PatentTips - Handling shared interrupts in bios under a virtualization technology environment
BACKGROUND
This relates to the operation of software under a virtualization technology (VT) environment.
In a VT environment, such as the Intel VT or AMD Pacifica, an infrastructure may be provided to execute applications in an isolated and protected partition, called the service partition, using the VT capability. The operating system that is visible to end users runs in another partition, called the user partition. For example, a firewall application running in service partition is forwarding the inspected/verified data packets to the user partition. A typical flow of a network packet consist of a) processing and inspection of the network packet by the firewall application in service partition, and b) subsequent forwarding of the network packet to the user partition through the inter-communication channel. The network packet eventually reaches the end-user application running in user partition (as it would happen in a non-VT environment).
In a particular VT environment, Windows CE can be used in the service partition and Windows XP in the user partition. The control flow of boot process can be summarized as follows: a) Basic input/output system passes the control to VT loader; b) VT loader loads itself and prepares the environments for the service partition and user partition for both guests Windows CE and Windows XP respectively; c) VT loader launches Windows CE in service partition, Windows CE completes its boot, and requests VT loader to launch Windows XP; d) VT loader then launches Windows XP and Windows XP starts booting.
During initial stages of a boot process, the XP operating system uses different basic input/output system services as usual. However, the XP operating system is unaware that it is running within a partition isolated and supervised by another entity. Although the control flow of the XP operating system in the VT aware environment remains identical to that of the non-VT environment, the underlying hardware environment differs as far as the device ownership is concerned.
Typically, devices are fully owned by one operating system or guest running in a particular partition (service partition or user partition), and, therefore, are isolated from one another. For example, network controllers may be owned by the Windows CE operating system running in service partition, that handles all incoming and outgoing packets, while storage devices, like hard disks, may be owned by the XP operating system running in user partition. However, some devices, like programmable interrupt controller, may be shared between the two operating systems and are thereby exposed to both guests via the underlying software models.
When an interrupt request is shared by different devices, owned by different guests, in level-triggered interrupt environments, the interrupt may be conveyed to both guests under the assumption that the service routine of both guests will be invoked; the service routine of a particular guest will check the interrupt source for the device it controls; if several devices raise a shared interrupt request simultaneously, all devices will be checked as possible interrupt sources and serviced as necessary; and if a guest detects that the interrupt source for the device it controls, it will service the interrupt or, otherwise, it will ignore the interrupt by sending an end of interrupt.
The basic input/output system (BIOS) installs a default interrupt request handler for all hardware interrupts. If no other entity installs a handler for a particular interrupt request, the basic input/output system default interrupt service routine remains as the only active interrupt handler for the concerned interrupt request. In a shared interrupt environment, when an entity installs a handler for a particular interrupt request, the concerned handler is installed in a chained fashion so that the last installed handler gets control first on the occurrence of the concerned interrupt request and the basic input/output system default interrupt service routine remains at the bottom of the interrupt handler chain. Thus, if no handler claims and services the generated interrupt request, the basic input/output system default interrupt service routine eventually gets control and finds the interrupt request that has been generated, but not claimed and, hence, not serviced by anybody, and disables the request, treating it like a spurious interrupt.
DETAILED DESCRIPTION
Some virtualization technology (VT) capabilities may expect that an interrupt request will be ignored if no owner is found, while the basic input/output system (BIOS) expects that the interrupt request will be disabled if no owner is found. The conflicting requirements regarding the handling of a shared interrupt request gives rise to a situation where the interrupt request may be disabled by the basic input/output system default interrupt service routine if no owner claims it. For example, where an interrupt request is shared by a network controller and a hard disk controller, if the interrupt is generated by the network controller in the virtualized environment when one operating system Windows XP is booting up in the user partition, the interrupt is injected into both operating system guests.
In an environment where one operating system Windows XP is booting in the user partition, the interrupt handlers that are installed by the basic input/output system (or other entities) is invoked. However, the installed interrupt handlers for the hard disk may not service the interrupt because it is not generated by a hard disk operation, but, instead, is generated by a network operation. Even though the other operating system guest Windows CE running in service partition installs a network driver and processes the interrupt as expected, no entity may install the interrupt handler for the network controller during the boot process of the operating system in the user partition. Hence, the basic input/output system default interrupt service routine is invoked as the last entry in the chained interrupt handlers, disabling the interrupt request which may subsequently result in an error while accessing the hard disk and possibly in the failure to boot the system.
This situation may be overcome by installing on demand a custom interrupt service routine. The BIOS may be requested to install the custom interrupt handler as required, allowing the basic input/output system default interrupt service routine to remain unchanged, while allowing installation of a custom interrupt service routine for a particular interrupt request as needed.
Thus, a custom interrupt service routine may be active only for a concerned shared interrupt request between two guests and existing basic input/output system default interrupt service routines will be active for all other interrupt requests. In a non-VT environment, the existing basic input/output system default interrupt service routine remains active for all interrupts as usual. This allows development of a single basic input/output system that works in both VT and non-VT environments, while maintaining the compatibility with all existing environments.
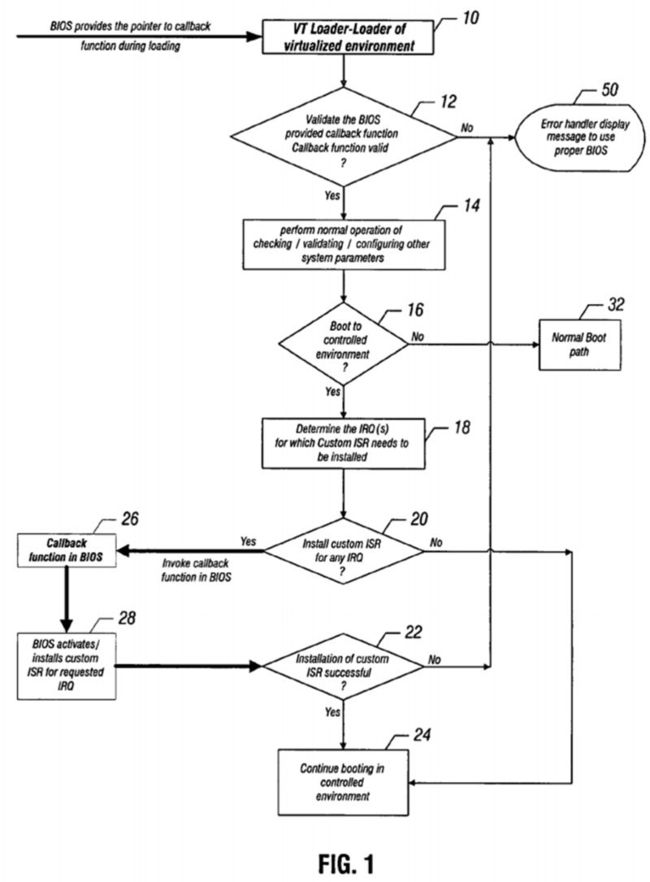
The invocation of a callback method by VT loader is illustrated in FIG. 1. The callback function 26 may be implemented in the basic input/output system in one embodiment. The basic input/output system may also implement the custom interrupt service routine that does not disable the interrupt request if no owner is found, but just issues an end of interrupt and keep the custom interrupt service routine inactive and make it active only when asked by the caller (e.g. VT loader). The basic input/output system may provide the pointer to the callback function when the basic input/output system passes the control to the VT loader (loader of VT environment), as indicated by the arrow adjacent to block 10 in FIG. 1.
Then in diamond 12, the loader validates the basic input/output system provided callback function. If the function is not valid, an error message may be displayed, as indicated at 50. Otherwise, the loader performs the normal operation of checking and validating and configuring other system parameters as indicated in block 14.
A check at diamond 16 determines whether the boot is to a controlled environment. If not, the normal boot path is followed as indicated in block 32. Otherwise, the loader determines the interrupt request for which a custom interrupt service routine needs to be installed, as indicated in block 18. A check at diamond 20 determines whether to install custom interrupt routines to service any interrupt requests. If so, the callback function is invoked by the loader, as indicated in block 26.
The loader thus uses a callback function to install and activate the custom interrupt service routine, as indicated in block 28, for a particular interrupt request during the boot process. A check at diamond 22 determines whether the custom interrupt service routine installation was successful. If so, booting continues in the controlled environment, as indicated in block 24.
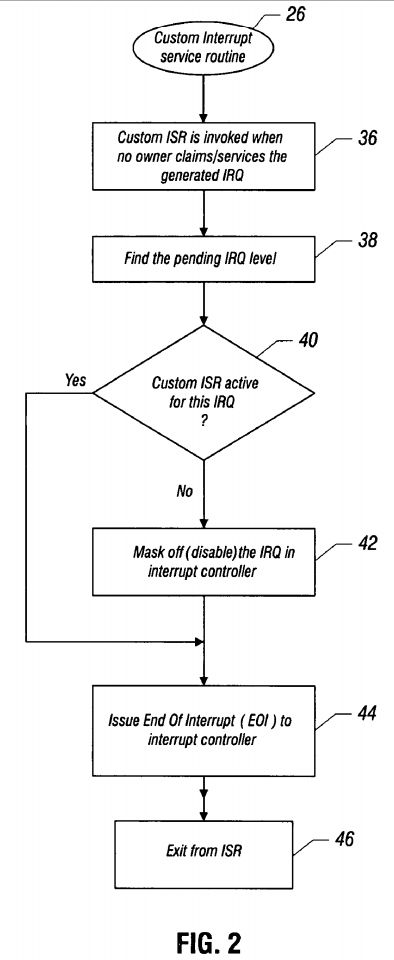
The custom interrupt service routine operates, as indicated in FIG. 2, in accordance with one embodiment. The custom interrupt service routine is invoked when no owner claims or services the generated interrupt request, as indicated in block 36. The pending interrupt request level is then identified, as indicated in block 38. If the custom interrupt service routine is active for the request, as determined in diamond 40, an end of interrupt is issued to the interrupt controller, as indicated in block 44. Then there is an exit from the interrupt service routine.
If the custom interrupt service routine is not active, the interrupt request is masked off and disabled in their interrupt controller, as indicated in block 42. Then an end of interrupt is issued to the interrupt controller, as indicated in block 44 and there is an exit from the interrupt service routine.
When active, the interrupt service routine finds the unclaimed interrupt request and whether the custom interrupt service routine has been activated for the unclaimed request. If the custom interrupt service routine has been activated for the unclaimed request, it issues an end of interrupt without disabling the interrupt request, as indicated in FIG. 2, block 44. The loader can also optionally uninstall a custom interrupt service routine when the boot process is complete. The loader may supply a new custom interrupt service routine or use a built-in custom interrupt service routine in the basic input/output system.
In some embodiments, the use of a custom interrupt service routine makes the basic input/output system compatible with various environments, including both VT and non-VT environments. A custom interrupt service routine may be installed on demand and may be installed for one or more interrupt requests. It may also be uninstalled in some embodiments.