATA_TOO_LARGE_FOR_KEY_SIZE); 25 return 0; 26 } 27 28 if (emlen < 2 * SHA_DIGEST_LENGTH + 1) 29 { 30 RSAerr(RSA_F_RSA_PADDING_ADD_PKCS1_OAEP, RSA_R_KEY_SIZE_TOO_SMALL); 31 return 0; 32 } 33 34 to[0] = 0; 35 seed = to + 1; 36 db = to + SHA_DIGEST_LENGTH + 1; 37 38 if (!EVP_Digest((void *)param, plen, db, NULL, EVP_sha1(), NULL)) 39 return 0; 40 memset(db + SHA_DIGEST_LENGTH, 0, 41 emlen - flen - 2 * SHA_DIGEST_LENGTH - 1); 42 db[emlen - flen - SHA_DIGEST_LENGTH - 1] = 0x01; 43 memcpy(db + emlen - flen - SHA_DIGEST_LENGTH, from, (unsigned int) flen); 44 if (RAND_bytes(seed, SHA_DIGEST_LENGTH) <= 0) 45 return 0; 46 #ifdef PKCS_TESTVECT 47 memcpy(seed, 48 "\xaa\xfd\x12\xf6\x59\xca\xe6\x34\x89\xb4\x79\xe5\x07\x6d\xde\xc2\xf0\x6c\xb5\x8f", 49 20); 50 #endif 51 52 dbmask = OPENSSL_malloc(emlen - SHA_DIGEST_LENGTH); 53 if (dbmask == NULL) 54 { 55 RSAerr(RSA_F_RSA_PADDING_ADD_PKCS1_OAEP, ERR_R_MALLOC_FAILURE); 56 return 0; 57 } 58 59 if (MGF1(dbmask, emlen - SHA_DIGEST_LENGTH, seed, SHA_DIGEST_LENGTH) < 0) 60 return 0; 61 for (i = 0; i < emlen - SHA_DIGEST_LENGTH; i++) 62 db[i] ^= dbmask[i]; 63 64 if (MGF1(seedmask, SHA_DIGEST_LENGTH, db, emlen - SHA_DIGEST_LENGTH) < 0) 65 return 0; 66 for (i = 0; i < SHA_DIGEST_LENGTH; i++) 67 seed[i] ^= seedmask[i]; 68 69 OPENSSL_free(dbmask); 70 return 1; 71 } 72 73 int RSA_padding_check_PKCS1_OAEP(unsigned char *to, int tlen, 74 const unsigned char *from, int flen, int num, 75 const unsigned char *param, int plen) 76 { 77 int i, dblen, mlen = -1; 78 const unsigned char *maskeddb; 79 int lzero; 80 unsigned char *db = NULL, seed[SHA_DIGEST_LENGTH], phash[SHA_DIGEST_LENGTH]; 81 unsigned char *padded_from; 82 int bad = 0; 83 84 if (--num < 2 * SHA_DIGEST_LENGTH + 1) 85 /* 'num' is the length of the modulus, i.e. does not depend on the 86 * particular ciphertext. */ 87 goto decoding_err; 88 89 lzero = num - flen; 90 if (lzero < 0) 91 { 92 /* signalling this error immediately after detection might allow 93 * for side-channel attacks (e.g. timing if 'plen' is huge 94 * -- cf. James H. Manger, "A Chosen Ciphertext Attack on RSA Optimal 95 * Asymmetric Encryption Padding (OAEP) [...]", CRYPTO 2001), 96 * so we use a 'bad' flag */ 97 bad = 1; 98 lzero = 0; 99 flen = num; /* don't overflow the memcpy to padded_from */ 100 } 101 102 dblen = num - SHA_DIGEST_LENGTH; 103 db = OPENSSL_malloc(dblen + num); 104 if (db == NULL) 105 { 106 RSAerr(RSA_F_RSA_PADDING_CHECK_PKCS1_OAEP, ERR_R_MALLOC_FAILURE); 107 return -1; 108 } 109 110 /* Always do this zero-padding copy (even when lzero == 0) 111 * to avoid leaking timing info about the value of lzero. */ 112 padded_from = db + dblen; 113 memset(padded_from, 0, lzero); 114 memcpy(padded_from + lzero, from, flen); 115 116 maskeddb = padded_from + SHA_DIGEST_LENGTH; 117 118 if (MGF1(seed, SHA_DIGEST_LENGTH, maskeddb, dblen)) 119 return -1; 120 for (i = 0; i < SHA_DIGEST_LENGTH; i++) 121 seed[i] ^= padded_from[i]; 122 123 if (MGF1(db, dblen, seed, SHA_DIGEST_LENGTH)) 124 return -1; 125 for (i = 0; i < dblen; i++) 126 db[i] ^= maskeddb[i]; 127 128 if (!EVP_Digest((void *)param, plen, phash, NULL, EVP_sha1(), NULL)) 129 return -1; 130 131 if (memcmp(db, phash, SHA_DIGEST_LENGTH) != 0 || bad) 132 goto decoding_err; 133 else 134 { 135 for (i = SHA_DIGEST_LENGTH; i < dblen; i++) 136 if (db[i] != 0x00) 137 break; 138 if (i == dblen || db[i] != 0x01) 139 goto decoding_err; 140 else 141 { 142 /* everything looks OK */ 143 144 mlen = dblen - ++i; 145 if (tlen < mlen) 146 { 147 RSAerr(RSA_F_RSA_PADDING_CHECK_PKCS1_OAEP, RSA_R_DATA_TOO_LARGE); 148 mlen = -1; 149 } 150 else 151 memcpy(to, db + i, mlen); 152 } 153 } 154 OPENSSL_free(db); 155 return mlen; 156 157 decoding_err: 158 /* to avoid chosen ciphertext attacks, the error message should not reveal 159 * which kind of decoding error happened */ 160 RSAerr(RSA_F_RSA_PADDING_CHECK_PKCS1_OAEP, RSA_R_OAEP_DECODING_ERROR); 161 if (db != NULL) OPENSSL_free(db); 162 return -1; 163 } 164 165 int PKCS1_MGF1(unsigned char *mask, long len, 166 const unsigned char *seed, long seedlen, const EVP_MD *dgst) 167 { 168 long i, outlen = 0; 169 unsigned char cnt[4]; 170 EVP_MD_CTX c; 171 unsigned char md[EVP_MAX_MD_SIZE]; 172 int mdlen; 173 int rv = -1; 174 175 EVP_MD_CTX_init(&c); 176 mdlen = EVP_MD_size(dgst); 177 if (mdlen < 0) 178 goto err; 179 for (i = 0; outlen < len; i++) 180 { 181 cnt[0] = (unsigned char)((i >> 24) & 255); 182 cnt[1] = (unsigned char)((i >> 16) & 255); 183 cnt[2] = (unsigned char)((i >> 8)) & 255; 184 cnt[3] = (unsigned char)(i & 255); 185 if (!EVP_DigestInit_ex(&c,dgst, NULL) 186 || !EVP_DigestUpdate(&c, seed, seedlen) 187 || !EVP_DigestUpdate(&c, cnt, 4)) 188 goto err; 189 if (outlen + mdlen <= len) 190 { 191 if (!EVP_DigestFinal_ex(&c, mask + outlen, NULL)) 192 goto err; 193 outlen += mdlen; 194 } 195 else 196 { 197 if (!EVP_DigestFinal_ex(&c, md, NULL)) 198 goto err; 199 memcpy(mask + outlen, md, len - outlen); 200 outlen = len; 201 } 202 } 203 rv = 0; 204 err: 205 EVP_MD_CTX_cleanup(&c); 206 return rv; 207 } 208 209 static int MGF1(unsigned char *mask, long len, const unsigned char *seed, 210 long seedlen) 211 { 212 return PKCS1_MGF1(mask, len, seed, seedlen, EVP_sha1()); 213 } 214 #endif
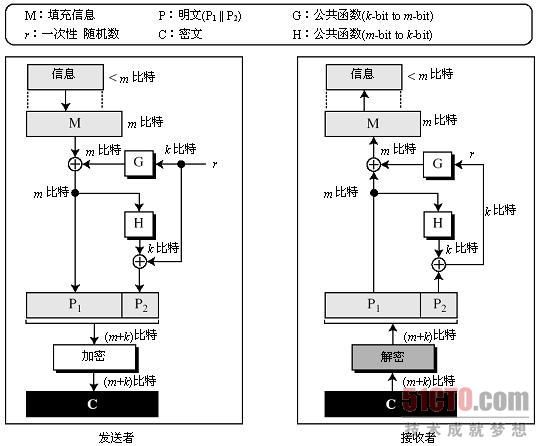
RSA中的一个短信息可以导致密文易遭受短信息攻击。也已经说明简单地给信息填充伪数据(填充位)也许就会使敌手的工作变得十分困难,但是通过更进一步的努力,她还可以对密文进行攻击。解决这种攻击的办法就是应用称为最优非对称加密填充(OAEP)的过程。下图,就是该过程的简单版本,执行时也许要用更为完善的版本。
图中的全部概念就是P = P1 || P2,这里P1就是填充信息的掩模版M;P2发送以便允许鲍勃找出掩模。
加密 下面就是加密的过程:
(1) 爱丽丝填充这个信息来制成一个m比特的信息,我们称之为M。
(2) 爱丽丝选择一个k比特的随机数r。注意r只能使用一次然后就要销毁。
(3) 爱丽丝运用一个公共单向函数G,这个单向函数用一个r比特的整数并且创建一个m比特的整数(m表示M的大小,并且r m)。这就是掩模。
(4) 爱丽丝运用掩模G(r)来创建明文![]() 的第一部分。
的第一部分。![]() 是掩模信息。
是掩模信息。
(5) 爱丽丝创建明文![]() 的第二部分。函数H是另一个公共函数,这个公共函数用一个m比特的输入创建一个k比特的输出。这个函数可以是一个加密的散列函数(参看第12章)。运用
的第二部分。函数H是另一个公共函数,这个公共函数用一个m比特的输入创建一个k比特的输出。这个函数可以是一个加密的散列函数(参看第12章)。运用![]() 以使鲍勃解密后重新创建掩模。
以使鲍勃解密后重新创建掩模。
解密 如下所示就是解密过程:
(4) 从M当中取消填充后,鲍勃得到了原信息。
1. 传输错误
即使在传输过程中有一个单比特的错误,RSA也会崩溃。如果收到的密文与所发送的不同,接收者就不能确定原明文。在接收方计算出来的明文也许和发送方发送出去的有很大的不同。传输媒介必须通过在密文上增加错误探测或错误纠正冗余比特使其没有错误。
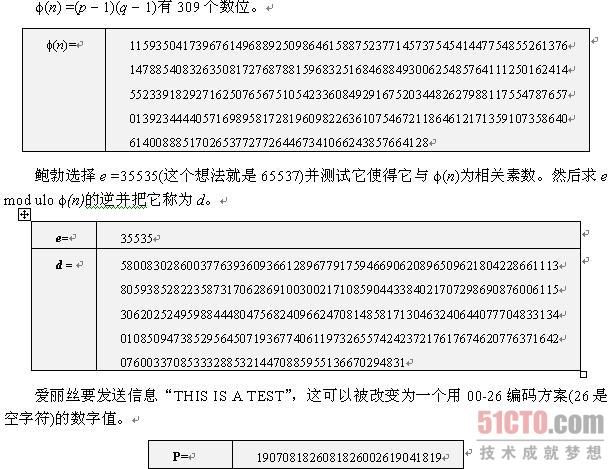
例: